The CRTE (Certified Red Team Expert) course is focused on attacking and defending Active Directory environments using an assume breach methodology. The course will cover a wide range of topics, with an emphasis on hands-on learning and real-world attack simulations. Here's a more detailed overview:
- Active Directory Concepts: The course will begin with a review of Active Directory (AD) fundamentals, including its structure (forests, domains, organizational units), and its role in enterprise environments, as well as the concept that a forest is a security boundary. It will focus on hybrid identity environments where on-premises Active Directory is used for identity and access management.
- Offensive Tooling: A variety of tools will be used throughout the course, including:
- PowerShell will be used for enumeration, lateral movement and other tasks, and the course will explore techniques to bypass security measures like AMSI and Constrained Language Mode.
- .NET tools such as Rubeus, and others will be used and the course will cover methods for bypassing AV/EDR detection via obfuscation and in-memory execution using loaders.
- Native Windows executables will also be employed as needed.
- The course emphasizes using built-in tools and avoiding exploitation frameworks.
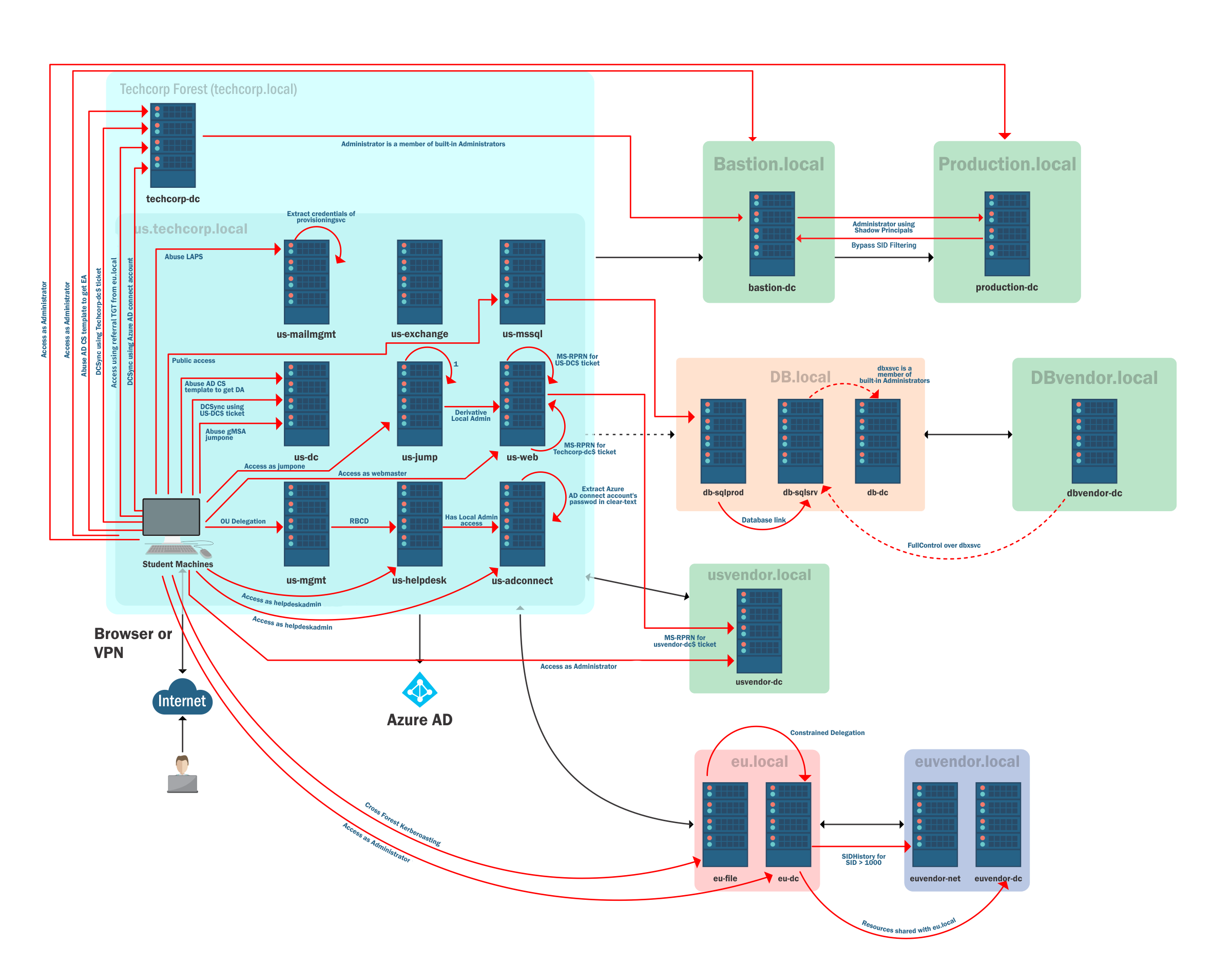
- Methodology: The course will follow an assume breach methodology, focusing on insider attack simulations. The course will simulate an adversary that has already gained initial access to the environment and will focus on:
- Targeted enumeration.
- Local privilege escalation.
- Identifying and exploiting admin privileges.
- Lateral movement across machines.
- Credential extraction.
- Privilege escalation to domain admin.
- Cross-trust attacks between different forests.
- Persistence and exfiltration.
- Bypassing Security Measures: The course will cover techniques to bypass various security measures such as Windows Defender, Microsoft Defender for Endpoint (MDE), and Windows Defender Application Control (WDAC). This includes both evading and bypassing these defenses.
