This guide provides an extensive overview of an advanced technical course dedicated to offensive security, penetration testing, and red teaming within Microsoft Azure and Entra ID environments. The curriculum is structured around the stages of an attack kill chain, beginning with discovery and reconnaissance to identify target services and followed by various initial access techniques, such as exploiting insecure services and performing illicit consent grant attacks.
Post-compromise activities heavily emphasize authenticated enumeration of Azure resources and Entra ID objects using tools like the Mg Graph PowerShell module and Az PowerShell module. The course covers Azure-specific attack vectors including Managed Identity abuse, Token theft, Pass-the-PRT attacks, and Cloud to On-Premise pivoting.
Lab Environment Overview
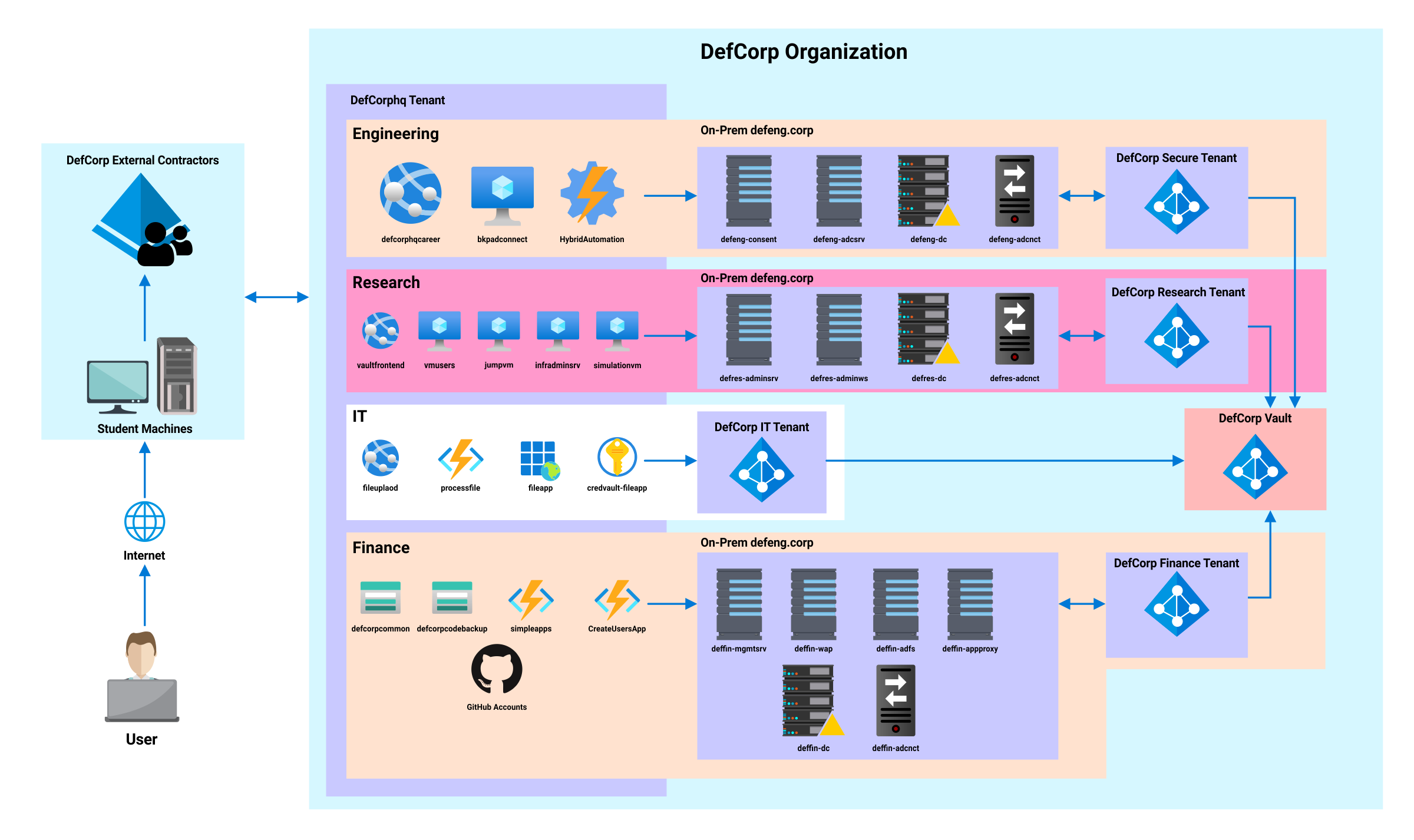
The CARTP lab simulates a hybrid environment with DefCorp, a defense contractor with high security requirements. The environment includes:
- Entra ID (Azure AD): Cloud identity provider with user and application management
- Azure Resources: Various Azure services including App Services, Storage Accounts, Virtual Machines
- Hybrid Setup: On-Premise Active Directory synced with Azure via Azure AD Connect
Attack Paths & Techniques
The CARTP certification covers advanced Azure Red Teaming techniques including:
- Unauthenticated Reconnaissance: Tenant identification, subdomain enumeration, user enumeration
- Token Manipulation: MFA bypass, token extraction, device code flow abuse
- Authenticated Enumeration: Mg Graph module, Az PowerShell, Azure REST API
- Initial Access Attacks: Illicit consent grants, insecure storage abuse, application vulnerabilities
- Managed Identity Abuse: Token extraction from Azure services, privilege escalation
- Pass-the-PRT Attacks: Primary Refresh Token theft and reuse
- Cloud to On-Premise Pivoting: Hybrid identity attacks, Azure AD Connect exploitation
- Lateral Movement: VM access, tunneling, credential harvesting
Lab Phases
- Phase 1: Foundational Concepts & Unauthenticated Reconnaissance: Azure/Entra ID architecture, tenant identification, user enumeration
- Phase 2: Authenticated Enumeration: Token acquisition, Mg/Az module usage, directory enumeration
- Phase 3: Initial Access Attacks & Tokens: MFA bypass, token theft, managed identity exploitation
The CARTP certification represents advanced Azure security assessment skills, requiring deep understanding of Microsoft cloud identity, Azure resource management, and hybrid attack vectors.