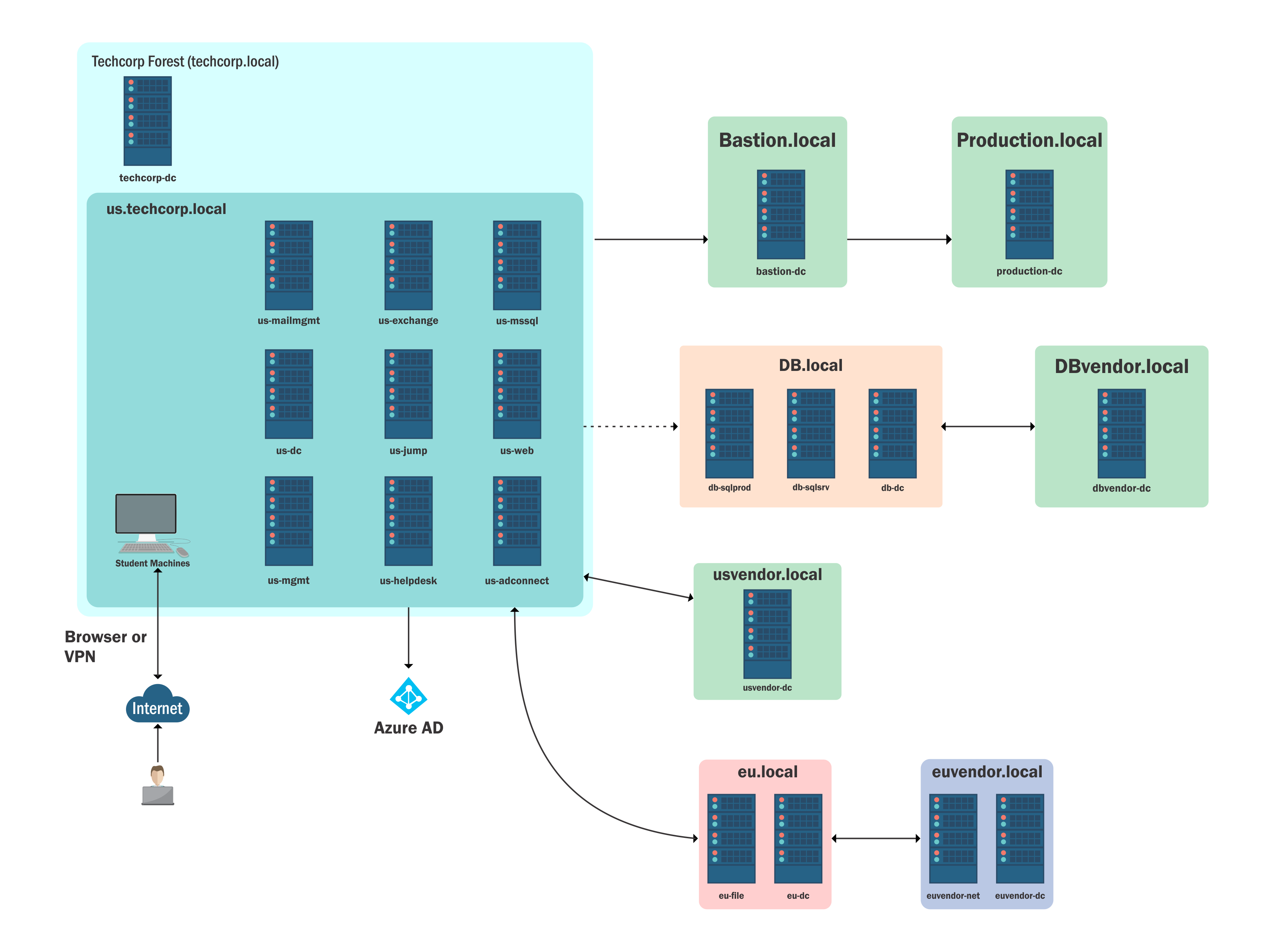
- Lab Environment: The lab environment is a simulation of a real-world network infrastructure with multiple forests belonging to the fictional company, Tech Corp, that is built using fully patched server 2019 machines running at the server 2016 forest functional level. The lab is designed to be easily accessible and realistic. The lab also incorporates a hybrid identity setup.
- Key Concepts and Techniques: The course will explore many attack techniques, including:
- Kerberoasting: Exploiting Kerberos service principal names (SPNs) to gain access to accounts.
- Resource Based Constrained Delegation (RBCD): Abusing resource-based delegation to gain access to other machines.
- Unconstrained Delegation: Exploiting unconstrained delegation to obtain domain or enterprise admin privileges.
- Credential Extraction: Extracting credentials from various sources, including LSASS memory. The course will explore the challenges and techniques for extracting credentials while evading detection.
- Silver and Diamond Tickets: Forging and using silver and diamond tickets for persistence and lateral movement.
- ACL Abuse: Manipulating Access Control Lists (ACLs) for persistence, including using AdminSDHolder.
- Cross-Trust Attacks: Performing attacks across different forests by abusing trust relationships.
- Active Directory Certificate Services (ADCS): Exploiting ADCS to obtain certificates for authentication and persistence.
- MSSQL Server Abuse: Leveraging MSSQL servers for lateral movement and command execution.
- Shadow Credentials: Using the MSDS-KeyCredentialLink attribute to add alternate credentials to user or computer objects, and then using those credentials to extract NTLM hashes or gain access.
- Persistence Methods: The course will also cover a variety of methods for achieving persistence in a domain environment including modifying security descriptors of remote access protocols, such as WMI, PowerShell remoting, and remote registry.
The CRTE course aims to provide a comprehensive understanding of offensive security tactics within Active Directory environments by emphasizing hands-on experience, realistic scenarios, and a focus on abusing functionality and avoiding simple exploits.